Professional Documents
Culture Documents
Bell LaPadula Model
Uploaded by
vai27100%(1)100% found this document useful (1 vote)
2K views8 pagesThe Bell-Lapadula model of protection systems deals with the control of information flow. Each subject has a clearance and each object has a classification which attaches it to a security level. Access rights given to a subject are the following: Read-Only: The subject can only read the object.
Original Description:
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
DOC, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe Bell-Lapadula model of protection systems deals with the control of information flow. Each subject has a clearance and each object has a classification which attaches it to a security level. Access rights given to a subject are the following: Read-Only: The subject can only read the object.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
100%(1)100% found this document useful (1 vote)
2K views8 pagesBell LaPadula Model
Uploaded by
vai27The Bell-Lapadula model of protection systems deals with the control of information flow. Each subject has a clearance and each object has a classification which attaches it to a security level. Access rights given to a subject are the following: Read-Only: The subject can only read the object.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
You are on page 1of 8
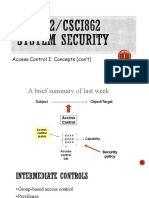
Protection: Bell-Lapadula Model
by Harsh Manocha
This page is under construction.
The Bell-Lapadula Model of protection systems deals with the
control of information flow. It is a linear non-discretionary model.
This model of protection consists of the following components:
• A set of subjects, a set of objects, and an access control
matrix.
• Several ordered security levels. Each subject has a
clearance and each object has a classification which
attaches it to a security level. Each subject also has a current
clearance level which does not exceed its clearance level.
Thus a subject can only change to a clearance level below its
assigned clearance level.
The set of access rights given to a subject are the following:
• Read-Only: The subject can only read the object.
• Append : The subject can only write to the object but it
cannot read.
• Execute : The subject can execute the object but can neither
read nor write.
• Read-Write: The subject has both read and write
permissions to the object.
Control Attribute: This is an attribute given to the subject that
creates an object. Due to this, the creator of an object can pass any
of the above four access rights of that object to any subject.
However, it cannot pass the control attribute itself. The creator of
an object is also known as the controller of that object.
Restrictions imposed by the Bell-Lapadula Model:
The following restrictions are imposed by the model:
• reading down: A subject has only read access to objects
whose security level is below the subject's current clearance
level. This prevents a subject from getting access to
information available in security levels higher than its current
clearance level.
• writing up: A subject has append access to objects whose
security level is higher than its current clearance level. This
prevents a subject from passing information to levels lower
than its current level.
The Bell-Lapadula model supplements the access matrix with the
above restrictions to provide access control and information flow.
For instance, if a subject has read access to an object in the access
matrix, it may still not be able to exercise this right if the object is
at a security level higher than its clearance level.
Bell and Lapadula modeled the behavior of a protection system as
a finite state machine and defined a set of state transitions that
would not violate the security of the system. The following
operations gaurantee a secure system:
• get access: Used by a subject to initiate access to an object
(read, append, execute etc )
• release access: Used by a subject to giveup an initiated
access.
• give access: Controller of an object can give a particular
access (to that object) to a subject.
• rescind access: Controller of an object can revoke a
designated access ( to that object) from a subject.
• create object: Allows a subject to activate an inactive object.
• delete object: Allows a subject to deactivate an active object.
• change security level:Allows a subject to change its clearance
level ( below an initial assigned value)
However certain conditions have to be satisfied before the above
operations can be performed. For instance, a subject can exercise
give and rescind rights to an object only if it has control attributes
to that object.
Bell-Lapadula is a simple linear model that exercises access and
information flow control through the above restrictive properties
and operations. However, it has a disadvantage of security levels of
objects being static. The properties of this model might become too
restrictive in cases when certain operations are outside the context
of protection system.
Questions
1) What is the effect of reading down and writing up restrictions
imposed by the Bell-Lapadula model?
2) Why is a subject's current clearance level only lower than its
initial assigned clearance level ?
3) Write down the conditions to be satisfied for each of the seven
operations to be executed.
4) Why is the Bell-Lapadula model a non-discretionary one?
References
Singhal,M. and Shivaratri,N.: Advanced Concepts in Operating
Systems , McGraw-Hill, 1994.
Peterson,J.L. and Silberschatz,A.: Operating System Concepts, 2nd
ed, Addison Wesley, 1985.
Landwehr,C.E, Formal Models of Computer Security, ACM
Computing Surveys, Sept. 1981
harsh@csgrad.cs.vt.edu
Go Back to the Operating Systems Page.
17.4 MANDATORY ACCESS CONTROL *
Discretionary access control mechanisms, while
generally e_ective, have certain weaknesses.
In particular they are susceptible to Trojan horse
schemes whereby a devious
Security 509
unauthorized user can trick an authorized user into
disclosing sensitive data. For example,
suppose that student Tricky Dick wants to break into
the grade tables of instructor
Trustin Justin. Dick does the following:
He creates a new table called MineAllMine and gives
INSERT privileges on this
table to Justin (who is blissfully unaware of all this
attention, of course).
He modi_es the code of some DBMS application that
Justin uses often to do a
couple of additional things: _rst, read the Grades
table, and next, write the result
into MineAllMine.
Then he sits back and waits for the grades to be
copied into MineAllMine and later
undoes the modi_cations to the application to ensure
that Justin does not somehow _nd
out later that he has been cheated. Thus, despite the
DBMS enforcing all discretionary
access controls|only Justin's authorized code was
allowed to access Grades|sensitive
data is disclosed to an intruder. The fact that Dick
could surreptitiously modify
Justin's code is outside the scope of the DBMS's
access control mechanism.
Mandatory access control mechanisms are aimed at
addressing such loopholes in discretionary
access control. The popular model for mandatory
access control, called
the Bell-LaPadula model, is described in terms of
objects (e.g., tables, views, rows,
columns), subjects (e.g., users, programs), security
classes, and clearances. Each
database object is assigned a security class, and
each subject is assigned clearance for
a security class; we will denote the class of an object
or subject A as class(A). The
security classes in a system are organized according
to a partial order, with a most
secure class and a least secure class. For
simplicity, we will assume that there are
four classes: top secret (TS), secret (S), con_dential
(C), and unclassi_ed (U). In this
system, TS > S > C > U, where A > B means that
class A data is more sensitive than
class B data.
The Bell-LaPadula model imposes two restrictions on
all reads and writes of database
objects:
1. Simple Security Property: Subject S is allowed
to read object O only if class(S)
_ class(O). For example, a user with TS clearance can
read a table with C clearance,
but a user with C clearance is not allowed to read a
table with TS classi_-
cation.
2. *-Property: Subject S is allowed to write object O
only if class(S) _ class(O). For
example, a user with S clearance can only write
objects with S or TS classi_cation.
If discretionary access controls are also speci_ed,
these rules represent additional restrictions.
Thus, to read or write a database object, a user must
have the necessary
privileges (obtained via GRANT commands) and the
security classes of the user and the
object must satisfy the preceding restrictions. Let us
consider how such a mandatory
510 Chapter 17
control mechanism might have foiled Tricky Dick.
The Grades table could be classi
_ed as S, Justin could be given clearance for S, and
Tricky Dick could be given a
lower clearance (C). Dick can only create objects of C
or lower classi_cation; thus,
the table MineAllMine can have at most the
classi_cation C. When the application
program running on behalf of Justin (and therefore
with clearance S) tries to copy
Grades into MineAllMine, it is not allowed to do so
because class(MineAllMine) <
class(application), and the *-Property is violated.
You might also like
- Bates V Post Office: Steve Parker Witness Statement 1Document79 pagesBates V Post Office: Steve Parker Witness Statement 1Nick Wallis100% (2)
- Deenas InvoiceDocument272 pagesDeenas Invoicevai27No ratings yet
- Module3 - Security EngineeringDocument218 pagesModule3 - Security EngineeringHùng ĐỗNo ratings yet
- Connected Car ASRv.1-1Document84 pagesConnected Car ASRv.1-1monel_24671No ratings yet
- InterviewDocument6 pagesInterviewvai27No ratings yet
- Access ControlDocument51 pagesAccess ControlIbrahimNo ratings yet
- Audio Steganography Complete MATLAB Report-1Document65 pagesAudio Steganography Complete MATLAB Report-1Chandana P100% (2)
- Oracle Quick Guides: Part 4 - Oracle Administration: Security and PrivilegeFrom EverandOracle Quick Guides: Part 4 - Oracle Administration: Security and PrivilegeNo ratings yet
- Bell LaPadula ModelDocument4 pagesBell LaPadula ModelNeeraj VishwakarmaNo ratings yet
- Security Models NotesDocument12 pagesSecurity Models NotesanuNo ratings yet
- Cissp 3Document64 pagesCissp 3gmkontNo ratings yet
- 4670 Lecture5 Mls Inference AggregationDocument82 pages4670 Lecture5 Mls Inference Aggregationsimonas_67No ratings yet
- Cccure 03. Security Architecture and Engineering Cissp Practice Test With Answer and ExplanationDocument423 pagesCccure 03. Security Architecture and Engineering Cissp Practice Test With Answer and ExplanationMona AdelNo ratings yet
- Bell LapadullaDocument17 pagesBell LapadullaShame BopeNo ratings yet
- Classic Security Models of Data Base SecurityDocument6 pagesClassic Security Models of Data Base SecurityYashi BajpaiNo ratings yet
- PIS Module 2Document32 pagesPIS Module 2Zayn TawfikNo ratings yet
- Computer Systems Security (CS470) : DR Ahmed Rafat AbasDocument16 pagesComputer Systems Security (CS470) : DR Ahmed Rafat AbasAh M EdNo ratings yet
- Assignment: Security IN ComputingDocument11 pagesAssignment: Security IN ComputingNithish GeorgeNo ratings yet
- L07 ISDS-Trusted ComputingDocument38 pagesL07 ISDS-Trusted ComputingedwinaNo ratings yet
- 2023+CISSP+Domain+3+Study+Guide+by+ThorTeaches.com+v3.1Document67 pages2023+CISSP+Domain+3+Study+Guide+by+ThorTeaches.com+v3.1MurthyNo ratings yet
- Security Architecture and DesignDocument38 pagesSecurity Architecture and DesigndonweenaNo ratings yet
- Security Methods and Security MechanismsDocument14 pagesSecurity Methods and Security MechanismsSIDDHARTHANo ratings yet
- Bell LaPadula ModelDocument8 pagesBell LaPadula Modeljiha2007No ratings yet
- CIS 4360 - Introduction To Computer Security - Fall 2010 - With AnswersDocument6 pagesCIS 4360 - Introduction To Computer Security - Fall 2010 - With AnswersrayNo ratings yet
- Security Part 2Document6 pagesSecurity Part 2kassahunNo ratings yet
- CSCI262 Trustedcomputing 1+2Document86 pagesCSCI262 Trustedcomputing 1+2ami_haroonNo ratings yet
- Week 2bDocument37 pagesWeek 2bThasleem ReyasNo ratings yet
- Biba Security Model ComparisonDocument9 pagesBiba Security Model Comparisonphuc4bkmaNo ratings yet
- Access Control: Today We Will Start To Cover Access ControlDocument54 pagesAccess Control: Today We Will Start To Cover Access Controlhiehie272No ratings yet
- Student NotesDocument10 pagesStudent NotesPRANAV PRAKASH TIWARYNo ratings yet
- Access Control: Today We Will Start To Cover Access ControlDocument54 pagesAccess Control: Today We Will Start To Cover Access ControlAli AshrafNo ratings yet
- Mandatory Flow Control Models ExplainedDocument23 pagesMandatory Flow Control Models ExplainedPrateek jainNo ratings yet
- Cram DM1Document8 pagesCram DM1Del NoitNo ratings yet
- Sec ModsDocument67 pagesSec ModsBodea FlorinNo ratings yet
- Mandatory Access Control: 1 Why Need MACDocument6 pagesMandatory Access Control: 1 Why Need MACSuada Bőw WéěžýNo ratings yet
- ISC2 3 Access Control ConceptsDocument21 pagesISC2 3 Access Control ConceptsAj JohnsonNo ratings yet
- Chapter 23 Database SecurityDocument11 pagesChapter 23 Database Securitykirtan71No ratings yet
- Lecture 2 Access Control (Part 2)Document23 pagesLecture 2 Access Control (Part 2)kwaheed100% (1)
- Subject: An Entity Capable of Accessing Objects. Generally, The Concept ofDocument6 pagesSubject: An Entity Capable of Accessing Objects. Generally, The Concept ofAnonymous woEiU4xNo ratings yet
- Week10-11-Access Control Models-PoliciesDocument33 pagesWeek10-11-Access Control Models-Policiesmahtab mahtabNo ratings yet
- Isc Chapter 3Document44 pagesIsc Chapter 3Cristina Joy CruzNo ratings yet
- Chapter 5 Security Mechanisms and Techniques Compatibility ModeDocument92 pagesChapter 5 Security Mechanisms and Techniques Compatibility Modeyordanos yohannesNo ratings yet
- Sec ModsDocument70 pagesSec ModsJasmin DamijanicNo ratings yet
- ch04 ModifiedDocument28 pagesch04 ModifiedFood FeedNo ratings yet
- Access Control Fundamentals: 2.1 Protection SystemDocument14 pagesAccess Control Fundamentals: 2.1 Protection SystemMuhammad Tehseen KhanNo ratings yet
- Week 3Document99 pagesWeek 3Thasleem ReyasNo ratings yet
- Database Security - FinalDocument11 pagesDatabase Security - FinalAnshuman021No ratings yet
- Firewall Trusted SystemDocument18 pagesFirewall Trusted SystemTanvi ModiNo ratings yet
- Ch09 ModelsDocument11 pagesCh09 ModelsDevy SagalaNo ratings yet
- Authorisation: by M.O. OdeoDocument33 pagesAuthorisation: by M.O. OdeoSNo ratings yet
- Lecture Notes: Potential Information Security ViolationsDocument9 pagesLecture Notes: Potential Information Security ViolationsTESFAHUNNo ratings yet
- A Pattern Language For Security ModelsDocument13 pagesA Pattern Language For Security ModelsThandenown1928No ratings yet
- Bell LapadulaDocument2 pagesBell LapadulaAshabe LindaNo ratings yet
- WeekDocument36 pagesWeekMaaz ChowdhryNo ratings yet
- Bell-LaPadula and Biba security modelsDocument6 pagesBell-LaPadula and Biba security modelsGrant DuncanNo ratings yet
- 3-Module-2 (Part-1) - 19-05-2023Document41 pages3-Module-2 (Part-1) - 19-05-2023Shreya RajpalNo ratings yet
- 03d - Access Control and AuthorizationDocument11 pages03d - Access Control and AuthorizationSyarifah AyuwandiraNo ratings yet
- Unit-8 Database SecurityDocument21 pagesUnit-8 Database SecurityShiv PatelNo ratings yet
- 12Document43 pages12vatsb22No ratings yet
- Database Management System: Chapter 24: Database Security (Part 2)Document20 pagesDatabase Management System: Chapter 24: Database Security (Part 2)Samah aldawoodNo ratings yet
- Information Security ModelDocument3 pagesInformation Security ModelDavidNo ratings yet
- MT5104 - Computer Security - Lecture 3 ModelsDocument17 pagesMT5104 - Computer Security - Lecture 3 Modelsameet_ngangomNo ratings yet
- File PDFDocument17 pagesFile PDFehsan.amimul3795No ratings yet
- Case Studies in GOF Creational Patterns: Case Studies in Software Architecture & Design, #2From EverandCase Studies in GOF Creational Patterns: Case Studies in Software Architecture & Design, #2No ratings yet
- Utgstact33 PDFDocument2 pagesUtgstact33 PDFvai27No ratings yet
- Utgstact33 PDFDocument2 pagesUtgstact33 PDFvai27No ratings yet
- OCJP 6 Planning Chart TemplateDocument2 pagesOCJP 6 Planning Chart Templatevai27No ratings yet
- DurgaSoft SCJP Notes Part 1 - JavabynataraJ PDFDocument255 pagesDurgaSoft SCJP Notes Part 1 - JavabynataraJ PDFSiva Sai Charan KondapiNo ratings yet
- Https Doc 10 A0 Apps Viewer - GoogleusercontentDocument1 pageHttps Doc 10 A0 Apps Viewer - Googleusercontentvai27No ratings yet
- CompleteDocument48 pagesCompletevai27No ratings yet
- XML CompleteDocument23 pagesXML Completevai27No ratings yet
- Idol Dbms Journal 1Document44 pagesIdol Dbms Journal 1vai27No ratings yet
- Clinical ChemistryDocument3 pagesClinical Chemistryvai27No ratings yet
- C++ Programming/Classes/Abstract ClassesDocument5 pagesC++ Programming/Classes/Abstract Classesvai27No ratings yet
- ER Airline ReservationDocument4 pagesER Airline Reservationvai27No ratings yet
- C++ Programming/Classes/Abstract ClassesDocument5 pagesC++ Programming/Classes/Abstract Classesvai27No ratings yet
- Differences Between ANSI C CPlusPlus and ANSI CPlusPlusDocument10 pagesDifferences Between ANSI C CPlusPlus and ANSI CPlusPlusvai27No ratings yet
- General Specifications: GS 33K01A10-50EDocument17 pagesGeneral Specifications: GS 33K01A10-50Eabbutalibb5407No ratings yet
- Student Thesis on 'Title of SDP' for Electrical EngineeringDocument22 pagesStudent Thesis on 'Title of SDP' for Electrical Engineeringfaiza elahiNo ratings yet
- Thirumalai ResumeDocument4 pagesThirumalai ResumeRadhakrishnan SivamoorthiNo ratings yet
- ODI Performance TuningDocument1 pageODI Performance Tuningmanoj kumarNo ratings yet
- Minesweeper GameDocument4 pagesMinesweeper GameAnurag PandeyNo ratings yet
- Graduate level civil employment benefitDocument2 pagesGraduate level civil employment benefitastikNo ratings yet
- ASSIGNMENTDocument12 pagesASSIGNMENTAshish KumarNo ratings yet
- Tori Tidswell: Work ExperienceDocument2 pagesTori Tidswell: Work Experienceapi-557437673No ratings yet
- Rhino Dot Net CrashDocument12 pagesRhino Dot Net CrashAnonymous qZT72R9No ratings yet
- N6073Document1 pageN6073d-fbuser-164431658No ratings yet
- Formulas VlookupDocument25 pagesFormulas VlookupJp CombisNo ratings yet
- Drawing Indicator's Emissions in MQL5 - MQL5 Articles PDFDocument8 pagesDrawing Indicator's Emissions in MQL5 - MQL5 Articles PDFnobodikNo ratings yet
- CCNA 4 Chapter 5 v5 Exam Answers 2014Document8 pagesCCNA 4 Chapter 5 v5 Exam Answers 2014adrian743842No ratings yet
- IEC61131 Logic For SCADA Optomization Entelec PaperDocument6 pagesIEC61131 Logic For SCADA Optomization Entelec PaperSurachet Pavanne100% (1)
- Unit Plan On Christmas Cake - VKDocument5 pagesUnit Plan On Christmas Cake - VKJessa LinsanganNo ratings yet
- Actvity Sheet No.4 Tabora, J 1mt04 HismlsDocument2 pagesActvity Sheet No.4 Tabora, J 1mt04 HismlsJanela Escalante Tabora100% (1)
- IT Support & Sales Engineer Seeking New ChallengeDocument2 pagesIT Support & Sales Engineer Seeking New Challengemikesoni SNo ratings yet
- Android Based Object Detection Application For Food ItemsDocument6 pagesAndroid Based Object Detection Application For Food ItemsHafza GhafoorNo ratings yet
- N Fs Maestro ClientDocument320 pagesN Fs Maestro ClientapariciocoolNo ratings yet
- Siemens Simatic Step 7 Programmers HandbookDocument64 pagesSiemens Simatic Step 7 Programmers HandbookMario BorgiattinoNo ratings yet
- Barco INSIGHTS Specialist EN v2.1Document66 pagesBarco INSIGHTS Specialist EN v2.1Siel de SchepperNo ratings yet
- WP SQL To Nosql Architectur Differences Considerations Migration 1+ (6) - 1641371845027Document13 pagesWP SQL To Nosql Architectur Differences Considerations Migration 1+ (6) - 1641371845027KP SNo ratings yet
- MX TL MXMC 1-8 en 20180703Document142 pagesMX TL MXMC 1-8 en 20180703aleksandar petrovicNo ratings yet
- Buffer Cache AdvisoryDocument8 pagesBuffer Cache Advisorysteve_fordNo ratings yet
- Networking Fundamentals Quiz with AnswersDocument4 pagesNetworking Fundamentals Quiz with AnswersSoru-Dara JemivakyNo ratings yet
- Application of Computer in NursingDocument53 pagesApplication of Computer in NursingAnushka Sweety100% (1)