Professional Documents
Culture Documents
Oil
Uploaded by
sushilk28Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Oil
Uploaded by
sushilk28Copyright:
Available Formats
American Journal of Scientific Research
ISSN 1450-223X Issue 46 (2012), pp. 34-42
EuroJournals Publishing, Inc. 2012
http://www.eurojournals.com/ajsr.htm
Crude Oil Supply Chain Risk Management with
Fuzzy Analytic Hierarchy Process
Mohammad Ali Vosooghi
Department of Industrial Management, Faculty of Social Sciences
Imam Khomeini International University, Qazvin, Iran
E-mail: mavosooghi@gmail.com
Safar Fazli
Assistant Professor, Department of Industrial Management
Faculty of Social Sciences, Imam Khomeini International University, Qazvin, Iran
E-mail: Fazli@ikiu.ac.ir
Reza Kiani Mavi
Corresponding Author, Assistant Professor
Department of Industrial Management, Faculty of Management and Accounting
Qazvin Branch, Islamic Azad University (IAU), Qazvin, Iran
E-mail: Rezakianimavi@yahoo.com
Tel: (+98)281 3665275-6
Abstract
Crude oil supply chain is extremely complex and vulnerable to various risks. Clear
understanding of these risks can help supply chain managers to make effective decisions.
This paper identifies main risks related to crude oil supply chain and implements fuzzy
analytic hierarch process (FAHP) for weighing them. The results show that the most
important risk area is the regulatory and environmental risks and that the transference and
cooperation policy is rated as the best response strategy. Contributions of this paper are
two-fold: (1) it provides a comprehensive framework of risks that need to be considered in
crude oil supply chain risk management (SCRM) context; and (2) it illustrates that how
various risks and risk management strategies can be assessed through the FAHP approach
to aid managers in their decision making processes.
Keywords: Supply chain risk management (SCRM); Fuzzy Analytic Hierarchy Process
(FAHP); Crude oil supply chain.
1. Introduction
Crude oil is the worlds main source of energy, consisting more than 10% of worlds trade. More than
160 different crude oil types with different qualities are internationally traded. Different crude oils have
different prices. The significance of oil in the global market is more than its impact on the energy
industry. Because of the global high profile of crude oil trading, and its important role on world
economy crude oil supply chain is subject to a high level of scrutiny. Crude oil supply chain is like the
supply chain of any other industry and supply chain concepts can be implemented to this industry.
Crude Oil Supply Chain Risk Management with Fuzzy Analytic Hierarchy Process 35
Most of the oil industry companies still operate their planning, central engineering, upstream
operations, refining, and supply and transportation groups as complete separate entities. Therefore,
systematic methods for efficiently managing petroleum supply chain as one entity must be exploited
(Shah, Li, and Ierapetritou, 2011).
There is sufficient literature on supply chain risk management (SCRM) acknowledging that
todays supply chains are more vulnerable than ever before, for several reasons: globalization, natural
disasters, wars, terrorist attacks, complexity of supply chains, new business strategies, etc (e.g., Chopra
and Sodhi, 2004; Jttner, 2005; Christopher and Lee, 2004; Jttner, Peck, and Christopher, 2003). Oil
supply chain is not only vulnerable to various risks like other industries but also extremely complex
compared to other industries. While many scholars have studied supply chain risks in different
industries, how to implement these concepts in oil supply chain is still a challenge. In this paper, we
respond to this challenge by comprehensive literature review, experts viewpoints and applying two
decision-making models.
This study aims to provide a comprehensive framework of risks that need to be considered in
crude oil supply chain risk management context. Then it illustrates that how various risks and risk
management strategies can be assessed through the FAHP approach to aid managers in effective
decision making process of SCRM.
Remaining parts of this paper is organized as follows. Section 2 reviews exiting literature on
supply chain risk management and oil supply chain. The methodology is illustrated in Section 3.
Section 4 classifies risk types as criteria and risk management as alternatives. Illustrated methodology
is applied in section 5. In section 6, we make concluding remarks.
2. Literature Review
Literature relevant to this article falls into two main areas: supply chain risk management and oil and
petroleum supply chain. Review of the literature is on these two topics.
2.1. Supply Chain Risk Management
Although SCRM is fairly new research area (Wagner and Bode, 2008) and still in the infancy stage
(Vanany, Zailani, and Pujawan, 2009), there are various helpful studies with different approaches and
methodologies. Here we briefly review the studies that are most relevant to our study.
In todays marketplaces supply chains are more vulnerable and are exposed to many different
forms of risks. This increased vulnerability is due to both external events such as wars and terrorist
attacks and changes in business strategies (internal factors) such as outsourcing and Lean practices.
Supply chain risks can be created through a lack of confidence among supply chain members. There
are two elements of supply chains that can reduce the lack of confidence: visibility and control.
Improved end-to-end visibility is one key element in strategies designed to mitigate supply chain risks
(Christopher and Lee, 2004). In dealing with different mitigating strategies Tang (2006) presents a
comprehensive review of quantitative models for managing supply chain risks. He defines supply chain
risk management as the management of supply chain risks through coordination and collaboration
among the supply chain partners so as to ensure profitability and continuity and analyzes four basic
approaches(supply management, demand management, product management, and information
management) for managing supply chain risks . He also argues that efficiency and resiliency are two
critical factors for firms to ensure profitability and business continuity, which is accordant with the
definition of SCRM.
The study of Manuj and Mentzer (2008) underlines the importance of understanding global
supply chains and indicates that beside the benefits that absorb firms there are uncertainties and risks
that managers face in global supply chains. They investigate and explore phenomenon risk
management and associated strategies. They implement grounded theory in order to address the three
major gaps identified in an initial SCRM literature review: nonexistence of an adequate definition of
36 Mohammad Ali Vosooghi, Safar Fazli and Reza Kiani Mavi
supply chain risk, inability to address the manner of selecting risk management strategy, and limited
research on moderators of risk management. Based on existing literature and in-depth interviews they
develop the definition of global supply chain risk management as: Global supply chain risk
management is the identification and evaluation of risks and consequent losses in the global supply
chain, and implementation of appropriate strategies through a coordinated approach among supply
chain members with the objective of reducing one or more of the following losses, probability, speed
of event, speed of losses, the time for detection of the events, frequency, or exposure for supply chain
outcomes that in turn lead to close matching of actual cost savings and profitability with those
desired.
Tang and Nurmaya Musa (2010) investigate recent literature relevant to SCRM and research
development in SCRM. They investigate major risk issues and risk mitigation techniques based on
material, cash, and information flows. This study indicates that the existing literature includes mainly
descriptive and conceptual models rather than quantitative models. Among 138 surveyed papers, 78%
belong to conceptual and qualitative category.
Blome and Schoenherr (2011) provide a general overview of the current state of SCRM in
business and investigate successful approaches and experiences by companies in dealing with SCRM
in economic and financial crisis, especially as it concerns the supply side. They use case studies among
eight European companies to study about how companies manage their supply risks in financial crises
and how their risk management approaches have shifted. They present an illustrative recent research
conducted in this area in the form of a Table which contains 23 papers and summarizes the main
objectives of the papers, their methodology, focus and perspective. Among these 23 papers, the
perspective of 13 papers is on supply chain and 9 papers on purchasing and the focus of all papers
except one paper is risk and disruption.
Clear understanding of risk types in supply chains can help managers of industries to apply
effective risk-reduction approaches to their own companies. Leading companies like Dell, Toyota, and
Motorola excel at identifying their supply chain risks, and at applying effective mitigation strategies
that neutralize potentially negative effects (Chopra and Sodhi, 2004). In an empirical study Wagner
and Bode (2008) provide a detailed operationalization of supply chain risk construct and examine the
relationship between supply chain risk sources and supply chain performance. They divide risk sources
into five categories.
2.2. Oil Supply Chain
Historical perspective on supply chain management indicates that the seeds of supply chain
management were planted in the early 1980s (Fawcett, 2000) and since early 1990s globalization has
witnessed major developments in supply chain management context (Fernandes, Barbosa-Pvoa, and
Relvas, 2009). Despite the improvements and importance of supply chain management and its growing
complexity, the petroleum industry is still in the development stage of efficiently managing their
supply chains. In fact, the oil and petrochemical industrys insight into the supply chain is still in its
infancy (Hussain, Assavapokee, and Khumawala, 2006).
The oil industry is global in nature and crude oil and its derivatives are transferred between
locations that are remote places. The oil supply chain is extremely complex compared to other
industries (Hussain et al. 2006). Oil supply chain contains various interconnected processes, activities
and components. In attempting to depict oil supply chain, many scholars have proposed different
simulations and descriptions. For example, Carneiro, Ribas, and Hamacher ( 2010) in their study on
strategic planning of an oil supply chain group activities into two main areas: upstream and
downstream. The first segment i.e., upstream involves well prospecting, exploration, drilling and
completion, and oil production. The second segment i.e., downstream involves transportation, refining,
and distribution of crude oil and refined products. Deviding oil supply chain activities into two
segment is a common way(method) used by many scholars and researches but this deviation is not a
uniq one. In other words different scholars mention different activities and terms in their depiction(e.g.
Crude Oil Supply Chain Risk Management with Fuzzy Analytic Hierarchy Process 37
Hussain et al. 2006; Fernandes et al. 2009; Fernandes et al. 2010; Carneiro et al. 2010; Shah et al.
2011).
Cigolini and Rossi (2010) divide oil supply chain into three main stages: drilling, primary
transport and refining. They emphasize on the importance of supply chain risks in oil and petroleum
industry and they indicate that the operational risk in oil supply chain is bullwhipped. Due to this
importance they propose a model to analyze the operational risk at the drilling, primary transport and
refining stage of the oil supply chain. They identify various operational risks which influence different
stages and recommend different risk management processes for each stage.
The study of Fernandes et al. (2010) provides a quantitative approach concerning the process of
risk analysis and assessment in petroleum supply chain. In order to identify the risks, this paper uses a
framework which hierarchically relate first the risk agents, second the risk sources, the risk objects and
finally the risk events and then it follows the risk mitigation process to complete the risk information.
The study of Carneiro et al. (2010) also applies a quantitave approach the goal of this study is to
include financial risk management in the integrated oil supply chain planning under uncertainty.
Despite the rich body of literature concerning SCRM in different industries, oil supply chain
risk issues have been studied less. This paper aims to present a comprehensive SCRM framework in oil
supply chain.
3. Methodology
In this section, FAHP method is illustrated. The procedures that are used in the methods are described
as follows.
3.1. Extent Analysis Method on Fuzzy AHP
The outlines of the extent analysis method on fuzzy AHP can be summarized as follows:
Let X = {x
1
, x
2
, . . . , x
n
} be an object set, and U = {u
1
, u
2
, . . . , u
m
} be a goal set. According to
the Changs extent analysis method, each object is taken and extent analysis for each goal g
i
is
performed, respectively. Therefore, m extent analysis values for each object can be obtained and shown
as follows:
1 2
, , , , 1, 2, . (1) =
m
gi gi gi
M M M i n (1)
Where all the
j
gi
M (j = 1; 2, . . . ,m) are triangular fuzzy numbers (TFNs) whose parameters are
l, m and u. They are the least possible value, the most possible value, and the largest possible value
respectively. A TFN is represented as (l,m,u). The steps of the extent analysis method can be given as
follows:
Step 1. The value of fuzzy synthetic extent with respect to its object is defined as:
1
1 1 1
m
j
= = =
(
=
(
n m
j j
i gi gi
i j
S M M (2)
To obtain
1
m
j =
j
gi
M perform the fuzzy addition operation of m extent analysis values for a
particular matrix
Such that:
1 1 1 1
, , (3)
= = = =
| |
=
|
|
\
m m m m
j
gi j j j
j j j j
M l m u (3)
and to obtain
1
1 1
= =
(
(
n m
j
gi
i j
M , perform the fuzzy edition operation of m extent analysis values
for a particular matrix such that:
38 Mohammad Ali Vosooghi, Safar Fazli and Reza Kiani Mavi
1 1 1 1 1
, , (4)
= = = = =
| |
=
|
|
\
n m m m m
j
gi i i i
i j j j j
M l m u (4)
Then, the inverse of the vector in equation (5) is computed as:
1
1 1
1 1 1
1 1 1
, ,
= =
= = =
| |
( |
=
|
\
n n
j
gi n n n
i j
i i i
i i i
M
u m l
(5)
Step 2. The degree of possibility of M
2
= (l
2
, m
2
, u
2
) M
1
= (l
1
, m
1
, u
1
) is defined as:
( ) ( ) ( )
2 1 1 2
[ ( , )]
M M
V M M Sup Min x y = (6)
this can be expressed equivalently as follows:
( ) ( )
2
2 1
2 1 2 1 1 2
1 2
2 2 1 1
1
( ) ( ) ( ) 0 (7)
if
V hgt d if
M
otherwise
m m
l u M M M M
l u
m u m l
= = =
(7)
where d is the ordinate of the highest intersection point D between
M1
and
M2
(see Figure. 1). To
compare M
1
and M
2
, both the values of V(M
1
M
2
) and V(M
2
M
1
) are needed.
Step 3. The degree possibility for a convex fuzzy number to be greater than k convex fuzzy
numbers Mi (i = 1, 2, . . . , k) can be defined by:
V (M M
1
, M
2
, . . . ,M
k
) = V[ (M M
1
) and (M M
2
) and . . . and (M M
k
) ] = min
V(M M
i
) , i = 1 , 2, . . . ,k . (8)
Assume That :
d (S
i
) = min V (S
i
S
k
) (9)
Figure 1: The intersection between M1 and M2
For k = 1, 2, . . . , n; k i. Then the weight vector is given by:
W = d (S
1
), d (S
2
), . . . , d (S
n
))
T
(10)
where S
i
(i = 1, 2, . . . , n) are n elements.
Step 4. After normalization (the elements of each column is divided by the sum of that column
and the elements in each resulting row are added and this sum is divided by the number of elements in
the row), the normalized weight vectors are obtained as follows:
W = (d(S
1
), d(S
2
), . . . , d(S
n
))
T
Where W is not a fuzzy number.
Crude Oil Supply Chain Risk Management with Fuzzy Analytic Hierarchy Process 39
In fuzzy-AHP, firstly, the criteria and alternatives importance weights must be compared. For
this reason, there must be linguistic terms and their equivalent fuzzy numbers denoting comparison
measures. Afterwards, for the first step, the comparisons about the criteria and alternatives, and the
weight calculation need to be made. Thus, the evaluation of the criteria according to the main goal and
the evaluation of the alternatives for these criteria must be realized. Then, after all these evaluation
procedure, the weights of the alternatives can be calculated (Gumus, 2009).
4. Criteria of Decision Making
In the following we define five risk sources, a, b, c, d, and e as our decision making criteria. For doing
so we apply the taxonomy of Wagner and Bode, (2008) and then by using experts viewpoints and
reviewing existing literature define risk types for each risk source as sub-criteria. Then we explain risk
management strategies.
1. Criteria
a) Demand side risks: These risks are based on downstream supply chain activities (Svensson,
2002). In other words demand side risks results from disruptions emerging from downstream
operations supply chain (Jttner, Supply Chain Risk Management - Understanding the
Business Requirements From a Practitioner Perspective, 2005).
b) Supply side risks: companies are exposed to various risks associated with the upstream side of
their supply chains. These risks reside in purchasing, suppliers, supplier relationships, and
supply networks (Wagner and Bode, 2008).
c) Regulatory risks: This category refers to the legal enforceability and execution of supply
chain-relevant laws and policies as well as the degree and frequency of changes in these laws
and policies (Wagner and Bode, 2008).
d) Infrastructure risks: This category of risk involves disruptions that materialize from the
infrastructure that a firm maintains for its supply chain operations (Wagner and Bode, 2008).
Among the risks reported in Marsh national oil company conference 2007, one of them is
upgrading systems and structures, such that they continue to meet required technical
standards and existing proposed usage requirements.
e) Catastrophic: This category involves pervasive events that, when they occur, have a severe
impact on the area of their occurrence (Wagner and Bode, 2008).
The hierarchy of the SCRM is as figure 2.
Figure 2:The hierarchy of the SCRM
5. Applying the Illustrated Method
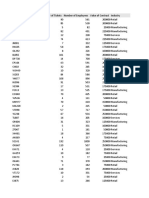
The aggregated comparison matrix for supply chain risk management can be seen from Table 1.
SCRM
Infrastructure
risks
Regulatory
risks
Supply side
risks
Demand side
risks
Catastrophic
40 Mohammad Ali Vosooghi, Safar Fazli and Reza Kiani Mavi
Table 1: Inter-criteria comparison matrix
C1 C2 C3 C4 C5
C1 (1,1,1) (1,3,5) (3/2,2,5/2) (2/5,1,2/3) (3/2,2,5/2)
C2 (1/5,1/3,1) (1,1,1) (1,3,5) (1/5,1/3,1) (1,3,5)
C3 (2/5,1,2/3) (1/5,1/3,1) (1,1,1) (1/6,1/4,1/2) (1,1,3)
C4 (3/2,2,5/2) (1,3,5) (2,4,6) (1,1,1) (3,5,7)
C5 (2/5,1,2/3) (1/5,1/3,1) (1/3,1,1) (1/7,1/5,1/3) (1,1,1)
First we calculate
1
m
j
gi
j
M
=
values for each row of the matrix:
C
1
: (1+1+3/2+2/5+3/2, 1+3+2+1+2, 1+5+5/2+2/3+5/2) = (5.4, 9, 11.67)
C
2
: (1/5+1+1+1/5+1, 1/3+1+3+1/3+3, 1+1+5+1+5) = (3.4, 7.64, 13)
C
3
: (2/5+1/5+1+1/6+1, 1+1/3+1+1/4+1, 2/3+1+1+1/2+3) = (2.77, 3.58, 6.17)
C
4
: (3/2+1+2+1+3, 2+3+4+1+5, 5/2+5+6+1+7) = (8.5, 15, 21.5)
C
5
: (2/5+1/5+1/3+1/7+1, 1+1/3+1+1/5+1, 2/3+1+1+1/3+1) = (2.076, 3.33, 4)
The
1 1
n m
j
gi
i j
M
= =
value is calculated as:
(1+1+3/2+2/5+3/2+1/5+1+1+1/5+1+2/5+1/5+1+1/6+1+3/2+1+2+1+3+2/5+1/5+1/3+1/7+1,
1+3+2+1+2+1/3+1+3+1/3+3+1+1/3+1+1/4+1+2+3+4+1+5+1+1/3+1+1/5+1,
1+5+5/2+2/3+5/2+1+1+5+1+5+2/3+1+1+1/2+3+5/2+5+6+1+7+2/3+1+1+1/3+1) = (22.14,
38.78, 56.34)
Then we can calculate the
1
n m
j
gi
i 1 j 1
M
= =
(
(
value:
1
n m
j
gi
i 1 j 1
1 1 1
M , , (0.0177, 0.0258, 0.0452)
56.34 38.78 22.14
= =
(
| |
= =
( |
\
S
i
values for each column of reciprocal matrix are calculated as:
S
1
= (5.4, 9, 11.67) (0.0177, 0.0258, 0.0452) = (0.0956, 0.2322, 0.5275)
S
2
= (3.4, 7.64, 13) (0.0177, 0.0258, 0.0452) = (0.0602, 0.1979, 0.5876)
S
3
= (2.77, 3.58, 6.17) (0.0177, 0.0258, 0.0452) = (0.049, 0.0924, 0.2789)
S
4
= (8.5, 15, 21.5) (0.0177, 0.0258, 0.0452) = (0.1505, 0.387, 0.9718)
S
5
= (2.076, 3.33, 4) (0.0177, 0.0258, 0.0452) = (0.0366, 0.0911, 0.1808)
Then the V values are calculated by using these vectors:
V (S
1
S
2
) = 1 V (S
1
S
3
) = 1 V (S
1
S
4
) =
( )
0.1505 0.5275
0.7089
0.2322 0.5257 (0.387 0.1505)
=
V (S
1
S
5
) = 1
V (S
2
S
1
) = 0.9348 V (S
2
S
3
) = 1 V (S
2
S
4
) = 0.69 V (S
2
S
5
) = 1
V (S
3
S
1
) =0.5673 V (S
3
S
2
) =0.6746 V (S
3
S
4
) =0.3035 V (S
3
S
5
) =1
V (S
4
S
1
) =1 V (S
4
S
2
) = 1 V (S
4
S
3
) = 1 V (S
4
S
5
) = 1
V (S
5
S
1
) =0.3756 V (S
5
S
2
) =0.5303 V (S
5
S
3
) =0.9902 V (S
5
S
4
) =0.0929
Table 2: V values result table
Criteria
1 2 3 4 5
Column Row 0.9348 0.5673 1 0.3756
Column Row 1 0.6746 1 0.5303
Column Row 1 1 1 0.9902
Column Row 0.7089 0.69 0.3035 0.0929
Column Row 1 1 1 1
Crude Oil Supply Chain Risk Management with Fuzzy Analytic Hierarchy Process 41
Final weights (W) and normalized weights (w) are shown in Table 3.
Table 3: Weight of Criteria
W W
C1 0.7089 0.2536
C2 0.69 0.2468
C3 0.3035 0.1086
C4 1 0.3577
C5 0.0929 0.0332
The weights of the five risk categories (C 1, C 2, C 3, C 4, C 5) for improving the decision of
crude oil SCRM are available in Table 3, which are 0.2356, 0.2468, 0.1086, 0.3577, and 0.0332,
respectively. They imply that the fourth criterion i.e., regulatory and environmental risk is the most
important and the fifth i.e., catastrophic risk is the least important
6. Conclusion
In the risky global market which is highly dependent on crude oil, risk management is a critical
problem for a crude oil supply chain. Despite this high dependency and the importance of the subject in
global economy, the existing literature has paid less attention to apply SCRM in oil industry in
comparison with other industries like automobile. This paper suggests that framing a risk structure of
crude oil supply chain and applying FAHP model can aid managers on risk management decisions.
The main risks related to crude oil supply chain were singled out from the literature and argued
with the experts. We applied ANP approach to rank the risks. The results presented that most important
risk area is the regulatory and environmental risks and within this area the most important risk is
government risk and the second important is international actions risk.
References
[1] Blome, C., & Schoenherr, T. (2011). Supply chain risk management in financial crisesA
multiple case-study approach. International Journal of Production Economics ,
doi:10.1016/j.ijpe.2011.01.002.
[2] Carneiro, M. C., Ribas, G. P., & Hamacher, S. (2010). Risk Management in the Oil Supply
Chain: A CVaR Approach. Ind. Eng. Chem. Res. , 32863294.
[3] Chopra, S., & Sodhi, M. S. (2004). Managing risk to avoid supply-chain breakdown. MIT
Sloan Management Review , 53-61.
[4] Christopher, M., & Lee, H. L. (2004). Mitigating Supply Chain Risk Through Improved
Confidence. International Journal of Physical Distribution & Logistics Management , 388396.
[5] Cigolini, R., & Rossi, T. (2010). Managing operational risks along the oil supply chain.
Production Planning & Control , 452467.
[6] Fawcett, S. E. (2000). SUPPLY CHAIN MANAGEMENT: COMPETING THROUGH
INTEGRATION . In P. M. Swamidass(ed.), ENCYCLOPEDIA OF PRODUCTION AND
MANUFACTURING MANAGEMENT (pp. 755-760). Boston/Dordrecht/London: Kluwer
Academic Publishers.
[7] Fernandes, L. J., Barbosa-Pvoa, A. P., & Relvas, S. (2009). Risk Management in Petroleum
Supply Chain. 14 Congresso da APDIO, (pp. 157-164).
[8] Gumus AT (2009) Evaluation of hazardous waste transportation firms by using a two step
fuzzy AHP and TOPSIS methodology. Expert Systems with Applications. 36: 40674074.
42 Mohammad Ali Vosooghi, Safar Fazli and Reza Kiani Mavi
[9] Hussain, R., Assavapokee, T., & Khumawala, B. (2006). Supply Chain Management in the
Petroleum Industry:Challenges and Opportunities. International Journal of Global Logistics &
Supply Chain Management , 90 97.
[10] Jttner, U. (2005). Supply Chain Risk Management - Understanding the Business Requirements
From a Practitioner Perspective. The International Journal of Logis tics Management , 120-141.
[11] Jttner, U., Peck, H., & Christopher, M. (2003). SUPPLY CHAIN RISK
MANAGEMENT:OUTLINING AN AGENDA FOR FUTURE RESEARCH. International
Journal of Logistics : Research & Applications , 6 (4), 197-210.
[12] Manuj, I., & Mentzer, J. T. (2008). Global supply chain risk management strategies.
International Journal of Physical Distribution & Logistics Management , 192-223.
[13] Shah, N. K., Li, Z., & Ierapetritou, M. G. (2011). Petroleum Refining Operations: Key Issues,
Advances, and Opportunities. Ind. Eng. Chem. Res. , 11611170.
[14] Tang, C. S. (2006). Perspectives in supply chain risk management. International Journal of
Production Economics , 451488.
[15] Vanany, I., Zailani, S., & Pujawan, N. (2009). Supply Chain Risk Management:Literature
Review and Future Research. Internationa Journal of Information Systems and Supply Chain
Management , 16-33.
[16] Wagner, S. M., & Bode, C. (2008). AN EMPIRICAL EXAMINATION OF SUPPLY CHAIN
PERFORMANCE ALONG SEVERAL DIMENSIONS OF RISK. JOURNAL OF BUSINESS
LOGISTICS , 307-325.
[17] Wagner, S. M., & Bode, C. (2006 ). An empirical investigation into supply chain vulnerability.
Journal of Purchasing & Supply Management , 301312.
You might also like
- Third Party Contracts Flyerl Lo Res Screen 01 PDFDocument8 pagesThird Party Contracts Flyerl Lo Res Screen 01 PDFsushilk28No ratings yet
- DEVINE FORGIVENESSDocument2 pagesDEVINE FORGIVENESSsushilk28100% (1)
- 9c9605181821ce223e PDFDocument17 pages9c9605181821ce223e PDFsushilk28No ratings yet
- Acrendon PDFDocument6 pagesAcrendon PDFsushilk28No ratings yet
- Causes of Contractor FailuresDocument3 pagesCauses of Contractor FailuresPradeep GsNo ratings yet
- 2 Stakerholder Brochure PDFDocument37 pages2 Stakerholder Brochure PDFsushilk28No ratings yet
- Willis Energy Market Review 2013 PDFDocument92 pagesWillis Energy Market Review 2013 PDFsushilk28No ratings yet
- Business Resilience Guide PDFDocument16 pagesBusiness Resilience Guide PDFsushilk28No ratings yet
- 04 - Contract Management - Areva PDFDocument27 pages04 - Contract Management - Areva PDFsushilk28No ratings yet
- Creating Resilient Supply Chains - A Practical GuideDocument100 pagesCreating Resilient Supply Chains - A Practical GuidePeter KlymNo ratings yet
- CMB Info PDFDocument7 pagesCMB Info PDFsushilk28No ratings yet
- Acrendon PDFDocument6 pagesAcrendon PDFsushilk28No ratings yet
- 49 10 PDFDocument19 pages49 10 PDFsushilk28No ratings yet
- Creating Resilient Supply Chains - A Practical GuideDocument100 pagesCreating Resilient Supply Chains - A Practical GuidePeter KlymNo ratings yet
- JCT2005Document272 pagesJCT2005SFeganUK100% (2)
- Building a Business Case for Procure-to-Pay AutomationDocument9 pagesBuilding a Business Case for Procure-to-Pay Automationsushilk28No ratings yet
- WWW - Tantrik-Astrologer - In: DR - Rupnathji (DR - Rupak Nath)Document4 pagesWWW - Tantrik-Astrologer - In: DR - Rupnathji (DR - Rupak Nath)sushilk28No ratings yet
- 3580 PDFDocument2 pages3580 PDFsushilk28No ratings yet
- WP Procurement Finance Collaboration RN PDFDocument14 pagesWP Procurement Finance Collaboration RN PDFsushilk28No ratings yet
- Example Risks and Risk TreatmentsDocument10 pagesExample Risks and Risk Treatmentssushilk28No ratings yet
- 6336 Brochure PDFDocument18 pages6336 Brochure PDFsushilk28No ratings yet
- 2011 Strategies September Issue PDFDocument28 pages2011 Strategies September Issue PDFsushilk28No ratings yet
- Ifpsm - Ya Ling Tsai PDFDocument21 pagesIfpsm - Ya Ling Tsai PDFsushilk28No ratings yet
- Chapter 3 Reading Material1 PDFDocument33 pagesChapter 3 Reading Material1 PDFsushilk28No ratings yet
- 3so SS PP PDFDocument49 pages3so SS PP PDFsushilk28No ratings yet
- Updated-2010 Civil KPIs PDFDocument12 pagesUpdated-2010 Civil KPIs PDFsushilk28No ratings yet
- Guidelines TalksDocument5 pagesGuidelines Talkssushilk28No ratings yet
- 250driving High Performance For Accenture Through Procurement Outsourcing PDFDocument12 pages250driving High Performance For Accenture Through Procurement Outsourcing PDFsushilk28No ratings yet
- AA Seminar 08 Presentation-PS 6 HandoutsDocument27 pagesAA Seminar 08 Presentation-PS 6 Handoutssushilk28No ratings yet
- 4 Theoretical Frames PDFDocument14 pages4 Theoretical Frames PDFsushilk28No ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Indian Institute of Materials Management: Course - GDMMDocument2 pagesIndian Institute of Materials Management: Course - GDMMShinjini Bag50% (2)
- Mysapplm Page 1Document23 pagesMysapplm Page 1Baalu KathirveluNo ratings yet
- Dubois Gadde 2000Document9 pagesDubois Gadde 2000Radu PanaitescuNo ratings yet
- Retailing in Electronic Commerce: Products and ServicesDocument11 pagesRetailing in Electronic Commerce: Products and ServicessynwithgNo ratings yet
- SAP APO Analyst SCM in Houston TX Resume Fauziah EmbiDocument3 pagesSAP APO Analyst SCM in Houston TX Resume Fauziah EmbiFauziahEmbiNo ratings yet
- Distribution ChannelsDocument15 pagesDistribution ChannelsZybel RosalesNo ratings yet
- Ewm Configuration GuideDocument322 pagesEwm Configuration GuideSUBHOJIT BANERJEE100% (13)
- Business Strategy Project: Submitted By: Abhishek Kulshrestha Suhas P CDocument37 pagesBusiness Strategy Project: Submitted By: Abhishek Kulshrestha Suhas P CsagarNo ratings yet
- Vendor Managed Inventory by Group 5Document13 pagesVendor Managed Inventory by Group 5Yadvendra ShekhawatNo ratings yet
- Logistics & Supply Chain Management:: Transportation Strategies For LCD TelevisionsDocument29 pagesLogistics & Supply Chain Management:: Transportation Strategies For LCD TelevisionsApurva SrivastavaNo ratings yet
- SCN-An Insight - SAP Toll ManufacturingDocument10 pagesSCN-An Insight - SAP Toll ManufacturingRavibabu Koduri67% (3)
- SCRC Article Library: CPFR Model: Collaborative Planning, Forecasting and Replenishment (CPFR) : A TutorialDocument2 pagesSCRC Article Library: CPFR Model: Collaborative Planning, Forecasting and Replenishment (CPFR) : A TutorialNikhilNo ratings yet
- Minda Rinder Mro & Vmi PPT Jun'19Document7 pagesMinda Rinder Mro & Vmi PPT Jun'19Digital SolutionsNo ratings yet
- Depiction of Total Quality Management During A Span of 2003-2013Document6 pagesDepiction of Total Quality Management During A Span of 2003-2013Marvin I. NoronaNo ratings yet
- Bill of LadingDocument1 pageBill of LadingboyNo ratings yet
- Goods movement and consumption transactionsDocument7 pagesGoods movement and consumption transactionssaurabhudr_grinfraNo ratings yet
- TPM Hand Book for Total Productive Maintenance ImplementationDocument30 pagesTPM Hand Book for Total Productive Maintenance ImplementationbayoepoetroNo ratings yet
- 2018 Jadwal Training PM IsDocument1 page2018 Jadwal Training PM IsDarussalam MuhammadNo ratings yet
- Linear Example DataDocument7 pagesLinear Example DataSanjay S RayNo ratings yet
- NFL Report FinalDocument26 pagesNFL Report FinalShamsher ShirazNo ratings yet
- Iteb G621 256Document2 pagesIteb G621 256saket reddyNo ratings yet
- Principles of Supply Chain Management 1652390545Document264 pagesPrinciples of Supply Chain Management 1652390545E ShamrockNo ratings yet
- KAIZEN PAPER KALDI Final PaperDocument34 pagesKAIZEN PAPER KALDI Final PaperClaire ZafraNo ratings yet
- A Case Study On Toyota's Jit RevolutionDocument8 pagesA Case Study On Toyota's Jit Revolutionmmjmmj100% (5)
- Wollo University: Lennox Wholesaler Group (Document16 pagesWollo University: Lennox Wholesaler Group (malede gashawNo ratings yet
- Career Objective:: Lokesh BabuDocument3 pagesCareer Objective:: Lokesh BabuLokesh ModemzNo ratings yet
- Topic 17Document50 pagesTopic 17C.S.ABHILASHNo ratings yet
- Apparel Merchandising - 2017 PDFDocument397 pagesApparel Merchandising - 2017 PDFalexandraherepean83% (18)
- Nestle: Good Food Good LifeDocument11 pagesNestle: Good Food Good LifeMudit SahaiNo ratings yet
- 104 PGP SCM End TermDocument4 pages104 PGP SCM End Termsanchit gargNo ratings yet