Professional Documents
Culture Documents
United States: (12) Patent Application Publication (10) Pub. No.: US 2005/0289060 A1
Uploaded by
acela32480 ratings0% found this document useful (0 votes)
26 views10 pagesOriginal Title
Us 20050289060
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
26 views10 pagesUnited States: (12) Patent Application Publication (10) Pub. No.: US 2005/0289060 A1
Uploaded by
acela3248Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 10
US 20050289060A1
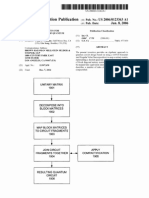
( 12) Patent Application Publication ( 10) Pub. N o. : US 2005/ 0289060 A1
( 19) United States
Abumehdi et al. ( 4 3 ) Pub. D ate: D ec. 29, 2005
( 54 ) SECURE METHOD OF CON SULTIN G ( 52) US. Cl. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 705/ 50
ARTICLE D ELIVERY RECEIPTS
( 76) Inv entor s : Cy r us Abumehdi, Har low ( GB ) ; ( 57) AB STRACT
Patr ick B lanluet, Par is ( FR) ; Ax el
Glaes er , Tauf f elen ( CH)
Cor r es pondence Addr es s :
PERMAN & GREEN
4 25 POST ROAD
FAIRFIELD , CT 06824 ( US)
( 21) Appl. N o. : 11/ 082, 224
( 22) Filed: Mar . 16, 2005
( 3 0) For eig n Application Pr ior ity D ata
Mar . 16, 2004 ( FR) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . FR 04 02682
Publication Clas s i? cation
( 51) Int. Cl? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . H04 L 9/ 00
In a s ecur e method of cons ulting ar ticle deliv er y r eceipts
f r om a r emote computer ter minal connected to a manag e
ment computer center v ia a telecommunications netw or k , a
dig ital imag e of each r eceipt is initially input to a por table
ter minal that includes a r adio inter f ace f or tr ans mitting s aid
imag e to the manag ement computer center . In or der to
cons ult the dig ital imag e in s ecur e manner f r om the r emote
computer ter minal, pr ov is ion is made in s aid r emote com
puter ter minal to us e a uniq ue k ey k SESSION that is dif f er ent
on each cons ultation in or der to decr y pt ? r s t data E1
g ener ated in the por table ter minal f r om the dig ital imag e,
s aid uniq ue k ey k SESSION its elf being the r es ult of the
manag ement computer center us ing one of its oWn pr iv ate
k ey s k PRWN LS to decr y pt s econd data E2 g ener ated in the
por table ter minal f r om the uniq ue k ey k SESSION .
| | 3 2 3 6 r 3 8 |
S1 \ E1
| M Sk FEillM] I EM, " ls k r attlmn E1 4 : 9
| K 3 o pg < 3 1. k . P | 10
I k IV s s s s lan I
k lb Ek ? h? k mm ) E2
LLE _______________J
FM M I
I I
| E1 E1
I E2 uk ' r l' hiv lnl W" Eas tman) E3 I
m__k ii' s v _____k h _______J
5k m; [ M] : S1
Patent Application Publication D ec. 29, 2005 Sheet 1 0f 5 US 2005/ 0289060 A1
llllllllllll
lllllllHlll
Patent Application Publication D ec. 29, 2005 Sheet 2 0f 5 US 2005/ 0289060 A1
FIG. 2
I I | I
1
| _| I I I Ill I I I I I L
Patent Application Publication D ec. 29, 2005 Sheet 3 0f 5 US 2005/ 0289060 A1
m- l' __ I
I z 4
LL- Fl
I I
| iw
I 3
|
M
lE1
E k s as s ion K 3 8
F \
M E1
S2
k s es s |
M
___. . ________. . _________|
l
M = l= { > 10
k s es s lon I
I
Z I J
_|
l
4 k ' k iv 4 M4
k s es s ion k \ I l
70 on I
= : A
56 k Ff iJ
s w [ M] = 5 IL
( D D ) k PRw 1 O5
62
L2 E
l 2 E2
( 4 2 S
H ( k m l 2
60
S
D k s es s ion
IV
N L PU
l
M
K 3 o
M
E1 E2
M
E1 S' 2
Patent Application Publication D ec. 29, 2005 Sheet 5 0f 5 US 2005/ 0289060 A1
FIGS
F102
k
100
k m
P0:
In.
| _ " Q ' JL ___2u| ill
SM . 5 5M
US 2005/ 0289060 A1
SECURE METHOD OF CON SULTIN G ARTICLE
D ELIVERY RECEIPTS
TECHN ICAL FIELD
[ 0001] The pr es ent inv ention r elates to the ? eld of log is
tics as applied to s hipping g oods , par cels , and pack ets , or
any other ar ticle, and it r elates mor e par ticular ly to a s ecur e
method of cons ulting g oods deliv er y r eceipts .
PRIOR ART
[ 0002] The log is tics s y s tems f or tr ack ing ar ticles that ar e
pr es ently in us e by car r ier s ar e Well k noWn. B y Way of
ex ample, US. Pat. N o. 5, 3 13 , 051 des cr ibes an ar ticle tr ack
ing s y s tem compr is ing a por table ter minal held in the hand
of a deliv er y per s on and pr ov ided With a bar code r eader and
a touch-s ens itiv e s cr een and als o With r adio communications
means f or tr ans f er r ing inf or mation to a centr al car r ier , Which
claim, in par ticular the identity and the s ig natur e of the
addr es s ee, is input v ia the s cr een by the deliv er y per s on.
Such a s y s tem enables the car r ier to hav e, in r eal time,
inf or mation r elating to g oods that hav e been deliv er ed.
N ev er theles s , that inf or mation s y s tem cannot be cons ulted
dir ectly by the car r ier s clients , nor can thos e clients cons ult
the inf or mation r elating to the deliv er y r eceipt that cons ti
tutes pr oof of deliv er y . That can only be cons ulted by the
client af ter the deliv er y r ound has been completed and all of
the r eceipts hav e been handed ov er to a s canner center
Wher e, af ter they hav e been pr oces s ed, they can be cons ulted
us ing a telecommunications netWor k .
OB JECT AN D D EFIN ITION OF THE
IN VEN TION
[ 0003 ] An obj ect of the pr es ent inv ention is thus to miti
g ate the abov e-mentioned dr aWback s by means of a method
and a s y s tem f or s ecur ely cons ulting ar ticle deliv er y r eceipts
enabling the client of a car r ier to cons ult in s ecur e manner
and in r eal time the v ar ious r eceipts r elating to g oods being
deliv er ed to their addr es s ees . Another obj ect of the inv ention
is to enable the r eceipts to be cons ulted in a manner that is
s imple, but not s ecur e, and Without any g uar antee as to
content. Another obj ect of the inv ention is to pr ov ide a
method that is s imple and that limits the amount of inf or
mation that needs to be eX chang ed in or der to implement the
s y s tem.
[ 0004 ] Thes e obj ects ar e achiev ed With a s ecur e method of
cons ulting ar ticle deliv er y r eceipts f r om a r emote computer
ter minal connected to a manag ement computer center v ia a
telecommunications netWor k , a dig ital imag e of each r eceipt
being initially input to a por table ter minal including a r adio
inter f ace f or tr ans mitting the imag e to the manag ement
computer center , Wher ein in or der to cons ult s aid dig ital
imag e in s ecur e manner f r om the r emote computer ter minal,
it is neces s ar y in s aid r emote computer ter minal to us e a k ey
k SESSION that is uniq ue and dif f er ent f or each cons ultation,
to decr y pt ? r s t data E1 g ener ated in the por table ter minal
f r om s aid dig ital imag e, s aid uniq ue k ey k SESSION its elf
being the r es ult of the manag ement computer center us ing a
pr iv ate k ey k PRWN LS of the manag ement computer center to
decr y pt s econd data E2 g ener ated in the por table ter minal
f r om the uniq ue k ey k SESSION .
[ 0005] Thus , the data input into the por table ter minal by
the deliv er y per s on can be cons ulted in s ecur e manner on
D ec. 29, 2005
line, e. g . immediately af ter the data has been input, but only
by a us er client in pos s es s ion of means f or decr y pting the
uniq ue s es s ion k ey that has pr ev ious ly been encr y pted in the
manag ement computer center .
[ 0006]
k PUB MMT
In the intended implementation, a ? r s t public k ey
may be us ed to v er if y a s ig natur e S1 as s ociated With
the dig ital imag e, this s ig natur e being obtained in the r emote
computer ter minal by us ing the uniq ue k ey k SESSION that is
dif f er ent on each cons ultation to decr y pt the ? r s t data E1
g ener ated in the por table ter minal and tr ans mitted to the
manag ement computer center , the uniq ue k ey k SESSION
being obtained in the computer ter minal by us ing a s econd
public k ey k PUB N LS to decr y pt thir d data E3 g ener ated in the
manag ement computer center by us ing the pr iv ate k ey
k PRIVN LS of the manag ement computer center to encr y pt the
uniq ue k ey k SESSION as obtained pr ev ious ly by us ing s aid
pr iv ate k ey k PRWN LS to decr y pt the s econd data E2 g ener
ated in the por table ter minal and tr ans mitted to the manag e
ment computer center .
[ 0007] It is als o pos s ible f or a ? r s t public k ey k PUB to
be us ed to v er if y a s ig natur e S1 as s ociated With the dig ital
imag e, s aid s ig natur e S1 being obtained in the r emote
computer ter minal by us ing the uniq ue k ey k SESSION that is
dif f er ent on each cons ultation to decr y pt the ? r s t data E1
g ener ated in the por table ter minal and tr ans mitted to the
manag ement computer center , this uniq ue k ey k SESSION
being tr ans mitted by the manag ement computer center
tog ether With a s ig natur e S2 as s ociated With s aid uniq ue k ey
k SESSION and being v er i? ed in the r emote computer ter minal
by means of a s econd public k ey k PUB N LS, the s ig natur e S2
being obtained by us ing the pr iv ate k ey k PRIVN LS of the
manag ement computer center to encr y pt the uniq ue k ey
k SESSION as obtained pr ev ious ly by us ing s aid pr iv ate k PRWN LS
to decr y pt the s econd data E2 g ener ated in the por table
ter minal and tr ans mitted to the manag ement computer cen
ter .
[ 0008] Pr ef er ably , the ? r s t data E1 is obtained by us ing the
uniq ue k ey k SESSION to encr y pt the s ig natur e S1, and the
s econd data E2 is obtained by us ing the uniq ue k ey k SESSION
to encr y pt the s econd public k ey k PUB N LS, the s ig natur e S1
its elf being the r es ult of the dig ital imag e of the r eceipt being
s ig ned With a pr iv ate k ey k PRWMMT of the por table ter minal.
[ 0009] In the intended implementation, the ? r s t public k ey
k PUB MMT may be encr y pted by means of the s econd public
k ey k PUB N LS to obtain ? r s t k ey data Ek 1 Which is tr ans mitted
to the manag ement computer center Wher e s aid ? r s t k ey data
Ek 1 is decr y pted us ing the pr iv ate k ey k PRIVN LS of the
manag ement computer center in or der to r ecov er the ? r s t
public k ey k PUB MMT, Which k ey is then encr y pted ag ain
us ing the pr iv ate k ey k PRWN LS of the manag ement computer
center in or der to obtain s econd k ey data Ek 2 f r om Which the
client can r ecov er the ? r s t public k ey k PUB MMT by decr y pt
ing the s econd data k ey With the s econd public k ey k PUB N LS
Adv antag eous ly , the ? r s t k ey data Ek 1 is tr ans mitted to the
manag ement computer center tog ether With the dig ital imag e
of the r eceipt and the ? r s t and s econd data E1 and E2.
[ 0010] It is als o pos s ible f or the ? r s t public k ey k PUB MM
to be s ig ned by means of the pr iv ate k ey k PRIVN LS in or der
to obtain a k ey s ig natur e Sk 1 Which is tr ans mitted tog ether
With the ? r s t public k ey k PUB MMT to the manag ement
computer center Wher e s aid k ey s ig natur e Sk 1 is v er i? ed by
means of the s econd public k ey k PUB N LS pr ior to being
MMT
T
US 2005/ 0289060 A1
r etr ans mitted tog ether With the ? r s t public k ey k PUB MMT to
the client ter minal Wher e s aid k ey s ig natur e Sk 1 is ag ain
v er i? ed by means of the s econd public k ey k PUB N LS, the
r es ult of this v er i? cation cons tituting acceptance or r ef us al
of the ? r s t public k ey k PUB MMT. Adv antag eous ly , the k ey
s ig natur e Sk 1 is tr ans mitted to the manag ement computer
center tog ether With the dig ital imag e of the r eceipt and the
? r s t and s econd data E1 and E2.
[ 0011] Pr ef er ably , the telecommunications netWor k is the
Inter net, the encr y pting / decr y pting pr oces s is of the D ES,
tr iple D ES, or AES ty pe, and the dig ital imag e of the r eceipt
is tr ans mitted tog ether With identity data and other inf or ma
tion r elating to the deliv er y as input to the por table ter minal.
B RIEF D ESCRIPTION OF THE D RAWIN GS
[ 0012] The inv ention Will be better under s tood on s ig ht of
the f olloWing detailed des cr iption accompanied by illus tr a
tiv e and non-limiting eX amples With r ef er ence to the f ol
loWing ? g ur es , in Which:
[ 0013 ] FIG. 1 is a g ener al v ieW of a computer netWor k
ar chitectur e enabling s ecur e cons ultation of the deliv er y of
ar ticles in accor dance With the inv ention;
[ 0014 ] FIGS. 2 and 3 s hoW the v ar ious s teps in tWo
implementations of a pr oces s f or v er if y ing mes s ag es s ent by
a por table ter minal of the FIG. 1 netWor k ; and
[ 0015] FIGS. 4 and 5 s hoW dif f er ent s teps in tWo imple
mentations of a pr oces s f or tr ans f er r ing k ey s that is imple
mented in the netWor k of FIG. 1.
D ETAILED D ESCRIPTION OF
IMPLEMEN TATION S
[ 0016] FIG. 1 s hoWs the ar chitectur e of a computer net
Wor k of a car r ier of g oods , par cels , or pack ets , or indeed any
other ar ticle of the s ame k ind, in Which it is neces s ar y to
implement s ecur e cons ultation of deliv er y r eceipts in accor
dance With the inv ention. N ev er theles s , it s hould be
obs er v ed that it is not es s ential f or the netWor k to belong to
the car r ier , and that it could eq ually Well belong to a thir d
par ty acting as the r epr es entativ e of the car r ier f or r eceiv ing
r eceipts and inf or mation concer ning deliv er ies .
[ 0017] This netWor k ar chitectur e is or g aniZ ed ar ound a
manag ement computer center 10 connected to a ? r s t tele
communications netWor k 12 of the Inter net ty pe. The man
ag ement computer center compr is es one or mor e computer
s er v er s , eg a s er v er 20, hav ing databas es 22, 24 connected
ther eto including an imag e databas e 22 that is acces s ible v ia
the Inter net f r om r emote computer ter minals , eg a per s onal
computer 14 . The s er v er is als o pr ov ided With a r adio
modem 26 to r eceiv e data f r om a multif unction por table
ter minal 16 v ia a s econd telecommunications netWor k 18 of
the g ener al pack et r adio s er v ice ( GPRS) or univ er s al mobile
telephone s y s tem ( UMTS) ty pe.
[ 0018] With this ar chitectur e, it is pos s ible f or the client of
a car r ier to cons ult in r eal time the r eceipts f or deliv er ies of
that client s g oods to their des tinations tog ether With any
other inf or mation r elating to s uch deliv er ies and enter ed into
the multif unction por table ter minal by an employ ee of the
car r ier , g ener ally a dr iv er and deliv er y per s on. The cons ul
tation can be per f or med r emotely in v er y s imple manner v ia
the Inter net 12 f r om any us er s tation of the client, eg a
D ec. 29, 2005
per s onal computer 14 or any other computer eq uipment
g iv ing acces s to the Inter net ( s uch as a per s onal dig ital
as s is tant ( PD A) ) . N atur ally , the r eceipts and the other inf or
mation r elating to deliv er y as input at the addr es s ee of the
g oods v ia the multif unction por table ter minal 16 held by the
car r ier s employ ee, ar e pr ev ious ly tr ans mitted v ia the tele
communications netWor k 18 in r eal time to the computer
center 10 f or manag ing s aid inf or mation.
[ 0019] The detail of the inf or mation that is tr ans mitted is
g iv en in the patent application ? led on the s ame day by the
s ame Applicant and entitled An optimiZ ed s y s tem f or
tr ack ing the deliv er y of ar ticles . That inf or mation, in addi
tion to the dig ital imag e of the deliv er y r eceipt bear ing the
s tamp of the addr es s ee, als o includes all us ef ul inf or mation
r elating to r eceipt of the g oods by the addr es s ee, s uch as the
name of the addr es s ee, the date and time of deliv er y , the
number of par cels deliv er ed, pos s ibly the number of par cels
r ef us ed, the s ig natur e and the name of the per s on s ig ning the
deliv er y r eceipt, and pos s ibly any r es er v ations about the
deliv er y . In addition, a photog r aph ( a dig ital imag e) of a
r ef us ed par cel and/ or of the addr es s ee, or indeed a v oice
comment made by the dr iv er or by the addr es s ee may
adv antag eous ly be as s ociated With the abov e inf or mation, as
can the number of eq uipments on depos it s or ted by ty pe of
eq uipment or pay ment of tr ans por t cos ts or pay ment f or
cas h-on-deliv er y ( COD ) .
[ 0020] Accor ding to the inv ention, all of this inf or mation
is tr ans mitted ov er the netWor k , and is s ubs eq uently con
s ulted, in s ecur e manner in or der to g uar antee to the client
that the inf or mation has not been tamper ed With. The s ecur e
cons ultation method that pr ov ides this g uar antee of tr ans
mis s ion is des cr ibed beloW With r ef er ence to FIGS. 2 to 5.
It r elies on encr y ption pr otocols and on pr otocols f or cr e
ating s ig natur es des cr ibed With r ef er ence to FIGS. 2 and 3 .
[ 0021] Implementation of the method as s umes pr ior cr e
ation of f our k ey s Which ar e s tor ed in the multif unction
por table ter minal bef or e any us e ther eof , pr ef er ably When it
is manuf actur ed or When the ter minal is put into oper ation in
the pr emis es of the car r ier or its r epr es entativ e. The ? r s t tWo
k ey s ar e s peci? c to the ter minal and compr is e a ter minal
pr iv ate k ey k PRWMMT and a ? r s t public k ey k PUB MMT. The
other tWo k ey s ar e s peci? c to the car r ier and lik eWis e
compr is e a pr iv ate k ey , this time f or the manag ement
computer center k PRWN LS and a s econd public k ey k PUB N LS
B y their natur e, the tWo pr iv ate k ey s ar e unk noWn to the
client or to any per s on other than the car r ier or the car r ier s
r epr es entativ e, While the tWo public k ey s ar e f r eely av ailable
to the client. They may nev er theles s thems elv es cons titute
the s ubj ect matter of the k ey eX chang e pr oces s des cr ibed
With r ef er ence to FIGS. 4 and 5.
[ 0022] FIG. 2 s hoWs a ? r s t eX ample of the s ecur e con
s ultation method of the inv ention. The mes s ag e 3 0 tr ans
mitted by the multif unction por table ter minal is initially
s ig ned 3 2 by means of the pr iv ate k ey k PRIVMMT of the
por table ter minal in or der to obtain a s ig natur e S1. Then, by
means of a uniq ue k ey g ener ated in the ter minal and r ef er r ed
to as k SESSION , this s ig natur e 3 4 is encr y pted 3 6 to deliv er
3 8 ? r s t encr y pted data E1. In par allel, this uniq ue k ey is
encr y pted 4 0 us ing the s econd public k ey k PUB N LS to deliv er
4 2 s econd encr y pted data E2. Once the ? r s t and s econd
encr y pted data items hav e been deliv er ed, they ar e s ent 4 4
US 2005/ 0289060 A1
to the manag ement computer center tog ether With the mes
s ag e M ( Which is thus tr ans mitted in the clear ) that Was us ed
f or cr eating them.
[ 0023 ] When the manag ement computer center r eceiv es
the data items E1 and E2 tog ether With the mes s ag e M, it
beg ins by r ecov er ing the uniq ue k ey k SESSION by decr y pting
4 6 the data E2 us ing the manag ement computer center s
pr iv ate k ey k PRIVN LS, and then it encr y pts 4 8 this k ey 50
ag ain by means of the pr iv ate k ey k PRWN LS to obtain 52
thir d encr y pted data E3 .
[ 0024 ] Then, pr ov iding the client can es tablis h a connec
tion to the manag ement computer center , pos s ibly tog ether
With an account number and a pas s Wor d f or ex ample, the
client can us e the Inter net to acces s the mes s ag e M and thus
f r eely cons ult the data tr ans mitted by the ter minal, ther eby
g aining acces s almos t at the time of deliv er y to all of the data
r elating to the deliv er y , and in par ticular to the data cons ti
tuting pr oof of deliv er y , ie the imag e of the deliv er y r eceipt
car r y ing the s tamp of the addr es s ee, the identity and the
s ig natur e of the per s on Who r eceiv ed the g oods , and the date
and time of deliv er y . N ev er theles s , at this s tag e, the data is
s till r aW data and has not been s ubj ected to any v er i? cation
pr oces s that could g uar antee its v alidity . In or der to acces s
s uch a pr oces s , the client needs to mak e a r eq ues t to the
manag ement computer center Which then als o g iv es the
client acces s to the data items E1 and E3 .
[ 0025] Star ting f r om E3 , the client can us e a per s onal
computer to r ecov er the k ey k SESSION by decr y pting 54 s aid
data us ing the s econd public k ey k PUB N LS. Then, by decr y pt
ing 56 the data item E1 us ing the k ey 58 as obtained in this
Way , it is pos s ible to obtain 60 the s ig natur e S1 as s ociated
With the mes s ag e M, Which s ig natur e S1 can then be us ed to
v er if y 62 v alidity by means of the ? r s t public k ey k PUB MMT
The r es ult of this v er i? cation cons is ts in the content of the
mes s ag e M being accepted or r ef us ed 64 .
[ 0026] FIG. 3 s hoWs a s econd ex ample of the s ecur e
cons ultation method of the inv ention. As in the pr eceding
ex ample, the pr oces s of tr ans f er r ing the mes s ag e to the
manag ement computer center is unchang ed. Thus , the mes
s ag e 3 0 tr ans mitted by the multif unction por table ter minal is
initially s ig ned 3 2 by means of the por table ter minal s
pr iv ate k ey k PRIVMMT in or der to obtain a s ig natur e S1.
Then, the uniq ue k ey k SESSION g ener ated by the ter minal is
us ed to encr y pt 3 6 the s ig natur e S1 in or der to deliv er 3 8 ? r s t
encr y pted data E1. In par allel, the uniq ue k ey is encr y pted
4 0 by means of the s econd public k ey k PUB N LS in or der to
deliv er 4 2 s econd encr y pted k ey E2. Once the ? r s t and
s econd encr y pted data items hav e been deliv er ed, they ar e
s ent 4 4 to the manag ement computer center tog ether With
the mes s ag e M ( Which is thus tr ans mitted in the clear ) that
Was us ed f or cr eating them. HoWev er , the pr oces s ing in the
manag ement computer center is s lig htly dif f er ent.
[ 0027] When the manag ement computer center r eceiv es
the data E1 and E2 tog ether With the mes s ag e M, it beg ins
by r ecov er ing the uniq ue k ey k SESSION by decr y pting 4 6 the
data E2 us ing the pr iv ate k ey k PRIVN LS of the manag ement
computer center , but ins tead of encr y pting the uniq ue k ey
ag ain, it s ig ns 70 it us ing the pr iv ate k ey k PRIVN LS in or der
to obtain a s econd s ig natur e S2. At this s tag e, as bef or e, the
client can cons ult the mes s ag e M but Without g uar antee.
HoWev er , if the client des ir es the mes s ag e to be v alidated,
the client needs to mak e a r eq ues t to the computer center ,
D ec. 29, 2005
Which Will then g iv e the client acces s als o to the ? r s t data
E1, to the s econd s ig natur e S2, and to the uniq ue k ey
k SESSION
[ 0028] The client can then us e the per s onal computer to
v er if y the v alidity of the k ey k SESSION by v er if y ing 74 the
s ig natur e S2 by means of the s econd public k ey k PUB N LS, the
r es ult of this v er i? cation cons is ting in the r eceiv ed k ey being
accepted or r ef us ed 76. If this tes t is pos itiv e, the client can
then decr y pt 56 the data E1 on the bas is of the v alidated
uniq ue k ey k SESSION , ther eby obtaining 60 the s ig natur e S1
as s ociated With the mes s ag e M, Which s ig natur e S1 can then
be us ed to v er if y 62 v alidity by means of the ? r s t public k ey
k PUB MMT. The r es ult of this v er i? cation cons titutes accep
tance or r ef us al 64 of the content of the mes s ag e M.
[ 0029] In the tWo abov e ex amples , it is as s umed that the
client has av ailable the ? r s t public k ey k PUB MMT enabling
the s ig natur e of the mes s ag e M to be v er i? ed. HoWev er , it is
als o pos s ible to env is ag e that this k ey is tr ans f er r ed to the
client s computer f r om the multif unction per s onal ter minal
v ia the manag ement computer center , as s hoWn in FIGS. 4
and 5.
[ 003 0] In FIG. 4 , the tr ans f er r elies on an encr y ption
pr oces s . The ? r s t public k ey k PUB MMT is initially encr y pted
80 by means of the s econd public k ey k PUB N LS in or der to
obtain ? r s t k ey data Ek 1 Which is tr ans mitted to the man
ag ement computer center tog ether With the mes s ag e M and
the data E1 and E2. In the manag ement computer center , the
k ey data Ek 1 is decr y pted 84 by means of the pr iv ate k ey
k PRIVN LS in or der to obtain 86 the initial k ey k PUB MMT Which
is ag ain encr y pted 88, but this time us ing the pr iv ate k ey
k PRIVN LS in or der to deliv er 90 s econd k ey data Ek z. It is f r om
this s econd k ey data Ek 2 that the client can then r ecov er 92
the ? r s t public k ey k PUB MMT by decr y pting With the s econd
public k ey k PUB N LS
[ 003 1] In FIG. 5, the abov e tr ans f er r elies on a pr oces s f or
cr eating a s ig natur e. The ? r s t public k ey k PUB MMT is initially
s ig ned 100 us ing the pr iv ate k ey k PRWN LS of the manag e
ment computer center in or der to obtain 102 a k ey s ig natur e
Sk l. This k ey s ig natur e Sk 1 is then tr ans mitted tog ether With
the ? r s t public k ey k PUB MMT to the manag ement computer
center tog ether With the mes s ag e M and the data E1 and E2.
At the manag ement computer center , the k ey s ig natur e Sk 1
is v er i? ed 104 by means of the s econd public k ey k PUB N LS,
With the r es ult of the v er i? cation 106 cons tituting accep
tance or r ef us al of the r eceiv ed ? r s t public k ey k PUB MMT
The client can then us e a ter minal to acces s the k ey s ig natur e
Sk 1 and can in tur n v er if y 108 this s ig natur e by means of the
s econd public k ey k PUB N LS, the r es ult of this v er i? cation 110
cons tituting acceptance or r ef us al of the ? r s t public k ey
MMT
k PUB
[ 003 2] In all of the abov e ex chang es , the encr y ption/
decr y ption pr oces s r elies on us ing a conv entional alg or ithm
of the D ES, tr iple D ES, or AES ty pe Well k noWn to the
per s on s k illed in the ar t and to Which r ef er ence can be made
if neces s ar y .
[ 003 3 ] Thus , With the method of the inv ention, the client
can cons ult all of the inf or mation concer ning the deliv er y
( including eq uipment on depos it, s ums r eceiv ed, f or
ex ample) , on line and f r om any location, becaus e acces s is
made v ia the Inter net. In addition, the as s ociated v er i? cation
pr oces s r ely ing on encr y ption or on a tr ans mitted data
US 2005/ 0289060 A1
s ig natur e enables the client to es tablis h ev idence of deliv er y
of the g oods of a k ind that is s uitable f or cons tituting
leg ally -enf or ceable pr oof .
What is claimed is :
1. A s ecur e method of cons ulting ar ticle deliv er y r eceipts
f r om a r emote computer ter minal connected to a manag e
ment computer center v ia a telecommunications netWor k , a
dig ital imag e of each r eceipt being initially input to a
por table ter minal including a r adio inter f ace f or tr ans mitting
the imag e to the manag ement computer center , Wher ein in
or der to cons ult s aid dig ital imag e in s ecur e manner f r om the
r emote computer ter minal, it is neces s ar y in s aid r emote
computer ter minal to us e a k ey k SESSION that is uniq ue and
dif f er ent f or each cons ultation, to decr y pt a ? r s t data E1
g ener ated in the por table ter minal f r om s aid dig ital imag e,
s aid uniq ue k ey k SESSION its elf being the r es ult of the
manag ement computer center us ing a pr iv ate k ey k PRWN LS
of the manag ement computer center to decr y pt, s econd data
E2 g ener ated in the por table ter minal f r om the uniq ue k ey
k SESSION '
2. A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 1, Wher ein a ? r s t public k ey k PUB MMT is
us ed to v er if y a s ig natur e S1 as s ociated With the dig ital
imag e, this s ig natur e being obtained in the r emote computer
ter minal by us ing the uniq ue k ey k SESSION that is dif f er ent
on each cons ultation to decr y pt the ? r s t data E1 g ener ated in
the por table ter minal and tr ans mitted to the manag ement
computer center , the uniq ue k ey k SESSION being obtained in
the computer ter minal by us ing a s econd public k ey k PUB N LS
to decr y pt thir d data E3 g ener ated in the manag ement
computer center by us ing the pr iv ate k ey k PRWN LS of the
manag ement computer center to encr y pt the uniq ue k ey
SE55 as obtained pr ev ious ly by us ing s aid pr iv ate k ey
lQ iLs -
k PRIV to decr y pt the s econd data E2 g ener ated in the
por table ter minal and tr ans mitted to the manag ement com
puter center .
3 . A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 1, Wher ein a ? r s t public k ey k PUB MMT is
us ed to v er if y a s ig natur e S1 as s ociated With the dig ital
imag e, s aid s ig natur e S1 being obtained in the r emote
computer ter minal by us ing the uniq ue k ey k SESSION that is
dif f er ent on each cons ultation to decr y pt the ? r s t data E1
g ener ated in the por table ter minal and tr ans mitted to the
manag ement computer center , this uniq ue k ey k SESSION
being tr ans mitted by the manag ement computer center
tog ether With a s ig natur e S2 as s ociated With s aid uniq ue k ey
k SESSION and being v er i? ed in the r emote computer ter minal
by means of a s econd public k ey k PUB N LS, the s ig natur e S2
being obtained by us ing the pr iv ate k ey k PRWN LS of the
manag ement computer center to encr y pt the uniq ue k ey
k SESSION as obtained pr ev ious ly by us ing s aid pr iv ate k PRWN LS
to decr y pt the s econd data E2 g ener ated in the por table
ter minal and tr ans mitted to the manag ement computer cen
ter .
D ec. 29, 2005
4 . A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 2, Wher ein the ? r s t data E1 is obtained by
us ing the uniq ue k ey k SESSION to encr y pt the s ig natur e S1,
and the s econd data E2 is obtained by us ing the uniq ue k ey
k SESSION to encr y pt the s econd public k ey k PUB N LS, the
s ig natur e S1 its elf being the r es ult of the dig ital imag e of the
r eceipt being s ig ned With a pr iv ate k ey k PRIVMMT of the
por table ter minal.
5. A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 2, Wher ein the ? r s t public k ey k PUB MMT
is encr y pted by means of the s econd public k ey k PUB N LS to
obtain ? r s t k ey data Ek 1 Which is tr ans mitted to the man
ag ement computer center Wher e s aid ? r s t k ey data Ek 1 is
decr y pted us ing the pr iv ate k ey k PRWN LS of the manag e
ment computer center in or der to r ecov er the ? r s t public k ey
k PUB MMT, Which k ey is then encr y pted ag ain us ing the
pr iv ate k ey k PRWN LS of the manag ement computer center in
or der to obtain s econd k ey data Ek 2 f r om Which the client
can r ecov er the ? r s t public k ey k PUB MMT by decr y pting the
s econd data k ey With the s econd public k ey k PUB N LS
6. A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 5, Wher ein the ? r s t k ey data Ek 1 is
tr ans mitted to the manag ement computer center tog ether
With the dig ital imag e of the r eceipt and the ? r s t and s econd
data E1 and E2.
7. A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 2, Wher ein the ? r s t public k ey k PUB MMT
is s ig ned by means of the pr iv ate k ey k PRIVN LS in or der to
obtain a k ey s ig natur e Sk 1 Which is tr ans mitted tog ether With
the ? r s t public k ey k PUB MMT to the manag ement computer
center Wher e s aid k ey s ig natur e Sk 1 is v er i? ed by means of
the s econd public k ey k PUB N LS pr ior to being r etr ans mitted
tog ether With the ? r s t public k ey k PUB MMT to the client
ter minal Wher e s aid k ey s ig natur e Sk 1 is ag ain v er i? ed by
means of the s econd public k ey k PUB N LS, the r es ult of this
v er i? cation cons tituting acceptance or r ef us al of the ? r s t
public k ey k PUB MMT
8. A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 7, Wher ein the k ey s ig natur e Sk 1 is
tr ans mitted to the manag ement computer center tog ether
With the dig ital imag e of the r eceipt and the ? r s t and s econd
data E1 and E2.
9. A s ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 1, Wher ein the telecommunications net
Wor k is the Inter net.
10. As ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 1, Wher ein the encr y pting / decr y pting
pr oces s is of the D ES, tr iple D ES, or AES ty pe.
11. As ecur e method of cons ulting ar ticle deliv er y r eceipts
accor ding to claim 1, Wher ein the dig ital imag e of the r eceipt
is tr ans mitted tog ether With identity data and other inf or ma
tion r elating to the deliv er y as input to the por table ter minal.
You might also like
- From Prognostics and Health Systems Management to Predictive Maintenance 2: Knowledge, Reliability and DecisionFrom EverandFrom Prognostics and Health Systems Management to Predictive Maintenance 2: Knowledge, Reliability and DecisionNo ratings yet
- Us 20140085181Document16 pagesUs 20140085181industrie_technosNo ratings yet
- Safe Use of Smart Devices in Systems Important to Safety in Nuclear Power PlantsFrom EverandSafe Use of Smart Devices in Systems Important to Safety in Nuclear Power PlantsNo ratings yet
- United States: (12) Patent Application Publication (10) Pub. No.: US 2012/0310602 A1Document22 pagesUnited States: (12) Patent Application Publication (10) Pub. No.: US 2012/0310602 A1Ryan MullinsNo ratings yet
- Us20120045042 PDFDocument23 pagesUs20120045042 PDFLissette HolderNo ratings yet
- 106 Yms @eiei: (19) United StatesDocument15 pages106 Yms @eiei: (19) United Statesacela3248No ratings yet
- Ulllted States Patent (10) Patent N0.: US 8,019,846 B2Document6 pagesUlllted States Patent (10) Patent N0.: US 8,019,846 B2Miguel Angel Bernabe CruzNo ratings yet
- Alt-O. : Indlvlduelly /@Document7 pagesAlt-O. : Indlvlduelly /@drivinerNo ratings yet
- SPE 187610 Application of Real-Time Data and Integrated Models in An AutomatedDocument15 pagesSPE 187610 Application of Real-Time Data and Integrated Models in An AutomatedEdgar GonzalezNo ratings yet
- E-Ticketing: Govind Ballabh Pant Engineering CollegeDocument31 pagesE-Ticketing: Govind Ballabh Pant Engineering CollegeAmanpwl92No ratings yet
- Intelligent Field Data ManagementDocument10 pagesIntelligent Field Data ManagementseemsaamNo ratings yet
- Design and Development of Microcontroller Based Electronic Queue Control SystemDocument5 pagesDesign and Development of Microcontroller Based Electronic Queue Control SystemFrederico MailaNo ratings yet
- Lecture Notes: (R15A0529) B.Tech Iv Year - I Sem (R15) (2019 - 20)Document223 pagesLecture Notes: (R15A0529) B.Tech Iv Year - I Sem (R15) (2019 - 20)javed prince786No ratings yet
- Commercial Branch Corporate Office 7 Floor, Bharat Sanchar Bhawan, H C Mathur Lane, Janpath, New Delhi 110001Document2 pagesCommercial Branch Corporate Office 7 Floor, Bharat Sanchar Bhawan, H C Mathur Lane, Janpath, New Delhi 110001Kabul DasNo ratings yet
- Anomaly Detection SystemsDocument46 pagesAnomaly Detection SystemsRajwecNo ratings yet
- Performance Analysis of A ®xed Local Anchor Scheme For Supporting UPT ServicesDocument14 pagesPerformance Analysis of A ®xed Local Anchor Scheme For Supporting UPT Servicesrawatbs2020No ratings yet
- PSTNDocument30 pagesPSTNShawn LeeNo ratings yet
- SIM7100 - ECALL - Application Note - V0.01Document17 pagesSIM7100 - ECALL - Application Note - V0.01pprandiniNo ratings yet
- Incrmental Heat RateDocument4 pagesIncrmental Heat RatePerumal PrabhuNo ratings yet
- Stopping Time Optimisation in Condition Monitoring: Tony RosqvistDocument7 pagesStopping Time Optimisation in Condition Monitoring: Tony Rosqvistho-faNo ratings yet
- Programmable Instruments Virtual InstrumDocument8 pagesProgrammable Instruments Virtual InstrumGraham KovalskyNo ratings yet
- Israsena, Kale 2006 - 2 FinalDocument5 pagesIsrasena, Kale 2006 - 2 FinalAbdullah Sha Navas KhanNo ratings yet
- Sjisr 3 3 359 369Document11 pagesSjisr 3 3 359 369Võ Hoàng KhôiNo ratings yet
- Inplant Training ReportDocument30 pagesInplant Training ReportTirumala Venkatesh100% (1)
- MssDocument93 pagesMsspoonamj24No ratings yet
- Transactions On FOR: K.S.SoDocument8 pagesTransactions On FOR: K.S.SoChandra ShettyNo ratings yet
- 08 OS86078EN41GLN1 Use Cases ExerciseDocument13 pages08 OS86078EN41GLN1 Use Cases ExerciseabedhamedshabiNo ratings yet
- 0420 w11 QP 13Document20 pages0420 w11 QP 13Wael El GendyNo ratings yet
- United States: (12) Patent Application Publication (10) Pub. No.: US 2006/0123363 A1Document20 pagesUnited States: (12) Patent Application Publication (10) Pub. No.: US 2006/0123363 A1coso1234No ratings yet
- Digital StethoscopeDocument28 pagesDigital StethoscopeHimanshu SaxenaNo ratings yet
- Internet of ThingsDocument5 pagesInternet of Thingsshaikrafi 13022001No ratings yet
- (NEW) Prepaid Electricity Billing IEEE 2014Document4 pages(NEW) Prepaid Electricity Billing IEEE 2014HarshalNo ratings yet
- Estimation of Dozer Production and Costs (OK)Document12 pagesEstimation of Dozer Production and Costs (OK)Denny TegarNo ratings yet
- Design Distributed Control System Power Supply of The TelecommunicationDocument4 pagesDesign Distributed Control System Power Supply of The TelecommunicationJorge MongesNo ratings yet
- Intelligent System Design of Microcontroller Based Real Time Process Control Trainer .Document12 pagesIntelligent System Design of Microcontroller Based Real Time Process Control Trainer .Kelvin NnamaniNo ratings yet
- Fault Detection and Diagnosis For Sensor in An Aero-Engine SystemDocument6 pagesFault Detection and Diagnosis For Sensor in An Aero-Engine Systemjymcrusher42No ratings yet
- Development of Smart Human Machine Interface PDFDocument4 pagesDevelopment of Smart Human Machine Interface PDFDave EzraNo ratings yet
- Application Platform and Token Generation Software For Prepayment Meter Administration in Electricity Distribution CompaniesDocument10 pagesApplication Platform and Token Generation Software For Prepayment Meter Administration in Electricity Distribution CompaniesCaptain ZedNo ratings yet
- A PROJECT REPORT ON Electronic Voting MachineDocument97 pagesA PROJECT REPORT ON Electronic Voting Machinereddu143No ratings yet
- Ip NewDocument24 pagesIp NewOm PandeyNo ratings yet
- Wireless Monitoring System For Lightweight Aircraft Landing GearDocument6 pagesWireless Monitoring System For Lightweight Aircraft Landing Gear759305169No ratings yet
- Work Force Management Workforce ManagementDocument27 pagesWork Force Management Workforce Managementdeepalim03No ratings yet
- ICCPDocument107 pagesICCPedy_marcelo6262100% (1)
- ApoorvaDocument25 pagesApoorvaSiddhant GuptaNo ratings yet
- SS7 Training and Sigtran Training Provided by SS7Document13 pagesSS7 Training and Sigtran Training Provided by SS7parulparas1100% (2)
- 165.zeppelin Reservation SystemDocument5 pages165.zeppelin Reservation SystemAmit AmitNo ratings yet
- Sensor Information Fusion For The Needs of Fault Diagnosis in Marine Diesel Engine Propulsion PlantDocument7 pagesSensor Information Fusion For The Needs of Fault Diagnosis in Marine Diesel Engine Propulsion PlantAmitabhaNo ratings yet
- Practical Knowledge About: Data: Acquisition, Metering, Monitoring and ManagementDocument8 pagesPractical Knowledge About: Data: Acquisition, Metering, Monitoring and ManagementxhunguNo ratings yet
- Digital CounterDocument57 pagesDigital Counter08078767% (3)
- World Bank CV FormatDocument7 pagesWorld Bank CV FormatTanveer AzizNo ratings yet
- Automatizare Macarale-31-45Document15 pagesAutomatizare Macarale-31-45alin grecuNo ratings yet
- (Total No of Pages - 19) : HQ SFCDocument20 pages(Total No of Pages - 19) : HQ SFCdillipsh123No ratings yet
- Powermind Insights CEA 01122023Document5 pagesPowermind Insights CEA 01122023Vanaja DNo ratings yet
- OPC Security WP2Document22 pagesOPC Security WP2selavilizationNo ratings yet
- Ch-11-Computerization in Weld InspectionDocument6 pagesCh-11-Computerization in Weld InspectionAram HovsepianNo ratings yet
- Sesar ConopsDocument214 pagesSesar ConopsDaniel Stanescu100% (1)
- S2000 VB20 DCSDocument164 pagesS2000 VB20 DCSVimak_46100% (1)
- Metering Manual - PgcilDocument93 pagesMetering Manual - PgcilKrishna Venkataraman100% (1)
- Digital Twin For Energy Optimization in AnDocument5 pagesDigital Twin For Energy Optimization in AnNoveri Dwi HardyantoNo ratings yet
- Kertas Penerangan: Institut Teknologi Perak E-3-10, Greentown Square, Jalan Dato' Seri Ahmad Said, 30450, IPOH, PERAKDocument6 pagesKertas Penerangan: Institut Teknologi Perak E-3-10, Greentown Square, Jalan Dato' Seri Ahmad Said, 30450, IPOH, PERAKMuhammad ZuhairiNo ratings yet
- Index Modulation Techniques For 5G Wireless Networks: Ertugrul Basar, Senior Member, IEEEDocument14 pagesIndex Modulation Techniques For 5G Wireless Networks: Ertugrul Basar, Senior Member, IEEEacela3248No ratings yet
- System and Method For Switching Foreign Patent Documents Between Base Stations in A Wireless Communications SystemDocument10 pagesSystem and Method For Switching Foreign Patent Documents Between Base Stations in A Wireless Communications Systemacela3248No ratings yet
- Terminal and Information Relay ApparatusDocument13 pagesTerminal and Information Relay Apparatusacela3248No ratings yet
- Discontinuous Inquiry For Wireless CommunicationDocument40 pagesDiscontinuous Inquiry For Wireless Communicationacela3248No ratings yet
- Pa3 - Us20110199908Document12 pagesPa3 - Us20110199908acela3248No ratings yet
- United States Patent: (12) (10) Patent N0.: US 6,766,454 B1Document27 pagesUnited States Patent: (12) (10) Patent N0.: US 6,766,454 B1acela3248No ratings yet
- Neighboring Cell Search Techniques For LTE Systems: CitationDocument7 pagesNeighboring Cell Search Techniques For LTE Systems: Citationacela3248No ratings yet
- Icc13 Part1 YenerDocument121 pagesIcc13 Part1 Yeneracela3248No ratings yet
- Bathinda - Wikipedia, The Free EncyclopediaDocument4 pagesBathinda - Wikipedia, The Free EncyclopediaBhuwan GargNo ratings yet
- 16 Personalities ResultsDocument9 pages16 Personalities Resultsapi-605848036No ratings yet
- Datos Adjuntos Sin Título 00013Document3 pagesDatos Adjuntos Sin Título 00013coyana9652No ratings yet
- R15 Understanding Business CyclesDocument33 pagesR15 Understanding Business CyclesUmar FarooqNo ratings yet
- Steel Price Index PresentationDocument12 pagesSteel Price Index PresentationAnuj SinghNo ratings yet
- Islamiyat ProjectDocument21 pagesIslamiyat ProjectSubhan Khan NiaziNo ratings yet
- Contigency Plan On Class SuspensionDocument4 pagesContigency Plan On Class SuspensionAnjaneth Balingit-PerezNo ratings yet
- Mangement of Shipping CompaniesDocument20 pagesMangement of Shipping CompaniesSatyam MishraNo ratings yet
- Sodexo GermanyDocument13 pagesSodexo GermanySandeep Kumar AgrawalNo ratings yet
- Abc Uae Oil and GasDocument41 pagesAbc Uae Oil and GasajayNo ratings yet
- 2432 - Test Solutions - Tsol - 2432 - 21702Document5 pages2432 - Test Solutions - Tsol - 2432 - 21702Anmol PanchalNo ratings yet
- Flowrox Valve Solutions Catalogue E-VersionDocument16 pagesFlowrox Valve Solutions Catalogue E-Versionjavier alvarezNo ratings yet
- Module 2Document7 pagesModule 2karthik karti100% (1)
- Specimen Signature FormDocument27 pagesSpecimen Signature FormnandukyNo ratings yet
- Pontevedra 1 Ok Action PlanDocument5 pagesPontevedra 1 Ok Action PlanGemma Carnecer Mongcal50% (2)
- Agm 1602W-818Document23 pagesAgm 1602W-818Daniel BauerNo ratings yet
- Using Visual Rating To Diagnose DementiaDocument10 pagesUsing Visual Rating To Diagnose DementiaImágenes Rosendo GarcíaNo ratings yet
- Nature of Science-Worksheet - The Amoeba Sisters HWDocument2 pagesNature of Science-Worksheet - The Amoeba Sisters HWTiara Daniel25% (4)
- Laudon - Mis16 - PPT - ch11 - KL - CE (Updated Content For 2021) - Managing Knowledge and Artificial IntelligenceDocument45 pagesLaudon - Mis16 - PPT - ch11 - KL - CE (Updated Content For 2021) - Managing Knowledge and Artificial IntelligenceSandaru RathnayakeNo ratings yet
- Paper II - Guidelines On The Use of DuctlessDocument51 pagesPaper II - Guidelines On The Use of DuctlessMohd Khairul Md DinNo ratings yet
- Anthony Robbins - Time of Your Life - Summary CardsDocument23 pagesAnthony Robbins - Time of Your Life - Summary CardsWineZen97% (58)
- Asu 2019-12Document49 pagesAsu 2019-12janineNo ratings yet
- Flip The Coin - EbookDocument306 pagesFlip The Coin - EbookAjesh Shah100% (1)
- Remedy MidTier Guide 7-5Document170 pagesRemedy MidTier Guide 7-5martin_wiedmeyerNo ratings yet
- Micro - Systemic Bacteriology Questions PDFDocument79 pagesMicro - Systemic Bacteriology Questions PDFShashipriya AgressNo ratings yet
- Lakh Only) Being The Amount Covered Under The Aforesaid Dishonoured Cheque, and So AlsoDocument2 pagesLakh Only) Being The Amount Covered Under The Aforesaid Dishonoured Cheque, and So AlsoShivam MishraNo ratings yet
- Nse 2Document5 pagesNse 2dhaval gohelNo ratings yet
- BA 4722 Marketing Strategy SyllabusDocument6 pagesBA 4722 Marketing Strategy SyllabusSri GunawanNo ratings yet
- Aspek Perpajakan Dalam Transfer Pricing: Related PapersDocument15 pagesAspek Perpajakan Dalam Transfer Pricing: Related PapersHasrawati AzisNo ratings yet
- Nyambe African Adventures An Introduction To African AdventuresDocument5 pagesNyambe African Adventures An Introduction To African AdventuresKaren LeongNo ratings yet
- Algorithms to Live By: The Computer Science of Human DecisionsFrom EverandAlgorithms to Live By: The Computer Science of Human DecisionsRating: 4.5 out of 5 stars4.5/5 (722)
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityFrom EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityRating: 5 out of 5 stars5/5 (1)
- Digital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires Trying to Reinvent MoneyFrom EverandDigital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires Trying to Reinvent MoneyRating: 4 out of 5 stars4/5 (51)
- The Future of Geography: How the Competition in Space Will Change Our WorldFrom EverandThe Future of Geography: How the Competition in Space Will Change Our WorldRating: 4 out of 5 stars4/5 (6)
- Cyber War: The Next Threat to National Security and What to Do About ItFrom EverandCyber War: The Next Threat to National Security and What to Do About ItRating: 3.5 out of 5 stars3.5/5 (66)
- Scary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldFrom EverandScary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldRating: 4.5 out of 5 stars4.5/5 (55)
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveFrom EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveNo ratings yet
- Generative AI: The Insights You Need from Harvard Business ReviewFrom EverandGenerative AI: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (2)
- Chaos Monkeys: Obscene Fortune and Random Failure in Silicon ValleyFrom EverandChaos Monkeys: Obscene Fortune and Random Failure in Silicon ValleyRating: 3.5 out of 5 stars3.5/5 (111)
- ChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindFrom EverandChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindNo ratings yet
- The Intel Trinity: How Robert Noyce, Gordon Moore, and Andy Grove Built the World's Most Important CompanyFrom EverandThe Intel Trinity: How Robert Noyce, Gordon Moore, and Andy Grove Built the World's Most Important CompanyNo ratings yet
- The Infinite Machine: How an Army of Crypto-Hackers Is Building the Next Internet with EthereumFrom EverandThe Infinite Machine: How an Army of Crypto-Hackers Is Building the Next Internet with EthereumRating: 3 out of 5 stars3/5 (12)
- Solutions Architect's Handbook: Kick-start your career as a solutions architect by learning architecture design principles and strategiesFrom EverandSolutions Architect's Handbook: Kick-start your career as a solutions architect by learning architecture design principles and strategiesNo ratings yet
- AI Superpowers: China, Silicon Valley, and the New World OrderFrom EverandAI Superpowers: China, Silicon Valley, and the New World OrderRating: 4.5 out of 5 stars4.5/5 (398)
- The E-Myth Revisited: Why Most Small Businesses Don't Work andFrom EverandThe E-Myth Revisited: Why Most Small Businesses Don't Work andRating: 4.5 out of 5 stars4.5/5 (709)
- Four Battlegrounds: Power in the Age of Artificial IntelligenceFrom EverandFour Battlegrounds: Power in the Age of Artificial IntelligenceRating: 5 out of 5 stars5/5 (5)
- ChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessFrom EverandChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessNo ratings yet
- Reality+: Virtual Worlds and the Problems of PhilosophyFrom EverandReality+: Virtual Worlds and the Problems of PhilosophyRating: 4 out of 5 stars4/5 (24)
- The Manager's Path: A Guide for Tech Leaders Navigating Growth and ChangeFrom EverandThe Manager's Path: A Guide for Tech Leaders Navigating Growth and ChangeRating: 4.5 out of 5 stars4.5/5 (99)
- Chip War: The Quest to Dominate the World's Most Critical TechnologyFrom EverandChip War: The Quest to Dominate the World's Most Critical TechnologyRating: 4.5 out of 5 stars4.5/5 (228)
- Mini Farming: Self-Sufficiency on 1/4 AcreFrom EverandMini Farming: Self-Sufficiency on 1/4 AcreRating: 4 out of 5 stars4/5 (76)
- The Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldFrom EverandThe Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldRating: 4.5 out of 5 stars4.5/5 (107)
- The Things We Make: The Unknown History of Invention from Cathedrals to Soda Cans (Father's Day Gift for Science and Engineering Curious Dads)From EverandThe Things We Make: The Unknown History of Invention from Cathedrals to Soda Cans (Father's Day Gift for Science and Engineering Curious Dads)No ratings yet