Professional Documents
Culture Documents
Comp Sci - IJCSEITR - Web Server Profiling Approach
Uploaded by
TJPRC PublicationsOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Comp Sci - IJCSEITR - Web Server Profiling Approach
Uploaded by
TJPRC PublicationsCopyright:
Available Formats
International Journal of Computer Science Engineering
and Information Technology Research (IJCSEITR)
ISSN(P): 2249-6831; ISSN(E): 2249-7943
Vol. 5, Issue 4, Aug 2015, 55-62
TJPRC Pvt. Ltd.
WEB SERVER PROFILING: APPROACH TO WEBSERVER SECURITY
JYOTI PANDEY & MANOJ JAIN
Department of Computer Science, Haryana, India
ABSTRACT
The Term Web server profiling is an approach to make Websever fully secured from any web attack, whether it
can affect any of the web security components like Transmission, System as well as Access Control. This paper presents a
program-based intrusion detection system to protect Web server based on the analysis of data source and detection
technique using standard Tracing Tool, this paper represents a framework (Methodology, Approaches & Techniques) for
monitoring web server activities by using System Tap, and a GUI based Interfacing is done to monitor all three together.
KEYWORDS: Operating System (OS), TCP IP, System Tap, Profiling, Probe, LINUX, Kernel, Tracing, Script Etc
INTRODUCTION
Developing security methods for the Web is a daunting task, in part because security concerns arose after the fact.
It offers a survey of Web security issues, focusing on particular areas of concern, such as server security, mobile code, data
transfer, and user privacy.
With no insult intended to the early Web designers, security was an afterthought. At the outset, the Webs highest
goal was seamless availability. Today, with an internationally connected user network and rapidly expanding Web
functionality, reliability and security are critical. Vendors engaged in retrofitting security must contend with the web
environments peculiarities, which include location irrelevance, statelessness, code and user mobility, and stranger-tostranger communication.
Now a days Web server security is becoming a very challenging as it includes a wide variety of system including
having simple file sharing to the extended critical applications. As nucleus of the web server always must monitor its
databases script interpretaters. Securing a web server leads to keep certain factors like remove unnecessary service, remote
access, web application content, server side scripting, security patches, auditing of server, removal of un used modules.
There are some operating system which releases/support a number of tools to help administrators secure web server
installation. Sometimes scanners are also used in a process of securing a web server. Generally to manage World Wide
Web server security, on a web server, two levels of security (window security and IIS (Internet Information services)) can
be completely integrated, this model allows using authentication based user and grouping.
At OS Level, It can be created various user accounts, configured access permissions for files and directories, and
set policies.
THEORY
Web Server basically consists of three essential components System Security (Server security, Host Security),
Transmission Security (Data transportation security, Mobile code security) as well as Access control (anonymity and
www.tjprc.org
editor@tjprc.org
56
Jyoti Pandey & Manoj Jain
privacy) [19]120], with all these three components being made robust together, Web server could be treated secure [6].
Typical relations of these components are shown as in next DFdiagrams.
As shown in Figure 1, Security of system is carefully considered under these components. Before launching a
specific task experienced attackers often gather information about a target system to exploit a discovered vulnerability.
Figure 1
As shown in Figure 2, Transmission security addresses authentication, non-repudiation, integrity and
confidentiality of the data communication between transmitter and receiver. Cryptography is an important element of any
strategy to cope with those transmission security requirements.
Figure 2
Access control deals with the issue on management of system resources toward system processes and/or users
[6][20]. One of the approaches is to using cookies. Cookies were invented to keep continuity and state on the Web.
However, sensitive information cannot be securely stored and communicated in typical cookies.
From the Web Server Protection Profile we figured out the minimum-security requirements for a secured Web
server used in environments [17] [18]. Then, we have proposed a framework for secured Web server possibly by using
System Tap Tool which is helpful for us to develop software for tracing various events of web-server in order to detect any
dangerous attack on web server which helps in reducing threat of attacks on web-server in real world.
ANALYSIS [PROFILING]
Web server profiling is being done to protect it from any type of attack threaten with respect to security concern.
One of these areas, Network Security, is primarily concerned with keeping unauthorized users from gaining access to the
system. The second area, file system security, is concerned with preventing unauthorized access, either by legitimate users
Impact Factor (JCC): 7.2165
NAAS Rating: 3.63
57
Web Server Profiling: Approach to Webserver Security
or crackers, to the data stored in the system. The third area, process monitoring deals with process activities and behaviour
of process flow in kernel level and looks for effectiveness and the efficiency of processes.
The term Protection is used related to make web server fully secured, just for illustration this concept as if there is
some virus present in any system, Antivirus search, detects it and remove it from its all possible existing directories, In
same way this software module uses tracing tool System Tap to detect the attack.
Same on web server all data is mostly holded in term of information stored at various kernel level. As any
possible attack on web server is possible through either network [TCP IP], through file processing or directory or any input
route to network.
SYSTEM TAP [16]
System Tap is a tool that allows developers and system administrators to write and reuse simple scripts to
finally examine the activities of a live Linux system. Data can be extracted, filtered, and summarized quickly and safely,
to enable diagnoses of complex performance or functional problems.
System Tap scripts are driven by events during execution. There are several kinds of events: entering or exiting
a function, a timer expiring, or the entire System Tap session beginning or ending through the use of a kprobe. A kprobe
is a Linux kernel tool that is used to interrupt the kernel execution flow even when the system is running. When a probe
is reached during execution, a predefined function called a handler can be executed as if it were a quick subroutine then
resumes execution to collect debugging information. A probe handler is a series of script language statements that
specify the work to be done whenever the event occurs.
This work typically includes extracting data from the event context, storing them into internal variables, or
printing well-formatted results. A handler can be made to run before each of these events.
System Tap works by translating its script to a C-language file that is compiled into a Linux kernel module. A
Linux kernel module is a binary file containing kernel code that is not loaded into the system during boot but can be
dynamically loaded or unloaded from the system. In this case, the Linux kernel module is basically a kprobes module.
When the module is loaded, all probes that are defined in the script are activated and handlers are executed
when the instrumented events occur. When the session stops, the probes or hooks are disconnected and the module is
unloaded. This behaviour ensures that there is no functional or performance impact when System Tap is not running.
System Tap has an advantage over other debugging techniques due to its powerful scripting language and builtin safety features. Tapsets are libraries of reusable scripts installed with SystemTap that provide helper functions and
predefined variables. It can be used in the scripting language and tap sets to create instrumentation code that otherwise
require several thousands of lines of kprobes module code when written using C.
System Tap can use Debugging with Attributed Record Formats (DWARF) debugging information that
accompanies kernel images and modules, such as how the GDB debugger uses them, to provide fine granular control
over debugging. DWARF is a standard for generating information by compilers, assemblers, and linkers that can be used
for debugging purposes. Availability of debugging information conforming to the DWARF standard provides visibility
into symbols and source code statements.
www.tjprc.org
editor@tjprc.org
58
Jyoti Pandey & Manoj Jain
APPROACH BEHIND SELECTING SYSTEM TAP
There are various tracing tool easily available, but still several remarkable features holded by System Tap, like in
terms of safety issues in scripts, as other tracing tool not having much safety concern at a time of infinite loops and
recursion, language infrastructure used by system tap is very common to all C Programs, while other tracing tool not .
System Tap Technical Overview
Architecture Overview
System Tap makes kernel debugging in Linux relatively easy, but relies on technology that preceded it to do the
work. The most common and well known facility used by System Tap is Kprobes. Another facility, which is growing in
use, are kernel markers.
KPROBES
Kprobes is an application programming interface (API) that allows developers to write Linux kernel modules to
insert probes into a Linux kernel [12].
Two types of Kprobes are utilized by System Tap- Kprobe and Return Probes.
Kprobe
A Kprobe is a general purpose hook that can be inserted almost anywhere in the kernel code.
Return Probes
A Return probe, also called a kretprobe, attaches to the entry point of a function like a regular Kprobe[12].
Processing Steps
The implementation of System Tap is through the command stap. This command takes as input a file (script) that
defines to System Tap where to insert probes and what subroutines to execute when those probes are reached.
Although executing a script with System Tap is as simple as calling the stap command with the script name to run,
there are a great number of steps that System Tap go through in order to check the script for errors, convert the script to a
form that can be executed in the kernel, run the program, and generate output.
Processing means how system tap gets from a script written by a developer to a kernel module, to producing
useful output. Logical flow of system tap processing is shown in DFD, as Figure 3[12][14].
Impact Factor (JCC): 7.2165
NAAS Rating: 3.63
59
Web Server Profiling: Approach to Webserver Security
Figure 3
IMPLEMENTATION & METHODOLOGY
Complete Test setup of web server profiling consists three separate part like System Tap [for monitor events],
LINUX Architecture [Kernel and hardware] and web server, up to user segments.
This setup has been implemented using System Tap Tool and later on interfaced with java for GUI purpose.
Block diagrams shows that System Tap helps to trace events which occur at kernel level of Linux system and web-server
hosted at Linux platform and number of users accessing web-server, Test Setup has been shown in Figure 5.
Figure 5
METHODOLOGY SCHEME
Once the test-setup for Web-server Scheme is confirmed with specification implementation of scheme has been
www.tjprc.org
editor@tjprc.org
60
Jyoti Pandey & Manoj Jain
divided into two stages
SYSTEMTAP Script
Interfacing with Java for GUI
SYSTEM TAP SCRIPT
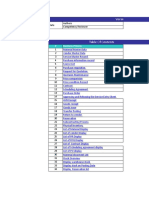
System Tap has various scripts as shown in Figure 4.
Figure 4
SCRIPT REGARDING TCP-IP CONNECTIONS
The Script monitor (TCP/IP connection) originated at system using kernel function and retrieving result by
probing function calls. Main purpose of this script is useful in identifying any unauthorized, suspicious, or otherwise
unwanted network access requests in real time.
SCRIPT REGARDING WEB-APPLICATION DIRECTORY
This script describes about I/O activity on specific device where Specific device is Web-Application Directory.
This section describes about monitoring files of specific directory if any processes are changing the control access right
attributes and processes are changing the attributes of a targeted file in real time.
SCRIPT REGARDING PROCESS MONITORING
This script describes about profiling kernel activity by monitoring function calls. Main purpose is to generate a
safe list of processes as a basis for judging the legitimacy of the process.
INTERFACING WITH JAVA FOR GUI
In order to understand the behavior of script output, it has been interfaced with java which will provide GUI for
understanding purpose in a complete way. GUI provide options for users to select options regarding displaying number of
records, defining script time, defining time for GUI refresh to display latest records on timely basis. Even user is provided
with report to view important data for particular day and also having various options for downloading report in .csv format
for later use.
PROGRAM MODULES
To make an effective completion of the project, the modules has been divided into various stages like System Tap
tool and scripts as shown in Figure 6.
Impact Factor (JCC): 7.2165
NAAS Rating: 3.63
61
Web Server Profiling: Approach to Webserver Security
Figure 6
Where scripts are the foundation for web server profiling modules, Report Generation where user allows
generating report of various modules on user requests, Report Download where users allow downloading report for later
use, and Database Handling where database used for module.
CONCLUSIONS
It presents a framework for monitoring Web Server activities possibly by using System Tap tool. A Program
based intrusion and detection system has been successfully implemented, to protect web server from any dangerous attack.
ACKNOWLEDGEMENTS
The authors sincerely thank Dr. Tapas Kumar, HOD CSE Dep.,Lingayas University Faridabad for his
encouragement to carry out work. The authors also would like to thank Utkarsh Tyagi , Abhishek Shukla for their support,
motivation and valuable discussions.
REFERENCES
1.
S. Jiang, S. Smith, and K. Minami, Securing Web Servers against Insider Attack," In the 17th Annual Computer
Security Applications Conference (ACSACOI j, pp. 265-276.
2.
Aviel D. Rubin (AT&T Labs), Daniel E. Geer Jr. Certco,"A Survey of Web Security.
3.
A.D. Rubin, D. Geer, and M.J. Ranum, Web Security Sourcebook, John Wiley & Sons, New York, 1997.
4.
Jared Karro, Jie Wang," Protecting Web Servers from Security Holes in Server-Side Includes.
5.
Sheng-Kang Lin," From Web Server Security to Web Components Security.
6.
Christian Gilmore, David Kormann, and Aviel D. Rubin, Secure Remote Access to an Internal Web Server,"
IEEE Network, Vol. 13, Issue 6, pp. 31-37, Nov.lDec., 1999.
7.
Jane Curry," Methods of monitoring processes with Zenoss Draft. www.skills-1st.co.uk
8.
J.G. Steiner, C. Neuman, and J.I. Schiller, Kerberos: "An Authentication Service for Open Network Systems,
Proc. Winter 1988 General Conf., Usenix Assoc., Berkeley, Calif., 1988, pp. 191202.
9.
M.K. Reiter and A.D. Rubin, Crowds: Anonymous and Web Transactions, ACM Trans. Information Systems
Security, Apr. 1998; see alsohttp://www.research.att.com/projects/crowds.
10. Wei Li, Long Chen, Hongjiang Ji, Tong Zhang ,Improvement of Real-Time Process Monitor Technology on
Linux Based on Mandatory Running Control Vol.4,Issue 4,pp 36-44 , July/August,2000
www.tjprc.org
editor@tjprc.org
62
Jyoti Pandey & Manoj Jain
11. .Bart Jacob,Paul Larsen, Breno Henrique Leitao and Saulo Augusto M Martins da Silva,Instrumenting the Linux
Kernel for Analyzing Performance and Functional Problems ibm.com/redbooks.
12. Miles Tracy, Wayne Jansen, Karen Scarfone, and Theodore Winograd," Guidelines on Securing Public Web
Servers, September 2007.
13. Don Domingo, Jacquelynn East and William Cohen, Red Hat Enterprise Linux5 System Tap Beginners
Guide.2011.
14. Installing and Using System Tap, IBM Corporation 2008, 2009.
15. Josh Stone, Dynamic Tracing and Performance Analysis Using System Tap Software Engineer Software and
Solutions Group August 4, 2008.
16. Web
Server
Protection
Profile
(Draft
Version:
.6j,
July
31,
2001,
http:llniap.nist.govIcc-
scheme/PP~WSPP~VO.6.Html.
17. Joon S. Park and Ravi Sandhu, Secure Cookies on the Web, in the IEEE Internet Computing, Vol. 4, lssue 4,
pp. 36-44, lul./Aug., 2000.
18. Joon S. Park, Ravi Sandhu, and Gail-Joon Ahn,Role-Based Access Control on the Web, in the ACM
Transaction on Information and System Security, Vol. 4, No. 1, pp. 37-71, Feb.,200 1.
Impact Factor (JCC): 7.2165
NAAS Rating: 3.63
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (120)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- International Baccalaureate (IB) Past Papers With Mark SchemesDocument128 pagesInternational Baccalaureate (IB) Past Papers With Mark SchemesFirasco24% (42)
- Software: CSC 101: Computer Fundamentals Presented By: Mr. Angelo P. Del RosarioDocument22 pagesSoftware: CSC 101: Computer Fundamentals Presented By: Mr. Angelo P. Del Rosariocrimpson leeNo ratings yet
- Miro TeardownDocument14 pagesMiro TeardownJaya ShankarNo ratings yet
- Getting Started Using ADAMS ControlsDocument120 pagesGetting Started Using ADAMS ControlsKajal AgrawalNo ratings yet
- 2 33 1641272961 1ijsmmrdjun20221Document16 pages2 33 1641272961 1ijsmmrdjun20221TJPRC PublicationsNo ratings yet
- Flame Retardant Textiles For Electric Arc Flash Hazards: A ReviewDocument18 pagesFlame Retardant Textiles For Electric Arc Flash Hazards: A ReviewTJPRC PublicationsNo ratings yet
- 2 29 1645708157 2ijtftjun20222Document8 pages2 29 1645708157 2ijtftjun20222TJPRC PublicationsNo ratings yet
- Baluchari As The Cultural Icon of West Bengal: Reminding The Glorious Heritage of IndiaDocument14 pagesBaluchari As The Cultural Icon of West Bengal: Reminding The Glorious Heritage of IndiaTJPRC PublicationsNo ratings yet
- Development and Assessment of Appropriate Safety Playground Apparel For School Age Children in Rivers StateDocument10 pagesDevelopment and Assessment of Appropriate Safety Playground Apparel For School Age Children in Rivers StateTJPRC PublicationsNo ratings yet
- Comparative Study of Original Paithani & Duplicate Paithani: Shubha MahajanDocument8 pagesComparative Study of Original Paithani & Duplicate Paithani: Shubha MahajanTJPRC PublicationsNo ratings yet
- Using Nanoclay To Manufacture Engineered Wood Products-A ReviewDocument14 pagesUsing Nanoclay To Manufacture Engineered Wood Products-A ReviewTJPRC PublicationsNo ratings yet
- 2 52 1649841354 2ijpslirjun20222Document12 pages2 52 1649841354 2ijpslirjun20222TJPRC PublicationsNo ratings yet
- 2 4 1644229496 Ijrrdjun20221Document10 pages2 4 1644229496 Ijrrdjun20221TJPRC PublicationsNo ratings yet
- 2 31 1648794068 1ijpptjun20221Document8 pages2 31 1648794068 1ijpptjun20221TJPRC PublicationsNo ratings yet
- 2 52 1642055366 1ijpslirjun20221Document4 pages2 52 1642055366 1ijpslirjun20221TJPRC PublicationsNo ratings yet
- Analysis of Bolted-Flange Joint Using Finite Element MethodDocument12 pagesAnalysis of Bolted-Flange Joint Using Finite Element MethodTJPRC PublicationsNo ratings yet
- The Conundrum of India-China Relationship During Modi - Xi Jinping EraDocument8 pagesThe Conundrum of India-China Relationship During Modi - Xi Jinping EraTJPRC PublicationsNo ratings yet
- 2 44 1653632649 1ijprjun20221Document20 pages2 44 1653632649 1ijprjun20221TJPRC PublicationsNo ratings yet
- Effectiveness of Reflexology On Post-Operative Outcomes Among Patients Undergoing Cardiac Surgery: A Systematic ReviewDocument14 pagesEffectiveness of Reflexology On Post-Operative Outcomes Among Patients Undergoing Cardiac Surgery: A Systematic ReviewTJPRC PublicationsNo ratings yet
- 2 51 1651909513 9ijmpsjun202209Document8 pages2 51 1651909513 9ijmpsjun202209TJPRC PublicationsNo ratings yet
- 2 51 1656420123 1ijmpsdec20221Document4 pages2 51 1656420123 1ijmpsdec20221TJPRC PublicationsNo ratings yet
- 2 51 1647598330 5ijmpsjun202205Document10 pages2 51 1647598330 5ijmpsjun202205TJPRC PublicationsNo ratings yet
- An Observational Study On-Management of Anemia in CKD Using Erythropoietin AlphaDocument10 pagesAn Observational Study On-Management of Anemia in CKD Using Erythropoietin AlphaTJPRC PublicationsNo ratings yet
- Dr. Gollavilli Sirisha, Dr. M. Rajani Cartor & Dr. V. Venkata RamaiahDocument12 pagesDr. Gollavilli Sirisha, Dr. M. Rajani Cartor & Dr. V. Venkata RamaiahTJPRC PublicationsNo ratings yet
- A Review of "Swarna Tantram"-A Textbook On Alchemy (Lohavedha)Document8 pagesA Review of "Swarna Tantram"-A Textbook On Alchemy (Lohavedha)TJPRC PublicationsNo ratings yet
- Vitamin D & Osteocalcin Levels in Children With Type 1 DM in Thi - Qar Province South of Iraq 2019Document16 pagesVitamin D & Osteocalcin Levels in Children With Type 1 DM in Thi - Qar Province South of Iraq 2019TJPRC PublicationsNo ratings yet
- Effect of Degassing Pressure Casting On Hardness, Density and Tear Strength of Silicone Rubber RTV 497 and RTV 00A With 30% Talc ReinforcementDocument8 pagesEffect of Degassing Pressure Casting On Hardness, Density and Tear Strength of Silicone Rubber RTV 497 and RTV 00A With 30% Talc ReinforcementTJPRC PublicationsNo ratings yet
- Covid-19: The Indian Healthcare Perspective: Meghna Mishra, Dr. Mamta Bansal & Mandeep NarangDocument8 pagesCovid-19: The Indian Healthcare Perspective: Meghna Mishra, Dr. Mamta Bansal & Mandeep NarangTJPRC PublicationsNo ratings yet
- Self-Medication Prevalence and Related Factors Among Baccalaureate Nursing StudentsDocument8 pagesSelf-Medication Prevalence and Related Factors Among Baccalaureate Nursing StudentsTJPRC PublicationsNo ratings yet
- 2 67 1648211383 1ijmperdapr202201Document8 pages2 67 1648211383 1ijmperdapr202201TJPRC PublicationsNo ratings yet
- 2 67 1653022679 1ijmperdjun202201Document12 pages2 67 1653022679 1ijmperdjun202201TJPRC PublicationsNo ratings yet
- Numerical Analysis of Intricate Aluminium Tube Al6061T4 Thickness Variation at Different Friction Coefficient and Internal Pressures During BendingDocument18 pagesNumerical Analysis of Intricate Aluminium Tube Al6061T4 Thickness Variation at Different Friction Coefficient and Internal Pressures During BendingTJPRC PublicationsNo ratings yet
- 2 67 1645871199 9ijmperdfeb202209Document8 pages2 67 1645871199 9ijmperdfeb202209TJPRC PublicationsNo ratings yet
- 2 67 1645017386 8ijmperdfeb202208Document6 pages2 67 1645017386 8ijmperdfeb202208TJPRC PublicationsNo ratings yet
- Diafix Troubleshooting NovoDocument242 pagesDiafix Troubleshooting NovoInfo e TecNo ratings yet
- Chapter 8 Metrics For Process and ProjectsDocument13 pagesChapter 8 Metrics For Process and ProjectsIrwandi Rizki PutraNo ratings yet
- ALC1024 v2-05 UsersGuideDocument105 pagesALC1024 v2-05 UsersGuideEinmerckNo ratings yet
- OutlineDocument11 pagesOutlineDr. M. Thillai Rani Asst Prof ECENo ratings yet
- BT Buys Counterpane To Boost IT Security Services: ... Continued From Page 1Document1 pageBT Buys Counterpane To Boost IT Security Services: ... Continued From Page 1s_sarfaraz64No ratings yet
- CV Mitta Hage Nyeste DecDocument1 pageCV Mitta Hage Nyeste Decapi-709401636No ratings yet
- HKNCII Common3 Perform Computer OperationsDocument30 pagesHKNCII Common3 Perform Computer OperationsFleet Calixto TrillanesNo ratings yet
- Take Control of Your Linux Instance and Start Building: Linux On Z: Go WorldwideDocument5 pagesTake Control of Your Linux Instance and Start Building: Linux On Z: Go WorldwideAnonymous PersonNo ratings yet
- Computer Architecture - Lab 5: Integer Multiplication, Division and Arithmetic Shift InstructionsDocument5 pagesComputer Architecture - Lab 5: Integer Multiplication, Division and Arithmetic Shift InstructionsDuy Tran MinhNo ratings yet
- Cmos 0 To 44 MHZ Single Chip 8-Bit Microntroller: DescriptionDocument20 pagesCmos 0 To 44 MHZ Single Chip 8-Bit Microntroller: DescriptionJoel Hauk HaukNo ratings yet
- Proposal Smart Lifestyle ProjectDocument7 pagesProposal Smart Lifestyle ProjectFaiz YunNo ratings yet
- TCS Placement Paper 3 PDFDocument5 pagesTCS Placement Paper 3 PDFSanrasniNo ratings yet
- CEG 2136 - Fall 2016 - MidtermDocument9 pagesCEG 2136 - Fall 2016 - MidtermAmin DhouibNo ratings yet
- Unit IDocument25 pagesUnit IRamarao BNo ratings yet
- Database Error MessagesDocument6,069 pagesDatabase Error Messagesraiizii2No ratings yet
- CPU Scheduling: CPU - I/O Burst CycleDocument4 pagesCPU Scheduling: CPU - I/O Burst Cyclearj0701No ratings yet
- S 4 P 4Document4 pagesS 4 P 4lpt0000No ratings yet
- GST - Global Smart Technologies Center: Setup and Run Codefest Server On PCDocument11 pagesGST - Global Smart Technologies Center: Setup and Run Codefest Server On PCĐại Phạm TrọngNo ratings yet
- What'sNew SWOOD2019Document16 pagesWhat'sNew SWOOD2019Muhammad Bustan100% (1)
- New Cookies MCATDocument20 pagesNew Cookies MCATARUALNo ratings yet
- 233 Sites ABIA Optimization - 20220329Document36 pages233 Sites ABIA Optimization - 20220329Senetor Brian BakariNo ratings yet
- Interaction Design BasicDocument14 pagesInteraction Design BasicKawaii GlamourNo ratings yet
- SRS Image Viewer & AnalyzerDocument16 pagesSRS Image Viewer & AnalyzerRajesh Kumar BeheraNo ratings yet
- # C4-Catalog - Equipment PDFDocument52 pages# C4-Catalog - Equipment PDFKomang Darmawan100% (1)
- Java AppletsDocument16 pagesJava AppletsSachin ShuklaNo ratings yet
- Fiori MM Test ScriptsDocument125 pagesFiori MM Test Scriptsabhi_ray22No ratings yet