Professional Documents
Culture Documents
Zigbee Network
Uploaded by
Sona Nelson0 ratings0% found this document useful (0 votes)
133 views71 pagesproject report
Original Title
zigbee network
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Documentproject report
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
133 views71 pagesZigbee Network
Uploaded by
Sona Nelsonproject report
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 71
DESIGN OF ASSURED DATA DELIVERY USING INDEGREE AND
CAPACITY CALCULATION IN WIRELESS ZIGBEE NETWORK
Submitted By
SANGEETHA S. NAIR
(Reg. No. 113112405011)
of
Department of Computer Science and Engineering
VEL TECH MULTITECH Dr. RANGARAJAN Dr. SAKUNTHALA
ENGINEERING COLLEGE
(ACCREDITED BY NBA & ISO 9001:2008 CERTIFIED INSTITUTION)
(Approved by AICTE, New Delhi & Affiliated to ANNA UNIVERSITY, CHENNAI)
Avadi, Chennai-600 062
A PROJECT PHASE II REPORT
Submitted To
Faculty of Computer Science and Engineering
in Partial Fulfillment of the Requirement for the Award of the Degree of
MASTER OF ENGINEERING
In
COMPUTER SCIENCE AND ENGINEERING
ANNA UNIVERSITY OF TECHNOLOGY, CHENNAI-113
JUNE 2014
VEL TECH MULTITECH Dr. RANGARAJAN Dr. SAKUNTHALA
ENGINEERING COLLEGE
(ACCREDITED BY NBA & ISO 9001:2008 CERTIFIED INSTITUTION)
(Approved by AICTE, New Delhi & Affiliated to ANNA UNIVERSITY, CHENNAI)
Avadi, Chennai-600 062
________________________________________________________________
Date: ...../../2014
BONAFIDE CERTIFICATE
Certified that the project report titled DESIGN OF ASSURED DATA DELIVERY
USING INDEGREE AND CAPACITY CALCULATION IN WIRELESS ZIGBEE
NETWORK, is a bonafide project work of SANGEETHA S. NAIR (Reg. No.
113112405011) who carried out research under my supervision certified further, that to the best
of my knowledge the work reported here in does not form part of any other project report or
dissertation on the basis of which a degree or award was conferred on an earlier occasion on this
or any other candidate.
SIGNATURE SIGNATURE
Ms. A.SATHIYAVANI, M.Tech., Mr. R.KARTHIKEYAN, M.E., (Ph.D),
INTERNAL GUIDE HEAD OF THE DEPARTMENT
ASSISTANT PROFESSOR ASSOCIATE PROFESSOR
Dept. of Computer Science & Engg Dept. of Computer Science & Engg
Vel Tech MultiTech Dr.Rangarajan Vel Tech MultiTech Dr.Rangarajan
Dr.Sakunthala Engineering College Dr.Sakunthala Engineering College
No 60, Avadi, Alamathi Road, Ch-62. No 60, Avadi, Alamathi Road, Ch-62.
SIGNATURE
Dr. V.RAJAMANI ME., Ph.D
PRINCIPAL
INTERNAL EXAMINER EXTERNAL EXAMINER
CERTIFICATE FOR EVALUATION
This is to certify that the project entitled DESIGN OF ASSURED DATA
DELIVERY USING INDEGREE AND CAPACITY CALCULATION IN WIRELESS
ZIGBEE NETWORK is the bonafide record of work done by SANGEETHA S.
NAIR (Reg. No. 113112405011) to carry out the project work under our guidance
during the year 2013-2014 in partial fulfillment for the award of Master Of
Engineering degree in Computer Science and Engineering conducted by Anna
University Chennai.
This project report was submitted for viva voice held on .................... at Vel Tech
Multi Tech Dr. Rangarajan Dr. Sakunthala Engineering College.
INTERNAL EXAMINER EXTERNAL EXAMINER
DATE.............................
ACKNOWLEDGEMENT
I thank God Almighty for giving me such tremendous opportunity and support through
the way of Vel Tech MultiTech Dr. Rangarajan Dr. Sakunthala Engineering College. I
express my deep gratitude to the Founder & Chairman Prof. Col. Dr. R. Rangarajan, B.E
(Elec.), B.E (Mech.), M.S (Auto.), D.Sc. and our Vice-Chairman Smt Dr. Sakunthala
Ranagarajan MBBS. for the benefaction encouragement and facilities that were offering to us
to carry out this project.
I thank my Principal Dr. V.Rajamani ME., Ph.D, who has always served as an
inspiration for us to perform our institutes name and recognition. I would like to express our
faithful thanks to our beloved HOD Mr. R.KARTHIKEYAN, M.E.,(Ph.D) and my respected
Internal Project Guide, Ms. A.SATHIYAVANI, M.E., for having extended all the department
facilities without slightest hesitation.
I extend my gratitude to thank my Project Co-ordinator Mr. M. Ramesh Kumar,
M.E.,(Ph.D) for guiding me in every phase of the project development.
Further I thank my Parents, Friends, Faculty members, supporting staff members of
Computer Science & Engineering and PPT department for the help they extended to
completion of this project.
v
ABSTRACT
ZigBee networks usually uses a tree topology to construct a wireless sensor network for
data delivery applications. There are 3 types of nodes in ZigBee networks; coordinator, router
and mobile end devices. Coordinator performs the initialization and maintenance functions in the
network. A router is responsible for routing data between the coordinator and mobile end device.
Inorder to avoid the delivery failures occurs due to node movements and network topology
changes, the existing system collect and analyze data about device movement and gives ZigBee
node deployment and tree construction framework, which is done in three phases: ZND(ZigBee
node deployment), ZCD(ZigBee coordinator decision) and ZTC(ZigBee tree construction). In the
proposed system we improve the data delivery by introducing the capacity calculation. If any
two nodes have same number of indegree or outdegree, we select the node with maximum
capacity.
. ,
.
.
.
: , , .
.
.
.
.
.
.
.
vi
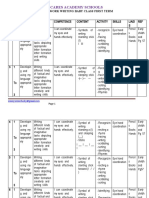
TABLE OF CONTENTS
CHAPTER
NO
TITLE PAGE
NO
ABSTRACT V
LIST OF FIGURES X
LIST OF ABBREVIATIONS XI
1 INTRODUCTION 1
1.1 Introduction 1
1.2 ZigBee Standard Architecture 1
1.3 Security 5
1.4 Commercial Applications of Wireless Sensor
Networks Using ZigBee
6
1.5 Network Simulator 9
1.6 Problem Definition and Objective 10
2 LITERATURE SURVEY 11
2.1 Grid Coverage for Surveillance and Target Location in Distributed
d Sensor Networks
11
2.2 ZigBee Wireless Sensor Networks and Their Applications 11
2.3 Performance Analysis And Improvement Of ZigBee Routing
Protocol
12
2.4 Toward Secure Low Rate Wireless Personal Area Networks 12
vii
2.5 Tree- Based Data Broadcast in IEEE 802.15.4 and ZigBee
Networks
13
2.6 Routing in ZigBee: Benefits from exploiting the IEEE 802.15.4
a association tree
13
2.7 Address Assignment and Routing Schemes for ZigBee- Based
Long-Thin Wireless Sensor Networks
14
2.8 Shortcut Tree Routing in ZigBee Networks 14
2.9 Improvement Of ZigBee Routing Protocol Including Energy And
Delay Constraints
15
2.10 Transmission Power Requirements for Novel ZigBee Implants in
a the Gastrointestinal Tract
15
2.11 Wireless Sensor Networks for Resources Tracking at Building
s Construction Sites
16
2.12 Social Network Analysis for Information Flow in Disconnected
s s Delay-Tolerant MANETs
16
2.13 UPnP-ZigBee Internetworking Architecture Mirroring a Multi-
s hop ZigBee Network Topology
17
2.14 A Lightweight Network Repair Scheme for Data Collection
s Applications in ZigBee WSNs
17
2.15 Reliable Data Broadcast for ZigBee Wireless Sensor Networks 18
2.16 Distributed Throughput Optimization for ZigBee Cluster-Tree
s Networks
18
2.17 Diagnosis of Failures in ZigBee Based WirelessSensor Networks 19
2.18 Distributed Fault Tolerant Algorithm for Identifying Node
s s Failures in Wireless Sensor Networks
19
2.19 Neighbor Table based Shortcut Tree Routing in ZigBee Wireless
h Networks
20
viii
2.20 Energy- Efficient Routing Protocols in Wireless Sensor
Networks: A Survey
20
3 EXISTING SYSTEM 21
3.1 Existing System 21
3.2 Disadvantages 22
4 PROPOSED SYSTEM 23
4.1 Proposed System 23
4.2 Advantages 23
5 SYSTEM REQUIREMENTS 24
5.1 Hardware Requirements 24
5.2 Software Requirements 24
6 ARCHITECTURAL REPRESENTATION 25
6.1 System Architecture 25
7 MODULES 27
7.1 Node Deployment 27
7.2 Coordinator Decision 28
7.3 Capacity Calculation 28
7.4 Flexible Routing 29
8
9
DATA FLOW DIAGRAM
CONCLUSION
30
31
ix
10
11
FUTURE ENHANCEMENT
APPENDIX A-CODINGS
32
33
12 APPENDIX B-COMPARISON TABLE 45
13 APPENDIX C-SCREENSHOTS 46
REFERENCES 54
x
LIST OF FIGURES
FIGURE NO TITLE PAGE NO
1.1 ZigBee Protocol Stack 2
1.2 ZigBee Mesh topology 4
1.3 ZigBee Cluster Tree Topology 5
1.4 NS2 Architecture 9
6.1 Capacity Calculation 26
6.2 Data Delivery 26
7.1 Node Deployment 27
7.2 Coordinator Decision 28
7.3 Tree Construction 29
7.4 Capacity Calculation 29
8.1 Data Flow Diagram 30
xi
LIST OF ABBREVIATIONS
WSN Wireless Sensor Networks
OSI Open System Interconnection
MAC Medium Access Control
WPAN Wireless Private Area Network
ZND ZigBee Node Deployment
ZCD ZigBee Coordinator Decision
ZTC ZigBee Tree Construction
MRZT Mobility Robust ZigBee Tree Topology
AODV Adhoc On demand Distance Vector
1
CHAPTER 1
INTRODUCTION
1.1. Introduction
ZigBee is a specification for a suite of high level communication protocols. ZigBee is
a typical wireless communication technology. ZigBee uses low rate, low-power digital radios
based on an IEEE 802 standard for personal area networks. The technology defined by the
ZigBee specification is intended to be simpler and less expensive than other WPANs
(Wireless personal area network), such as Bluetooth. ZigBee is targeted at radio-frequency
(RF) applications that require a low data rate, long battery life, and secure networking.
ZigBee has a defined rate of 250 kbps best suited for periodic or intermittent data or a single
signal transmission from a sensor or input device. It is Open standard protocol with no or
negligible licensing fees, chipsets available from multiple sources, remotely upgraded
firmware, fully wireless and low power, mesh networking to operate on batteries, low
maintenance and larger network size with standard based high security.
ZigBee is a typical wireless communication technology, which is widely used in
wireless sensing networks. ZigBee wireless sensor network is widely used in military
security, environment monitoring, and home automation. Various progressive wireless
communication standards were developed and implemented into practice during the last
decade. GSM, WiFi and Bluetooth are well known amongst people in the modern society.
These standards have penetrated into their daily routine with outstanding popularity. An
Internet of people has become ordinary for everyone who wants to have everybody and
everything within reach. As a new technology, in the practical application the advantage of
the ZigBee wireless sensor network was not very ideal, especially in a large scale wireless
Zigbee sensor network, because the coordinator processing ability is limited. In the large
scale ZigBee wireless network the coordinator should deal with too much message, so some
shortcomings come out, such as information time delay, data packet loss, and sensor node out
of control.
1.2. ZigBee Standard Architecture
1.2.1. Network reference model
Network devices, whether wired or wireless, are commonly described by the Open
Systems Interconnection (OSI) reference model. This abstraction model was developed by
2
the International Standards Organization (ISO), starting in th1e 1980 description of
communication-related protocols and services. The generic seven-layer model is applied to
all network and media types. The adaptation ISO-OSI network reference model for ZigBee
purposes is illustrated in the Fig.1.1. ZigBee network model does not use presentation,
session or transport layer and user application is directly tied into Application layer (APL).
This figure shows also IEEE, ZigBee Alliance, and ZigBee product end manufacturer
particular responsibility for ZigBee certified product as well as hardware and software
proportion in ZigBee.
Fig.1.1 ZigBee Protocol Stack
1.2.2. IEEE 802.15.4 Standard
The IEEE standard [3] brings the ability to identify uniquely every radio in a network
as well as the method and format of communications between these radios, but does not
specify beyond a peer-to-peer communications link, a network topology, routing schemes or
network growth and repair mechanisms. The ZigBee Alliance selected the IEEE 802.15.4
standard, released in May 2003, as the wheels and chassis upon which ZigBee networking
and applications have to be constructed. IEEE 802.15.4 defines three frequency bands to
3
employ a standard over the world. Overview of available bands, modulation method and
other properties of each is resumed in the table below (Table 1).
Table 1 Available frequency band within IEEE 802.15.4 spec with appropriate bit rate and
modulation method
1.2.3. ZigBee Standard
The ZigBee specification identifies three kinds of devices that incorporate ZigBee
radio, with all three found in a typical ZigBee network (Fig.2):
Coordinator (ZC): organizes the network and maintains routing tables
Routers (ZR): can talk to the coordinator, to other routers and to reduced-function end
devices
End devices (ZED): can talk to routers and the coordinator, but not to each other.
ZigBee supports three kinds of network topology, namely, star, cluster-tree, and mesh
topologies. In a star network, multiple ZigBee end devices connect directly to the ZigBee
coordinator. For cluster-tree and mesh networks, communications can be conducted in a
multihop fashion through ZigBee routers. In a cluster-tree network, each ZigBee router with
surrounding devices is regarded as a respective cluster, and each cluster operates individually
as a star network, as shown in Fig.
4
Fig.1.2 ZigBee mesh topology
.
5
Fig.1.3 ZigBee Cluster Tree topology
1.3. Security
Security and data integrity are key benefits of the ZigBee technology. ZigBee
leverages the security model of the IEEE 802.15.4 MAC sub layer which specifies four
security services:
access control: the device maintains a list of trusted devices within the network
data encryption: which uses symmetric key 128-bit advanced encryption standard
frame integrity to protect data from being modified by parties without cryptographic keys
sequential freshness : to reject data frames that have been replayed, the network controller
compares the freshness value with the last known value from the device and rejects it if the
freshness value has not been updated to a new value.
6
Table 2 Wireless Technology Comparison
1.4. Commercial Applications of Wireless Sensor Networks Using ZigBee
1.4.1. Home Automation
Possibly the highest volume shipping application using ZigBee mesh networks today,
home automation originally was not one of the typically envisioned applications for sensor
networking. A variety of factors, including the speed at which consumer products are
designed and brought to market has caused this market to move quickly. Initial applications
brought to market focused on two primary areas: comfort and awareness/safety. Products that
focused on comfort and convenience fit into the traditional home automation applications
such as lighting control and audio/video control. However, sensor networking is used in the
home for much more than the traditional home automation uses. Some products focus on
providing home owners with more awareness of the state of their homes without requiring a
full-blown security system. Others are starting to focus on using sensor and control
technology to save energy.
Eatons Home Heartbeat system is a home awareness system that is essentially a
sensor network for a house. The system consists of a variety of sensors that can monitor a
home. A gateway device can send messages to a mobile phone when the home owner is away
from the house, or to a keychain display when a home owner is at home. The Home
Heartbeat system can monitor events such as water leaks via a water presence sensor, small
appliance usage via a power sensor, door and windows with an open/close sensor, or presence
via an occupancy sensor. At any time, the state of each sensor can be checked via the
keychain or a mobile phone interface. Alerts can be set on the keychain so that the user can
be informed of state changes in any of the sensors. Intended to be an awareness system rather
than a security system, it is designed to be installed by an end consumer and is marketed
7
through both electronics stores and home improvement stores. The system also brings some
control elements into the network in the form of a water shut-off valve and switchable outlet.
1.4.2. Building Automation
Another application area that experienced substantial commercial deployment is
building automation. This relatively broad term can cover all aspects of building system
control including heating and air conditioning (HVAC), lighting control, and security
systems. The relatively high cost of energy and a growing movement toward energy
efficiency has made energy management one of the key drivers in the adoption of wireless
sensor networks in commercial buildings. Similar to the residential market, a substantial
market exists in retrofitting existing buildings. Traditional wired building automation
networks usually are used only in new construction or major retrofits. The low installation
cost of mesh-based wireless systems allows the larger retrofit market to be addressed. Unlike
residential automation systems, the relatively frequent repartitioning of commercial space as
tenants come and go makes a wireless system (that can be easily moved and reconfigured) an
even better proposition than it may appear at first. Finally, the granularity with which sensors
such as temperature and occupancy can be placed permits a level of control that would be
prohibitive with wired systems.
An example of energy management systems using wireless sensor networking is the
WiSuite automation system from Riga Development . This energy management system is
targeted initially at hotel and motel properties. Consisting primarily of thermostat devices and
control interfaces for in-room heating and cooling units, the system interfaces into the hotel
reservation system for occupancy information. When a room is occupied, temperature can be
set using the in-room thermostat. When a room becomes unoccupied, the system
automatically dials back the set point on the thermostat to minimize energy usage. Because of
the relatively low hardware and installation costs when using a wireless mesh for
communications, the cost of energy saved on a monthly basis usually exceeds the monthly
payments for a system financed over just a few years. This enables an installation to be cash-
flow positive on installation and minimizes the amount of capital required. From the
perspective of a network architecture, this application is a mix of line-powered and battery-
powered devices. The energy savings alone can justify the entire system; however, the
presence of a communication network and sensors in the hotel also permits run-time analysis
of the performance and state of the HVAC units.
8
1.4.3. Utility Meter Communication
A large percentage of the residential utility meters (water, gas, electric) in the U.S.
and Europe are read remotely using a variety of technologies. A growing number in other
places are rapidly being converted to remote reading. Although radios based on 802.15.4
2.4GHz technology do not have the point-to-point range required for many metering
applications, in some situations, it is a compelling technology. In areas where utility meters
are densely deployed, such as large apartment or condominium buildings or dense urban
areas, sub-metering solutions using ZigBee wireless sensor networks are being fielded. One
area of utility metering that is experiencing a large amount of interest is in energy savings and
demand control. Upcoming legislation in California , regarding energy efficiency of
buildings, requires a certain amount of electricity demand management to be available. One
commonly discussed form is a meter that can communicate into the house to indicate more
dynamic pricing of electricity, as well as turn down air conditioning (increase the set
temperature) in situations where the electricity grid is nearing failure. As in other areas of
automation, devices that can be controlled for energy management easily can be extended by
making use of other home automation products that already support ZigBee.
1.4.4.Location Detection
The promise of asset tracking through supply chains helped propel the adoption of
RFID (radio frequency identification) in both retail and military applications. Although
passive RFID is useful in situations where items pass through doors that can be outfitted with
readers or will sit on shelves that also can be outfitted, a wide variety of assets are better
suited to being tracked with an active RF device. In a situation such as tracking medical
equipment inside a hospital, it would be cost prohibitive to cover enough of the area with
RFID readers to find the equipment. In these situations, a wireless sensor network that could
report the locations of critical equipment is valuable. While 802.15.4 does not lend itself well
to precise time of- flight measurements due to its narrow bandwidth, it can be used to obtain a
signal. strength measurement. Signal strength (RSSI) is not a good way to measure distance,
given the high variation seen due to small scale fading and very different path loss
characteristics found in typical buildings. However, when enough different readings are
combined with a priori knowledge of the building or network layout, accuracy in the range of
a few meters is obtainable.
9
1.5. Network Simulator
Network Simulator (Version 2), widely known as NS2, is simply an event driven
simulation tool that has proved useful in studying the dynamic nature of communication
networks. Simulation of wired as well as wireless network functions and protocols (e.g.,
routing algorithms, TCP, UDP) can be done using NS2. In general, NS2 provides users with a
way of specifying such network protocols and simulating their corresponding behaviours.
NS2 provides users with an executable command ns which takes on input argument, the name
of a Tcl simulation scripting file. Users are feeding the name of a Tcl simulation script
(which sets up a simulation) as an input argument of an NS2 executable command ns. In most
cases, a simulation trace file is created, and is used to plot graph and/or to create animation.
NS2 consists of two key languages: C++ and Object-oriented Tool Command
Language (OTcl). While the C++ defines the internal mechanism (i.e., a backend) of the
simulation objects, the OTcl sets up simulation by assembling and configuring the objects as
well as scheduling discrete events (i.e., a frontend). The C++ and the OTcl are linked together
using TclCL. Mapped to a C++ object, variables in the OTcl domains are sometimes referred
to as handles. Conceptually, a handle (e.g., n as a Node handle) is just a string in the OTcl
domain, and does not contain any functionality. Instead, the functionality (e.g., receiving a
packet) is defined in the mapped C++ object (e.g., of class Connector). In the OTcl domain, a
handle acts as a frontend which interacts with users and other OTcl objects. It may defines its
own procedures and variables to facilitate the interaction. Note that the member procedures
and variables in the OTcl domain are called instance procedures (instprocs) and instance
variables (instvars), respectively.
FFig 1.4 Ns2 Architecture
10
1.6. Problem Definition and Objective
In ZigBee networks, we often use the tree topology to construct a wireless sensor
network for data delivery applications. Due to the node movements and Network Topology
changes, the delivery failures are occurring constantly in ZigBee Wireless Networks. The
location of the mobile end device is recognized by the network and maintained by the
coordinator, which identifies the last router that was used to forward the end devices uplink
data packets. When a downlink packet is sent to a mobile end device, the coordinator delivers
the packet to the last recorded location, i.e., the last router that received the uplink packet
from the mobile end device. Upon the reception of the downlink packet, the router simply
forwards it to the mobile end device and waits for an acknowledgement message from the
end device. If the mobile end device has moved from the last known location, the data
delivery fails, and the coordinator starts a search by broadcasting a message that asks for
information about the mobile end devices current location. Broadcast operations are
expensive in terms of bandwidth and power consumption, particularly when mobile end
devices frequently move between different routers coverage areas.
The conventional route reconstruction method is designed to mitigate the effects of
topology changes, but it consumes a large amount of resources. So the positions of the routers
are determined and design the tree topology so that most movements are directed towards the
root of the tree. To achieve our objective, we gather information about node movements in
the environment and construct a ZigBee tree topology framework. Our proposed Model
Consist of Three Phases namely. 1. ZigBee Node Deployment-which determines the number
and locations of router nodes; 2.Zigbee Coordinator Decision- which selects one of the
router nodes as the coordinator by calculating its in-degree connectivity. A router node which
has the maximum number of in-degree is considered as coordinator for the entire data
transfer; 3. ZigBee Tree Construction- constructs a mobility robust ZigBee tree based on the
deployment in the previous two phases. The proposed system implements the capacity
calculation to find the coordinator node. When two or more nodes have the same indegree the
proposed system will calculate the capacity of each nodes and selects the node with
maximum capacity as coordinator node. It will allow the network to find the best route
through which the data will be delivered to the destination.
11
CHAPTER 2
LITERATURE SURVEY
Title: Grid Coverage for Surveillance and Target Location in Distributed Sensor
Networks[Dec 2002]
Authors: Krishnendu Chakrabarty, S.Sitharama Iyengar, Hairong Qi, and Eungchun Cho
We present novel grid coverage strategies for effective surveillance and target
location in distributed sensor networks. We represent the sensor field as a grid (two or three-
dimensional) of points (coordinates) and use the term target location to refer to the problem
of locating a target at a grid point at any instant in time. We first present an integer linear
programming (ILP) solution for minimizing the cost of sensors for complete coverage of the
sensor fieldWe then use the framework of identifying codes to determine sensor placement
for unique target location. We provide coding-theoretic bounds on the number of sensors and
present methods for determining their placement in the sensor field. We also show that grid-
based sensor placement for single targets provides asymptotically complete (unambiguous)
location of multiple targets in the grid.
Title: ZigBee Wireless Sensor Networks and Their Applications
[Jan 2005]
Authors: Meng-Shiuan Pan and Yu-Chee Tseng
Today, applications in the areas of home automation, building automation, and utility meter
reading represent the bulk of the deployed wireless sensor network devices. The current.
deployments are largely wireless adaptations of existing applications. The initial impetus for
the use of wireless technology was access to retrofit markets and lower installation costs
compared to traditional wired systems. Increasingly, commercial users of wireless sensor
networks are taking advantage of the technology to provide services and features that were
impossible or cost prohibitive in the past. Predictive maintenance of HVAC and lighting
systems and advanced energy management through utility meters are good examples of this
trend. With ZigBee Pro arriving this year and other competing standards and propriety
systems experiencing continued development, wireless sensor networking is a very dynamic
field and likely will remain so over the next few years. Todays applications will give way to
new applications that are more novel and less about replacing costly communication.
12
Title: Performance Analysis And Improvement Of Zigbee Routing Protocol
[Feb 2006]
Authors: Bilel NEFZI and Ye-Qiong Song
ZigBee is a recent wireless standard based on IEEE 802.15.4 for Personal Area Networks. Its
use in Wireless Sensor Networks arouses many interests. In this paper, a performance
analysis and an improvement of ZigBee routing protocol are carried out. ZigBee routing
protocol uses a modified AODV by default and Hierarchical Tree Routing as last resort.
Firstly, these two algorithms are compared in terms of delay performance and energy
consumption. The results showed that Hierarchical Tree Routing provides shorter average
end to end delay but performs poorly in terms of energy consumption. So for supporting real
time communication, it is desirable to freely choose one or another according to the type of
traffic (real- time and non real-time). Secondly, Hierarchical Tree Routing algorithm is
slightly modified to provide shorter delays than the original one.
Title: Toward Secure Low Rate Wireless Personal Area Networks[Oct 2006]
Authors: Jianliang Zheng, Myung J. Lee, and Michael Anshel
Low rate wireless personal area networks (LR-WPANs) offer device level wireless
connectivity. They bring to light a host of new applications as well as enhance existing
applications. Due to their low cost, low power consumption and self-organization features,
LR-WPANs are ideal for applications such as public security, battle field monitoring,
inventory tracking, as well as home and office automation. Nevertheless, one critical issue,
security, needs to be solved before LR-WPANs are commonly accepted. Pursuing security in
LR-WPANs is a challenging task. On one hand, wireless communications are inherently
susceptible to interception and interference. On the other hand, most devices in LR-WPANs
are resource-constrained and lack physical safeguards. This paper presents a systematic
analysis of the threats faced by LR-WPANs with respect to the protocol stack defined by
IEEE 802.15.4 and the ZigBee Alliance. Attacks are modelled and their impacts are
evaluated. Some security problems within the current LR-WPAN security architecture are
identified and remedies are suggested. Countermeasures of various attacks are also given.
13
Title: Tree-Based Data Broadcast in IEEE 802.15.4 and ZigBee Networks [Nov 2006]
Authors : Gang Ding, , Zafer Sahinoglu, Philip Orlik, Jinyun Zhang and Bharat Bhargava
This paper studies efficient and simple data broadcast in IEEE 802.15.4-based ad
hoc networks (e.g., ZigBee). Since finding the minimum number of rebroadcast nodes in
general ad hoc networks is NP-hard, current broadcast protocols either employ heuristic
algorithms or assume extra knowledge such as position or two-hop neighbour table.
However, the ZigBee network is characterized as low data rate and low cost. It cannot
provide position or two-hop neighbour information, but it still requires an efficient broadcast
algorithm that can reduce the number of rebroadcast nodes with limited computation
complexity and storage space. Only one-hop neighbour information is needed; a partial list of
two-hop neighbors is derived without exchanging messages between neighbouring nodes.
The ZigBee forward node selection algorithm finds the minimum rebroadcast nodes set with
polynomial computation time and memory space. Using the proposed localized algorithms, it
is proven that the entire network is covered. Simulations are conducted to evaluate the
performance improvement in terms of the number of rebroadcast nodes, number of duplicated
receiving, coverage time, and communication overhead
Title: Routing in ZigBee: benefits from exploiting the IEEE 802.15.4 association
tree[Jan 2007]
Authors: Francesca Cuomo, Sara Della Luna, Ugo Monaco and Tommaso Melodia
An IEEE 802.15.4-based Wireless Sensor Network is considered, and the relationship
between the IEEE 802.15.4 topology formation mechanism and possible routing strategies at
the network layer is studied. Two alternative routing schemes proposed in the framework of
the ZigBee Alliance are analyzed. The first is the well-known Ad-hoc On demand Distance
Vector (AODV) routing protocol, which was designed for highly dynamic application
scenarios in wireless ad-hoc networks. The second is a tree-based routing scheme based on a
hierarchical structure established among nodes during the network formation phase. This
latter approach, referred to as HERA (Hierarchical Routing Algorithm) in the paper, routes
packets from sensors to sink based on the parent-child relationships established by the IEEE
802.15.4 topology formation procedure.It is to be noted that most sensor network scenarios
are concerned with delivery of packets from a series of static sensors to a single, static, sink.
14
Title: Address Assignment and Routing Schemes for ZigBee-Based Long-Thin Wireless
Sensor Networks[Mar 2007]
Authors: Meng-Shiuan Pan, Hua-Wei Fang, Yung-Chih Liu, and Yu-Chee Tseng
Wireless sensor networks (WSNs) have been extensively researched recently. This
paper makes two contributions to this field. First, we promote a new concept of long-thin
(LT)topology for WSNs, where a network may have a number of linear paths of nodes as
backbones connecting to each other. These backbones are to extend the network to the
intended coverage areas. At the first glance, a LT WSN only seems to be a special case of
numerous WSN topologies. However, we observe, from real deployment experiments, that
such a topology is quite general in many applications and deployments. The second
contribution is that we show that the address assignment and thus the tree routing scheme
defined in the original ZigBee specification may work poorly, if not fail, in a LT topology.
We thus propose simple, yet efficient, address assignment and routing schemes for a LT
WSN. Simulation results and prototyping experiences are also reported.
Title: Shortcut Tree Routing in ZigBee Networks[Nov 2007]
Authors: Taehong Kim, Daeyoung Kim, Noseong Park*, Seong-eun Yoo, Toms Snchez
Lpez
ZigBee is the emerging industrial standard for ad hoc networks based on IEEE
802.15.4. Due to characteristics such as low data rate, low price, and low power consumption,
ZigBee is expected to be used in wireless sensor networks for remote monitoring, home
control, and industrial automation. Since one of the most important goals is to reduce the
installation and running cost, ZigBee stack is embedded in small and cheap micro-controller
units. Since tree routing does not require any routing tables to send the packet to the
destination, it can be used in ZigBee end devices that have limited resources. However, tree
routing has the problem that the packets follow the tree topology to the destination even if the
destination is located nearby. We propose the shortcut tree routing protocol to reduce the
routing cost of ZigBee tree routing by using the neighbour table that is originally defined in
the ZigBee standard. While following the ZigBee tree routing algorithm, we suggest
forwarding the packet to the neighbour node if it can reduce the routing cost to the
destination. Simulation results show that the shortcut tree routing algorithm saves more than
30 percent of the hop count compared with ZigBee tree routing.
15
Title: Improvement Of Zigbee Routing Protocol Including Energy And Delay
Constraints[Feb 2008]
Authors: Najet Boughanmi and YeQiong Song
Besides energy constraint, wireless sensor networks should also be able to provide
bounded communication delay when they are used to support real time applications. In this
paper, we propose an improvement of ZigBee routing protocol integrating both energy and
delay constraints. By mathematical analysis and simulations, we have shown the efficiency of
this improvement. A successful deployment of real-time applications over WSNs needs to
satisfy the required timing properties under energy consumption constraints. As Zigbee
routing protocol does not address energy and delay issues together at the same time, we
propose in this paper a new routing metric is proposed.
Title: Transmission Power Requirements for Novel ZigBee Implants in the
Gastrointestinal Tract[Jun 2008]
Authors: Pietro Valdastri, Arianna Menciassi, and Paolo Dario
In this paper, a ZigBee multinode wireless monitoring platform based on commercial
components is presented. The performances of two nodes, introduced in different districts of
the GI tract, were assessed in vivo. A star network was established with an external data
collector, and the lowest levels of transmission power that the implant needed to establish
reliable wireless connections were recorded. These values were compared with international
regulatory levels for human safety and can be used as reference levels to estimate the implant
battery lifetime. Reliable communication can be established from the different districts of the
GI tract with values of transmission power that comply with international regulations. These
results can be the starting point for the development of novel and miniaturized sensor
networks that can be either implanted or worn by the patients and constitute a step toward the
goal of pervasive healthcare and WCE.
16
Title: Wireless Sensor Networks for Resources Tracking at Building Construction
Sites[Oct 2008]
Authors: SHEN Xuesong, CHEN Wu, LU Ming
This paper evaluate the technical feasibility of applying emerging wireless network
technologies for resources tracking at building construction sites. It first identifies practical
constraints in solving resource tracking problems in an enclosed or partially covered
environment. Then compare pros and cons of available localization principles and examine
the latest wireless communication technologies, including Wi-Fi, Bluetooth, Ultra-Wideband
(UWB) and ZigBee. And find that the ZigBee-based wireless sensor network and
the received signal strength indicator (RSSI) localization method are most promising to tackle
on-site tracking of construction resources. Finally, it anticipate some application challenges
associated with deploying wireless sensor networks for resources tracking in the practical
context.
Title: Social Network Analysis for Information Flow in Disconnected Delay-Tolerant
MANETs[may 2009]
Authors: Ossama Elizabeth M. Daly and Mads Haahr, Member, IEEE
Message delivery in sparse mobile ad hoc networks (MANETs) is difficult due to the
fact that the network graph is rarely (if ever) connected. A key challenge is to find a route
that can provide good delivery performance and low end-to-end delay in a disconnected
network graph where nodes may move freely. We cast this challenge as an information flow
problem in a social network. This paper presents social network analysis metrics that may be
used to support a novel and practical forwarding solution to provide efficient message
delivery in disconnected delay-tolerant MANETs. These metrics are based on social analysis
of a nodes past interactions and consists of three locally evaluated components: a nodes
betweenness centrality (calculated using ego networks), a nodes social similarity to the
destination node, and a nodes tie strength relationship with the destination node. We present
simulations using three real trace data sets to demonstrate that by combining these metrics
delivery performance may be achieved close to Epidemic Routing but with significantly
reduced overhead.
17
Title: UPnP-ZigBee Internetworking Architecture Mirroring a Multi-hop ZigBee
Network Topology[Aug 2009]
Authors: Seong Hoon Kim, Jeong Seok Kang, Hong Seong Park, Daeyoung Kim,
and Young-Joo Kim
In this paper, we present a UPnP-ZigBee internetworking architecture. Different from
traditional internetworking architectures which focus on integrating either wired networks or
single-hop wireless networks into UPnP networks, integrating ZigBee with UPnP is more
difficult because ZigBee nodes communicate over multi-hop wireless network, and further
their short addresses can be changed due to mobility of ZigBee nodes. A UPnP-ZigBee
gateway mirrors ZigBee network topology; therefore, it creates, terminates, and updates
virtual UPnP proxies according to ZigBee topology changes. Thus, the proposed
internetworking architecture dynamically and automatically integrates ZigBee devices into
the UPnP network and provides seamless internetworking between a multi-hop ZigBee
network and the UPnP network. We have demonstrated the proposed architecture by
implementing both the UPnP-ZigBee gateway and network monitoring functions and
integrating them together. By conducting experiments on physical test bed, we have shown
that the proposed architecture provides dynamic integration and seamless internetworking.
Title: A Lightweight Network Repair Scheme for Data Collection Applications in
ZigBee WSNs[Sep 2009]
Authors: Meng-Shiuan Pan and Yu-Chee Tseng
Data collection is a fundamental operation in wireless sensor networks (WSNs). A
quick converge cast solution is proposed for data collection in a ZigBee beacon-enabled tree
based WSN. However, it does not consider the network repair issue. When a ZigBee router
loses its link to its parent, all its descendants have to rejoin the network. The rejoining
procedure is time-consuming and may incur high communication overheads. The proposed
network repair scheme consists of a regular repair and an instant repair schemes.
Periodically, the network coordinator can issue regular repair to refresh the network (so as to
keep the network in good shape). During normal operations, if a router loses its parent, it tries
instant repair to reconnect to a new parent. Our design thus improves over ZigBee in that
nodes can continue their operations even during instant repair.
18
Title: Reliable Data Broadcast for Zigbee Wireless Sensor Networks[Sep 2010]
Authors: Tien-Wen Sung, Ting-Ting Wu, Chu-Sing Yang, Yueh-Min Huang
. As we know, the data transmission in the wireless networks is more unreliable than it is in
the wired network environment. Although the virtual carrier sensing scheme can be used in
the wireless unicast transmission, the multicast and broadcast still not utilize the
acknowledgement mechanism for reliable transmission. This is due to the acknowledgement
packets of broadcast transmission will cause much higher communication traffic and
overhead. Some previous related papers improved the broadcast reliability by introducing
redundant transmission and increasing coverage ratio of every receiver node, but there still
exists probability of packet loss and extra communication cost due to redundant broadcast.
This paper proposes an efficient acknowledgement-based approach for reliable data broadcast
in wireless sensor networks. Hierarchical acknowledgement mechanism, reduction of
rebroadcast packets and ACK packets, degree-based ACK/rebroadcast Jitter, and parent-
oriented retransmission are the key schemes to achieve the efficient data broadcast.
Simulation results show that the proposed schemes can efficiently reduce the
acknowledgement traffic as well as communication overhead and provide the high reliable
data broadcast transmission in ZigBee networks..
Title: Distributed Throughput Optimization for ZigBee Cluster-Tree Networks [Mar
2012]
Authors: Wenjing Yu-Kai Huang, Ai-Chun Pang, Pi-Cheng Hsiu, Weihua Zhuang, and
Pangfeng Liu
ZigBee, a unique communication standard designed for low-rate wireless personal area
networks, has extremely low complexity, cost, and power consumption for wireless
connectivity in inexpensive, portable, and mobile devices. Among the well known ZigBee
topologies, ZigBee cluster-tree is especially suitable for low-power and low-cost wireless
sensor networks because it supports power saving operations and light-weight routing. In a
constructed wireless sensor network, the information about some area of interest may require
further investigation such that more traffic will be generated. In this paper, we present an
adoptive-parent-based framework for a ZigBee cluster-tree network to increase bandwidth
utilization without generating any extra message exchange.
19
Title: Diagnosis of Failures in ZigBee Based Wireless Sensor Networks [Mar 2013]
Authors: Mumtaz M.Ali AL-Mukhtar , Teeb Hussein Hadi
In this work, based on the characteristics of ZigBee protocol, ZigBee technology is
used to model and simulate a wireless sensor network. Nodes failures and their effect on the
traffic are considered in different scenarios for cluster-tree topology to certify the reliability
of this communication network. The parameters: throughput, delay, data traffic sent, and data
traffic received are measured during these scenarios. Simulation results quantify the impact
of a ZigBee device failure on the performance factors. Overall effects of failures on the traffic
factors are considered to certify the reliability of this communication network. The results
indicate that throughput is low in case of ZR failure. Data traffic sent is low in case of ZR
failure. Data traffic received is low in case of ZR failure. Delay is high in case of ZED
failure. The result concludes that the coordinator failure prevents the whole network from
communicating. Router failure blocks a part of the network and thus may be less critical than
the coordinator failure. However, end device failure, usually, is not critical.
Title: Distributed Fault Tolerant Algorithm for Identifying Node Failures in Wireless
Sensor Networks[Apr 2013]
Authors: Navneet N Tewani, Neeharika Ithapu, K Raghava Rao, Sheik Nissar Sami, B. Sai
Pradeep,V. Krishna Deepak
A Wireless Sensor Network is a set of multiple connected components. Sometimes
due to the failure of some of its nodes, the sensor network communication fails. So that we
consider this problem of node(s) failure termed as cut from the remaining nodes of a
wireless sensor network. We propose an algorithm that allows (i) every node to detect when
the connectivity to a specially designated node has been lost, and (ii) one or more nodes (that
are connected to the special node after the cut) to detect the occurrence of the cut. The
algorithm proposed is distributed and asynchronous i.e. every node needs to communicate
with only those nodes that are within its communication range. The algorithm is based on the
iterative computation of the nodes. The convergence rate of the underlying iterative scheme is
independent of the size and structure of the network.
20
Title: Neighbour Table based Shortcut Tree Routingin ZigBee Wireless Networks[May
2013]
Authors: Taehong Kim,Seong Hoon Kim,Jinyoung Yang,Seong-eun Yoo and Daeyoung
Kim
The ZigBee tree routing is widely used in many resource-limited devices and
applications, since it does not require any routing table and route discovery overhead to send
a packet to the destination. However, the ZigBee tree routing has the fundamental limitation
that a packet follows the tree topology; thus, it cannot provide the optimal routing path. The
shortcut tree routing is fully distributed and compatible with ZigBee standard in that it only
utilizes addressing scheme and neighbour table without any changes of the specification. The
mathematical analysis proves that the 1- hop neighbour information improves overall
network performances by providing an efficient routing path and distributing the traffic load
concentrated on the tree links. In the performance evaluation, we show that the shortcut tree
routing achieves the comparable performance to AODV with limited overhead of neighbour
table maintenance as well as overwhelms the ZigBee tree routing in all the network
conditions such as network density.
Title: Energy-Efficient Routing Protocols in Wireless Sensor Networks: A Survey[Jun
2013]
Authors: Nikolaos A. Pantazis, Stefanos A. Nikolidakis and Dimitrios D. Vergados
The distributed nature and dynamic topology of Wireless Sensor Networks (WSNs)
introduces very special requirements in routing protocols that should be met. The most
important feature of a routing protocol, in order to be efficient for WSNs, is the energy
consumption and the extension of the networks lifetimeThe routing protocols belonging to
the first category can be further classified as flat or hierarchical. The routing protocols
belonging to the second category can be further classified as Query-based or Coherent and
non-coherent based or Negotiation-based. The routing protocols belonging to the third
category can be further classified as Location-based or Mobile Agent-based. The routing
protocols belonging to the fourth category can be further classified as QOS-based or
Multipath based. Then, an analytical survey on energy efficient routing protocols for WSNs
is provided. In this paper, the classification initially proposed by Al-Karaki, is expanded, in
order to enhance all the proposed papers since 2004 and to better describe which
issues/operations in each protocol illustrate/enhance the energy efficiency issues.
21
CHAPTER 3
EXISTING SYSTEM
3.1. Existing System
ZigBee is a specification formalized by the IEEE 802.15.4 standard for low-power
low-cost low-data-rate wireless personal area networks. A ZigBee network comprises the
following three types of devices: 1) a coordinator; 2) multiple routers; and 3) multiple end
devices. The coordinator performs the initialization, maintenance, and control functions in the
network. A router is responsible for routing data between the end devices and the coordinator.
An end device is not equipped with forwarding capability, and its hardware requirements are
minimized to control costs.
In ZigBee networks, a tree topology is often used to construct a wireless sensor
network for data delivery applications. in cluster tree and mesh networks, the devices
communicate with each other in a multihop fashion A device discovery procedure is triggered
if the central server cannot locate a certain mobile end device. During the procedure, the
central server simply floods the whole network with messages to locate the displaced end
device. However, flooding the network is costly in terms of resources, and during the
procedure, the network cannot accommodate multiple instances of rapid node mobility .
Thus, we need a more efficient and automatic approach for locating mobile end devices. In
many applications, the mobility patterns of sensor nodes are inherently regular due to the
geographical structure of the network or physical constraints. The regularity provides useful
information that can be exploited to construct a proper routing topology for sensing data
deliveries.
To improve the data delivery ratio, an approach is used that exploits the
aforementioned information to optimize the locations of routers and construct a mobility
robust tree topology in a ZigBee wireless network. The approach deploys routers and
constructs a topology with the property that mobile nodes will move along the constructed
data-forwarding path with high probability. Data will reach the target mobile nodes as long as
they are within the transmission range of any router on the forwarding path. In other words,
we choose the positions of the routers and design the tree topology so that most movements
are directed toward the root of the tree. To achieve this objective, we gather information
about node movements in the environment and construct a ZigBee tree topology framework.
22
In particular, the framework considers the regularity of the mobility patterns during the
construction of the tree and deployment of the routing nodes, and it incorporates an
overhearing mechanism for mobile nodes to further improve the data delivery ratio. And also
design heuristic and low-complexity algorithms for node deployment and tree construction
and analyze their performance in ZigBee networks.
3.2. Disadvantages
When constructing the tree topology, the nodes having maximum indegree are
selected. So if there are two nodes having same indegree the nodes will be selected randomly.
This will reduce the efficiency of the system. To overcome this disadvantage the proposed
system introduce capacity calculation of nodes to find the best node, when two or more nodes
have same indegree.
23
CHAPTER 4
PROPOSED SYSTEM
4.1. Proposed System
A mobile end device simply sends a packet, which is then forwarded to the
coordinator through the routers. Upon the reception of the downlink packet, the router simply
forwards it to the mobile end device and waits for an acknowledgement message from the
end device. If the mobile end device has moved from the last known location, the data
delivery fails, and the coordinator starts a search by broadcasting a message that asks for
information about the mobile end devices current location. Broadcast operations are
expensive in terms of bandwidth and power consumption. So the existing system deploys
routers and constructs a topology with the property that mobile nodes will move along the
constructed data-forwarding path with high probability. The nodes are selected in such a way
that the nodes having maximum indegree are included.
If two or more nodes have same indegree the nodes will be selected randomly. So in
the proposed system we introduce capacity calculation to find the best node. When two or
more nodes have same indegree, the capacity of each node is calculated and the node with
maximum capacity will be chosen.
4.2. Advantages
The proposed system allows to choose the best node when two or more nodes ,which
has maximum connectivity, have the same in-degree.
It will allow the network to find the best path by which the data will be delivered to
the destination.
24
CHAPTER 5
SYSTEM REQUIREMENTS
5.1. Hardware Requirements
Hard Disk : 40GB and above.
RAM : 512MB and above.
Processor : Pentium4 and above.
5.2. Software Requirements
Operating System : Windows XP
Simulator : NS2
Language : TCL
Software : Cygwin
25
CHAPTER 6
ARCHITECTURAL REPRESENTATION
6.1. System Architecture
In ZigBee networks, a device discovery procedure is triggered if the central server
cannot locate a certain mobile end device. During the procedure, the central server simply
floods the whole network with messages to locate the displaced end device. flooding the
network is costly in terms of resources, and during the procedure, the network cannot
accommodate multiple instances of rapid node mobility. In many applications, the mobility
patterns of sensor nodes are inherently regular due to the geographical structure of the
network or physical constraints. The regularity provides useful information that can be
exploited to construct a proper routing topology for sensing data deliveries. The approach
deploys routers and constructs a topology with the property that mobile nodes will move
along the constructed data-forwarding path with high probability. We also design heuristic
and low-complexity algorithms for node deployment and tree construction. There are three
such algorithms. The algorithm is implemented in the following three phases: 1) ZigBee node
deployment (ZND); 2) ZigBee coordinator decision (ZCD); and 3) ZigBee tree construction
(ZTC). The ZND phase determines the number and locations of router nodes, the ZCD phase
selects one of the routers as the coordinator, and the ZTC phase constructs an MRZT based
on the deployment in the previous two phases.
The nodes with maximum Indegree is selected for forwarding the packet. The
disadvantage of this system is that when two or more nodes have same indegree any node
will be selected randomly. This may reduce the efficiency. To overcome this drawback we
introduce capacity calculation. This algorithm calculates the capacity of each node and
compares it. Capacity means the ratio of packets that the node sends successfully out of
which it receives. Nodes having highest ratio is said to have highest capacity. This will
improve the efficiency of the system and improve the data delivery ratio.
26
Fig. 6.1 Capacity Calculation
Fig.6.2 Data Delivery
27
CHAPTER 7
MODULES
7.1 Node Deployment
7.2 Coordinator Decision.
7.3 Capacity Calculation
7.4 Flexible Routing
MODULES AND DESCRIPTION
7.1. Node Deployment
A ZigBee wireless sensor network is a collection of nodes cooperates with each
other and forms a network. There are three types of nodes in a ZigBee network.1)Coordinator
2)Router and 3)Mobile end device. For Initializing a network first a central server will
continuously send beacon signals for finding the neighboring nodes. On receiving this signals
the node will send an acknowledgement to the central server. This nodes will be registered in
the network.
Fig.7.1 Node Deployment
28
7.2. Coordinator Decision
The coordinator performs the initialization, maintenance, and control functions in the
network. This module will select the coordinator node in the network. For this, the indegree
of each node will be calculated. The node with maximum indegree will be selected as the
coordinator.
Fig.7.2 Coordinator Decision
7.3. Capacity Calculation
The nodes with maximum Indegree is selected for forwarding the packet. The
disadvantage of this system is that when two or more nodes have same indegree any node
will be selected randomly. This may reduce the efficiency. To overcome this drawback we
introduce capacity calculation. This algorithm calculates the capacity of each node and
compares it. Capacity means the ratio of packets that the node sends successfully out of
which it receives. Nodes having highest ratio is said to have highest capacity. This will
improve the efficiency of the system and improve the data delivery ratio.
29
Capacity
Fig.7.3 Capacity Calculation
7.4. Flexible Routing
In this module the data will be routed to the destination. First the sever will route the
data to the coordinator. Coordinator then routes the data to the mobile end device. Router
will be having the location of the mobile end devices. So the router will forward the data to
the mobile end devices.
Fig. 7.4 Flexible Routing
30
CHAPTER 8
DATA FLOW DIAGRAM
Figure 8.1 Data Flow Diagram
31
CHAPTER 9
CONCLUSION
This project proposes a scheme that exploits the regularity in node movements in
wireless ZigBee networks. It proposes three algorithms to construct a mobility based ZigBee
cluster tree topology. The primary objective of the proposed approach is to deploy the routers
and construct a tree topology that enables mobile end devices to move with high probability
in the direction of the routing paths. The proposed system implements the capacity
calculation to find the coordinator node. When two or more nodes have the same indegree the
proposed system will calculate the capacity of each node and selects the node with maximum
capacity as coordinator node. It will allow the network to find the best route through which
the data will be delivered to the destination.
32
CHAPTER 10
FUTURE ENHANCEMENT
As a future enhancement, we can improve the security in the Zigbee data
transmission by introducing some encryption algorithm.
33
CHAPTER 11
APPENDIX A
11. CODINGS
set udp0we [$ns_ create-connection UDP $n3 LossMonitor $n7 0]
set cbr0we [$udp0we attach-app Traffic/CBR]
$cbr0we set packetSize_ 1000
$cbr0we set interval_ .09
$ns_ at 12.75 "$n3 label Data_Sending"
$ns_ at 12.85 "$n3 label To_Destination"
$ns_ at 12.95 "$n3 label With_FileSize"
$ns_ at 13.05 "$n3 label 2MB=20J"
$ns_ at 13.15 "$n3 label Remaining=80J"
$ns_ at 13.25 "$n3 label Maintaining.."
$ns_ at 13.35 "$n3 label Node_3"
$ns_ at 12.75 "$cbr0we start"
$ns_ at 13.35 "$cbr0we stop"
set udp01qw [$ns_ create-connection UDP $n7 LossMonitor $n9 0]
set cbr01qw [$udp01qw attach-app Traffic/CBR]
$cbr01qw set packetSize_ 1000
$cbr01qw set interval_ .
$ns_ at 13.45 "$n7 label Data_Sending"
$ns_ at 13.55 "$n7 label To_Destination"
$ns_ at 13.65 "$n7 label Remaining=98J"
$ns_ at 13.75 "$n7 label Maintaining.."
$ns_ at 13.85 "$n7 label Node_7"
$ns_ at 13.75 "$n9 label Data_Received"
$ns_ at 13.85 "$n9 label From_Source"
$ns_ at 13.95 "$n9 label Node_9"
$ns_ at 13.45 "$cbr01qw start"
$ns_ at 13.85 "$cbr01qw stop"
34
udp0we [$ns_ create-connection UDP $n8 LossMonitor $n7 0]
set cbr0we [$udp0we attach-app Traffic/CBR]
$cbr0we set packetSize_ 1000
$cbr0we set interval_ .09
$ns_ at 13.75 "$n8 label Data_Sending"
$ns_ at 13.85 "$n8 label To_Destination"
$ns_ at 13.95 "$n8 label With_FileSize"
$ns_ at 14.05 "$n8 label 3MB=30J"
$ns_ at 14.15 "$n8 label Remaining=70J"
$ns_ at 14.25 "$n8 label Maintaining.."
$ns_ at 14.35 "$n8 label Node_8"
$ns_ at 13.75 "$cbr0we start"
$ns_ at 14.35 "$cbr0we stop"
set udp01qw [$ns_ create-connection UDP $n7 LossMonitor $n9 0]
set cbr01qw [$udp01qw attach-app Traffic/CBR]
$cbr01qw set packetSize_ 1000
$cbr01qw set interval_ .09
$ns_ at 13.45 "$n7 label Data_Sending"
$ns_ at 13.55 "$n7 label To_Destination"
$ns_ at 13.65 "$n7 label Remaining=95J"
$ns_ at 13.75 "$n7 label Maintaining.."
$ns_ at 13.85 "$n7 label Node_7"
$ns_ at 13.45 "$cbr01qw start"
$ns_ at 13.9 "$cbr01qw stop"
set udp01qwa [$ns_ create-connection UDP $n9 LossMonitor $n15 0]
set cbr01qwa [$udp01qwa attach-app Traffic/CBR]
$cbr01qwa set packetSize_ 1000
$cbr01qwa set interval_ .09
$ns_ at 13.95 "$n9 label Data_Sending"
$ns_ at 14.05 "$n9 label To_Destination"
35
$ns_ at 14.15 "$n9 label Remaining=97J"
$ns_ at 14.25 "$n9 label Maintaining.."
$ns_ at 14.35 "$n9 label Node_9"
$ns_ at 13.95 "$cbr01qwa start"
$ns_ at 14.35 "$cbr01qwa stop"
set udp01qwasx [$ns_ create-connection UDP $n1 LossMonitor $n15 0]
set cbr01qwasx [$udp01qwasx attach-app Traffic/CBR]
$cbr01qwasx set packetSize_ 1000
$cbr01qwasx set interval_ .09
$ns_ at 14.15 "$n1 label Monitoring"
$ns_ at 14.25 "$n1 label Other_Network"
$ns_ at 14.35 "$n1 label Nodes_Details&"
$ns_ at 14.45 "$n1 label Allowed"
$ns_ at 14.55 "$n1 label Network_2"
$ns_ at 14.15 "$cbr01qwasx start"
$ns_ at 14.55 "$cbr01qwasx stop"
set udp01qwas [$ns_ create-connection UDP $n15 LossMonitor $n14 0]
set cbr01qwas [$udp01qwas attach-app Traffic/CBR]
$cbr01qwas set packetSize_ 1000
$cbr01qwas set interval_ .09
$ns_ at 14.40 "$n15 label Data_Sending"
$ns_ at 14.50 "$n15 label To_Destination"
$ns_ at 14.60 "$n15 label Remaining=97J"
$ns_ at 14.70 "$n15 label Maintaining.."
$ns_ at 14.80 "$n15 label Node_15"
$ns_ at 14.75 "$n14 label Data_Received"
$ns_ at 14.85 "$n14 label From_Source"
$ns_ at 14.95 "$n14 label Destination"
$ns_ at 14.35 "$cbr01qwas start"
36
$ns_ at 15.0 "$cbr01qwas stop"
set udp0we [$ns_ create-connection UDP $n3 LossMonitor $n7 0]
set cbr0we [$udp0we attach-app Traffic/CBR]
$cbr0we set packetSize_ 1000
$cbr0we set interval_ .09
$ns_ at 12.75 "$n3 label Data_Sending"
$ns_ at 12.85 "$n3 label To_Destination"
$ns_ at 12.95 "$n3 label With_FileSize"
$ns_ at 13.05 "$n3 label 2MB=20J"
$ns_ at 13.15 "$n3 label Remaining=80J"
$ns_ at 13.25 "$n3 label Maintaining.."
$ns_ at 13.35 "$n3 label Node_3"
$ns_ at 12.75 "$cbr0we start"
$ns_ at 13.35 "$cbr0we stop"
set udp01qw [$ns_ create-connection UDP $n7 LossMonitor $n9 0]
set cbr01qw [$udp01qw attach-app Traffic/CBR]
$cbr01qw set packetSize_ 1000
$cbr01qw set interval_ .09
$ns_ at 13.45 "$n7 label Data_Sending"
$ns_ at 13.55 "$n7 label To_Destination"
$ns_ at 13.65 "$n7 label Remaining=98J"
$ns_ at 13.75 "$n7 label Maintaining.."
$ns_ at 13.85 "$n7 label Node_7"
$ns_ at 13.75 "$n9 label Data_Received"
$ns_ at 13.85 "$n9 label From_Source"
$ns_ at 13.95 "$n9 label Node_9"
$ns_ at 13.45 "$cbr01qw start"
$ns_ at 13.85 "$cbr01qw stop"
############################## Neighbor node selected 2 round ######
37
set udp0we [$ns_ create-connection UDP $n10 LossMonitor $n11 0]
set cbr0we [$udp0we attach-app Traffic/CBR]
$cbr0we set packetSize_ 1000
$cbr0we set interval_ .09
$ns_ at 5.75 "$n10 label Connect"
$ns_ at 5.85 "$n10 label For_Neighbor"
$ns_ at 5.95 "$n10 label Nodes"
$ns_ at 6.05 "$n10 label Total_Node=2"
$ns_ at 6.15 "$n10 label Connected"
$ns_ at 6.25 "$n10 label Successfully"
$ns_ at 6.35 "$n10 label Node_10"
$ns_ at 5.75 "$cbr0we start"
$ns_ at 6.35 "$cbr0we stop"
set udp01qw [$ns_ create-connection UDP $n10 LossMonitor $n15 0]
set cbr01qw [$udp01qw attach-app Traffic/CBR]
$cbr01qw set packetSize_ 1000
$cbr01qw set interval_ .09
$ns_ at 5.85 "$cbr01qw start"
$ns_ at 6.40 "$cbr01qw stop"
##################
set udp0sa [$ns_ create-connection UDP $n11 LossMonitor $n10 0]
set cbr0sa [$udp0sa attach-app Traffic/CBR]
$cbr0sa set packetSize_ 1000
$cbr0sa set interval_ .09
$ns_ at 6.45 "$n11 label Connect"
$ns_ at 6.55 "$n11 label For_Neighbor"
38
$ns_ at 6.65 "$n11 label Nodes"
$ns_ at 6.75 "$n11 label Total_Node=2"
$ns_ at 6.85 "$n11 label Connected"
$ns_ at 6.95 "$n11 label Successfully"
$ns_ at 7.05 "$n11 label Node_11"
$ns_ at 6.45 "$cbr0sa start"
$ns_ at 7.05 "$cbr0sa stop"
set udp01mn [$ns_ create-connection UDP $n11 LossMonitor $n12 0]
set cbr01mn [$udp01mn attach-app Traffic/CBR]
$cbr01mn set packetSize_ 1000
$cbr01mn set interval_ .09
$ns_ at 6.5 "$cbr01mn start"
$ns_ at 7.10 "$cbr01mn stop"
#####################
set udp0i [$ns_ create-connection UDP $n12 LossMonitor $n11 0]
set cbr0i [$udp0i attach-app Traffic/CBR]
$cbr0i set packetSize_ 1000
$cbr0i set interval_ .09
$ns_ at 7.05 "$n12 label Connect
$ns_ at 7.15 "$n12 label For_Neighbor"
$ns_ at 7.25 "$n12 label Nodes"
$ns_ at 7.35 "$n12 label Total_Node=2"
$ns_ at 7.45 "$n12 label Connected"
$ns_ at 7.55 "$n12 label Successfully"
$ns_ at 7.65 "$n12 label Node_12"
$ns_ at 7.05 "$cbr0i start"
$ns_ at 7.65 "$cbr0i stop"
set udp01nb [$ns_ create-connection UDP $n12 LossMonitor $n13 0]
39
set cbr01nb [$udp01nb attach-app Traffic/CBR]
$cbr01nb set packetSize_ 1000
$cbr01nb set interval_ .09
$ns_ at 7.15 "$cbr01nb start"
$ns_ at 7.7 "$cbr01nb stop"
##################
set udp0iy [$ns_ create-connection UDP $n13 LossMonitor $n11 0]
set cbr0iy [$udp0iy attach-app Traffic/CBR]
$cbr0iy set packetSize_ 1000
$cbr0iy set interval_ .09
$ns_ at 7.75 "$n13 label Connect"
$ns_ at 7.85 "$n13 label For_Neighbor"
$ns_ at 7.95 "$n13 label Nodes"
$ns_ at 8.05 "$n13 label Total_Node=3"
$ns_ at 8.15 "$n13 label Connected"
$ns_ at 8.25 "$n13 label Successfully"
$ns_ at 8.35 "$n13 label Node_13"
$ns_ at 7.75 "$cbr0iy start"
$ns_ at 8.35 "$cbr0iy stop"
set udp01tt [$ns_ create-connection UDP $n13 LossMonitor $n12 0]
set cbr01tt [$udp01tt attach-app Traffic/CBR]
$cbr01tt set packetSize_ 1000
$cbr01tt set interval_ .09
$ns_ at 7.85 "$cbr01tt start"
$ns_ at 8.4 "$cbr01tt stop"
set udp01ttq [$ns_ create-connection UDP $n13 LossMonitor $n14 0]
set cbr01ttq [$udp01ttq attach-app Traffic/CBR]
40
$cbr01ttq set packetSize_ 1000
$cbr01ttq set interval_ .09
$ns_ at 7.85 "$cbr01ttq start"
$ns_ at 8.4 "$cbr01ttq stop"
##################
set udp0bg [$ns_ create-connection UDP $n14 LossMonitor $n13 0]
set cbr0bg [$udp0bg attach-app Traffic/CBR]
$cbr0bg set packetSize_ 1000
$cbr0bg set interval_ .09
$ns_ at 8.45 "$n14 label Connect"
$ns_ at 8.55 "$n14 label For_Neighbor"
$ns_ at 8.65 "$n14 label Nodes"
$ns_ at 8.75 "$n14 label Total_Node=2"
$ns_ at 8.85 "$n14 label Connected"
$ns_ at 8.95 "$n14 label Successfully"
$ns_ at 9.05 "$n14 label Node_14"
$ns_ at 8.75 "$cbr0bg start"
$ns_ at 9.05 "$cbr0bg stop"
##################
set udp0xz [$ns_ create-connection UDP $n15 LossMonitor $n10 0]
set cbr0xz [$udp0xz attach-app Traffic/CBR]
$cbr0xz set packetSize_ 1000
$cbr0xz set interval_ .09
$ns_ at 9.0 "$n15 label Connect"
$ns_ at 9.1 "$n15 label For_Neighbor"
$ns_ at 9.2 "$n15 label Nodes"
$ns_ at 9.3 "$n15 label Total_Node=2"
41
$ns_ at 9.4 "$n15 label Connected"
$ns_ at 9.5 "$n15 label Successfully"
$ns_ at 9.6 "$n15 label Node_15"
$ns_ at 9.0 "$cbr0xz start"
$ns_ at 9.6 "$cbr0xz stop"
set udp01v [$ns_ create-connection UDP $n15 LossMonitor $n14 0]
set cbr01v [$udp01v attach-app Traffic/CBR]
$cbr01v set packetSize_ 1000
$cbr01v set interval_ .09
$ns_ at 9.1 "$cbr01v start"
$ns_ at 9.6 "$cbr01v stop"
##################
set udp01zn [$ns_ create-connection UDP $n1 LossMonitor $n13 0]
set cbr01zn [$udp01zn attach-app Traffic/CBR]
$cbr01zn set packetSize_ 1000
$cbr01zn set interval_ .09
$ns_ at 10.0 "$n1 label Select"
$ns_ at 10.1 "$n1 label Co-ordinate_Node"
$ns_ at 10.1 "$n13 label Co-ordinate_Node"
$ns_ at 10.2 "$n1 label For_Higher"
$ns_ at 10.3 "$n1 label Connectivity"
$ns_ at 10.4 "$n1 label Available"
$ns_ at 10.5 "$n1 label Successfully"
$ns_ at 10.6 "$n1 label Network_2"
$ns_ at 10.0 "$cbr01zn start"
$ns_ at 10.6 "$cbr01zn stop"
#############################
42
############################## Neighbor node selected 3 round ######
set udp0we [$ns_ create-connection UDP $n16 LossMonitor $n18 0]
set cbr0we [$udp0we attach-app Traffic/CBR]
$cbr0we set packetSize_ 1000
$cbr0we set interval_ .09
$ns_ at 5.75 "$n16 label Connect"
$ns_ at 5.85 "$n16 label For_Neighbor"$ns_ at 5.95 "$n16 label Nodes"
$ns_ at 6.05 "$n16 label Total_Node=1"
$ns_ at 6.15 "$n16 label Connected"
$ns_ at 6.25 "$n16 label Successfully"
$ns_ at 6.35 "$n16 label Node_16"
$ns_ at 5.75 "$cbr0we start"
$ns_ at 6.35 "$cbr0we stop"
##################
set udp0sa [$ns_ create-connection UDP $n18 LossMonitor $n16 0]
set cbr0sa [$udp0sa attach-app Traffic/CBR]
$cbr0sa set packetSize_ 1000
$cbr0sa set interval_ .09
$ns_ at 6.45 "$n18 label Connect"
$ns_ at 6.55 "$n18 label For_Neighbor"
$ns_ at 6.65 "$n18 label Nodes"
$ns_ at 6.75 "$n18 label Total_Node=2"
$ns_ at 6.85 "$n18 label Connected"
$ns_ at 6.95 "$n18 label Successfully"
$ns_ at 7.05 "$n18 label Node_18"
$ns_ at 6.45 "$cbr0sa start"
$ns_ at 7.05 "$cbr0sa stop"
43
############################## Neighbor node selected 1 round ######
set udp0we [$ns_ create-connection UDP $n2 LossMonitor $n16 0]
set cbr0we [$udp0we attach-app Traffic/CBR]
$cbr0we set packetSize_ 1000
$cbr0we set interval_ .09
$ns_ at 15.5 "$n2 label Monitoring"
$ns_ at 15.6 "$n2 label EverySeconds"
$ns_ at 15.7 "$n2 label To_AllSubnodes"
$ns_ at 15.8 "$n2 label Network_3"
$ns_ at 16.1 "$n16 label Node_16"
$ns_ at 15.5 "$cbr0we start"
$ns_ at 16.1 "$cbr0we stop"
set udp01qw [$ns_ create-connection UDP $n2 LossMonitor $n17 0]
set cbr01qw [$udp01qw attach-app Traffic/CBR]
$cbr01qw set packetSize_ 1000
$cbr01qw set interval_ .09
$ns_ at 15.85 "$n17 label Node_17"
$ns_ at 15.55 "$cbr01qw start"
$ns_ at 15.85 "$cbr01qw stop"
set udp01qwa [$ns_ create-connection UDP $n2 LossMonitor $n18 0]
set cbr01qwa [$udp01qwa attach-app Traffic/CBR]
$cbr01qwa set packetSize_ 1000
$cbr01qwa set interval_ .09
$ns_ at 15.9 "$n18 label Node_18"
$ns_ at 15.6 "$cbr01qwa start"
$ns_ at 15.9 "$cbr01qwa stop"
44
set udp01qwasx [$ns_ create-connection UDP $n2 LossMonitor $n19 0]
set cbr01qwasx [$udp01qwasx attach-app Traffic/CBR]
$cbr01qwasx set packetSize_ 1000
$cbr01qwasx set interval_ .09
$ns_ at 16.0 "$n19 label Node_19"
$ns_ at 15.7 "$cbr01qwasx start"
$ns_ at 16.0 "$cbr01qwasx stop"
set udp01qwas [$ns_ create-connection UDP $n2 LossMonitor $n20 0]
set cbr01qwas [$udp01qwas attach-app Traffic/CBR]
$cbr01qwas set packetSize_ 1000
$cbr01qwas set interval_ .09
$ns_ at 16.1 "$n20 label Node_20"
$ns_ at 15.8 "$cbr01qwas start"
$ns_ at 16.1 "$cbr01qwas stop"
set udp01qwasa [$ns_ create-connection UDP $n2 LossMonitor $n21 0]
set cbr01qwasa [$udp01qwasa attach-app Traffic/CBR]
$cbr01qwasa set packetSize_ 1000
$cbr01qwasa set interval_ .09
$ns_ at 16.2 "$n21 label Node_21"
$ns_ at 15.9 "$cbr01qwasa start"
$ns_ at 16.2 "$cbr01qwasa stop"
45
CHAPTER 12
APPENDIX B
12. COMPARISION TABLE
Existing System Proposed System
Coordinator node is selected using
indegree calculation.
Coordinator node is selected using
capacity calculation.
Nodes through which data is routed
are selected randomly.
Best path is selected through which
data is delivered to the destination.
Sometimes delay is high because data
is routed through randomly selected
nodes.
Delay will be less as data is routed
through best path always.
46
CHAPTER 13
APPENDIX C
13. SCREENSHOTS
Network Initialization
47
Co-ordinator Selection
48
Capacity calculation
49
Flexible Routing
50
End-End Delay
51
Packet Delivery Ratio
52
Energy Consumption
53
Throughput
54
REFERENCES
[1] Krishnendu Chakrabarty, S.Sitharama Iyengar, Hairong Qi, and Eungchun Cho, Grid
Coverage for Surveillance and Target Location in Distributed Sensor Networks, in
Proc. IEEE ICC,DEC 2002, pp. 16.
[2] Meng-Shiuan Pan and Yu-Chee Tseng, ZigBee Wireless Sensor Networks and Their
Applications, IEEE Commun. Mag., vol. 40, no. 8, pp. 102114, Jan2005.
[3] Bilel NEFZI and Ye-Qiong Song, Performance Analysis And Improvement Of
Zigbee Routing Protocol, Comput. Netw., vol. 38, no. 4, pp. 393422,Feb 2006.
[4] Jianliang Zheng, Myung J. Lee, and Michael Anshel, Toward Secure Low Rate
Wireless Personal Area Networks, in Proc. ACM WSNA,Oct 2006, pp. 8897.
[5] Gang Ding, , Zafer Sahinoglu, Philip Orlik, Jinyun Zhang and Bharat
Bhargava,Tree-Based Data Broadcast in IEEE 802.15.4 and ZigBee Networks, Ad
Hoc Netw., vol. 3, no. 3, pp. 325349, Nov 2006.
[6] Z. Alliance, ZigBee Specifications 2006. [Online]. Available: http://www.zigbee.org/
[7] Francesca Cuomo, Sara Della Luna, Ugo Monaco and Tommaso Melodia , Teeb
Hussein Hadi, Routing in ZigBee: benefits from exploiting the IEEE 802.15.4
association tree, Proc. IEEE, vol. 93, no. 6, pp. 11301151, Jan. 2007.
[8] Meng-Shiuan Pan, Hua-Wei Fang, Yung-Chih Liu, and Yu-Chee Tseng, Address
Assignment and Routing Schemes for ZigBee-Based Long-Thin Wireless Sensor
Networks, in Proc. IEEE WiCom, Mar 2007. pp. 30633066.
[9] Taehong Kim, Daeyoung Kim, Noseong Park*, Seong-eun Yoo, Toms Snchez
Lpez , Shortcut Tree Routing in ZigBee Networks, in Proc. ACM SIGMOBILE
HealthNet, 2008, pp. 3742.
[10] Najet Boughanmi and YeQiong Song, Improvement Of Zigbee Routing Protocol
Including Energy And Delay Constraints, in Proc. IEEE AICT, Jun 2008, pp. 1520.
[11] Pietro Valdastri, Arianna Menciassi, and Paolo Dario, Transmission Power
Requirements for Novel ZigBee Implants in the Gastrointestinal Tract in Proc.
Second IEEEWorkshop on Dependability and Security in Sensor Networks and
Systems, Oct 2008, pp. 1022.
[12] SHEN Xuesong, CHEN Wu, LU Ming, Wireless Sensor Networks for Resources
Tracking at Building Construction Sites, in Proc. IEEE ICC, May 2009, pp. 16.
55
[13] Pietro Valdastri, Arianna Menciassi, and Paolo Dario, Transmission Power
Requirements for Novel ZigBee Implants in the Gastrointestinal Tract, IEEE Trans.
Parallel Distrib. Syst., vol. 20, no. 11, pp. 16981712, Aug 2009.
[14] Meng-Shiuan Pan and Yu-Chee Tseng, ZigBee Wireless Sensor Networks and Their
Applications , in Proc. ECTI-CON, Sep 2009, pp. 303606.
[15] SHEN Xuesong, CHEN Wu, LU Ming, Wireless Sensor Networks for Resource
Tracking at Building Construction Sites, in Proc. IEEE IECON, 2012, pp. 46 51.
[16] Osama Elizabeth M. Daly and Mads Haahr, Member, IEEE,Social Network Analysis
for Information Flow in Disconnected Delay-Tolerant MANETs,ISWC 2013.
[17] Seog Hoon Kim, Jeong Seok Kang, Hong Seong Park, Daeyoung Kim, UPnP-ZigBee
Internetworking Architecture Mirroring a Multi-hop ZigBee Network Topology, in
Proc. IEEE ICC, Mar 2013, pp. 16.
[18] Meng-Shiuan Pan and Yu-Chee Tseng, A Lightweight Network Repair Scheme for
Data Collection Applications in ZigBee WSNs, in Proc. IEEE ICC, Apr 2013
[19] Kijm,Seong Honon Kim,Jinyoung Yang, Seong- eun Yoo and Daeyoung Kim,
Neighbour Table based Shortcut Tree Routing in ZigBee Wireless Networks, in
Proc. IEEE ICC, 2013.
[20] Nikolaos A. Pantazis, Stefanos A. Nikolidakis and Dimitrios D. Vergados, Energy-
Efficient Routing Protocols in WirelessSensor Networks: A Survey, in Proc. IEEE
ICC, 2013, pp.9-23.
You might also like
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Cloud PaperDocument4 pagesCloud PaperSona NelsonNo ratings yet
- WSNDocument77 pagesWSNSona NelsonNo ratings yet
- Wireless Sensor NetworkDocument7 pagesWireless Sensor NetworkSona NelsonNo ratings yet
- Unit 5 Mesh Networks Upto 802Document26 pagesUnit 5 Mesh Networks Upto 802Sona NelsonNo ratings yet
- 1303 5274v1 PDFDocument6 pages1303 5274v1 PDFSona NelsonNo ratings yet
- IEEE Outline FormatDocument3 pagesIEEE Outline FormatAlex HerrmannNo ratings yet
- A Secure and Reliable Bootstrap ArchitectureDocument4 pagesA Secure and Reliable Bootstrap ArchitectureSona NelsonNo ratings yet
- Challenge Based Identification System For Banking ServerDocument4 pagesChallenge Based Identification System For Banking ServerSona NelsonNo ratings yet
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (120)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Scheme of Work Writing Baby First TermDocument12 pagesScheme of Work Writing Baby First TermEmmy Senior Lucky100% (1)
- Computer Keyboard Shortcut Keys PDFDocument7 pagesComputer Keyboard Shortcut Keys PDFmuhammad sohail janjuaNo ratings yet
- A Lifetime of OpportunityDocument24 pagesA Lifetime of OpportunityCaleb Newquist100% (1)
- (SQP2) Sample Question Paper 2Document2 pages(SQP2) Sample Question Paper 2Vraj M BarotNo ratings yet
- Discrete Mathematics Sets Relations FunctionsDocument15 pagesDiscrete Mathematics Sets Relations FunctionsMuhd FarisNo ratings yet
- CIVL4903 2014 Semester 2 StudentDocument3 pagesCIVL4903 2014 Semester 2 StudentSuman SahaNo ratings yet
- Graham HoltDocument4 pagesGraham HoltTung NguyenNo ratings yet
- Sample PREP-31 Standard Sample Preparation Package For Rock and Drill SamplesDocument1 pageSample PREP-31 Standard Sample Preparation Package For Rock and Drill SampleshNo ratings yet
- Questionnaire of Measuring Employee Satisfaction at Bengal Group of IndustriesDocument2 pagesQuestionnaire of Measuring Employee Satisfaction at Bengal Group of IndustriesMuktadirhasanNo ratings yet
- Ignou Solved Assignment MS-07Document2 pagesIgnou Solved Assignment MS-07vikasmishraelexNo ratings yet
- Manual ViscosimetroDocument55 pagesManual ViscosimetroLUIS XV100% (1)
- Arts & Science: Government First Grade College, AlavandiDocument5 pagesArts & Science: Government First Grade College, AlavandiAnonymous cyZVcDeNo ratings yet
- Understanding Culture, Society, and Politics Quarter 2 - Module 1Document21 pagesUnderstanding Culture, Society, and Politics Quarter 2 - Module 1Allaine's ChannelNo ratings yet
- Thesis Chapter IiiDocument6 pagesThesis Chapter IiiJohn Rafael AtienzaNo ratings yet
- A Comprehensive Guide To Oracle Partitioning With SamplesDocument36 pagesA Comprehensive Guide To Oracle Partitioning With SamplesSreenivasa Reddy GopireddyNo ratings yet
- Remaking The Indian Historians CraftDocument9 pagesRemaking The Indian Historians CraftChandan BasuNo ratings yet
- Stone ColumnDocument116 pagesStone ColumnNur Farhana Ahmad Fuad100% (1)
- HP SMART ARRAY 641 USER GUIDEDocument69 pagesHP SMART ARRAY 641 USER GUIDEMichele BarbaNo ratings yet
- Eng 105 S 17 Review RubricDocument1 pageEng 105 S 17 Review Rubricapi-352956220No ratings yet
- Genogram and Eco GramDocument5 pagesGenogram and Eco GramGitichekimNo ratings yet
- MercerDocument33 pagesMercersadir16100% (4)
- 111Document16 pages111Squall1979No ratings yet
- Perkembangan Kurikulum USADocument25 pagesPerkembangan Kurikulum USAFadhlah SenifotoNo ratings yet
- Connections I V2.1.0.aDocument72 pagesConnections I V2.1.0.ajh50000No ratings yet
- PyramidsDocument10 pagesPyramidsapi-355163163No ratings yet
- Phoenix Journal # 246: by Gyeorgos Ceres HatonnDocument126 pagesPhoenix Journal # 246: by Gyeorgos Ceres HatonnLa Regina del VaporeNo ratings yet
- Mini Test PBD - SpeakingDocument4 pagesMini Test PBD - Speakinghe shaNo ratings yet
- Jillin ExplosionDocument10 pagesJillin ExplosionArjun ManojNo ratings yet
- Injection Machine RobotDocument89 pagesInjection Machine Robotphild2na250% (2)
- Discovery Issues Resolution Naga NotesDocument7 pagesDiscovery Issues Resolution Naga NotesNagaPrasannaKumarKakarlamudi100% (1)