Professional Documents
Culture Documents
Auditing Racf
Uploaded by
சிங்கார வேலன்Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Auditing Racf
Uploaded by
சிங்கார வேலன்Copyright:
Available Formats
Copyright 2000, 2006 EKC Inc.
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Auditing the
Auditing the
RACF
RACF
Environment
Environment
Topic 1: Auditing RACF
Auditing 2
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Topic 1 Objectives
Topic 1 Objectives
The Audit Environment
Sample Audit Points
Audit Controls
Audit Data
Audit Reporting
Auditing 3
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Separation of Powers
Separation of Powers
SPECIAL AUDITOR
Auditing 4
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Conducting the Audit
Conducting the Audit
Judge how effectively RACF has been
implemented to handle security at the
installation.
Identify any security exposures.
Recommend ways to improve the system.
Auditing 5
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
The Audit Cycle
The Audit Cycle
Establish Benchmark
Check loggings regularly
Re-examine security implementation and
compare against last benchmark
Establish new benchmark
Auditing 6
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Twelve Point Approach
Twelve Point Approach
Point 1 - System Controls - Level of Implementation
Point 2 - Change Control Over Options and Software
Point 3 - Protection for Database and SMF Files
Point 4 - Enforcement of Security Policy
Point 5 - Password Administration
Point 6 - Approach to Access Profiles
Auditing 7
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Twelve Point Approach
Twelve Point Approach
Point 7 - Ability to Bypass Controls
Point 8 - Control of Non-Owned Ids
Point 9 - Controls Over Production Ids
Point 10 - Controls for Key System Components
Point 11 - Ability to Gain Unauthorized Access
Point 12 - Security Reporting and Follow-Up
Auditing 8
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
1 1 - - System Implementation System Implementation
Limit / Control / Review
Where to Look
RACF Release level
System Release level
DSMON
System Report
shows zOS and RACF
Release / FMID levels
SETROPTS LIST
shows module names and
lengths of installed exits
shows PROTECTALL
level and options
RACF Exits
DSMON System
Exits Report
PROTECTALL settings
Auditing 9
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
2 2 Administration / Change Control Administration / Change Control
Limit / Control / Review
Where to Look
assignment of
system-SPECIAL
DSMON Selected
User Attribute
Report
shows number of users
and user IDs given
system-SPECIAL
use of RVARY command SETROPTS LIST
shows if there is an
RVARY password specified
use of SETROPTS
REFRESH command
DSMON SUAR
shows number of users
and user IDs with SPECIAL
and AUDITOR
Auditing 10
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
3 3 Securing access to RACF & SMF Securing access to RACF & SMF
Limit / Control / Review
Where to Look
Access to RACF
database carefully
controlled
LISTDSD
shows access lists for
primary and backup
RACF databases
LISTDSD
Site specific
Access to SMF
files limited
shows access lists for
primary and backup
RACF databases
Review procedures and
schedule for backup
of RACF database(s)
Regularly scheduled
backups of RACF
database files
Auditing 11
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
4 4 Security Policy Review Security Policy Review
Limit / Control / Review
Where to Look
Determine existence
of security policy
Interviews with Security management staff.
Procedures in place
for PASSWORD
changes, makeup.
Review site specific procedures,
SETROPTS LIST
Handeling of deleted
userids
Review site specific procedures
Auditing 12
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
5 5 Password Policy Review Password Policy Review
Limit / Control / Review
Where to Look
Periodic required
password change
Review change interval.
PASSWORD
length
Review site specific
procedures,
Review unsuccessful
password attempts
SETROPTS LIST
SETROPTS LIST
PASSWORD
hacking
SETROPTS LIST
Auditing 13
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
6 6 Access Hierarchy Access Hierarchy
Limit / Control / Review
Where to Look
Verify access lists
for individuals and
groups
Review groups to determine
definition and use of
functional groups.
Verify appropriate
UACC access
Review dataset profiles for
apropriate UACC access.
DSMON
GROUP TREE
LISTDSD
Verify OWNER data
for profiles and
groups
LISTDSD
DSMON
GROUP TREE
Review owner data to
determine inheritance of
data / application ownership
Auditing 14
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
7 7 Ability to Bypass Controls Ability to Bypass Controls
Limit / Control / Review
Where to Look
Verify SETROPTS
PROTECTALL active
in FAILURE mode
shows if
PROTECTALL FAILURE
is in effect
SETROPTS LIST
shows if profile creator is
automatically added with
ALTER to access list
DSMON
shows number of users
with OPERATIONS
SETROPTS LIST
Ensure SETROPTS
NOADDCREATOR
is applied
Minimize use of
OPERATIONS
attribute
Auditing 15
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
8 8 Non Non- -Owned Owned Userids Userids
Limit / Control / Review
Where to Look
Use of region IDs for
batch jobs submitted
on behalf of users
SEARCH CLASS(PROPCNTL)
NOMASK
Search for
PROPCNTL
profiles
Review use of
surrogate profiles
Search for
SURROGAT
profiles
SEARCH CLASS(SURROGAT)
NOMASK
Auditing 16
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
9 9 Controls over Production IDs Controls over Production IDs
Limit / Control / Review
Where to Look
Review rationale used
to associate production
IDs with jobs
Site specific
Verify controls
over production
JCL libraries
Dataset
profiles
Review profiles to ensure
appropriate access
Review SURROGAT
use to ensure only
authorized use
SURROGAT
profiles
RL userid.SUBMIT
CL(SURROGAT) AU
Auditing 17
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
10 10 Key System Components Key System Components
Limit / Control / Review
Where to Look
Review inventory of
products requiring
security interface
Site specific-
List of installed products
Verify adequacy of
access controls
in place
Review general resource profiles
for vendor products.
Assure adequate use
of SAF-based
controls
DSMON Authorized
Caller Report
Auditing 18
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
11 11 Ability to gain unauthorized access Ability to gain unauthorized access
Limit / Control / Review
Where to Look
User IDs which have
never been used or not
used for an extended
period of time
SEARCH CLASS(USER) AGE(120)
Default userids
(IBMUSER)
LU IBMUSER
RACF default
password
Review procedures for changing passwords
Auditing 19
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
12 12 Security Reporting and Follow Security Reporting and Follow- -up up
Limit / Control / Review
Where to Look
Review types and
frequency of
reports
Review report
distribution
Determine actions
from violation
attempts
Site specific procedures
Site specific procedures
Site specific procedures
Auditing 20
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Auditor Controls
Auditor Controls
General Controls
SETROPTS Commands SETR AUDIT(*)
Specific Controls
User activity ALU
Dataset activity ALTDSD
Resource activity RALTER
Auditing 21
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Audit Controls
Audit Controls
-
-
SETROPTS
SETROPTS
APPLAUDIT and NOAPPLAUDIT
AUDIT and NOAUDIT
CMDVIOL and NOCMDVIOL
LIST
LOGOPTIONS
OPERAUDIT and NOOPERAUDIT
REFRESH GENERIC
REFRESH RACLIST
SAUDIT and NOSAUDIT
SECLABELAUDIT and NOSECLABELAUDIT
SECLEVELAUDIT and NOSECLEVELAUDIT
Auditing 22
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Controlling Logging
Controlling Logging
Application
Owner
SYS1.MANx
Auditor
Auditing 23
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Owner
Owner
-
-
Controlled Logging
Controlled Logging
ALTDSD 'PAYROLL.MASTER.*'
AUDIT(FAILURES(READ))
PAYROLL.MASTER.* . . . FAILURES(READ)
Profile Name AUDIT GLOBALAUDIT
Auditing 24
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Auditor Controls
Auditor Controls
Logging
Logging
ALTDSD 'PAYROLL.MASTER.*'
GLOBALAUDIT(SUCCESS(UPDATE))
SETR LOGOPTIONS(ALWAYS(DASDVOL))
SETR LOGOPTIONS(FAILURES(TERMINAL))
PAYROLL.MASTER.* . . . FAILURES(READ) SUCCESS(UPDATE)
Profile Name AUDIT GLOBALAUDIT
ALU STAN UAUDIT
Auditing 25
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Two Types of Audit Data
Two Types of Audit Data
Snapshot Data The Implementation
RACF Commands L, SETR LIST
Data Security Monitor DSMON
RACF Database Unload IRRDBU00
Event Data Wazhappnin???
RACF Commands LOGOPTIONS, GLOBALAUDIT
SMF Data Unload Utility IFASMFDP
Reporting Tools SAMPLIB
RICE reports ICEMAN statements for DB & SMF unloaded data
DB2 queries RACDBUxx, IRRADUxx
Auditing 26
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Running the DSMON Program
Running the DSMON Program
I
C
H
D
S
M
0
0
//stepname EXEC PGM=ICHDSM00
//SYSPRINT DD SYSOUT=A
//SYSUT2 DD SYSOUT=A
//SYSIN DD *
LINECOUNT 55
FUNCTION ALL
USEROPT USRDSN PAY.MASTER.FILE
Hardware
Software
D
S
M
O
N
R
e
p
o
r
ts
Auditing 27
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
DSMON Reports
DSMON Reports
Selected Data Sets Report
Group Tree Report
RACF Global Access Table Report
RACF Class Descriptor Table Report
RACF Started Procedures Table Report
Selected User Attribute Summary Report
Selected User Attribute Report
RACF Authorized Caller Table Report
Program Properties Table Report
System Report
CPU-ID
CPU MODEL
OPERATING SYSTEM/LEVEL z/OS . . .
SYSTEM RESIDENCE VOLUME
RACF FMID HRF7709 IS ACTIVE
D
S
M
O
N
R
e
p
o
r
t s
RACF Exits Report
Auditing 28
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
System Report
System Report
CPU-ID 111606
CPU MODEL 2064
OPERATING SYSTEM/LEVEL z/OS 1.6.0
SYSTEM RESIDENCE VOLUME DR250B
SMF-ID ZOSR
RACF FMID HRF7709 IS ACTIVE
Auditing 29
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Program Properties Table Report Program Properties Table Report
PROGRAM BYPASS PASSWORD SYSTEM
NAME PROTECTION KEY
---------------------------------------------------------------------------------
IEDQTCAM NO YES
ISTINM01 YES YES
IKTCAS00 NO YES
AHLGTF NO YES
HHLGTF NO YES
IHLGTF NO YES
IEFIIC NO YES
IEEMB860 YES YES
IEEVMNT2 NO YES
IASXWR00 NO YES
CSVVFCRE NO YES
HASJES20 YES YES
DFSMVRC0 NO YES
IATINTK YES YES
DXRRLM00 NO YES
Auditing 30
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
RACF Authorized Caller Table Report RACF Authorized Caller Table Report
MODULE RACINIT RACLIST
NAME AUTHORIZED AUTHORIZED
---------------------------------------------------------------------------
DFHSIP NO YES
Auditing 31
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
RACF Exit Report
RACF Exit Report
EXIT MODULE MODULE
NAME LENGTH
----------------------------------------------------------
ICHPWX01 1354
ICHDEX01 224
Auditing 32
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Selected User Attribute Report
Selected User Attribute Report
USERID ---------------- ATTRIBUTE TYPE ----------------------------------------- ASSOCIATIONS ----------------------
SPECIAL OPERATIONS AUDITOR REVOKE NODE.USERID PASSWORD ASSOCIATION
SYNC TYPE
---------------------------------------------------------------------------------------------------------------------------------------------------
BIGBIRD SYSTEM SYSTEM
BERT SYSTEM
ELMO GROUP GROUP
ERNIE SYSTEM SYSTEM
GROVER SYSTEM SYSTEM
GROUCH GROUP
IBMUSER SYSTEM SYSTEM SYSTEM
SNUFFY GROUP
ZOE GROUP
Auditing 33
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Selected User Attribute Summary Selected User Attribute Summary
--------------------------------------------------------------------------------------------------------------
TOTAL DEFINED USERS: 563
TOTAL SELECTED ATTRIBUTE USERS:
ATTRIBUTE BASIS SPECIAL OPERATIONS AUDITOR REVOKE
-------------------------- ------------- -------------------- -------------- -------------
SYSTEM 4 3 1 2
GROUP 1 2 1 1
Auditing 34
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Started Procedures Table Report Started Procedures Table Report
FROM THE STARTED PROCEDURES TABLE (ICHRIN03):
FROM PROFILES IN THE STARTED CLASS:
------------------------------------------------------------------------------------------------------------------------------------------------
PROFILE ASSOCIATED ASSOCIATED
NAME USER GROUP PRIVILEGED TRUSTED TRACE
------------------------------------------------------------------------------------------------------------------------------------------------
CICS.REGIONA CICSA NO NO NO
CICS.REGIONB CICSB NO NO NO
DCEKERN.* (G) DCEKERN DCEGRP NO NO NO
EZAFTPAP.* (G) TCPIP OMVSGRP NO YES NO
FTPD.* (G) OMVSKERN OMVSGRP NO NO NO
MVSNFS.* (G) TCPIP OMVSGRP NO NO NO
OMVS.* (G) OMVSKERN OMVSGRP NO NO NO
PORTMAP.* (G) TCPIP OMVSGRP NO YES YES
FTPSERVE.* (G) TCPIP OMVSGRP NO YES NO
INETD.* (G) INETD SYS1 NO NO NO
SMF.* (G) STCUSR SYS1 NO YES NO
IRRDPTAB.* (G) STCUSR SYS1 NO YES NO
JES2.* (G) STCUSR SYS1 NO YES NO
LLA.* (G) STCUSR SYS1 NO YES NO
TSO.* (G) TSO TSOGRP NO NO NO
VTAM.* (G) VTAM VTAMGRP NO YES NO
LOGREC.* (G) LOGREC SYS1 NO NO NO
** (G) =MEMBER STCGRP NO NO YES
Auditing 35
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Class Descriptor Table Report
Class Descriptor Table Report
CLASS DEFAULT OPERATIONS
NAME STATUS AUDITING STATISTICS UACC ALLOWED
----------------------------------------------------------------------------------------------------------------------------
RACFVARS ACTIVE NO NO NONE NO
SECLABEL INACTIVE NO NO NONE NO
DASDVOL ACTIVE NO NO ACEE YES
GDASDVOL ACTIVE NO NO ACEE YES
TAPEVOL ACTIVE NO NO ACEE YES
TERMINAL INACTIVE NO NO ACEE NO
GTERMINL INACTIVE NO NO ACEE NO
APPL ACTIVE NO NO NONE NO
TIMS INACTIVE NO NO NONE NO
GIMS INACTIVE NO NO NONE NO
AIMS INACTIVE NO NO NONE NO
TCICSTRN ACTIVE NO NO NONE NO
GCICSTRN ACTIVE NO NO NONE NO
PCICSPSB INACTIVE NO NO NONE NO
GLOBAL ACTIVE NO NO NONE NO
GMBR INACTIVE NO NO NONE NO
DSNR INACTIVE NO NO ACEE NO
FACILITY ACTIVE NO NO NONE NO
Auditing 36
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Global Access Checking Table Report Global Access Checking Table Report
CLASS ACCESS ENTRY
NAME LEVEL NAME
----------------------------------------------------------------------------------------
DATASET ALTER &RACUID.*
READ ISPF.*
UPDATE SYS1.BRODCAST
RVARSMBR -- NO ENTRIES --
SECLABEL -- NO ENTRIES --
DASDVOL -- NO ENTRIES --
TAPEVOL -- NO ENTRIES --
TERMINAL -- NO ENTRIES --
APPL -- NO ENTRIES --
TIMS -- NO ENTRIES --
AIMS -- NO ENTRIES --
TCICSTRN -- NO ENTRIES --
PCICSPSB -- NO ENTRIES --
Auditing 37
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Group Tree Report
Group Tree Report
LEVEL GROUP (OWNER)
---------------------------------------------------------
1 SYS1 (IBMUSER)
|
2 | DATASETG (TOMC)
| |
3 | | ABA
| |
3 | | ARP
| | |
4 | | | ARPLST
|
2 | CICSADM
| |
3 | | TRANA
| |
3 | | TRANB
|
2 | DATACTRL
Auditing 38
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Selected Data Sets Report
Selected Data Sets Report
VOLUME SELECTION
DATA SET NAME SERIAL CRITERION
-------------------------------------------------------------------------------------------
PAY.MASTER.FILE USER23 USERDSN
PAY.SALARY.FILE USER23 USERDSN
ISP.PPLIB.ISPLLIB M80LIB LNKLST - APF
ISP.V3R1M0.ISPLOAD M80LIB APF
ISP.V3R2M0.ISPLOAD M80LIB APF
LNKLST - APF
JES2311.STEPLIB SMS036 APF
JES2313.STEPLIB SMS036 APF
JES2410.STEPLIB SMS036 APF
JES2420.STEPLIB SMS036 APF
SYS1.CMDLIB JS2RES APF
LNKLST - APF
SYSTEM
SYS1.COBLIB M80LIB LNKLST - APF
SYS1.LINKLIB MVSRES LNKLST - APF
SYSTEM
SYS1.NCATLG M80PGE MASTER CATALOG
SYS1.NUCLEUS MVSRES SYSTEM
SYS1.PROCLIB M80PGE SYSTEM
SYS1.RACF.BACKUP SMS124 RACF BACKUP
SYS1.RACF.PRIMARY SMS073 RACF PRIMARY
SYS1.UADS M80PGE SYSTEM
RACF RACF
INDICATED PROTECTED UACC
-------------------------------------------------------
NO YES NONE
NO YES NONE
NO YES READ
N.F YES READ
NO YES READ
N.C YES READ
NO YES READ
NO YES READ
NO YES READ
NO YES READ
NO YES READ
N.F YES NONE
NO YES READ
NO YES NONE
NO YES NONE
NO YES NONE
NO YES NONE
NO YES NONE
Auditing 39
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Reporting on the Unloaded Database Reporting on the Unloaded Database
Valid users
IRRDBU00
Output Data
R
e
p
o
r
ts
Selected groups
Connections
MVS Open Edition
SQL Queries
or ICETOOLs
Auditing 40
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
SMF Data Unload Utility
SMF Data Unload Utility
DB2 or
Other
RDMS
IFASMFDP
ICETOOL
or Utilities
Installation
Written
Programs
Browse
SMF Data
Unloaded
SMF Data
USER2(IRRADU00)
USER3(IRRADU86)
Auditing 41
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
SMF Unload JCL Example
SMF Unload JCL Example
//SMFUNLD JOB ,'SMF DATA UNLOAD',
// MSGLEVEL=(1,1),TYPRUN=HOLD
//SMFDUMP EXEC PGM=IFASMFDP
//SYSPRINT DD SYSOUT=A
//ADUPRINT DD SYSOUT=A
//OUTDD DD DISP=SHR,DSN=USER01.RACF.IRRADU00
//SMFDATA DD DISP=SHR,DSN=USER01.RACF.SMFDATA
//SMFOUT DD DUMMY
//SYSIN DD *
INDD(SMFDATA,OPTIONS(DUMP))
OUTDD(SMFOUT,TYPE(000:255))
ABEND(NORETRY)
USER2(IRRADU00)
USER3(IRRADU86)
/*
Auditing 42
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Samplib
Samplib
Tools Available
Tools Available
IRRICE Collection
Uses DFSORT and ICETOOL to produce reports
based on Unloaded Database data and SMF data.
IRRADULD, ..QR, ..TB
Uses SQL to define (TB), Load (LD), and Query
(QR) auditing (unloaded SMF) data.
RACDBULD, ..QR, ..TB
Uses SQL to define (TB), Load (LD), and Query
(QR) security definition data.
Auditing 43
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Sample IRRDBU00 Report
Sample IRRDBU00 Report
- 1 - UAGR: GR Profiles with a UACC Other Than None 06/09/28
Class General Resource Profile Name Generic Owner UACC
-------- ----------------------------- ------- -------- --------
DSNR DSN.WLM_REFRESH.DB8GENV1 NO 0 P390A READ
DSNR SYSPROC.WLM_REFRESH.DB8GRFSH NO 0 P390A READ
DSNR SYSPROC.WLM_REFRESH.WLMENV1 NO 0 IBMUSER READ
DSNR SYSPROC.WLM_REFRESH.WLMENV2 NO 0 IBMUSER READ
FIRECALL FIRECALL NO 0 SYS1 READ
FACILITY DITTO.* YES 0 IBMUSER READ
FACILITY MVSADMIN.WLM.POLICY NO 0 IBMUSER READ
Auditing 44
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Sample IRRADU00 Report
Sample IRRADU00 Report
- 1 - CADU: Number of IRRADU00 Events
06/09/28 09:57:32 am
Type Count
-------- ---------------
ACCESS 1842
ALTUSER 6
CONNECT 3
DACCESS 1
DEFINE 4
DIRSRCH 15
JOBINIT 2951
PERMIT 1
RDEFINE 2
REMOVE 3
SETROPTS 1
Auditing 45
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Conducting the Audit
Conducting the Audit
Weve checked the RACF implementation
for appropriate security controls.
Identified security exposures.
Made our recommendations.
Whats this 18 hour Special?
Copyright 2000, 2006 EKC Inc.
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Part 2: Emergency Access
Auditing 47
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
What is Emergency Access?
What is Emergency Access?
Non-standard access
Storage fixes
General Error fixes
System upgrades
Testing the Recovery Plan
Auditing 48
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Typical Methods
Typical Methods
May I have the envelope please?
Temporary connect
Scheduled connect
Always on, just in case security
Secondary accounts
Auditing 49
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
The Pre
The Pre
-
-
loaded Account
loaded Account
All the access in the world
Keeping it relevant
Turning it off / Re-loading
Not tied to an individual
Accounting for use
Auditing 50
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Temporary Connection
Temporary Connection
Connect at 5pm
Disconnect at 9am
Is it enough?
Less difficult to audit
Request/approval trace
Auditing 51
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Temporary Connection
Temporary Connection
Scheduled connect at 3am
Disconnect at 9am
Is it enough?
Less difficult to audit
Request/approval trace
Auditing 52
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
The Trusted Professional
The Trusted Professional
Extra access for the normal fixer
Enough access for typical emergencies
May not be enough
Difficult to audit
What paper trail?
Auditing 53
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Dual Accounts
Dual Accounts
Secondary account for the normal fixer
Enough access for typical emergencies
May not be enough
Less difficult to audit
After the fact request/approval
Auditing 54
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
The Business Recovery Plan
The Business Recovery Plan
Most companies use test data, right?
DRP accounts do everything
Minimum alteration risk
Maximum disclosure risk
Auditing the Recovery Test
Auditing 55
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
The BRP Reality
The BRP Reality
> -----Original Message-----
> From: RACF Discussion List On Behalf Of XXXX XXXXXXXX
>
> We want to give users testing programs in a D/R LPAR the
> authority to run production jobs. The production jobs run
> under the USERID of SYSMANT. What's the RACF command to allow
> this to happen.
PERMIT SYSMANT.SUBMIT CLASS(SURROGAT) ACCESS(READ) ID(userID) .
Auditing 56
Copyright 2000, 2006 EKC Inc.
www.ekcinc.com
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Emergency Access Recommendations Emergency Access Recommendations
Keep a good trail of request & authorization.
For periodical needs, use 2 accounts, log
access used by second account. (UAUDIT)
Rip up the envelope, get rid of the pre-loaded
account.
Collect and examine SMF data from DRP
Restrict or remove software capable of
editing raw SMF data.
Copyright 2000, 2006 EKC Inc.
Eberhard Klemens Co.
Experts in Computer
Systems - Software - Security
Audit Reporting & Emergency Access
You might also like
- 6th Central Pay Commission Salary CalculatorDocument15 pages6th Central Pay Commission Salary Calculatorrakhonde100% (436)
- RACF Commands - MVS TrainingDocument10 pagesRACF Commands - MVS TrainingSreejithsreenathNo ratings yet
- (SA22-7683-12) (V1R10) zOS - Security Server RACF Security Administrator's GuideDocument848 pages(SA22-7683-12) (V1R10) zOS - Security Server RACF Security Administrator's GuideJosé Antonio Osorio RodríguezNo ratings yet
- zCEE Customization Security With MVS Batch PDFDocument43 pageszCEE Customization Security With MVS Batch PDFapmountNo ratings yet
- Mainframe Admin Course SyllabusDocument4 pagesMainframe Admin Course SyllabusENDLURI DEEPAK KUMARNo ratings yet
- Tesla v. Zoox ComplaintDocument26 pagesTesla v. Zoox ComplaintmashablescribdNo ratings yet
- RACF - To - ACF2 CommandsDocument4 pagesRACF - To - ACF2 CommandsGino ThompsonNo ratings yet
- Racf - Auditing Unix On ZosDocument29 pagesRacf - Auditing Unix On ZosAlejandro PonceNo ratings yet
- r05 Racf Digital CertificateDocument32 pagesr05 Racf Digital CertificateryangangitanoNo ratings yet
- RacfDocument132 pagesRacfLeandro Gabriel LópezNo ratings yet
- RACF Utilities: KOIRUG April 2016Document40 pagesRACF Utilities: KOIRUG April 2016dinesh nali100% (1)
- RSH Consulting RACF Admin Authorities Oct 2005Document31 pagesRSH Consulting RACF Admin Authorities Oct 2005asimNo ratings yet
- Racf RexxDocument18 pagesRacf RexxalejandrosantanaasmNo ratings yet
- IBM Security ProductsDocument2 pagesIBM Security ProductsRafael MorenoNo ratings yet
- IPL Logic FlowDocument40 pagesIPL Logic FlowPriya Ekambaram100% (1)
- RACF6 Ichza7c0Document862 pagesRACF6 Ichza7c0Siranjeevi MohanarajaNo ratings yet
- How To+use QuickRefDocument223 pagesHow To+use QuickRefkashifmfNo ratings yet
- ABCs of Z.os System Programming Volume6Document420 pagesABCs of Z.os System Programming Volume6quezeeNo ratings yet
- Omega MomDocument534 pagesOmega MomshyhackerNo ratings yet
- SMF Utility With IRRADU00 and IRRADU86 ExitsDocument9 pagesSMF Utility With IRRADU00 and IRRADU86 ExitsKarthikeyan ChandramohanNo ratings yet
- RACFDocument55 pagesRACFpablo romeoNo ratings yet
- A000 System Z NetworkingDocument267 pagesA000 System Z NetworkingapmountNo ratings yet
- Accessing The IseriesDocument23 pagesAccessing The Iseriesvaltech20086605No ratings yet
- SDSF - Beyond The BasicsDocument69 pagesSDSF - Beyond The BasicsKota Venkata Sukumar0% (1)
- What Is A Firewall?: Network-Level FirewallsDocument3 pagesWhat Is A Firewall?: Network-Level Firewallsgaurav sharmaNo ratings yet
- 04 Z OS REXX Scripting Advanced CH01Document33 pages04 Z OS REXX Scripting Advanced CH01fasfgasNo ratings yet
- Hardening Your AIX SecurityDocument3 pagesHardening Your AIX SecuritySujeet KumarNo ratings yet
- IBM OS 390 Server User ManualDocument76 pagesIBM OS 390 Server User ManualAttilio Salutari0% (1)
- CommandsDocument10 pagesCommandsWoundedsoul Sou LNo ratings yet
- Jes MaterialDocument20 pagesJes Materialapi-3828592100% (1)
- IBM SecurityDocument718 pagesIBM SecurityHARISH BEVARANo ratings yet
- Debug Tool GUI v11 Basic Mentor Workshop-00Document221 pagesDebug Tool GUI v11 Basic Mentor Workshop-00Nagarajan VenkatesanNo ratings yet
- I-Series SecurityDocument198 pagesI-Series Securityapi-27605687No ratings yet
- GR8ZY Student Manual Ce5001studDocument168 pagesGR8ZY Student Manual Ce5001studPhung Anh TuanNo ratings yet
- My Smp/E Notes: What Is A SYSMOD?Document3 pagesMy Smp/E Notes: What Is A SYSMOD?Özgür HepsağNo ratings yet
- MQ Series For Z-OsDocument2 pagesMQ Series For Z-OskarthickmsitNo ratings yet
- Comandos RacfDocument716 pagesComandos RacfPablo SeguridadNo ratings yet
- Automation GuideDocument598 pagesAutomation GuideanonNo ratings yet
- Zos User GuideDocument452 pagesZos User GuideTasmbna NdasdNo ratings yet
- RACF V1R10 Command Language Reference - Ichva404Document514 pagesRACF V1R10 Command Language Reference - Ichva404kshameemibmNo ratings yet
- ZVM and IBMDocument26 pagesZVM and IBMaksmsaidNo ratings yet
- RACF3 Ichza3c0Document592 pagesRACF3 Ichza3c0Siranjeevi MohanarajaNo ratings yet
- TSO Commands: XMIT Node - Userid DA ('Your - PDS') OUTDA ('Your - PS')Document4 pagesTSO Commands: XMIT Node - Userid DA ('Your - PDS') OUTDA ('Your - PS')Satyabrata DashNo ratings yet
- 3032 - A Guided Tour of The DFSMSHSM Parmlib, Part 1 of 2Document74 pages3032 - A Guided Tour of The DFSMSHSM Parmlib, Part 1 of 2gborja8881331No ratings yet
- Db2 Components & Basics 1Document18 pagesDb2 Components & Basics 1Abdul GafarNo ratings yet
- How WLM WorksDocument44 pagesHow WLM WorksMaestro Ilayaraja SuperHit SongsNo ratings yet
- AIX 5L System Administration Student BookDocument815 pagesAIX 5L System Administration Student Bookic3man16No ratings yet
- QMFDocument70 pagesQMFpreetisagar_vmNo ratings yet
- SSH As400Document74 pagesSSH As400mduranscribdNo ratings yet
- Apostila zOSDocument64 pagesApostila zOSFabioFabios0% (1)
- Batch Xpediter Set Up For Program Calling Both IMS DB and DB2Document20 pagesBatch Xpediter Set Up For Program Calling Both IMS DB and DB2Anonymous hsRemjfwq5No ratings yet
- Ol 629 StudDocument436 pagesOl 629 Studapi-291717360No ratings yet
- SMPEDocument272 pagesSMPESamayNo ratings yet
- Tivoli NetViewDocument9 pagesTivoli NetViewAkash PopliNo ratings yet
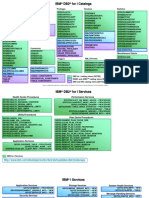
- IBM DB2 For I CatalogsDocument3 pagesIBM DB2 For I Catalogsinogomezpy5435No ratings yet
- Rac 0305Document66 pagesRac 0305Mehrdad RastegarNo ratings yet
- DB2 9 System Administration for z/OS: Certification Study Guide: Exam 737From EverandDB2 9 System Administration for z/OS: Certification Study Guide: Exam 737Rating: 3 out of 5 stars3/5 (2)
- The Linux Audit Framework-2Document39 pagesThe Linux Audit Framework-2Paulo Eduardo Dos SantosNo ratings yet
- Oracle E-Business (General)Document11 pagesOracle E-Business (General)hydersdNo ratings yet
- Wail InsDocument1 pageWail Insசிங்கார வேலன்No ratings yet
- 50 Common English Phrasal Verbs PDFDocument54 pages50 Common English Phrasal Verbs PDFPapitch Do DuneNo ratings yet
- Murrah, Austin CDocument3 pagesMurrah, Austin Cசிங்கார வேலன்No ratings yet
- UselessDocument3 pagesUselessசிங்கார வேலன்No ratings yet
- Traffic Violations TrackingDocument3 pagesTraffic Violations Trackingசிங்கார வேலன்No ratings yet
- DobDocument1 pageDobசிங்கார வேலன்No ratings yet
- Mvs Console CommandsDocument2 pagesMvs Console Commandscheers_2008No ratings yet
- LGPLagama Cuuiiyyyy Ayobuatmakalah Cemungud EaaaDocument3 pagesLGPLagama Cuuiiyyyy Ayobuatmakalah Cemungud EaaaAdinda DynaNo ratings yet
- Acute Renal Failure: o o o oDocument2 pagesAcute Renal Failure: o o o oசிங்கார வேலன்No ratings yet
- Julian Day CalendarDocument2 pagesJulian Day Calendarddante_1No ratings yet
- Suraj Banker (2514)Document1 pageSuraj Banker (2514)சிங்கார வேலன்No ratings yet
- SL No Date Location Emp ID Emp Name GenderDocument10 pagesSL No Date Location Emp ID Emp Name Genderசிங்கார வேலன்No ratings yet
- Catalogo IndoAsian Switch DisconnectorsDocument8 pagesCatalogo IndoAsian Switch DisconnectorsjackiwongzNo ratings yet
- A Real-World Look at Data Center RelocationDocument6 pagesA Real-World Look at Data Center Relocationsriramrane0% (1)
- 20 API Function Starting With Letter ADocument164 pages20 API Function Starting With Letter ARobertoLupiniNo ratings yet
- Paparan Access ControlDocument20 pagesPaparan Access ControlFrihartiniefiNo ratings yet
- SchelDocument33 pagesScheldawn.devNo ratings yet
- Vanson Bourne Research Report: Big DataDocument16 pagesVanson Bourne Research Report: Big DataVanson BourneNo ratings yet
- Easy Step by Step Configuration of Your 3027c Ssas Option ADocument6 pagesEasy Step by Step Configuration of Your 3027c Ssas Option AChoirul NizarNo ratings yet
- System AdministrationDocument15 pagesSystem AdministrationhailaaaNo ratings yet
- Cisco MDS Series Swich Zoning PDFDocument5 pagesCisco MDS Series Swich Zoning PDFSathish Vikruthamala0% (1)
- Minutes AircraftSafetySubcom 03242015Document19 pagesMinutes AircraftSafetySubcom 03242015Elmer VillegasNo ratings yet
- Stephen CardotDocument2 pagesStephen CardotphillosisNo ratings yet
- Netskope Risk Insights: Quick GlanceDocument4 pagesNetskope Risk Insights: Quick GlanceffNo ratings yet
- SD-WAN Strategies Survey ReportDocument30 pagesSD-WAN Strategies Survey ReportJeff100% (1)
- Probability of Failure On Demand - The Why and The HowDocument2 pagesProbability of Failure On Demand - The Why and The HowRubenNo ratings yet
- How To Configure VLAN and Route FailoverDocument5 pagesHow To Configure VLAN and Route FailoverwebpcnetlinkNo ratings yet
- Scope Review ChecklistDocument4 pagesScope Review ChecklistPRINCEBLRNo ratings yet
- Ferpa Authorization To Access Educational Record 20080915 ActiveDocument3 pagesFerpa Authorization To Access Educational Record 20080915 ActiveMary Anne MandarioNo ratings yet
- Computer Engineering Certificate No PWDDocument37 pagesComputer Engineering Certificate No PWDTakudzwa Gatse100% (1)
- UNIT - IV - Protection and InterlockDocument30 pagesUNIT - IV - Protection and InterlockmalaNo ratings yet
- Solution Manual For Information Technology Auditing 3rd Edition by HallDocument22 pagesSolution Manual For Information Technology Auditing 3rd Edition by HallPeter Mossien100% (32)
- Ds Ir Ats1251Document2 pagesDs Ir Ats1251Ngô Xuân HàNo ratings yet
- Material Curso Seguridad Funcional PDFDocument321 pagesMaterial Curso Seguridad Funcional PDFBrenda PárragaNo ratings yet
- Bharat Sanchar Nigam Limited: Application Form For New Mobile Connection (D-Kyc Process)Document3 pagesBharat Sanchar Nigam Limited: Application Form For New Mobile Connection (D-Kyc Process)Sales CTO LucknowNo ratings yet
- Manual Testing Session-6: WWW - PavanonlinetrainingsDocument11 pagesManual Testing Session-6: WWW - Pavanonlinetrainingssai prathyushNo ratings yet
- CTPAT - Minimum Security Criteria: Open Source Resources ListDocument7 pagesCTPAT - Minimum Security Criteria: Open Source Resources ListTuan VietNo ratings yet
- G120 Cu240beDocument942 pagesG120 Cu240beRaphael Paulino BertiNo ratings yet
- Commun Nonlinear Sci Numer Simulat: S. Behnia, M. Teshnehlab, P. AyubiDocument10 pagesCommun Nonlinear Sci Numer Simulat: S. Behnia, M. Teshnehlab, P. Ayubimilad2647No ratings yet
- Training Manual-V12-20211025 - 114024Document197 pagesTraining Manual-V12-20211025 - 114024Rabah AbbassiNo ratings yet
- DTP - NEP Application - ViewDocument3 pagesDTP - NEP Application - ViewChandan PrintoutNo ratings yet