Professional Documents
Culture Documents
Multiple Choice
Uploaded by
Raviraja RamasamyOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Multiple Choice
Uploaded by
Raviraja RamasamyCopyright:
Available Formats
Introduction to E-Commerce
Chapter 9 Payments and Order Fulfillment
Practical Exercises
True-False Questions
1 Almost 50% of the purchases made online are done with credit cards. Answer: Reference: LensDoc Organizes Payments Online
2 B2B transactions are traditionally conducted using credit cards. Answer: Reference: Paying with Credit Cards Online
3 E-payment systems that require the payer to install specialized components have proven less likely to succeed. Answer: Reference: Characteristics of Successful E-payment Methods
4 Even if the same algorithm is used, the same plaintext encrypted with two different keys will produce two different pieces of ciphertext. Answer: Reference: Public key Encryption
5 In symmetric key encryption, the private key falling into the hands of hackers with the ability to intercept encrypted packets would not compromise the privacy of the ciphertext. Answer: Reference: Public Key Infrastructure
6 Digital signatures in the United States now have the same legal standing as a signature written in ink on paper. Answer: Reference: Digital Signatures: Authenticity and Nondenial
7 SET specifications are managed through a joint venture of Visa and MasterCard. Answer: Reference: Secure Electronic Transactions
8 When a stolen credit card is used to make purchases, the issuer of the credit card will, with adequate documentation, credit the cardholders account and charge back the merchant. Answer: Reference: Security Risks with Credit Cards
9 Like charge cards, the balance on purchasing cards is paid in full each month. Answer: Reference: Purchasing Cards for B2B
Payments and Order Fulfillment
Chapter 10
10 With current technology, it is theoretically impossible to hack into a smart card. Answer: Reference: Securing Smart Cards
11 Prepaid long distance phone cards are the most widely used smart cards today. Answer: Reference: Applications of Smart Cards
12 Like traditional cash, e-cash is anonymous. Answer: Reference: E-Cash and Innovative Payment Methods
13 P2P payments enable the transfer of funds between individuals. Answer: Reference: Person-To-Person Payments
14 Order fulfillment includes not only providing customers with what they ordered on a timely basis, but also includes all related customer services. Answer: Reference: Overview of Order Fulfillment
15 Demand uncertainties and variability along the supply chain are the primary causes of the bullwhip effect. Answer: Reference: The Bullwhip Effect
16 B2B order fulfillment is different from B2C because orders usually involve larger quantities. Answer: Reference: Order Fulfillment in B2B
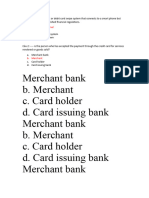
Multiple Choice Questions
17 The government agency that controls the e-payment process is called the: a. b. c. d. regulator. payee. merchant. issuer. Reference: Paying with Credit Cards Online
Answer:
Introduction to E-Commerce
18 All of the following are critical factors in determining whether a particular method of epayment achieves widespread acceptance EXCEPT: a. b. c. d. independence. interoperability. portability. transferability. Reference: Characteristics of Successful E-Payment Methods
Answer:
19 The Public Key Infrastructure is/are: a. a security company that sells locking devices to protect Internet hardware components. b. the security protocols in place within an organization to safeguard the tangible computing assets of a company. c. the technical components, infrastructure, and practices needed to enable the use of public key encryption. d. the technical components, software, and procedures overseen by the government that protect the public and private hardware attached to the Internet. Answer: Reference: Public Key Infrastructure
20 An encryption key system in which the same key is used to encrypt and decrypt the message is called the: a. b. c. d. public key. asymmetric key. data key. private key. Reference: Public Key Infrastructure
Answer:
21 One encryption key system sends the same public key to all users who use the key to encrypt messages. The resulting ciphertext, however, cant be read without a private key known only by the sender. This encryption scheme is known as: a. b. c. d. private key. data key. asymmetric key. symmetric key. Reference: Public Key Infrastructure
Answer:
Payments and Order Fulfillment 22 Third parties who issue digital certificates are called: a. b. c. d. certificate brokers. certificate processors. certificate issuers. certificate authorities.
Chapter 10
Answer:
Reference: Digital Certificates and Certificate Authorities
23 A protocol developed by Netscape which handles data encryption in a transparent manner within the Web browser is called: a. b. c. d. Netscape Navigator. secure socket layer. IPSec. Verisign. Reference: Secure Socket Layer
Answer:
24 Harold uses a card to buy a baseball card online. The cost of the card is deducted from his checking account. Harold used a: a. b. c. d. credit card. charge card. debit card. e-wallet. Reference: Payment Cards
Answer:
25 The card which provides the holder credit to make purchases which are paid in full upon receipt of the monthly statement is called the: a. b. c. d. credit card. charge card. debit card. e-wallet. Reference: Payment Cards
Answer:
26 A special-purpose nonrevolving card issued to employees solely for the purpose of purchasing and paying for nonstrategic materials and services is called: a. b. c. d. a virtual credit card. a debit card. an e-wallet. a purchase card. Reference: Purchasing Cards for B2B
Answer:
Introduction to E-Commerce 27 An advantage of e-cash is: a. b. c. d.
the identity of the purchaser doesnt have to be revealed at the place of purchase. it is widely accepted offline. a critical mass of users was established in the earliest days of the Internet. it is widely accepted online. Reference: E-Cash and Innovative Payment Methods
Answer:
28 An e-reward from a merchant for visiting, registering, or purchasing from its site that can be accumulated by the buyer and traded for products at a later date is called: a. b. c. d. e-cash. a debit card. beenz. a purchase card. Reference: E-Loyalty and Rewards Programs
Answer:
29 The major source of uncertainty in supply chains is: a. b. c. d. inflation. fluctuations in foreign currency exchange rates. internal manufacturing schedules. demand forecasts. Reference: Typical Problems
Answer:
Essay Questions
30 Describe four processes involved in the order fulfillment process.
Reference: The Process of Order Fulfillment in EC
You might also like
- Electronic Commerce 2012 7E Test Bank Chapter 10: Subscribers Only. The Answer May Locate at The End of This PageDocument10 pagesElectronic Commerce 2012 7E Test Bank Chapter 10: Subscribers Only. The Answer May Locate at The End of This Pageyoussef888 tharwatNo ratings yet
- AllDocument8 pagesAllNguyễn Thị Hồng YếnNo ratings yet
- Mid TermDocument9 pagesMid Termhyd.hus54646No ratings yet
- 4 Electronic Payment SystemsDocument39 pages4 Electronic Payment SystemsYashasweeNo ratings yet
- EpaymentDocument6 pagesEpaymentvyknk21No ratings yet
- E-Business AssignmentDocument21 pagesE-Business AssignmentYashi BokreNo ratings yet
- E - Commerce Unit 2 RGPV SylabbusDocument22 pagesE - Commerce Unit 2 RGPV SylabbusDeepak Kumar RajakNo ratings yet
- Chapter 5Document14 pagesChapter 5Soll HaileNo ratings yet
- Tif 9780273761389 10Document52 pagesTif 9780273761389 10Anh Nguyễn100% (1)
- Ecommerce Final ExamDocument5 pagesEcommerce Final ExamZerihun Bekele100% (4)
- Chapter 3 E - CommerceDocument11 pagesChapter 3 E - CommerceWolde JanfaNo ratings yet
- Chapter 3 E - CommerceDocument11 pagesChapter 3 E - CommerceAtaklti TekaNo ratings yet
- Electronic Payment SystemDocument20 pagesElectronic Payment SystemThe PaletteNo ratings yet
- Components+of+E+ 1Document8 pagesComponents+of+E+ 1Mui GaiNo ratings yet
- Electronic Payment Systems-FinalDocument105 pagesElectronic Payment Systems-FinalDileep VkNo ratings yet
- Individual AssingmentDocument8 pagesIndividual Assingmentdavi gibranNo ratings yet
- Irene Jepkosgei Kemu BUSS 342-E-Commerce Assignment 1st Trimester 2019 Instructions: Answer All QuestionsDocument9 pagesIrene Jepkosgei Kemu BUSS 342-E-Commerce Assignment 1st Trimester 2019 Instructions: Answer All QuestionsKevin ObaraNo ratings yet
- Electronic Payment GatewayDocument25 pagesElectronic Payment GatewayAnvar Vh V HNo ratings yet
- E Commerce Notes Chapter 5-10Document5 pagesE Commerce Notes Chapter 5-10Taniya Bhalla100% (1)
- Surveying Fintech LandscapeDocument23 pagesSurveying Fintech LandscapeMEENUNo ratings yet
- E Commerce AssignmentDocument6 pagesE Commerce AssignmenthassankitwangoNo ratings yet
- E PaymentDocument15 pagesE PaymentRohan KirpekarNo ratings yet
- DefinitionDocument6 pagesDefinitionSaifur Rahman SteveNo ratings yet
- Communication BbaDocument33 pagesCommunication BbaParmeet KaurNo ratings yet
- MisDocument3 pagesMisDevanshi AroraNo ratings yet
- Payment Systems For Electronic CommerceDocument15 pagesPayment Systems For Electronic CommerceMỹ NgọcNo ratings yet
- Topic 7Document32 pagesTopic 7Safinah HassanNo ratings yet
- Chapter Five: E-Commerce Payment SystemsDocument17 pagesChapter Five: E-Commerce Payment SystemsAgmasie TsegaNo ratings yet
- Electronic CashDocument12 pagesElectronic CashEnam HossainNo ratings yet
- What Is E-Commerce Technology? AnswerDocument13 pagesWhat Is E-Commerce Technology? AnswerRadia Jahan PrantiNo ratings yet
- Unit - IiDocument20 pagesUnit - IiAnkush JadaunNo ratings yet
- E CommerceDocument10 pagesE CommerceSwathi SwaNo ratings yet
- Fundamentals of E-CommerceDocument7 pagesFundamentals of E-CommerceWendoor6696No ratings yet
- June 2022 Vol 2 Issue I - JJ - 2204Document9 pagesJune 2022 Vol 2 Issue I - JJ - 2204Sushmita DevkotaNo ratings yet
- E-Business Models and E-Business Products: (Chapter # 2)Document12 pagesE-Business Models and E-Business Products: (Chapter # 2)NimrahNo ratings yet
- Module IV E-Commerce (Sem II)Document11 pagesModule IV E-Commerce (Sem II)chiragNo ratings yet
- (2014) A Critical Study - Secure Gateway in Payment System For Electronic Transaction PDFDocument7 pages(2014) A Critical Study - Secure Gateway in Payment System For Electronic Transaction PDFAkram PashaNo ratings yet
- Credit Card Processing SystemDocument18 pagesCredit Card Processing System2 CSE 042 VENGIDESAN KNo ratings yet
- Electronic Commerce and E-Wallet: Abhay UpadhayayaDocument5 pagesElectronic Commerce and E-Wallet: Abhay UpadhayayaSavitha VjNo ratings yet
- Chapter 10 - Study GuideDocument40 pagesChapter 10 - Study GuideLoretta Lynn AltmayerNo ratings yet
- Unit-3 Payment Systems, Social Networks and Online AuctionsDocument20 pagesUnit-3 Payment Systems, Social Networks and Online AuctionsPal BhartiNo ratings yet
- Electronic Payment SystemDocument5 pagesElectronic Payment SystemSwati HansNo ratings yet
- Topic: Electronic Payment System. Group No.: 21 Name of The Members: Kirti Vardam 407 Roselene Jathana 408 Kirti Gorivale 409 Vaibhav Basutkar 410Document6 pagesTopic: Electronic Payment System. Group No.: 21 Name of The Members: Kirti Vardam 407 Roselene Jathana 408 Kirti Gorivale 409 Vaibhav Basutkar 410Kirti ParkNo ratings yet
- Cyber Unit 2 Lecture 4Document21 pagesCyber Unit 2 Lecture 4VijayNo ratings yet
- Research Paper On e Cash Payment SystemDocument5 pagesResearch Paper On e Cash Payment Systemcarkdfp5100% (1)
- E-Commerce and E-Bidding: Dr. Kishor AdhikariDocument75 pagesE-Commerce and E-Bidding: Dr. Kishor AdhikariKishor AdhikariNo ratings yet
- Creditcardprocessing SEprojectDocument12 pagesCreditcardprocessing SEprojectMalla Abhinaya100% (2)
- E COMMERCE FINAL COVERAGE MODULE 1 and 2Document9 pagesE COMMERCE FINAL COVERAGE MODULE 1 and 2BRIAN CORPUZ INCOGNITONo ratings yet
- EC ValuDocument8 pagesEC ValuTarun BambhaniyaNo ratings yet
- Final Exams MKTG 15Document4 pagesFinal Exams MKTG 15Michael DimalantaNo ratings yet
- Chapter 5: E-Commerce Payment SystemsDocument8 pagesChapter 5: E-Commerce Payment SystemsAgmasie TsegaNo ratings yet
- E-Business and OutsourcingDocument14 pagesE-Business and Outsourcingáñìkét àfNo ratings yet
- Electronic Payment SystemDocument28 pagesElectronic Payment Systemnehapaspuleti4891100% (1)
- A Review: Secure Payment System For Electronic TransactionDocument8 pagesA Review: Secure Payment System For Electronic Transactioneditor_ijarcsseNo ratings yet
- Unit-4 E-Commerce (PDF - Io) - 1Document6 pagesUnit-4 E-Commerce (PDF - Io) - 1rahuldodiyat001No ratings yet
- Unit - IiDocument7 pagesUnit - IiAnushka YNo ratings yet
- E - Payment and Security System MbaDocument5 pagesE - Payment and Security System MbaShwetaNo ratings yet
- 2.4. E-Commerce Payment Systems and Security IssuesDocument68 pages2.4. E-Commerce Payment Systems and Security IssuesNency ThummarNo ratings yet
- MIS ReportDocument17 pagesMIS Reportzaber chowdhuryNo ratings yet
- Summary of Ahmed Siddiqui & Nicholas Straight's The Anatomy of the SwipeFrom EverandSummary of Ahmed Siddiqui & Nicholas Straight's The Anatomy of the SwipeNo ratings yet
- A Plan of Life - Scepter BookletDocument10 pagesA Plan of Life - Scepter Bookletpeteatkinson@gmail.comNo ratings yet
- Toba Tek SinghDocument4 pagesToba Tek Singhrupal aroraNo ratings yet
- Group6 Business-Proposal Delivery AppDocument15 pagesGroup6 Business-Proposal Delivery AppNathaniel Karl Enin PulidoNo ratings yet
- QuizDocument15 pagesQuizGracie ChongNo ratings yet
- 2019 - List of Equipment, Tools & MaterialsDocument3 pages2019 - List of Equipment, Tools & Materialsreynald manzanoNo ratings yet
- Allergens 08242023Document5 pagesAllergens 08242023Maalvika SinghNo ratings yet
- ORtHOGRAPHIC Plan FinalDocument8 pagesORtHOGRAPHIC Plan FinalKrizzie Jade CailingNo ratings yet
- John Lear UFO Coverup RevelationsDocument30 pagesJohn Lear UFO Coverup RevelationscorneliusgummerichNo ratings yet
- (NewResultBD - Com) Mymensingh Board JSC Scholarship Result 2019Document80 pages(NewResultBD - Com) Mymensingh Board JSC Scholarship Result 2019rthedthbdeth100% (1)
- Chen, Y.-K., Shen, C.-H., Kao, L., & Yeh, C. Y. (2018) .Document40 pagesChen, Y.-K., Shen, C.-H., Kao, L., & Yeh, C. Y. (2018) .Vita NataliaNo ratings yet
- Assignment # (02) : Abasyn University Peshawar Department of Computer ScienceDocument4 pagesAssignment # (02) : Abasyn University Peshawar Department of Computer ScienceAndroid 360No ratings yet
- Xi'an City Sports Park Landscape Improvement ProjectDocument3 pagesXi'an City Sports Park Landscape Improvement ProjectGirija Sankar SahuNo ratings yet
- Making A Spiritual ConfessionDocument2 pagesMaking A Spiritual ConfessionJoselito FernandezNo ratings yet
- Clarifications IntraDocument2 pagesClarifications Intrapm278No ratings yet
- A Psychological Crusade by Fernando Sorrentino - Text 7Document2 pagesA Psychological Crusade by Fernando Sorrentino - Text 7Donnie DominguezNo ratings yet
- 2016 ILA Berlin Air Show June 1 - 4Document11 pages2016 ILA Berlin Air Show June 1 - 4sean JacobsNo ratings yet
- Anna May de Leon Galono, A089 528 341 (BIA Sept. 29, 2015)Document7 pagesAnna May de Leon Galono, A089 528 341 (BIA Sept. 29, 2015)Immigrant & Refugee Appellate Center, LLCNo ratings yet
- Climate Change Forests and Forest Management An O-Wageningen University and Research 481068Document145 pagesClimate Change Forests and Forest Management An O-Wageningen University and Research 481068gulnuromar034No ratings yet
- New Microsoft Office Word DocumentDocument3 pagesNew Microsoft Office Word DocumentVince Vince100% (1)
- AWSCertifiedBigDataSlides PDFDocument414 pagesAWSCertifiedBigDataSlides PDFUtsav PatelNo ratings yet
- TV Studio ChainDocument38 pagesTV Studio ChainKalpesh Katara100% (1)
- Downloaded From Manuals Search EngineDocument29 pagesDownloaded From Manuals Search EnginehaivermelosantanderNo ratings yet
- PHYTOCHEMICAL AND CYTOTOXICITY TESTING OF RAMANIA LEAVES (Bouea Macrophylla Griffith) ETHANOL EXTRACT TOWARD VERO CELLS USING MTT ASSAY METHODDocument6 pagesPHYTOCHEMICAL AND CYTOTOXICITY TESTING OF RAMANIA LEAVES (Bouea Macrophylla Griffith) ETHANOL EXTRACT TOWARD VERO CELLS USING MTT ASSAY METHODLaila FitriNo ratings yet
- Staedtler FIMO Catalogue 2019 (STAEDTLER Hobby Creative Catalogue 2019 En)Document100 pagesStaedtler FIMO Catalogue 2019 (STAEDTLER Hobby Creative Catalogue 2019 En)Tom S50% (2)
- CVT / TCM Calibration Data "Write" Procedure: Applied VehiclesDocument20 pagesCVT / TCM Calibration Data "Write" Procedure: Applied VehiclesАндрей ЛозовойNo ratings yet
- Soal CautionDocument10 pagesSoal Cautionadhyatnika geusan ulun50% (2)
- Business Analytics Case Study - NetflixDocument2 pagesBusiness Analytics Case Study - NetflixPurav PatelNo ratings yet
- Adverbial Phrases 3Document21 pagesAdverbial Phrases 3Jobelle VergaraNo ratings yet
- Grid / Hippodamian Model: Hippodamus of MiletusDocument34 pagesGrid / Hippodamian Model: Hippodamus of MiletusVriti SachdevaNo ratings yet
- Financial Management Full Notes at Mba FinanceDocument44 pagesFinancial Management Full Notes at Mba FinanceBabasab Patil (Karrisatte)86% (7)