Professional Documents
Culture Documents
Os Midterm Exam-1
Uploaded by
jenniferespanol0 ratings0% found this document useful (0 votes)
70 views3 pagesOs Midterm Exam-1
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentOs Midterm Exam-1
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
70 views3 pagesOs Midterm Exam-1
Uploaded by
jenniferespanolOs Midterm Exam-1
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 3
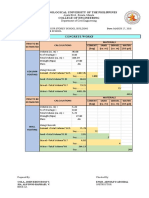
SYSTEMS PLUS COLLEGE FOUNDATION
Balibago, Angeles City
COLLEGE OF COMPUTING AND INFORMATION SCIENCES
MIDTERM EXAMINATION
1st Semester S.Y. 2014-2015
OS_L - Operating Systems
Name: _________________________________
Score: ________________________
Section: ________________________________
Date: _________________________
General Directions: Read and understand the instructions carefully. Avoid making erasures or
superimpositions on your answers. Any forms of cheating will be dealt with accordingly based on
your student manual.
Test 1 Multiple Choice. Encircle the best answer.
SCENARIO 1: Holly Holt is a systems administrator for Lucerne Publishing, a highly recognized
publishing company that specializes in barbecue cookbooks. One of the editors was having
difficulty printing several chapters of a recent cookbook and contacted Holly to find out what can
be done to get the printer to work. This editor also has informed Holly that he is continually
getting warnings when he starts his computer in the morning, indicating that his firewall has failed
to start, and he is concerned that his computer may be compromised. Holly examines his computer
and when she looks at the System Event Log, she notices a Service Control Manager error
indicating that the firewall service has failed to start. Holly opens the Services console and starts
the Windows Firewall Service without any problem.
1.What can Holly do to ensure that the Windows Firewall Service starts as expected?
a. Visit the editors office every morning and manually start the service after the machine has
booted.
b.Configure the service to have a delayed start temporarily and research why the service isnt
starting automatically.
c. Ask the editor not to plug into the network until she gets the issue resolved
2. What should Holly do first to troubleshoot the editors printing issues?
a. Verify that the Print Spooler status indicates that it is running.
b.Check to be sure the printer has paper.
c. Ask the editor to email the chapters to her so she can print a copy.
3.After some investigation, Holly notices that the editor attempted to print the same job 20
times after it failed the first time. She cannot delete the print jobs because the queue states
that it is Not Responding. What should Holly do to clear the print queue and correct the print
issues?
a. Reboot the workstation.
b. Restart the Print Spooler service from the Services console.
c. Unplug the printer, wait several minutes, and plug it back in.
SCENARIO 2: Woodgrove Bank is a small community bank with five branch offices. Their loan
officers rotate to each branch as needed. They each have laptops running Windows 7 Professional
and also have external mobile drives for data storage and backups. Due to the sensitive nature of
banking, it is of high importance to Woodgrove Bank to ensure that their customers information is
secure. Woodgrove Bank has hired Jeff Price, a security consultant, to perform a security audit and
submit his findings and recommendations to the board of directors. This information is vital
because the bank will be undergoing a security audit from their governing regulatory agency.
4. Jeffs initial recommendation is to have the laptops secured with BitLocker. What must be
done first to make this change?
a.Purchase BitLocker because Woodgrove Bank does not have licensing for it.
b.Upgrade the laptops to Windows7 Enterprise or Ultimate edition because BitLocker is not
available with Windows 7 Professional.
c. The bank doesnt have to do anything ;it is ready.
5. What recommendation can Jeff make for securing the removable storage drives?
Page 1 of 3
SYSTEMS PLUS COLLEGE FOUNDATION
Balibago, Angeles City
a. Secure the drives with Encrypting File System(EFS).
b. Secure the drives with BitLockerToGo.
c. Make sure that the drives are locked to the desks when they arrive.
6.What hardware must the laptops have to provide better security through BitLocker?
a.Security locks on the outside of the laptops, so the loan officers can secure the machine physically.
b.Trusted Platform Module (TPM)can be used in addition to BitLocker.
c.Smart card readers for authentication.
7.Where can you find the program to help you use a projector connected to your computer?
a.The All Programs Accessories folder
b.Computer Management console
c.Administrative Tools folder
d.Windows Media Player
8. Which of the following is not a security or privacy feature of Internet Explorer 9?
a.InPrivate Browsing
b.Pinned site
c.ActiveX Filtering
d.Domain highlighting
9.You want to use the Run command, however, the program requires elevated or administrative privileges. When you right-click the program to run it, which command do you select
from the shortcut menu?
a. Run elevated
b. Run protected
c. Run with permission
d. Run as administrator
10.Where do you configure security zones in Internet Explorer 9?
a.Internet Options Security tab
b.Internet Options Privacy tab
c.Safety menu
d.Tracking Protection window
11.Which of the following can you do with the Snipping Tool?
a.Annotate an image with the pen tool
b.Change the color of a captured image
c.Add typed callouts
d.Save in PDF format
12.Which of the following is an option in Windows Media Center but not in Windows Media
Player?
a.Record TV programming
b.Watch recorded TV
c.Share files over a network
d.Create playlists
13.After you compress a folder, in what color does it display in Windows Explorer?
a. Blue
b. Green
c. Black
d. Red
14.WhichofthefollowingdoyouaccesstoenterSafeModethenexttimethecomputerstarts?
a.The General tab
b.The Boot tab
c.The Startup tab
d.Services console
15.Which of the following can you do in the Programs and Features applet in Control Panel?
a.Install an application
b.Uninstall an application
c.Encrypt an applications files
Page 2 of 3
SYSTEMS PLUS COLLEGE FOUNDATION
Balibago, Angeles City
d.Compress an applications files
Test II. Identification. Identify the term being referred in the sentence.
___________________1. It is also known as the System Configuration utility, lets you enable or disable
startup services, set boot options such as booting into Safe Mode, access tools like Action Center
and Event Viewer, and more.
___________________2. What blocks ActiveX controls, which are created for interactivity on the Web and
commonly used on sites that display animations or offer multimedia such as videos?
___________________3. What helps you control which Web sites can track your online browsing activity
and receive that information?
___________________4. What is used to detect threats on Web sites, such as phishing attacks and
malware downloads, and prevents them from running?
___________________5. What is used to prevent cross-site scripting attack when you visit a
compromised Web site that runs a script that installs a key logger program on your computer?
___________________6. What allows you to write and correct free-hand math equations using your
mouse or other pointing device?
___________________7. What is the overall structure your computer uses to name, store, and organize
files and folders on a hard disk or partition?
___________________8. What is a virtual folder that can display content from different locations (folders,
for example) on your computer or an external drive?
___________________9. What is a popular snap-in that includes several tools such as Disk Management
for configuring hard disks and their partitions and Event Viewer, which allows you to view
computer event information such as program starting and stopping (including program crashes)
and security problems?
___________________10. What allows you to sync any folder in your computer with a folder on an
external drive connected to your computers or a network drive?
___________________11. What allows you to control many different computer settings, such as screen
brightness, volume, power/battery, WiFi, Bluetooth, sound, and so on?
___________________12.What opens a command window useful for IT professionals?
___________________13.What gives you access to Control Panel, Disk Cleanup, Disk Defragmenter,
Resource Monitor, System Restore, and much more ?
___________________14. What is used to prevent some Web sites use deceptive Web addresses, making
you think youre visiting a legitimate site when youre actually on a phishing site or another
dangerous site?
___________________15. What is a multi-faceted program that provides a complete entertainment
system for your computer?
___________________16. What is the process of decreasing the size of files or folders without affecting
the files content?
___________________17. What automatically prevents pop-up windows from appearing?
___________________18. What helps prevent personal information and browsing history from being
stored by Internet Explorer 9?
___________________19. What is a program that runs on top of the operating system or from a server,
and helps a user perform a specific task, such as word processing, appointment scheduling, or
accounting? An application
___________________20. What is used to protect the contents of files and folders from unauthorized
access?
TEST III ENUMERATION. ENUMERATE THE FOLLOWING
1.
2.
List the six (6) parts of Windows Media Player
List at least four (4) parts of Internet Explorer 9
Prepared by:
Reviewed by:
Approved by:
Jennifer R. Espanol
Instructor
Melissa M. Pantig
Program Chair
Grace F. Tyler Ph.D.
College Dean
Page 3 of 3
You might also like
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Nha Balut Tondo Manila - Less 1tDocument20 pagesNha Balut Tondo Manila - Less 1tTechnical Unit SjmdoNo ratings yet
- VR and Ar Pushing Connectivity LimitsDocument24 pagesVR and Ar Pushing Connectivity LimitsQuyVuNo ratings yet
- March 2012 LET Review - Sample - ItemsDocument15 pagesMarch 2012 LET Review - Sample - Itemsatong827100% (1)
- LET ReviewerDocument7 pagesLET Reviewerrotsacreijav66666No ratings yet
- Adobe PageMakerDocument3 pagesAdobe PageMakerAquarius MGNo ratings yet
- DRFM Basic PaperDocument7 pagesDRFM Basic PaperAjinkya Kale100% (1)
- ISO 9001 - 2015 Awareness Training at PuneDocument1 pageISO 9001 - 2015 Awareness Training at PunematrixmazeNo ratings yet
- 5G Transport Network Requirements, Architecture and Key TechnologiesDocument27 pages5G Transport Network Requirements, Architecture and Key TechnologiesFreedomNo ratings yet
- Review of Related AlexDocument9 pagesReview of Related AlexjenniferespanolNo ratings yet
- Vincent Lagmay - Layout ArtistDocument4 pagesVincent Lagmay - Layout ArtistjenniferespanolNo ratings yet
- SPCF Prelim Prog 3-1Document2 pagesSPCF Prelim Prog 3-1jenniferespanolNo ratings yet
- Information Management: Chapter ObjectivesDocument14 pagesInformation Management: Chapter ObjectivesjenniferespanolNo ratings yet
- 12-09-14 Fax MachineDocument2 pages12-09-14 Fax MachinejenniferespanolNo ratings yet
- SPCF It PolicyDocument7 pagesSPCF It PolicyjenniferespanolNo ratings yet
- Quotation: Balibago Angeles CityDocument2 pagesQuotation: Balibago Angeles CityjenniferespanolNo ratings yet
- General Education 2008 With AnswersDocument19 pagesGeneral Education 2008 With AnswersjenniferespanolNo ratings yet
- 3.1.2.7 Packet Tracer - Troubleshooting Serial Interfaces InstructionsDocument2 pages3.1.2.7 Packet Tracer - Troubleshooting Serial Interfaces InstructionsjenniferespanolNo ratings yet
- LET Review General Science 2009 2010Document13 pagesLET Review General Science 2009 2010jenniferespanolNo ratings yet
- Server Management-MTA SyllabusDocument8 pagesServer Management-MTA SyllabusjenniferespanolNo ratings yet
- Server Management-MTA SyllabusDocument8 pagesServer Management-MTA SyllabusjenniferespanolNo ratings yet
- 2 Concrete Works CompuDocument14 pages2 Concrete Works CompuALFONSO RAPHAEL SIANo ratings yet
- TPM KN MMHDocument12 pagesTPM KN MMHKn ShaplaNo ratings yet
- Experiment No.7: Aim: Design Differential Amplifier Software Used: AWR Design Environment 10 TheoryDocument12 pagesExperiment No.7: Aim: Design Differential Amplifier Software Used: AWR Design Environment 10 TheorySaurabh ChardeNo ratings yet
- Geoscience Data Management ReportDocument18 pagesGeoscience Data Management ReportSantiagoCuartasNo ratings yet
- Robotic Surgery: A Seminar Report OnDocument16 pagesRobotic Surgery: A Seminar Report OnWendy CannonNo ratings yet
- File 000096Document196 pagesFile 000096Wahyu PranataNo ratings yet
- Agt Lim Katrin SaskiaDocument4 pagesAgt Lim Katrin SaskiaJanine RoceroNo ratings yet
- STS Module 3Document28 pagesSTS Module 3Arlo GutayNo ratings yet
- DB 0032400 enDocument2 pagesDB 0032400 enMihai BancuNo ratings yet
- How To Grow Audience On TikTokDocument2 pagesHow To Grow Audience On TikTokIrene TayongNo ratings yet
- Mc2550 Tech GuideDocument42 pagesMc2550 Tech Guidecynneath4045No ratings yet
- CourseSyllabus Bki114-IHCI-2016 v11Document5 pagesCourseSyllabus Bki114-IHCI-2016 v11Erno LedderNo ratings yet
- ElectrecityDocument2 pagesElectrecityMarchli AhmedNo ratings yet
- Assignment1 Microsoft WordDocument9 pagesAssignment1 Microsoft Wordmamadila1056No ratings yet
- Informe Practica II Lab de MedidasDocument5 pagesInforme Practica II Lab de MedidasMaria Isabel Martinez NorenaNo ratings yet
- M340 and ATV71 Using ModbusTCPIP and Data - Exch FunctionDocument9 pagesM340 and ATV71 Using ModbusTCPIP and Data - Exch FunctionJose MarcialNo ratings yet
- CV Qazim PDFDocument1 pageCV Qazim PDFUtkarsh Anand CSENo ratings yet
- The A - Z Guide of PythonDocument11 pagesThe A - Z Guide of PythonSakshi JainNo ratings yet
- Tle 10 W 3-4Document6 pagesTle 10 W 3-4Jomar MendrosNo ratings yet
- Parallel Port InterfacingDocument34 pagesParallel Port InterfacingKingsprincessNo ratings yet
- Inotec Mixer BrochureDocument11 pagesInotec Mixer Brochureyyukin1No ratings yet
- Lecture 2 - Hello World in MLDocument49 pagesLecture 2 - Hello World in MLYi HengNo ratings yet
- Automation TestingDocument104 pagesAutomation TestingAnant ChavanNo ratings yet
- Panduan TimeTrexDocument53 pagesPanduan TimeTrexAdi Wibowo Yudo Pranoto100% (1)