Professional Documents
Culture Documents
Public Key Cryptosystem Using Improved Rabin Algorithm For Wireless Sensor Networks
Uploaded by
editor_ijcat0 ratings0% found this document useful (0 votes)
16 views6 pagesWireless Sensor Networks have observed a wide variety of applications in security areas such as defense, ecological etc. Providing security in such complications has made Wireless Sensor Networks security a challenge. This system tracks the location of sensor nodes and the location of the nodes will become the input for key generation phase. The communication between the server and the sensor will take place by encrypting the location address of the respected sensor.
Original Description:
Original Title
Public Key Cryptosystem Using Improved Rabin Algorithm for Wireless Sensor Networks
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentWireless Sensor Networks have observed a wide variety of applications in security areas such as defense, ecological etc. Providing security in such complications has made Wireless Sensor Networks security a challenge. This system tracks the location of sensor nodes and the location of the nodes will become the input for key generation phase. The communication between the server and the sensor will take place by encrypting the location address of the respected sensor.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
16 views6 pagesPublic Key Cryptosystem Using Improved Rabin Algorithm For Wireless Sensor Networks
Uploaded by
editor_ijcatWireless Sensor Networks have observed a wide variety of applications in security areas such as defense, ecological etc. Providing security in such complications has made Wireless Sensor Networks security a challenge. This system tracks the location of sensor nodes and the location of the nodes will become the input for key generation phase. The communication between the server and the sensor will take place by encrypting the location address of the respected sensor.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 6
IJCAT - International Journal of Computing and Technology
Volume 1, Issue 1, February 2014
www.IJCAT.org
24
Public Key Cryptosystem using Improved Rabin
Algorithm for Wireless Sensor Networks
1
Aaisha Jabeen Siddiqui,
2
Praveen Sen ,
3
Jagdish Pimple
1, 3
Computer Science & Engineering, RTM Nagpur University, Nagpur Institute of Technology
Nagpur, Maharashtra, India
2
Information Technology, RTM Nagpur University, Nagpur Institute of Technology
Nagpur, Maharashtra, India
Abstract - Wireless Sensor Networks are one of the most
popular areas of research now days. These types of networks
have observed a wide variety of applications in security areas
such as defense, ecological etc. These applications are highly
dependent on monitoring sensitive information such as
movement of particulars, detecting and tracking of location etc.
Providing security in such complications has made Wireless
Sensor Networks security a challenge. As sensor nodes are
powered by batteries, energy efficiency becomes a critical aspect
in such type of networks and because of this many security
protocols proposed earlier for Wireless Sensor Networks are
proved out to be expensive. In this paper, we have focused on a
security protocol which provides a strong level security and also
uses the battery of the sensor nodes efficiently. The proposed
work is tested on confidentiality and integrity of data and
authenticity in communication. This system tracks the location
of sensor nodes and the location of the nodes will become the
input for key generation phase. The communication between the
server and the sensor will take place by encrypting the location
address of the respected sensor.
Keywords - Security in WSN, Rabin public key
cryptosystem, CRT, Java Eclipse, Android SDK.
1. Introduction
A wireless sensor network is a collection of wireless nodes
that work in a cooperative manner. These nodes have self
processing capabilities. They may contain different types
of memory. They exchange information about their
environments/ surroundings with each other or to a base
station [1]. While doing this tremendous/ intense security
is necessary if the application is used for military (sensing
or) surveillance. The energy of the batteries has to be
made to last as long as possible. The use of a
cryptographically algorithm should save both time and
energy. Various other security algorithms implemented on
WSNs have proved to be expensive and consume more
energy. WSNs are unprotected to various types of attacks
or to node compromises that exploit various
susceptibilities of protocols and threaten the authenticity,
confidentiality and integrity of the information.
Encryption-Decryption algorithm is categorized as
symmetric and asymmetric. Symmetric is a secret key
algorithm which depends on single key. And Asymmetric
algorithm is a public key cryptosystem which makes it
harder at factorization.Many asymmetric algorithms have
been used for secure communication to wireless sensor
networks. Because of the large keys used they take more
execution time which uses up the batteries of the nodes.
RSA and Ecliptic Curves, which are asymmetric
algorithms implemented on WSNs, use large keys. Both
require large prime numbers as input to the key
generation phase and because of this take more execution
time. An important aspect of WSNs is saving battery
power. If we reduce the execution time of the algorithm, it
will reduce battery power consumption.
The proposed algorithm Rabin is an asymmetric
algorithm which is difficult at factorization/ to factorize.
This system will first track the location of the sensor
nodes, then their latitude and longitude value will become
keys for encrypting the sensed data. For decryption, the
Chinese remainder theorem is implemented, along with
two modular exponentiations.
As key size becomes small here, this system proves to be
more efficient than any other security algorithm.Hence,
for authenticity and non-repudiation security
requirements, asymmetric algorithms are implemented on
wireless sensor networks for hard mathematical
factorization. [2], [3], [4], [5] are several public-key
system protocols proposed for wireless sensor networks.
IJCAT - International Journal of Computing and Technology
Volume 1, Issue 1, February 2014
www.IJCAT.org
25
2. Background and Related Work
We present a location based authentication protocol for
sensors in a secure and efficient manner. Because it is
location based key pairs will be different with any change
in distance and direction.
To give more prospective to our proposed authentication
algorithm, this section review resulting performance of
different protocols used for securing sensor nodes.
A study in [2] shows that this paper has proposed a
protocol based public key cryptography for outside entity
authentication and session key generation.
Communication between the base station and the sensors
is through private key cryptography and communication
between external entity and base station is through public
key cryptography. According to the paper, system can be
prevented from node comprise attack and traffic analysis
attack.
In [3], symmetric key based protocol has been proposed
for secure communication in wireless sensor networks.
This paper investigates various attacks on cluster base
data gathering protocol and tries to give a symmetric key
based solution to it. Analysis on paper results shows that
attacks like spoofed, altered or replayed can be avoided by
adopting a symmetric technique. This system is reliable
only for smaller networks as single key usage can make
guessing attacks strong.
In [4], Rabin public key cryptography is adopted for
mobile network authentication. In this, mobile starts the
protocol by sending its identification number to the
server. The server stores mobile ID for the purpose of
authentication. According to the algorithm, it selects large
prime numbers as a key pair and transfers this to
encryption phase. Cipher text is calculated by applying
public key. Using CRT, validity of the cipher text is
checked. Execution time taken by the algorithm is 20
ms/byte.
In [5], a study is conducted to investigate the fast
developing security systems in the field of wireless
information security. ECCs uses smaller key size to
provide high security and high speed in a low bandwidth.
Due to their difficulty in discrete logarithmic problem,
execution time for ECC is 120 ms/byte according to the
result comparison in [6].As wireless sensor nodes are
battery dependant the system taking more time will not be
efficient. The paper also discusses issues involved in
implementing Elliptic Curve Cryptography (ECC). It
provides a brief explanation about ECC basic theory,
implementation, and also provides guidance for further
reading by referring to cryptography techniques.
In paper [6], a 160 bit ECC processor is proposed. The
implementation presented in this paper chooses an ECC
based authentication technique with a key size of 160 bits
as it provides strong security and can be used for a longer
time. According to the paper, the time required by single
point multiplication is good and the time consumed for
single 160 bit multiplication at 10 MHz is 0.39 seconds.
In this paper [7], an Identity authentication scheme has
been implemented in wireless peer-to-peer network.
Proposed scheme apply a hybrid P2P topology and tickets
issued by super peers to perform the user mutual
authentication. Also presented a quick re-authentication
technique dealing with non-permanent broken down link
to simplify the authentication procedure and improve the
efficiency. Scheme can resist most malicious attack
effectively.In [8], RSA public key cryptography has been
proposed as a solution to security in wireless sensor
networks. Although RSA uses large key size, execution
time is more as compared to Rabin authentication
algorithm proposed in []. According to comparative result
RSA takes 40 ms/bytes to execute. RSA for wireless
sensor networks proved out to be cost worthy and
inefficient. In this paper [9], Tiny PK authentication
scheme have been proposed by Watloel. The security
scheme is used to authenticate outside entity from network
and allow the sensor nodes to share information with
outside entity. The scheme provides trusted certificate
authority, which is a public key private key for the entity.
2.1 Security Requirements
The security system in WSNs should fall on the following
requirements to satisfy the purity of the transmitted data.
It should be protected while being transmitted to various
public channels and resources [1], [2], [16].
A. Data Confidentiality: This implies a relationship
between the communicating nodes to keep the
message confidential, so no other node should come
between them. Various attacks such as traffic
analysis attack can be restricted through keeping
data confidential.
.
B. Data Integrity: Protocol should ensure that no
alteration or updating can be made on transmitted
message. Message should appear at other end as it
was transmitted.
IJCAT - International Journal of Computing and Technology
Volume 1, Issue 1, February 2014
www.IJCAT.org
26
C. Data Authentication: Authenticity is the important
aspect in WSNs. Protocol should ensure that data
must be transmitted to the actual receiver. It also
ensures that evidence received at the other end is
correct and not tampered with.
D. Data Freshness: Protocol should ensure that data
transmitted is very recent and any attacker should
not replay messages.
E. Secure localization: Accurate location information
is necessary to diagnose faults immediately. The
Rabin location based algorithm gives accurate
location information and also protects privacy of
data.
2.2 Proposed Authentication Algorithm
The location based Rabin Public-Key cryptosystem is an
asymmetric algorithm which uses different location
parameters for each individual sensor node. Here, input
will be different every time the sensor changes its
position. Latitude and Longitude of sensors are calculated
through GPS or other location tracking software or
through manual configuration.The proposed Rabin
algorithm is divided into four modules. First the sensors
are located. After this, key pairs are generated using
latitude and longitude of a wireless node. In the
encryption module, cipher text is generated by applying
public key. It is then transmitted to the receiver to check
the validity.
With the help of Chinese Remainder Theorem, four
squares modulo m1, m2, m3, m4 are calculated. If the
value of the cipher text is equal to any of the square
modulo then the login request is accepted, otherwise the
login request is rejected. Chinese remainder theorem is a
proven algorithm for strong authentication. Hence, using
the proposed algorithm will ensure confidentiality,
integrity and authenticity of information transmitted
within wireless sensor networks.
A. Location Tracking Module:
Location based protocols have been adopted to take into
account the position of each sensor node in a network.
GPS can be used to track location in order to increase the
level of data security. As each time distance and direction
are changed, we always get different input keys.
Step I: Calculate Latitude and Longitude by using GPS or
other location tracking software.
Step II: Take variable p=latitude and q=longitude.
Step III: Pass variable p & q to Key Generation Module.
B. Key Generation Module:
The system creates key pairs by following steps:
Step I: Compute n=p*q
Step II: Systems public key is n and systems private
key is [p, q].
Step III: Send public key and private key to Encryption
Module.
C. Encryption Module:
System creates cipher text by the following steps:
Step I: Receive key pairs.
Step II: Calculate Cipher text C = M
2
mod n.
Step III: Generate cipher text and send it to remote
machine.
D. Authentication Module:
The system authenticates by checking the validity of the
cipher text. Private keys are necessary to decode it. If both
it and the location are known then the plain text belongs
to the set of square roots generated through CRT. i.e
M{0,,n-1}. Following are the steps involved in the
authentication phase:
Step I: Receive request C
and checks for validity.
Step II: Apply Chinese remainder theorem for
authenticity. Theorem states that for any set of integers
and for given integers there exists commons modulo,
which can be cipher text according to proposed scenario.
Step III:
X
1
= a
1
(mod m
1
)
X
2
= a
2
(mod m
2
)
.
.
.
Xn= a
n
(mod m
n
)
has a unique solution mod (m
1
, m
2
,,m
n
)
Where, m
1
, m
2
,,m
n
are the square moduluss generated
by Chinese remainder theorem. If cipher text is equal to
any of the square root value then accept the login request.
Step IV: Otherwise reject the login request.
Step V: The square roots are in the set [0,, n-1]
Step VI: Among these square roots one is the original
plaintext.
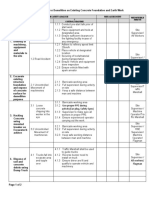
2.3 System Architecture
The idea behind above protocol is simple. Track location
of sensor node using GPS or manual configuration. In
IJCAT - International Journal of Computing and Technology
Volume 1, Issue 1, February 2014
www.IJCAT.org
27
step 1, latitude and longitude are calculated to generate
key pairs. In step 2, Public key and private key are
inserted in Encryption module to generate cipher text. In
step 3, transfer cipher text to remote system, so that
authenticity can be achieved. In step 4, receiver after
receiving cipher text, checks for its validity.
Authentication is the key aspect of Rabin algorithm.
Chinese remainder theorem will generate square moduli
and check the value of C with these modulo. If match
occur then accept login request otherwise reject login
request. With the help of Chinese Remainder Theorem,
four squares modulo m1, m2, m3, m4 are calculated. If
the value of the cipher text is equal to any of the square
modulo then the login request is accepted, otherwise the
login request is rejected. Chinese remainder theorem is a
proven algorithm for strong authentication. Hence, using
the proposed algorithm will ensure confidentiality,
integrity and authenticity of information transmitted
within wireless sensor networks.
Here, standard Chinese remainder theorem is
implemented for proving authenticity to the received
message. Due to its location based nature, security attacks
like secure localization can be easily overcome.
Fig 1: Process Architecture
2. 4 Analysis Of Proposed Authentication Protocol
In this section we introduce possible attacks take on
Wireless sensor networks and steps taken on attack by
proposed authentication algorithm.
A. Monitoring and Eavesdropping: This is the most
common attack on privacy of data. By snooping
the attacker can easily analyze the content of
the transmitted data. Every transmission
between sensor nodes and the base station is in
encrypted form so no such attack is possible on
WSNs with the proposed algorithm.
B. Camouflage Adversaries: In this, attackers can
insert and hide their nodes into the sensor
network. These nodes then copy normal nodes
and transmit information on their behalf. This is
prevented by the proposed algorithm as it is
location based. Every node carries a different
location address; therefore one cannot copy
another node within the WSN.
3. Evaluation 0f Algorithm
As Rabin cryptosystem is location based algorithm many
attacks can be solved. The huge advantage of proposed
algorithm is that multiple plaintexts can be recovered to
generate cipher text. As data is represented in numeric
value, it makes code breaking difficult.
The efficiency of algorithm can be calculated by
encryption and decryption. For encryption location of
particular node and square modulo of n is calculated,
which make it hard at factorization, like security in RSA.
For decryption, Chinese remainder theorem is applied,
along with two modular exponentials.
4. Implementation and Results
We have used Android Development Tools (ADT) which
is a plug-in for Eclipse IDE. ADT extends capabilities of
Java Eclipse, which is excellent tool to run projects on
Android environment. Idea behind using such setup is,
Android tools create run time environment for project and
one can easily demonstrate it on Android cell phones.
We have implemented location listener interface for
calculating location of the sensor nodes. Experimental
results show that text message is transferred between the
nodes. Latitude and Longitude along with the text
IJCAT - International Journal of Computing and Technology
Volume 1, Issue 1, February 2014
www.IJCAT.org
28
message take 1.2ms/byte time to execute. Total time
required to execute encryption-decryption phase is 6ms.
Fig 2 shows performance analysis of execution time of
Elliptic curve cryptographic algorithm, RSA and location
based Rabin cryptosystem. According to the papers
referred for ECC and RSA, both have provided security
over communication on wireless sensor networks. They
have taken parameter as long prime numbers along with
the text message to transfer over communication channel
in wireless sensor networks. Where, Rabin improved the
parameter by accepting location of any sensor nodes.
Fig 2: Performance of execution time of different algorithm
Performance comparison is taken on key size of 64 for
ECC ,64 for RSA and 32 key size for location based
Rabin cryptosystem.
Fig 3 illustrates the instantaneous time taken to run
location based Rabin cryptosystem algorithm with
Android virtual device manager. Location is calculated
through manual configuration as GPS systems are there in
computer devices. After this, encryption and decryption
phase is run in 6ms time.
We observe that due to time taken by this algorithm is
very less compare to any other algorithm existed for
WSNs security; it will take less battery power
consumption. We also have experimented Location based
Rabin algorithm with large files. Performance analysis for
the same is also less. It takes lesser time any other
algorithm. Transmitting large files have disadvantage due
to problem occur in wireless sensing nodes. As it requires
battery power and more memory.
Fig 3 shows time taken to run Location based Rabin algorithm
5. Conclusion
Wireless sensor nodes have strict constraints on the
resources, such as battery power and memory, and time
efficiency. Minimizing the battery consumption, while
maintaining a desirable level of security is very
challenging task. In this paper we have proposed a
location based security algorithm to calculate time
efficiency and to authenticate received data.
Our results shows that time taken by proposed
authentication algorithm is very less as compare to any
other algorithm exist for wireless sensor network security.
Performance analysis shows that proposed authentication
algorithm is secure and efficient. As this system is
location dependant, it will be difficult for adversaries to
track every time changing locations of a node. Hence,
from experiments and results we can say that, proposed
authentication algorithm is secure and efficient for
wireless sensor networks security.
References
[1] Garcia-Hernandez, C. F., Ibarguengoytia-Gonzalez, P. H
and Perez-DiaZo J. A 'Wireless Sensor Networks and
Applications: A Survey', IJCSNS, 7(3),264-273 (2007)
[2] V. C Shekhar, Mrudala Sarvabhatla , Security in WSNs
with Public Key Techniques, ICCCI-(2012), Jan 10-12,
Coimbatore, India
IJCAT - International Journal of Computing and Technology
Volume 1, Issue 1, February 2014
www.IJCAT.org
29
[3] P. Mohanty, N. Sarma, S. Panigrahi, S. S. Satapathy, A
Symmetric Key based secured data gathering protocol for
WSN, ICCCI-(2012), Jan 10-12, Coimbatore, India
[4] K .Saravana selvi T. Rabin Public Key Cryptosystem
for Mobile Authentication.. IEEE- (ICAESM -2012)
March 30, 31, 2012.
[5] Dr. Lawrence Washington. Elliptic Curve Cryptography
and Its Applications to Mobile Devices. Wendy Chou,
University of Maryland, College Park. Department of
Mathematics.
[6] Dr. R. Shanmugalakshmi ,"Research Issues on Elliptic
Curve Cryptography and Its applications - IJCSNS,
VOL.9 No.6, June 2009,
[7] Gaoxiang Chen, Gelian Song, Tao Zhuang, An identity
Authentication Scheme in Wireless Peer-to-Peer
Network, IEEE (2010), Oct 3, 2010
[8] Lein Harn & Thomas Kiesler Two New Efficient
Cryptosystems Based on Rabin's Scheme: Alternatives to
RSA Cryptosystem .Computer Science
Telecommunications Program University of Missouri -
Kansas City Kansas City, MO 64110. 1990 IEEE.
[9] C. Karlof, N. Sastry, and D. Wagner, "TinySec: a link
layer security architecture for wireless sensor networks,"
in Proceedings of the Second International Conference
on Embedded Networked Sensor Systems (SenSys '04),
pp. 162-175, Baltimore, Md, USA, November 2004.
[10] S. Prasanna Ganesan An Asymmetric Authentication
Protocol for Mobile Devices Using HyperElliptic Curve
Cryptography. India. 2010 IEEE.
[11] A Perrig, R Szewczyk, J. D. Tygar, V. Wen, and D. E.
Culler, "SPINS: security protocols for sensor networks,"
Wireless Networks, vol. 8, no. 5, pp. 521-534, 2002.
[12] M. J. Beller, L. F. Chang, and Y. Yacobi, "Privacy and
authentication on a portable
communications system, " IEEE J. Set. Areas Commun. ,
vol. 11, pp. 821-829, 1993
[13] "A Performance Comparison of Data Encryption
Algorithms," IEEE [Information and
Communication Technologies, 2005. ICICT 2005. First
International Conference ,2006-02-27, PP. 84- 89
[14] W.-B. Lee and C.-K. Yeh, "A new delegation-based
authentication protocol for use in portable
communication systems, " IEEE Trans. Wireless
Communication. , vol. 4, no. 1, pp. 57-64, 2005.
[15] Jian-zhu Lu and Jipeng Zhou On the Security of an
Efficient Mobile Authentication Scheme for Wireless
Networks. Department of Computer Science University
of Jinan Guangzhou, Guangdong, China 510632. 2010
IEEE
[16] Dr. G. Padmavathi, Mrs. D. Shanmugapriya, A Survey
of Attacks, Security Mechanisms and Challenges in
Wireless Sensor Networks, (IJCSIS) International
Journal of Computer Science and Information Security,
Vol. 4, No. 1 & 2, 2009
Ms Aaisha Jabeen Siddiqui, Student of Mtech Final Year studying
in Nagpur Institute of Technology, Nagpur .She received the B.E
degree in Computer Science and Engineering, from RTMNU, Nagpur
in 2010. She has received progressive success in various Debate
Competition and Elocution. Her main research interests include
network securities, Cryptography, Database Management..
Prof. Praveen Sen, he is working as a Head of the Department in
Information Technology, in Nagpur Institute of Technology . His
various research paper has been published in various international
Journal. He is member of various international journal committee. He
has good grip in design, development and implementation of IT,
Software tools. He has a good hand on various Programming
languages. His main research interests include Android,
Cryptography, Social Computing.
Prof. Jagdish Pimple, he is working as a Head of the Department in
Computer Science & Engineering, in Nagpur Institute of Technology .
His various research paper has been published in various
international Journal. He is member of various international journal
committee. He has good grip in design, development and
implementation of IT, Software tools. He has a good hand on various
Programming languages. His main research interests include
Android, Cryptography, Social Computing.
You might also like
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Laminated Composite Stiffened Panels Application and BehaviourDocument46 pagesLaminated Composite Stiffened Panels Application and BehaviourHemendra Jain100% (1)
- 6T40 45 Diag FixesDocument69 pages6T40 45 Diag Fixesjosue100% (12)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- ULSADO-JSA-Demolation Existing Concrete FoundationDocument2 pagesULSADO-JSA-Demolation Existing Concrete FoundationKelvin Tan75% (4)
- Physics of SuperconductivityDocument106 pagesPhysics of SuperconductivityRaj JanaNo ratings yet
- MPC6515 ManualDocument37 pagesMPC6515 ManualJerome CeleraNo ratings yet
- Technical Guidance Notes: Level 2, No. 13Document4 pagesTechnical Guidance Notes: Level 2, No. 13Τε ΧνηNo ratings yet
- Boiler FormulasDocument5 pagesBoiler FormulasAnonymous 6Mb7PZjNo ratings yet
- Multiple Disease Diagnosis by Using Fuzzy Pattern Applications On Large DatabaseDocument8 pagesMultiple Disease Diagnosis by Using Fuzzy Pattern Applications On Large Databaseeditor_ijcatNo ratings yet
- Various Pitch Extraction Techniques of Audio Files For Audio Information RetrievalDocument4 pagesVarious Pitch Extraction Techniques of Audio Files For Audio Information Retrievaleditor_ijcatNo ratings yet
- Parallelization of BFS Graph Algorithm Using CUDADocument6 pagesParallelization of BFS Graph Algorithm Using CUDAeditor_ijcatNo ratings yet
- Text Cryptosystem Based On Elliptic Curve Cryptography For NetworksDocument4 pagesText Cryptosystem Based On Elliptic Curve Cryptography For Networkseditor_ijcatNo ratings yet
- Various Methods For Preventing Flooding Attack in MANET A Comparative AnalysisDocument3 pagesVarious Methods For Preventing Flooding Attack in MANET A Comparative Analysiseditor_ijcatNo ratings yet
- Missing Value Estimation and Impact On Heterogeneous Data SetDocument4 pagesMissing Value Estimation and Impact On Heterogeneous Data Seteditor_ijcatNo ratings yet
- NIOS II Based Embedded Web Server Development For Networking ApplicationsDocument5 pagesNIOS II Based Embedded Web Server Development For Networking Applicationseditor_ijcatNo ratings yet
- Preserving Privacy and Illegal Content Distribution For Cloud EnvironmentDocument7 pagesPreserving Privacy and Illegal Content Distribution For Cloud Environmenteditor_ijcatNo ratings yet
- Two Ways Security On Cloud Computing Using Cryptography and Intrusion Detection A Review PDFDocument3 pagesTwo Ways Security On Cloud Computing Using Cryptography and Intrusion Detection A Review PDFeditor_ijcatNo ratings yet
- Multi Region Extraction Image Segmentation Based On Centroid Clustering TechniqueDocument5 pagesMulti Region Extraction Image Segmentation Based On Centroid Clustering Techniqueeditor_ijcatNo ratings yet
- Review On Brain Tumor Detection Techniques From MRI Images and Rough Set TheoryDocument6 pagesReview On Brain Tumor Detection Techniques From MRI Images and Rough Set Theoryeditor_ijcatNo ratings yet
- Implementation of Modified RSA Cryptosystem Based On Offline Storage and Prime Number PDFDocument3 pagesImplementation of Modified RSA Cryptosystem Based On Offline Storage and Prime Number PDFeditor_ijcatNo ratings yet
- Parallel K Means Clustering Based On Hadoop and HamaDocument5 pagesParallel K Means Clustering Based On Hadoop and Hamaeditor_ijcatNo ratings yet
- Performance Evaluation of Wireless Sensor Network Under Black Hole AttackDocument5 pagesPerformance Evaluation of Wireless Sensor Network Under Black Hole Attackeditor_ijcatNo ratings yet
- User Deadline Based Job Scheduling in Grid Computing PDFDocument8 pagesUser Deadline Based Job Scheduling in Grid Computing PDFeditor_ijcatNo ratings yet
- A Distributed Method To Protect Disruption Tolerant Networks From The Effects of Packet Overflow PDFDocument6 pagesA Distributed Method To Protect Disruption Tolerant Networks From The Effects of Packet Overflow PDFeditor_ijcatNo ratings yet
- Android Help Alert System Using Speech Recognition PDFDocument5 pagesAndroid Help Alert System Using Speech Recognition PDFeditor_ijcatNo ratings yet
- Self Improved ODMP Protocol (ODMP E) PDFDocument6 pagesSelf Improved ODMP Protocol (ODMP E) PDFeditor_ijcatNo ratings yet
- Relative Study On Malayalam English Translation Using Transfer Based Approach PDFDocument6 pagesRelative Study On Malayalam English Translation Using Transfer Based Approach PDFeditor_ijcatNo ratings yet
- Study On Security Breaches in PHP Applications PDFDocument5 pagesStudy On Security Breaches in PHP Applications PDFeditor_ijcatNo ratings yet
- Analysis of Noise Exposure From Different Machines by Graph Based Clustering Method PDFDocument6 pagesAnalysis of Noise Exposure From Different Machines by Graph Based Clustering Method PDFeditor_ijcatNo ratings yet
- Power Quality Monitoring of Induction Motor Using Lab VIEW PDFDocument8 pagesPower Quality Monitoring of Induction Motor Using Lab VIEW PDFeditor_ijcatNo ratings yet
- Securing Images Using Encryption Techniques A Survey PDFDocument5 pagesSecuring Images Using Encryption Techniques A Survey PDFeditor_ijcatNo ratings yet
- Towards A Statistical Context For Source Obscurity in Sensor Network PDFDocument4 pagesTowards A Statistical Context For Source Obscurity in Sensor Network PDFeditor_ijcatNo ratings yet
- Securing Websites Through Multi CAPTCHA PDFDocument4 pagesSecuring Websites Through Multi CAPTCHA PDFeditor_ijcatNo ratings yet
- Secure Sharing of Data Over Cloud Computing Using Different Encryption Schemes An Overview PDFDocument4 pagesSecure Sharing of Data Over Cloud Computing Using Different Encryption Schemes An Overview PDFeditor_ijcatNo ratings yet
- Selection of Accurate & Robust Model For Binary Classification Problems PDFDocument4 pagesSelection of Accurate & Robust Model For Binary Classification Problems PDFeditor_ijcatNo ratings yet
- Recognizing Character Using Bayesian Network in Data Mining PDFDocument5 pagesRecognizing Character Using Bayesian Network in Data Mining PDFeditor_ijcatNo ratings yet
- Real Time Eye Tracking System For People With Several Disabilities Using Single Web Cam PDFDocument4 pagesReal Time Eye Tracking System For People With Several Disabilities Using Single Web Cam PDFeditor_ijcatNo ratings yet
- Proposed Model of Encryption Technique Using Block Cipher Concept To Enhance Avalanche Effect PDFDocument5 pagesProposed Model of Encryption Technique Using Block Cipher Concept To Enhance Avalanche Effect PDFeditor_ijcatNo ratings yet
- Lab 02 - Boundary Layer-2Document21 pagesLab 02 - Boundary Layer-2Walid El AhnafNo ratings yet
- 6991 1767 01b - Diamec U4 - LRDocument4 pages6991 1767 01b - Diamec U4 - LRPABLONo ratings yet
- Heliobond GI WE3Document24 pagesHeliobond GI WE3jarodzeeNo ratings yet
- PHCbi Refrigerators MPRS163 MPRS313Document2 pagesPHCbi Refrigerators MPRS163 MPRS313Eslam HassanNo ratings yet
- 10.4 Modes of TransportDocument12 pages10.4 Modes of TransportAya Magdy AhmedNo ratings yet
- Furniture Plans How To Build A Rocking ChairDocument10 pagesFurniture Plans How To Build A Rocking ChairAntónio SousaNo ratings yet
- P28 and P128 Series Lube Oil Controls With Built-In Time Delay RelayDocument8 pagesP28 and P128 Series Lube Oil Controls With Built-In Time Delay RelayFreddy de los SantosNo ratings yet
- Technical Data Demag Hoist Units Volume 2: Double-Rail Crab EZDH 600 - EZDH 1000 Double-Rail Crab EZLDH 600 - EZLDH 2000Document88 pagesTechnical Data Demag Hoist Units Volume 2: Double-Rail Crab EZDH 600 - EZDH 1000 Double-Rail Crab EZLDH 600 - EZLDH 2000mohammad khoraminiaNo ratings yet
- Performance of A Test Embankment Constructed On An Organic Clayey Silt DepositDocument10 pagesPerformance of A Test Embankment Constructed On An Organic Clayey Silt DepositGurtejSinghChanaNo ratings yet
- 2023.04.24 BSNL FTTH LeafletDocument2 pages2023.04.24 BSNL FTTH LeafletSatan SinghNo ratings yet
- Heat StrokeDocument8 pagesHeat StrokePrateek Barapatre0% (1)
- Commissioning Report Generator - SAMPLEDocument5 pagesCommissioning Report Generator - SAMPLEMax JohnNo ratings yet
- Ulei Honda Jazz 1.4i CVTDocument1 pageUlei Honda Jazz 1.4i CVTcmlad1No ratings yet
- DrillingMotors MKT 001 01Document10 pagesDrillingMotors MKT 001 01Aman Aayra SrivastavaNo ratings yet
- Company Profile Pt. DutaflowDocument62 pagesCompany Profile Pt. DutaflowRizkiRamadhanNo ratings yet
- DF PDFDocument8 pagesDF PDFAtif JaveadNo ratings yet
- Machine Guarding LP PDFDocument4 pagesMachine Guarding LP PDFrexivyNo ratings yet
- Vastu Tips For CareerDocument2 pagesVastu Tips For CareerBeyond ThoughtsNo ratings yet
- Actividad 5 TermodinamicaDocument4 pagesActividad 5 TermodinamicaAngel EncastinNo ratings yet
- Gfps 9182 Product Range PVC U en PDFDocument568 pagesGfps 9182 Product Range PVC U en PDFjj bagzNo ratings yet
- Home water pressure booster pumpDocument3 pagesHome water pressure booster pumpbadaasaabNo ratings yet
- Commercial LightingDocument6 pagesCommercial LightingRehan RameezNo ratings yet
- Catalogue Cable Tray RevDocument40 pagesCatalogue Cable Tray RevhardiyantodonniNo ratings yet