Professional Documents
Culture Documents
Chapter 12
Uploaded by
Ayrton WidiutomoOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Chapter 12
Uploaded by
Ayrton WidiutomoCopyright:
Available Formats
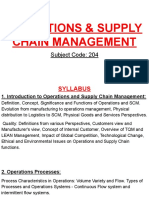
Information Security Maintenance
Module 12 Chapter 12
Based on the Fourth Edition of: M. E. Whitman, H. J. Mattord:. Principles of Information Security
School of Business, Department of Information Technology
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
The only thing we can predict with certainty is change. Jayne Spain, Department of Children and Family Learning, State of Minnesota
Module 12 Chapter 12
Information Security Maintenance
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Learning Objectives
Discuss the need for ongoing maintenance of the information security program List the recommended security management models, and dene a model for a full maintenance program Identify the key factors involved in monitoring the external and internal environment, and describe how planning into information security maintenance Dene digital forensics, and describe the management of the digital forensics function Describe the process of acquiring, analyzing, and maintaining potential evidentiary material
Module 12 Chapter 12 Information Security Maintenance 3
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Outline
Introduction Security Management Models The Security Maintenance Model Digital Forensics
Module 12 Chapter 12
Information Security Maintenance
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Introduction
Organizations should avoid overcondence after improving their information security prole Organizational changes that may occur include:
Acquisition of new assets; emergence of new vulnerabilities; business priorities shift; partnerships form or dissolve; organizational divestiture and acquisition; employee hire and turnover
If program does not adjust, may be necessary to begin cycle again More expensive to re-engineer information security prole again and again
Module 12 Chapter 12
Information Security Maintenance
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Security Management Models
Management model must be adopted to manage and operate ongoing security program Models are frameworks that structure tasks of managing particular set of activities or business functions
Module 12 Chapter 12
Information Security Maintenance
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Provides managerial guidance for establishing and implementing of an information security program Thirteen areas of information security management
Provide for specic monitoring activities for each task Tasks should be done on an ongoing basis Not all issues are negative
Module 12 Chapter 12
Information Security Maintenance
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
1. Information security governance Agencies should monitor the status of their programs to ensure that:
Ongoing information security activities provide support to agency mission Current policies and procedures are technology-aligned Controls are accomplishing the intended purpose
2.
System development life cycle: The overall process of developing, implementing, and retiring information systems through a multi-step process
Module 12 Chapter 12
Information Security Maintenance
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
3. Awareness and training Tracking system should capture key information on program activities Tracking compliance involves assessing the status of the program The program must continue to evolve 4. Capital planning and investment control Designed to facilitate and control the expenditure of agency funds Select-control-evaluate investment life cycle
Module 12 Chapter 12 Information Security Maintenance 9
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Figure 12-1 Select-Control-Evaluate Investment Life Cycle
Module 12 Chapter 12 Information Security Maintenance 10
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
5. Interconnecting systems The direct connection of two or more information systems for sharing data and other information resources Can expose the participating organizations to risk When properly managed, the added benets include greater eciency, centralized access to data, and greater functionality 6. Performance measures Metrics: tools that support decision making Six phase iterative process
Module 12 Chapter 12
Information Security Maintenance
11
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Figure 12-3 Information Security Metrics Development Process
Module 12 Chapter 12 Information Security Maintenance 12
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
7. Security planning: one of the most crucial ongoing responsibilities in security management 8. Information technology contingency planning: consists of a process for recovery and documentation of procedures 9. Risk management Ongoing eort Tasks include performing risk identication, analysis, and management
Module 12 Chapter 12 Information Security Maintenance 13
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Figure 12-4 Information Security Metrics Program Implementation Process
Module 12 Chapter 12 Information Security Maintenance 14
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Figure 12-5 The NIST Seven-Step Contingency Planning Process
Module 12 Chapter 12 Information Security Maintenance 15
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Figure 12-6 Risk Management in the System Security Life Cycle
Module 12 Chapter 12 Information Security Maintenance 16
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
10. Certication, accreditation, and security assessments An essential component in any security program The status of security controls is checked regularly Auditing: the process of reviewing the use of a system for misuse or malfeasance 11. 12. Security services and products acquisition Incident response: incident response life cycle
13. Conguration (or change) management: manages the eects of changes in congurations
Module 12 Chapter 12
Information Security Maintenance
17
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Figure 12-7 The Information Security Services Life Cycle
Module 12 Chapter 12 Information Security Maintenance 18
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
NIST SP 800-100 IS Handbook: A Guide for Managers
Figure 12-8 The Incident Response Life Cycle
Module 12 Chapter 12
Information Security Maintenance
19
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: If an organization deals successfully with change and has created procedures and systems that can be adjusted to the environment, the existing security improvement program can continue to work well. Answer:
Module 12 Chapter 12
Information Security Maintenance
20
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: If an organization deals successfully with change and has created procedures and systems that can be adjusted to the environment, the existing security improvement program can continue to work well. Answer: True
Module 12 Chapter 12
Information Security Maintenance
20
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: If an organization deals successfully with change and has created procedures and systems that can be adjusted to the environment, the existing security improvement program can continue to work well. Answer: True An eective information security governance program requires review. Answer:
Module 12 Chapter 12
Information Security Maintenance
20
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: If an organization deals successfully with change and has created procedures and systems that can be adjusted to the environment, the existing security improvement program can continue to work well. Answer: True An eective information security governance program requires review. Answer: constant
Module 12 Chapter 12
Information Security Maintenance
20
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: If an organization deals successfully with change and has created procedures and systems that can be adjusted to the environment, the existing security improvement program can continue to work well. Answer: True An eective information security governance program requires review. Answer: constant An is dened as the direct connection of two or more information systems for sharing data and other information resources. Answer:
Information Security Maintenance 20
Module 12 Chapter 12
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: If an organization deals successfully with change and has created procedures and systems that can be adjusted to the environment, the existing security improvement program can continue to work well. Answer: True An eective information security governance program requires review. Answer: constant An is dened as the direct connection of two or more information systems for sharing data and other information resources. Answer: system interconnection
Information Security Maintenance 20
Module 12 Chapter 12
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer:
Module 12 Chapter 12
Information Security Maintenance
21
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer: Contingency
Module 12 Chapter 12
Information Security Maintenance
21
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer: Contingency True or False: Information security technical controls are not aected by the same factors as most computer-based technologies. Answer:
Module 12 Chapter 12
Information Security Maintenance
21
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer: Contingency True or False: Information security technical controls are not aected by the same factors as most computer-based technologies. Answer: False
Module 12 Chapter 12
Information Security Maintenance
21
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer: Contingency True or False: Information security technical controls are not aected by the same factors as most computer-based technologies. Answer: False True or False: The rst clue that an attack is underway often comes from reports by observant users. Answer:
Module 12 Chapter 12
Information Security Maintenance
21
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer: Contingency True or False: Information security technical controls are not aected by the same factors as most computer-based technologies. Answer: False True or False: The rst clue that an attack is underway often comes from reports by observant users. Answer: True
Module 12 Chapter 12
Information Security Maintenance
21
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer: Contingency True or False: Information security technical controls are not aected by the same factors as most computer-based technologies. Answer: False True or False: The rst clue that an attack is underway often comes from reports by observant users. Answer: True Reparing known vulnerabilities in any of the network or system environments is known as . Answer:
Information Security Maintenance 21
Module 12 Chapter 12
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
4
planning consists of a process for recovery and documentation of procedures for conducting recovery Answer: Contingency True or False: Information security technical controls are not aected by the same factors as most computer-based technologies. Answer: False True or False: The rst clue that an attack is underway often comes from reports by observant users. Answer: True Reparing known vulnerabilities in any of the network or system environments is known as . Answer: patching
Information Security Maintenance 21
Module 12 Chapter 12
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
The Maintenance Model
Designed to focus organizational eort on maintaining systems. Recommended maintenance model based on ve subject areas:
1 2 3 4 5
External monitoring Internal monitoring Planning and risk assessment Vulnerability assessment and remediation Readiness and review
Module 12 Chapter 12
Information Security Maintenance
22
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
The Security Maintenance Model(cont.)
Figure 12-10 The Maintenance Model
Module 12 Chapter 12 Information Security Maintenance 23
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the External Environment
Objective to provide early awareness of new threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective defense Entails collecting intelligence from data sources and giving that intelligence context and meaning for use by organizational decision makers
Module 12 Chapter 12
Information Security Maintenance
24
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the external Environment (cont.)
Figure 12-11 External Monitoring
Module 12 Chapter 12 Information Security Maintenance 25
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the external Environment (cont.)
Data Sources Acquiring threat and vulnerability data is not dicult Turning data into information decision makers can use is the challenge External intelligence comes from three classes of sources:
1 2 3
vendors computer emergency response teams (CERTs) public network sources
Regardless of where or how external monitoring data is collected, must be analyzed in context of organizations security environment to be useful
Module 12 Chapter 12 Information Security Maintenance 26
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the external Environment (cont.)
Monitoring, Escalation, and Incident Response Function of external monitoring process is to monitor activity, report results, and escalate warnings Monitoring process has three primary deliverables:
1
Specic warning bulletins issued when developing threats and specic attacks pose measurable risk to organization Periodic summaries of external information. Detailed intelligence on highest risk warnings.
2 3
Module 12 Chapter 12
Information Security Maintenance
27
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the external Environment (cont.)
Data Collection and Management Over time, external monitoring processes should capture knowledge about external environment in appropriate formats External monitoring collects raw intelligence, lters for relevance, assigns a relative risk impact, and communicates to decision makers in time to make a dierence
Module 12 Chapter 12
Information Security Maintenance
28
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the external Environment (cont.)
Figure 12-12 Data Flow Diagrams for External Data Collection
Module 12 Chapter 12 Information Security Maintenance 29
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the Internal Environment
Maintain informed awareness of state of organizations networks, systems, and security defenses Internal monitoring accomplished by:
Doing inventory of network devices and channels, IT infrastructure and applications, and information security infrastructure elements Leading the IT governance process Real-time monitoring of IT activity Monitoring the internal state of the organizations networks and systems
Module 12 Chapter 12
Information Security Maintenance
30
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the Internal Environment (cont.)
Figure 12-13 Internal Monitoring
Module 12 Chapter 12 Information Security Maintenance 31
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the Internal Environment (cont.)
Network Characterization and Inventory Organizations should have carefully planned and fully populated inventory for network devices, communication channels, and computing devices Once characteristics identied, they must be carefully organized and stored using a mechanism (manual or automated) that allows timely retrieval and rapid integration of disparate facts
Module 12 Chapter 12
Information Security Maintenance
32
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the Internal Environment (cont.)
Making Intrusion Detection and Prevention Systems Work The most important value of raw intelligence provided by intrusion detection systems (IDS) is providing indicators of current or imminent vulnerabilities Log les from IDS engines can be mined for information Another IDS monitoring element is trac analysis Analyzing attack signatures for unsuccessful system attacks can identify weaknesses in various security eorts
Module 12 Chapter 12
Information Security Maintenance
33
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Monitoring the Internal Environment (cont.)
Detecting deferences Dierence analysis: procedure that compares current state of network segment against known previous state of same segment Dierences between the current state and the baseline state that are unexpected could be a sign of trouble and need investigation
Module 12 Chapter 12
Information Security Maintenance
34
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Planning and Risk assessment
Primary objective is to keep lookout over entire IS program Accomplished by identifying and planning ongoing information security activities that further reduce risk Primary objectives:
Establishing a formal information security program review Instituting formal project identication, selection, planning, and management processes Coordinating with IT project teams to introduce risk assessment and review for all IT projects. Integrating a mindset of risk assessment across organization
Module 12 Chapter 12
Information Security Maintenance
35
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Planning and Risk assessment (cont.)
Figure 12-14 Planning and Risk Assessment
Module 12 Chapter 12 Information Security Maintenance 36
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Planning and Risk assessment (cont.)
Information security Program Planning and Review Periodic review of ongoing IS program coupled with planning for enhancements and extensions is recommended Should examine IT needs of future organization and impact those needs have on information security recommended approach takes advantage of the fact most organizations have annual capital budget planning cycles and manage security projects as part of that process
Module 12 Chapter 12
Information Security Maintenance
37
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Planning and Risk assessment (cont.)
Large projects should be broken into smaller projects for several reasons:
Smaller projects tend to have more manageable impacts on networks and users Larger projects tend to complicate change control process in implementation phase Shorter planning, development, and implementation schedules reduce uncertainty Most large projects can easily be broken down into smaller projects, giving more opportunities to change direction and gain exibility.
Module 12 Chapter 12
Information Security Maintenance
38
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Planning and Risk assessment (cont.)
Risk Security Assessments A key component for driving security program change is information security operational risk assessment (RA) RA identies and documents risk that project, process, or action introduces to organization and oers suggestions for controls Information security group coordinates preparation of many types of RA documents
Module 12 Chapter 12
Information Security Maintenance
39
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
The objective of the is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer:
Module 12 Chapter 12
Information Security Maintenance
40
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
The objective of the is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: external monitoring domain
Module 12 Chapter 12
Information Security Maintenance
40
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
The objective of the is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: external monitoring domain The primary goal of the is to maintain an informed awareness of the state of all of the organizations networks, information systems, and information security defenses. Answer:
Module 12 Chapter 12
Information Security Maintenance
40
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
The objective of the is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: external monitoring domain The primary goal of the is to maintain an informed awareness of the state of all of the organizations networks, information systems, and information security defenses. Answer: internal monitoring domain
Module 12 Chapter 12
Information Security Maintenance
40
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
The objective of the is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: external monitoring domain The primary goal of the is to maintain an informed awareness of the state of all of the organizations networks, information systems, and information security defenses. Answer: internal monitoring domain The primary objective of the is to keep a lookout over the entire information security program. Answer:
Information Security Maintenance 40
Module 12 Chapter 12
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
The objective of the is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: external monitoring domain The primary goal of the is to maintain an informed awareness of the state of all of the organizations networks, information systems, and information security defenses. Answer: internal monitoring domain The primary objective of the is to keep a lookout over the entire information security program. Answer: planning and risk assessment domain
Information Security Maintenance 40
Module 12 Chapter 12
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation
Primary goal: identication of specic, documented vulnerabilities and their timely remediation Accomplished by:
blue Using vulnerability assessment procedures Documenting background information and providing tested remediation procedures for vulnerabilities Tracking vulnerabilities from when they are identied Communicating vulnerability information to owners of vulnerable systems Reporting on the status of vulnerabilities Ensuring the proper level of management is involved
Module 12 Chapter 12 Information Security Maintenance 41
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Figure 12-15 Vulnerability Assessment and Remediation
Module 12 Chapter 12 Information Security Maintenance 42
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Process of identifying and documenting specic and provable aws in organizations information asset environment Five vulnerability assessment processes that follow can serve many organizations as they attempt to balance intrusiveness of vulnerability assessment with need for stable and productive production environment
Module 12 Chapter 12
Information Security Maintenance
43
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Penetration Testing: A level beyond vulnerability testing Is a set of security tests and evaluations that simulate attacks by a malicious external source (hacker) Penetration test (pen test): usually performed periodically as part of a full security audit Can be conducted one of two ways: black box or white box
Module 12 Chapter 12
Information Security Maintenance
44
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Internet Vulnerability Assessment Designed to nd and document vulnerabilities present in organizations public-facing network Steps in the process include:
Planning, scheduling, and notication Target selection Test selection Scanning Analysis Record keeping
Module 12 Chapter 12
Information Security Maintenance
45
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Intranet Vulnerability Assessment Designed to nd and document selected vulnerabilities present on the internal network Attackers are often internal members of organization, aliates of business partners, or automated attack vectors (such as viruses and worms) This assessment is usually performed against selected critical internal devices with a known, high value by using selective penetration testing Steps in process almost identical to steps in Internet vulnerability assessment
Module 12 Chapter 12 Information Security Maintenance 46
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Platform security Validation Designed to nd and document vulnerabilities that may be present because of mis-congured systems in use within organization These mis-congured systems fail to comply with company policy or standards Fortunately, automated measurement systems are available to help with the intensive process of validating compliance of platform conguration with policy
Module 12 Chapter 12
Information Security Maintenance
47
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Wireless Vulnerability Assessment Designed to nd and document vulnerabilities that may be present in wireless local area networks of organization Since attackers from this direction are likely to take advantage of any loophole or aw, assessment is usually performed against all publicly accessible areas using every possible wireless penetration testing approach
Module 12 Chapter 12
Information Security Maintenance
48
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Modem Vulnerability Assessment Designed to nd and document any vulnerability present on dial-up modems connected to organizations networks Since attackers from this direction take advantage of any loophole or aw, assessment is usually performed against all telephone numbers owned by the organization One element of this process, often called war dialing, uses scripted dialing attacks against pool of phone numbers
Module 12 Chapter 12
Information Security Maintenance
49
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Documenting Vulnerability Vulnerability tracking database should provide details as well as a link to the information assets Low-cost and ease of use makes relational databases a realistic choice Vulnerability database is an essential part of eective remediation
Module 12 Chapter 12
Information Security Maintenance
50
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Remediating Vulnerability Objective is to repair aw causing a vulnerability instance or remove risk associated with vulnerability As last resort, informed decision makers with proper authority can accept risk Important to recognize that building relationships with those who control information assets is key to success Success depends on organization adopting team approach to remediation, in place of cross-organizational push and pull
Module 12 Chapter 12
Information Security Maintenance
51
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Acceptance or Transference of Risk In some instances, risk must simply be acknowledged as part of organizations business process Management must be assured that decisions made to assume risk the organization are made by properly informed decision makers Information security must make sure the right people make risk assumption decisions with complete knowledge of the impact of the decision
Module 12 Chapter 12
Information Security Maintenance
52
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Threat Removal In some circumstances, threats can be removed without repairing vulnerability Vulnerability can no longer be exploited, and risk has been removed Other vulnerabilities may be amenable to other controls that do not allow an expensive repair and still remove risk from situation
Module 12 Chapter 12
Information Security Maintenance
53
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Vulnerability Assessment and Remediation (cont.)
Vulnerability Repair Optimum solution in most cases is to repair vulnerability Applying patch software or implementing a workaround often accomplishes this In some cases, simply disabling the service removes vulnerability; in other cases, simple remedies are possible Most common repair is application of a software patch
Module 12 Chapter 12
Information Security Maintenance
54
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Readiness and Review
Primary goal is to keep information security program functioning as designed and continuously improving Accomplished by:
Policy review Program review Rehearsals
Module 12 Chapter 12
Information Security Maintenance
55
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Readiness and Review
Figure 12-16 Readiness and Review
Module 12 Chapter 12 Information Security Maintenance 56
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: The objective of the internal monitoring domain is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer:
Module 12 Chapter 12
Information Security Maintenance
57
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: The objective of the internal monitoring domain is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: False
Module 12 Chapter 12
Information Security Maintenance
57
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: The objective of the internal monitoring domain is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: False The primary goal of the is to maintain an informed awareness of the state of all of the organizations networks, information systems, and information security defenses.
(a) (b) (c) (d) awareness monitoring domain information monitoring domain internal monitoring domain external monitoring domain
Answer:
Module 12 Chapter 12 Information Security Maintenance 57
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
True or False: The objective of the internal monitoring domain is to provide the early awareness of new and emerging threats, threat agents, vulnerabilities, and attacks that is needed to mount an eective and timely defense. Answer: False The primary goal of the is to maintain an informed awareness of the state of all of the organizations networks, information systems, and information security defenses.
(a) (b) (c) (d) awareness monitoring domain information monitoring domain internal monitoring domain external monitoring domain
Answer: (c)
Module 12 Chapter 12 Information Security Maintenance 57
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
3
The primary goal of the to identify specic, documented vulnerabilities and their timely remediation. Answer:
Module 12 Chapter 12
Information Security Maintenance
58
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
3
The primary goal of the to identify specic, documented vulnerabilities and their timely remediation. Answer: vulnerability assessment and remediation domain
Module 12 Chapter 12
Information Security Maintenance
58
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
3
The primary goal of the to identify specic, documented vulnerabilities and their timely remediation. Answer: vulnerability assessment and remediation domain The primary goal of the is to keep the information security program functioning as designed and to keep it continuously improving over time. Answer:
Module 12 Chapter 12
Information Security Maintenance
58
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
3
The primary goal of the to identify specic, documented vulnerabilities and their timely remediation. Answer: vulnerability assessment and remediation domain The primary goal of the is to keep the information security program functioning as designed and to keep it continuously improving over time. Answer: readiness and review domain
Module 12 Chapter 12
Information Security Maintenance
58
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
3
The primary goal of the to identify specic, documented vulnerabilities and their timely remediation. Answer: vulnerability assessment and remediation domain The primary goal of the is to keep the information security program functioning as designed and to keep it continuously improving over time. Answer: readiness and review domain The process is designed to nd and document the vulnerabilities that may be present because of mis-congured systems in use within the organization. Answer:
Module 12 Chapter 12
Information Security Maintenance
58
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
3
The primary goal of the to identify specic, documented vulnerabilities and their timely remediation. Answer: vulnerability assessment and remediation domain The primary goal of the is to keep the information security program functioning as designed and to keep it continuously improving over time. Answer: readiness and review domain The process is designed to nd and document the vulnerabilities that may be present because of mis-congured systems in use within the organization. Answer: platform security validation (PSV)
Module 12 Chapter 12
Information Security Maintenance
58
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Digital Forensics
Digital forensics is used to investigate what happened during attack on assets and how attack occurred Based on the eld of traditional forensics Involves preservation, identication, extraction, documentation, and interpretation of computer media for evidentiary and/or root cause analysis Evidentiary material (EM) is any information that could potentially support organizations legal or policy-based case against suspect
Module 12 Chapter 12
Information Security Maintenance
59
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Digital Forensics (cont.)
Used for two key purposes:
1 2
To investigate allegations of digital malfeasance To perform root cause analysis
Organization chooses one of two approaches:
1
Protect and forget (patch and proceed): defense of data and systems that house, use, and transmit it Apprehend and prosecute (pursue and prosecute): identication and apprehension of responsible individuals, with additional attention on collection and preservation of potential EM that might support administrative or criminal prosecution
Module 12 Chapter 12
Information Security Maintenance
60
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Digital Forensics Team
Most organizations
Cannot sustain a permanent digital forensics team Collect data and outsource analysis
Information security group personnel should be trained to understand and manage the forensics process to avoid contamination of potential EM Expertise can be obtained by training
Module 12 Chapter 12
Information Security Maintenance
61
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Adavits and Search Warrants
Adavit
Sworn testimony that certain facts are in the possession of the investigating ocer that they feel warrant the examination of specic items located at a specic place The facts, the items, and the place must be specied
When an approving authority signs the adavit, it becomes a search warrant, giving permission to:
Search the EM at the specied location Seize items to return to the investigator for examination
Module 12 Chapter 12
Information Security Maintenance
62
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Digital Forensics Methodology
All investigations follow the same basic methodology:
1
Identify relevant items of evidentiary value (EM) Acquire (seize) the evidence without alteration or damage Take steps to assure that the evidence is at every step veriably authentic and is unchanged from the time it was seized Analyze the data without risking modication or unauthorized access Report the ndings to the proper authority
Module 12 Chapter 12
Information Security Maintenance
63
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Digital Forensics Methodology
Figure 12-17 The Digital Forensics Process
Module 12 Chapter 12 Information Security Maintenance 64
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Evidentiary Procedures
Strong procedures for the handling of potential EM can minimize the probability of an organizations losing a legal challenge Organizations should develop specic procedures with guidance, for example:
Who may conduct an investigation and who is authorized in an investigation What adavit and search warrant-related issues are required The methodology to be followed The nal report format
Module 12 Chapter 12
Information Security Maintenance
65
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
is the coherent application of methodical investigatory techniques to present evidence of crimes in a court of court-like setting. Answer:
Module 12 Chapter 12
Information Security Maintenance
66
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
is the coherent application of methodical investigatory techniques to present evidence of crimes in a court of court-like setting. Answer: Forensics
Module 12 Chapter 12
Information Security Maintenance
66
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
is the coherent application of methodical investigatory techniques to present evidence of crimes in a court of court-like setting. Answer: Forensics The v model of data acquisition is where the investigator removes the power source and then uses a utility or special device to make a bit-stream sector-by-sector copy of the hard drives contained in the system. Answer:
Module 12 Chapter 12
Information Security Maintenance
66
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
is the coherent application of methodical investigatory techniques to present evidence of crimes in a court of court-like setting. Answer: Forensics The v model of data acquisition is where the investigator removes the power source and then uses a utility or special device to make a bit-stream sector-by-sector copy of the hard drives contained in the system. Answer: oine
Module 12 Chapter 12
Information Security Maintenance
66
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
is the coherent application of methodical investigatory techniques to present evidence of crimes in a court of court-like setting. Answer: Forensics The v model of data acquisition is where the investigator removes the power source and then uses a utility or special device to make a bit-stream sector-by-sector copy of the hard drives contained in the system. Answer: oine In information security, most operation focus on Answer: .
Module 12 Chapter 12
Information Security Maintenance
66
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Quick Quiz
1
is the coherent application of methodical investigatory techniques to present evidence of crimes in a court of court-like setting. Answer: Forensics The v model of data acquisition is where the investigator removes the power source and then uses a utility or special device to make a bit-stream sector-by-sector copy of the hard drives contained in the system. Answer: oine In information security, most operation focus on Answer: policies .
Module 12 Chapter 12
Information Security Maintenance
66
Introduction
Security Management Models
The Security Maintenance Model
Digital Forensics
Additional resources
Computer Forensics Investigator http://www.jobproles.org/govcpolicie1.htm SANS Reading Room Penetration Testing http://www.sans.org/reading room/whitepapers/testing/ High Tecdh Crime Institute http://www.hightechcrimeinstitute.com/ High Tech Crime Network http://www.htcn.org/
Module 12 Chapter 12
Information Security Maintenance
67
You might also like
- (Laboratory No. 1.3: E-Car Battery Monitoring) : ObjectivesDocument4 pages(Laboratory No. 1.3: E-Car Battery Monitoring) : ObjectivesAmrosy Bani BunsaNo ratings yet
- LectureNotes IASEC2Document15 pagesLectureNotes IASEC2Leary John TambagahanNo ratings yet
- How To Create A Utility TreeDocument2 pagesHow To Create A Utility TreeJackson ChuaNo ratings yet
- MIS - Chapter - 6 - Database & Information SystemDocument40 pagesMIS - Chapter - 6 - Database & Information Systemovi_hassan74No ratings yet
- Case Study 2 Carlson Department StoreDocument2 pagesCase Study 2 Carlson Department StoreMaricar PinedaNo ratings yet
- An Android Based Computer Aided Instruction of Quadratic Functions For Grade 9 StudentsDocument33 pagesAn Android Based Computer Aided Instruction of Quadratic Functions For Grade 9 StudentsNorieta BetorioNo ratings yet
- Sia102 Midterm Lab Activity 2Document4 pagesSia102 Midterm Lab Activity 2Vida, John PaulNo ratings yet
- Whitman Ch01Document61 pagesWhitman Ch01lekhaharsha100% (1)
- Quality Consciousness Habits and Processes: Activity #: 1Document2 pagesQuality Consciousness Habits and Processes: Activity #: 1Brodley James TorresNo ratings yet
- Lecture 3 Product and Service DesignDocument47 pagesLecture 3 Product and Service DesignNickifah Alleyne100% (1)
- CPM Problems With Solution: Solving Network Problem On Computer Using TORA (Input Screen)Document10 pagesCPM Problems With Solution: Solving Network Problem On Computer Using TORA (Input Screen)Aswin Sivaramakrishnan0% (1)
- Polytechnic University of The Philippines: Jireh Trading Sales and Inventory Management SystemDocument8 pagesPolytechnic University of The Philippines: Jireh Trading Sales and Inventory Management SystemSheikaina Mia SiacorNo ratings yet
- Handouts Review On FSDocument2 pagesHandouts Review On FSMaetherese SaradponNo ratings yet
- Review of Related LiteratureDocument6 pagesReview of Related LiteratureAlexander IgnacioNo ratings yet
- 10 Tle Ccs q2 Week 6Document11 pages10 Tle Ccs q2 Week 6sim jay-hunNo ratings yet
- Tools in Accounting For BusinessDocument5 pagesTools in Accounting For BusinessKylie sheena MendezNo ratings yet
- Bsa Department: Philippine School of Business Administration-ManilaDocument8 pagesBsa Department: Philippine School of Business Administration-ManilaKendrew SujideNo ratings yet
- Ch3 - Systems Documentation TechniquesDocument11 pagesCh3 - Systems Documentation Techniquesadeline chengNo ratings yet
- Assessment of Records Management Practice by Administrative Assistants For Effective Administration of Tertiary Institutions in Ebonyi StateDocument6 pagesAssessment of Records Management Practice by Administrative Assistants For Effective Administration of Tertiary Institutions in Ebonyi StateEditor IJTSRDNo ratings yet
- Course OutlineDocument1 pageCourse OutlineAfzaalNo ratings yet
- Operations & Supply Chain ManagementDocument35 pagesOperations & Supply Chain ManagementAnimesh kumarNo ratings yet
- Tugas 1 - ER ModelDocument3 pagesTugas 1 - ER ModelBilly PurdianantoNo ratings yet
- EDS 111 COURSE OUTLINE ExtendedDocument19 pagesEDS 111 COURSE OUTLINE ExtendedPreciousNo ratings yet
- Platform Technologies Module 3Document54 pagesPlatform Technologies Module 3Christian KingawNo ratings yet
- Evolving Roles of A System Analyst in The Contemporary Society For Organizational GrowthDocument6 pagesEvolving Roles of A System Analyst in The Contemporary Society For Organizational GrowthInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Soc Sci 104 - Basic Econ - Course OutlineDocument2 pagesSoc Sci 104 - Basic Econ - Course OutlinearciblueNo ratings yet
- Web-Based Requisition and Bidding SystemDocument45 pagesWeb-Based Requisition and Bidding SystemTeremaeNo ratings yet
- Quegan, Jaren G. Bscs 1A Assignment 2Document3 pagesQuegan, Jaren G. Bscs 1A Assignment 2Jaren QueganNo ratings yet
- Introduction To Database SystemDocument26 pagesIntroduction To Database SystemE-oNeIchiNo ratings yet
- Introduction To Information SecurityDocument127 pagesIntroduction To Information SecurityNirai Mathi100% (1)
- Introduction of MS Excel 2010 PDFDocument25 pagesIntroduction of MS Excel 2010 PDFWena Prado - AbuelNo ratings yet
- Application Development & Emerging TechnologyDocument2 pagesApplication Development & Emerging TechnologyMaria Liza OcañaNo ratings yet
- Artificial Intelligence For DummiesDocument3 pagesArtificial Intelligence For DummiesBulbula Kumeda0% (2)
- AE21 - COURSE LEARNING Content PDFDocument3 pagesAE21 - COURSE LEARNING Content PDFcharlotte FijerNo ratings yet
- Group 4 Final Group Activity IADocument1 pageGroup 4 Final Group Activity IAFernando GaringoNo ratings yet
- Rule 29 Sec 3 Genove EditDocument5 pagesRule 29 Sec 3 Genove EditAC MirandaNo ratings yet
- Institutional Waiver CMT For CovidDocument2 pagesInstitutional Waiver CMT For CovidElaina JoyNo ratings yet
- AE 108 Handout No.4Document14 pagesAE 108 Handout No.4Christine DamesNo ratings yet
- Data Privacy ActDocument2 pagesData Privacy ActJecky Delos ReyesNo ratings yet
- Forecasting IntroductionDocument29 pagesForecasting IntroductionRajan ManchandaNo ratings yet
- LO1: What Factors Should A Retailer Consider When Establishing Pricing Objectives and Policies?Document5 pagesLO1: What Factors Should A Retailer Consider When Establishing Pricing Objectives and Policies?Suresh KumarNo ratings yet
- Euthenics Prelims CoverageDocument14 pagesEuthenics Prelims CoverageDarlene De PazNo ratings yet
- Online Sales and InventoryDocumentationDocument122 pagesOnline Sales and InventoryDocumentationJahiruddin AhamedNo ratings yet
- Point of Sales SystemDocument9 pagesPoint of Sales SystemJordan SegundoNo ratings yet
- Chapter 9 Hypothesis TestingDocument44 pagesChapter 9 Hypothesis TestingTitis SiswoyoNo ratings yet
- Syllabus Business Analytics Second Sem Sy 2019-2020Document5 pagesSyllabus Business Analytics Second Sem Sy 2019-2020Phia BrumaNo ratings yet
- Chapter 1Document2 pagesChapter 1Andreas BrownNo ratings yet
- CBLM CSS COC JCDocument113 pagesCBLM CSS COC JCJc CapistranoNo ratings yet
- Philippines PPTDocument18 pagesPhilippines PPTKristopher FreemanNo ratings yet
- Short Notes On Public Speaking MaterialsDocument2 pagesShort Notes On Public Speaking Materialsstrawberry_89No ratings yet
- Capstone TitleDocument14 pagesCapstone TitleRasmiah SambolawanNo ratings yet
- Online Shopping: Ccs University MeerutDocument11 pagesOnline Shopping: Ccs University Meerutsaikripa121No ratings yet
- Legal Opinion SampleDocument3 pagesLegal Opinion SampleJoanna Diane MortelNo ratings yet
- The Systems Development Life CycleDocument8 pagesThe Systems Development Life CycleRichelle PolicarpioNo ratings yet
- Chapter 7 Micro-Economics ReviewDocument50 pagesChapter 7 Micro-Economics ReviewMeg GregoireNo ratings yet
- 100 Most Promising Big Data Solution ProvidersDocument2 pages100 Most Promising Big Data Solution ProvidersInfo TrellisNo ratings yet
- Chapter IIDocument18 pagesChapter IIJoseph DegamoNo ratings yet
- Maintenance of Information Security and EdiscoveryDocument62 pagesMaintenance of Information Security and EdiscoveryAntonyNo ratings yet
- Computers, Business, and Security: The New Role for SecurityFrom EverandComputers, Business, and Security: The New Role for SecurityNo ratings yet
- The NIST Special PublicationsDocument27 pagesThe NIST Special Publicationsb meherbabaNo ratings yet
- Regenerative DriveDocument2 pagesRegenerative DriveAyrton WidiutomoNo ratings yet
- Answer Tut11Document4 pagesAnswer Tut11Ayrton WidiutomoNo ratings yet
- Answer Tut12Document4 pagesAnswer Tut12Ayrton WidiutomoNo ratings yet
- Answer Tut8Document4 pagesAnswer Tut8Ayrton WidiutomoNo ratings yet
- Answer Tut7Document3 pagesAnswer Tut7Ayrton WidiutomoNo ratings yet
- NSC Topic 8 Access ControlDocument13 pagesNSC Topic 8 Access ControlrubbyNo ratings yet
- Lab 10: IDPS - Snort & Cisco IDPS Sensors: 9.1 DetailsDocument24 pagesLab 10: IDPS - Snort & Cisco IDPS Sensors: 9.1 DetailsewNo ratings yet
- © 2019 Caendra Inc. - Hera For IHRP - Effectively Using SnortDocument27 pages© 2019 Caendra Inc. - Hera For IHRP - Effectively Using SnortSaw GyiNo ratings yet
- Iaas311 Prelims Reviewer 1Document29 pagesIaas311 Prelims Reviewer 1CLARENCE MIGUEL PALOMARESNo ratings yet
- 5.5.1.1 Lab - Configuring An Intrusion Prevention System (IPS) Using The CLI and CCP - InstructorDocument53 pages5.5.1.1 Lab - Configuring An Intrusion Prevention System (IPS) Using The CLI and CCP - InstructorSalem TrabelsiNo ratings yet
- Ebusiness Risks ManagementDocument410 pagesEbusiness Risks ManagementDana DangNo ratings yet
- Correlation Reference Guide: Alienvault Unified Security Management™ SolutionDocument18 pagesCorrelation Reference Guide: Alienvault Unified Security Management™ Solutionr.borges.almeidaNo ratings yet
- Hack IT Security Through Penetration TestingDocument575 pagesHack IT Security Through Penetration TestingRaja Mustafa0% (1)
- Threat HuntingDocument2 pagesThreat HuntingDrShubhamangala SunilaNo ratings yet
- Impact of Cybercrime On Tourism IndustryDocument15 pagesImpact of Cybercrime On Tourism IndustryVladimir Lav LajovićNo ratings yet
- Case Study 1Document21 pagesCase Study 1Nasira RanaNo ratings yet
- Meitsec Soc NF v11Document28 pagesMeitsec Soc NF v11Digit OktaviantoNo ratings yet
- Week 1 Lecture 1 Information SecurityDocument28 pagesWeek 1 Lecture 1 Information SecurityZulkifl HasanNo ratings yet
- Comparison 2018Document14 pagesComparison 2018Brenton BudlerNo ratings yet
- Log Management Presentation.Document21 pagesLog Management Presentation.rishukansaliwal0% (1)
- Rahul - ProfileDocument12 pagesRahul - ProfileRahul GoyalNo ratings yet
- FINAL CHEAT SHEET Industrial Network Security Monitoring Incident ResponseDocument2 pagesFINAL CHEAT SHEET Industrial Network Security Monitoring Incident ResponseAni MNo ratings yet
- Asset ProtectionDocument13 pagesAsset ProtectionJefferson KagiriNo ratings yet
- Huawei IP Network Products Sales TrainingDocument53 pagesHuawei IP Network Products Sales TrainingfestauNo ratings yet
- Incident Detection and Response To Suspicious Root Access PlaybookDocument10 pagesIncident Detection and Response To Suspicious Root Access PlaybookirokoNo ratings yet
- CEH v10 Exam C With AnswersDocument29 pagesCEH v10 Exam C With AnswersBryan Wat KimsNo ratings yet
- ARP SpoofingDocument6 pagesARP SpoofingDileep Kumar ManjhiNo ratings yet
- Detection of Cyber Attack in Network Using Machine Learning Techniques FinalDocument50 pagesDetection of Cyber Attack in Network Using Machine Learning Techniques FinalMohan Krishna100% (3)
- Security Services ApplianceDocument19 pagesSecurity Services ApplianceDarlene HillNo ratings yet
- OT Security ChecklistDocument15 pagesOT Security Checklistct pentestNo ratings yet
- Cisco Clean Air Technology White PaperDocument10 pagesCisco Clean Air Technology White PaperganuiyerNo ratings yet
- Trend Micro Apex One: Endpoint Security RedefinedDocument2 pagesTrend Micro Apex One: Endpoint Security Redefinedpier Aguilar RamirezNo ratings yet
- MX Sizing Guide: September 2018Document6 pagesMX Sizing Guide: September 2018Walter PurezaNo ratings yet
- Session 3 - CRISC Exam Prep Course - Domain 3 - Risk Response and Mitigation PDFDocument88 pagesSession 3 - CRISC Exam Prep Course - Domain 3 - Risk Response and Mitigation PDFAmor Dulce88% (8)
- Nortel Comparision With CiscoDocument7 pagesNortel Comparision With CisconeelNo ratings yet