Professional Documents
Culture Documents
The Ballot SRS
Uploaded by
Joseph JosefCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
The Ballot SRS
Uploaded by
Joseph JosefCopyright:
Available Formats
SOFTWARE REQUIREMENTS
SPECIFICATION FOR
E-Ballot
A semi-automated vote Casting system
VERSION 1.0
Supervisor:
Course:
Date:
Mr. Jonathan Kizito
Bachelor of Science in Computer Science
31 January 2016
Prepared by Group CS 16 035
Names
Registration No.
NAMIIRO MARTHA
13/U/11025/EVE
KABENGE JOSEPH
10/U/23283/EVE
Software Requirements Specification for E-Ballot
Page ii
Contents
1
REVISIONS ................................................................................................................................................................... III
INTRODUCTION ............................................................................................................................................................ 1
2.1
2.2
2.3
DOCUMENT PURPOSE ..................................................................................................................................................... 1
PRODUCT SCOPE ............................................................................................................................................................ 1
INTENDED AUDIENCE AND DOCUMENT OVERVIEW ........................................................................................................ 1
2.3.1
Document Overview ............................................................................................................................................. 1
2.4 DEFINITIONS, ACRONYMS AND ABBREVIATIONS ............................................................................................................ 2
2.4.1
Definitions ............................................................................................................................................................ 2
2.4.2
Acronyms and Abbreviations ............................................................................................................................... 2
2.5 DOCUMENT CONVENTIONS............................................................................................................................................. 2
2.5.1
Formatting Conventions ...................................................................................................................................... 2
2.5.2
Naming Conventions ............................................................................................................................................ 2
2.6 REFERENCES AND ACKNOWLEDGMENTS ........................................................................................................................ 3
3
OVERALL DESCRIPTION............................................................................................................................................ 4
3.1
PRODUCT PERSPECTIVE .................................................................................................................................................. 4
3.1.1
Proposed Flow of Activity .................................................................................................................................... 5
3.2 USER CHARACTERISTICS................................................................................................................................................. 6
3.3 GENERAL CONSTRAINTS................................................................................................................................................. 6
3.4 ASSUMPTIONS AND DEPENDENCIES ................................................................................................................................ 6
4
SPECIFIC REQUIREMENTS ........................................................................................................................................ 6
4.1
EXTERNAL INTERFACE REQUIREMENTS ......................................................................................................................... 6
4.1.1
Software Interface ................................................................................................................................................ 6
4.1.2
Hardware Interface: ............................................................................................................................................ 7
4.1.3
Communication Interface: ................................................................................................................................... 7
4.2 FUNCTIONAL REQUIREMENTS......................................................................................................................................... 7
4.2.1
Voters ................................................................................................................................................................... 7
4.2.2
Administrator ....................................................................................................................................................... 7
4.2.3
Candidate ............................................................................................................................................................. 8
4.3 BEHAVIOUR REQUIREMENTS .......................................................................................................................................... 8
4.3.1
Use Case View ..................................................................................................................................................... 8
5
NON-FUNCTIONAL REQUIREMENTS ..................................................................................................................... 9
5.1
PERFORMANCE REQUIREMENTS ..................................................................................................................................... 9
5.1.1
Time / space bounds ............................................................................................................................................. 9
5.1.2
Reliability ............................................................................................................................................................. 9
5.1.3
Security ................................................................................................................................................................ 9
5.2 SOFTWARE QUALITY ATTRIBUTES .................................................................................................................................. 9
5.2.1
Availability ........................................................................................................................................................... 9
5.2.2
Robustness ........................................................................................................................................................... 9
Software Requirements Specification for E-Ballot
Page iii
1 REVISIONS
Version
Primary
Author(s)
Description of Version
Date
Completed
Software Requirements Specification for THE e-BALLOT
Page 1
2 INTRODUCTION
2.1 Document Purpose
The purpose of this document is to make the functional and non-functional requirements of the eBallot Vote Casting System easy to comprehend. It also serves the purpose of making the
functionality clear to end users
2.2 Product Scope
The system produced will be an electronic vote casting system. The software will be used by citizens
to cast their vote using biometrics as the way of authentication. It will also enhance computing of
voting percentage. It will only be used for casting the ballot not any other functionality. This will leave
it independent of fraud and easy of manipulation.
The aim of this is to create an easy in the way people vote in various elections and as well reduce
amounts of money spent on ballot papers. It will be used at the time of elections. Before voting each
voter will get a unique id number that corresponds to their biometrics. to caste their valuable vote. It
will maintain a database of all the eligible voter biometric information with each biometric having a
corresponding number that only corresponds to a voter. It will also maintain a database of candidates
contesting in a particular position. With the fingerprint detail, it will have details of the voters such as
citizen name, date of birth, their constituency area, and region.
2.3 Intended Audience and Document Overview
The purpose of this document is to make the functional and non-functional requirements of the eBallot System easy to understand and as well put the intended parts of the system apart. It also serves
the purpose of making the functionality clear to end users. For academic purposes the document is for
full analysis of the supervisor to see it fit for accomplishment of the project.
2.3.1 Document Overview
The remainder of this document identifies the actors, use-cases, use-case scenarios, activity
diagrams, assumptions and dependencies needed for the analysis and design of the e-Ballot System
software package. The rest of the document contains the overall description of the system,
requirements, data model and behavioral description of the system and project planning.
Software Requirements Specification for THE e-BALLOT
Page 2
2.4 Definitions, Acronyms and Abbreviations
2.4.1 Definitions
Biometrics : Mainly referring to the finger print as the main biometric property of use in this
project
Apache Tomcat:
2.4.2 Acronyms and Abbreviations
HTML:
Hypertext Markup Language is a markup language used to design static web
pages.
CSS:
Cascade Style Sheets.
JDBC:
Java database Connector.
J2EE: Java 2 Enterprise Edition is a programming platform part of the Java Platformfor
developing and running distributed multitier architecture Java applications, based largely on
modular software components running on an application server.
SQL: DB2 Database is the database management system that delivers a flexible and cost
effective database platform to build robust on demand business applications.
HTTP: Hypertext Transfer Protocol is a transaction oriented client/server protocol between
web browser & a Web Server.
WAS: Web Application Server.
HTTPS: Secure Hypertext Transfer Protocol is a HTTP over SSL (secure socket layer).
2.5 Document Conventions
2.5.1 Formatting Conventions
In general this document will follow APA formatting requirements. The entire documents will be
justified with spacing 1.15. Headings will be aligned to the left and will be numbered according to the
heading type.
2.5.2 Naming Conventions
Naming will be done mainly using paragraphs, Chapters will be in Gill Sans Font type, 16 for Font size
and automatic heading. Sections will be in Gill San MT font type, 14 font size and normal text will be in
Gill San MT font type, 12 font size.
Software Requirements Specification for THE e-BALLOT
Page 3
2.6 References and Acknowledgments
Olaniyan O.M, Mapayi .2T, & Adejumo. 3S.A, 2011. A Proposed Multiple Scan Biometric-Based System
for Electronic Voting. Afr J. of Comp & ICTs. Vol 4, No. 2. pp 9-16
Raura. L, 2013, A Secure Electronic Voting Software Application based on Image Steganography and
Cryptography, Swinburne University of Technology
Rexha, B., Neziri, V., & Dervishi, R., 2012. Improving authentication and transparency of e-Voting
system Kosovo case. International Journal of Computers and Communications, 84-91.
Richard. S. and Patrick, D, 2007, Security analysis of remote e-voting. E-voting. Architecture. Issue
Date: Aug-2007. Proceedings of the International Conference on Computing and ICT Research.
Retrieved online from http://dspace.mak.ac.ug/handle/123456789/682
Volkamer, M 2009, Evaluation of Electronic Voting - Requirements and Evaluation Procedures to
Support Responsible Election Authorities, Springer, Google Books, viewed 27 May 2013.
D. P. Gilliam, T. L. Wolfe, J. S. Sherif, and M. Bishop, Software Security Checklist for the Software Life
Cycle, in Proc. WETICE03, 2003, pp. 243-248
HTML Forms http://www.w3schools.com/html/html_forms.asp accessed on 2 january 2016
Aneesha. B, (2001), Java Servlet Pages, Prima Tech
SRS report for ONEVS, iTeam4, 2010, www.ceng.metu.edu.tr/~e1591114/SRS
Web Application, www.experiencezen.com/wp-content/uploads/2007/04/adaptive-path-ajax-a-new%20approach-to-web-applications1.pdf, accessed on 2 January 2016
Software Requirements Specification for THE e-BALLOT
Page 4
3 OVERALL DESCRIPTION
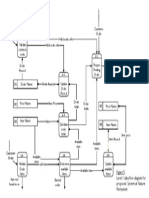
3.1 Product Perspective
The software product is a standalone system and not a part of a larger system. The system will be
made up of two parts. Before the Election Day, the system will be used for general purposes such as
setting up users and their privileges and administration, entering candidate details, profiling
candidates for the election and setting the various modules before elections. The voters will reach
the system through web pages by using web-browsers such as Mozilla, Internet Explorer and Google
Chrome or by clicking on the icon of the system software on mobiles that have finger print
recognition functionality. The system will be modular in a way that it can be used for various
election i.e. it will allow for customization.
During election, the system is connected to the thumb print database with all the voters
information. This system will be adapted to the computers at the polling stations. The voters cast
their votes using the interface that are provided at these machines. These votes are accepted by the
system on the server. The SSL will ensure secure thumb print information transfer and easy access.
SSL
Client Interface
Finger Print Module
Finger Print
DB
HTTP
HTTP
Web App Server
Voter DB
The web pages (XML/JSP) are present to provide the user interface on customer client side.
Communication between customer and server is provided through HTTP/HTTPS protocols. On the
server side web server is for java servlets and database server is for storing the information. Product
functionality
The election admin will be able to register Candidates in the system after their nomination.
Candidates can then verify this on the system there and then.
A detailed profile the candidates, will also be include
Software Requirements Specification for THE e-BALLOT
Page 5
Voters will be able to vote from anywhere in the area of voting, since there is centralised
control of the voting process. This will provide for convenience and time saving
The Election Administrators will be able to update thumb print and voters Database through a
sync function with their existing voter pool available. The sync function can be a later stage
development idea.
The system would show the statistics after voting of the votes casted and the votes obtained by
the various candidates. But to reduce controversy, the system will report after election time is
closed
The system will not provide for manual input of election result by any one user
3.1.1 Proposed Flow of Activity
Start
Voters
Thumb
ID
Candidates
Administrator
Invalid
Invalid
Log In
Details
Invalid
Log Ins
Valid
Valid
Voters
Activity
Admin
Activity
Valid
Candidates
Activity
Stop
Software Requirements Specification for THE e-BALLOT
Page 6
3.2 User characteristics
Every user should be comfortable of working with computer and net browsing.
Every user must have basic knowledge of English too.
3.3
General Constraints
The system is only in English.
This system is working from multiple servers including a web server then two database servers.
The system is tied to HTTP/HTTPS only.
Novice and handicapped are not into system knowing.
3.4 Assumptions and Dependencies
For the proper working of the system these are required.
Biometric finger print scanner either inbuilt or attached
Internet connection
A web server should have Java installed on the machine, along with Javas cryptographic
packages.
The web server runs on a http server, that is java server pages (jsp) and servlet enabled.
A web browser through which the voters access the server should have minimal support for cookies
and encrypted transactions.
4 SPECIFIC REQUIREMENTS
4.1 External Interface Requirements
4.1.1 Software Interface
Client on Internet: Web Browser, Operating System (any)
Web Server:
Data Base Server: DB2, Operating System (any)
WAS, Operating System (any)
Software Requirements Specification for THE e-BALLOT
Page 7
Development End: WSAD (J2EE, Java, Java Bean, Servlets, XML), DB2, OS (Windows), Web
Server.
4.1.2 Hardware Interface:
Client side
Server side
Ram
256 MB
Free Disk Space
100 MB
Web Application Server
256 MB
120 MB
SQL
512 MB
512 MB
Web Browser (any)
Web app
4.1.3 Communication Interface:
Client on Internet will be using HTTP/HTTPS protocol.
4.2 Functional Requirements
The system should be able do the following for the users and the voters
4.2.1 Voters
The citizens of the country who are eligible for casting vote.
Get a Biometric ID The voters should be able to access the system using their voter ID
number and be able to generate a unique biometric ID that they will use during elections.
Cast vote the system should the voters to cast their votes for their favorite candidates
on the system either online in their choice location or at a gazetted place using a finger
print as access authentication.
View their Details The voters will view their own details which they filled up at the time
of their registration using the system.
4.2.2 Administrator
Responsible for maintaining all the databases, generating results of polling and nominating candidates
for elections.
Register candidates Administrator will register the candidates who will nominate
for the position area.
Register other user and Candidates Using the system, the admin must be able to
register other officer with the same privileges and also register candidate accounts for
them to view results and polling activities.
Software Requirements Specification for THE e-BALLOT
Page 8
Voter Details Administrator must be able to connect the system with the voter
database or register voters.
4.2.3 Candidate
Register for nomination, add details to profile, modify profile and campaign for elections.
View Election results Candidates will be able to view election details also view
statistics
View own details The details filled by the candidates at the time of nomination will be
viewed by them for future references.
4.3 Behaviour Requirements
4.3.1 Use Case View
Below is a use case diagram of the whole system including the voter perspective and then the
administrator perspective?
Place Thumb
Get BioMetric ID
View Results
View Profile
Details
View Profile
Details
Voter
Candidate
Cast Vote
View Election
Reports Statistics
Add Candidate
Account
Nominate
Candidate
Add Voters Details
Add User
Administrator
Users
Log In
Software Requirements Specification for THE e-BALLOT
Page 9
5 NON-FUNCTIONAL REQUIREMENTS
5.1 Performance Requirements
5.1.1 Time / space bounds
The system is expected to have a short response time. The user, candidate and voters should be
able to get response for their requests in less than 5 seconds in relations to their connection
strength.
5.1.2 Reliability
The system in all case should avail integral information to all users
The system will in all cases update changes in vote casting in all user accounts
5.1.3 Security
All Biometric information is transmitted encrypted and then decrypted at the receiving end
The data transaction between client and server must be encrypted using SSL technology.
All the passwords that are generated or accepted must be stored in database in an
encrypted form.
In election mode, the different password should be generated for a TCK in every different
election.
To help the voters the system should allow for three tries to enter Biometric ID In which
it will be invalid pending equitation of another
5.2 Software Quality Attributes
5.2.1 Availability
At the voting time, the e- Ballot system shall be available to users on the network and to dial-in
users 99.9% of the time between 7:00am and 5:00pm local time for voting and 95% of the time
between 5:00pm and 6:00am local time for winner announcement.
5.2.2 Robustness
If the connection between the user and the system is broken prior to voting being either
confirmed or canceled, the E-Ballot System shall enable the user to recover an incomplete vote
casting process.
You might also like
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- CP R80.20.15 1500 Appliance Series AdminGuide Locally ManagedDocument281 pagesCP R80.20.15 1500 Appliance Series AdminGuide Locally ManagedJoseph JosefNo ratings yet
- Kodak I4000 Series Scanner BrochureDocument4 pagesKodak I4000 Series Scanner BrochureJoseph JosefNo ratings yet
- Resell Opportunities in Oracle Partnernetwork: Products Available For Partners To ResellDocument1 pageResell Opportunities in Oracle Partnernetwork: Products Available For Partners To ResellJoseph JosefNo ratings yet
- Arrangement of Sections: National Housing Fund ActDocument11 pagesArrangement of Sections: National Housing Fund ActJoseph JosefNo ratings yet
- E-Voting and Biometric SystemsDocument10 pagesE-Voting and Biometric SystemsrashmibuntyNo ratings yet
- Topic Document For Police AppDocument1 pageTopic Document For Police AppJoseph JosefNo ratings yet
- Internship Report SampleDocument33 pagesInternship Report SampleJoseph Josef80% (10)
- Test Marking GuideDocument3 pagesTest Marking GuideJoseph Josef100% (1)
- Pure Mathematics For Advanced Level - Bunday, MulhollandDocument538 pagesPure Mathematics For Advanced Level - Bunday, Mulhollandgauss202100% (3)
- Object Oriented ProgrammingDocument11 pagesObject Oriented ProgrammingJoseph JosefNo ratings yet
- Analysis PhaseDocument63 pagesAnalysis PhaseJoseph Josef0% (1)
- Chapter 12 - Enhanced Entity Relationship ModelingDocument16 pagesChapter 12 - Enhanced Entity Relationship ModelingJoseph JosefNo ratings yet
- Sample Level I DiagramDocument1 pageSample Level I DiagramJoseph JosefNo ratings yet
- Numerical AnalysisDocument119 pagesNumerical AnalysisJoseph JosefNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Oracle® Mobile Supply Chain Applications: User's Guide Release 11iDocument182 pagesOracle® Mobile Supply Chain Applications: User's Guide Release 11inabendusenguptaNo ratings yet
- Maximo761 Cognos11011 IntegrationInstall Guide Rev1Document60 pagesMaximo761 Cognos11011 IntegrationInstall Guide Rev1Raja PrasadNo ratings yet
- p8 WorksheetDocument95 pagesp8 WorksheetMakyfranciscoNo ratings yet
- BW Roles PDFDocument18 pagesBW Roles PDFMario CruzNo ratings yet
- SAP R - 3 Performance Monitoring and TuningDocument12 pagesSAP R - 3 Performance Monitoring and TuningBharath PriyaNo ratings yet
- MDM Installation Guide v2 2 0 3Document102 pagesMDM Installation Guide v2 2 0 3ali labbiNo ratings yet
- PowerMedia® XMS Release 3.4Document41 pagesPowerMedia® XMS Release 3.4foehn2002No ratings yet
- FileNet P8 SecurityDocument291 pagesFileNet P8 SecuritySatyabrata MahapatraNo ratings yet
- Himabindu GeraDocument6 pagesHimabindu GeraAvishek Datta GuptaNo ratings yet
- Aris Business Publisher Quick StartDocument124 pagesAris Business Publisher Quick Startjean.luc.berthou1427No ratings yet
- MDM Server Administration Guide v2 2 0 3Document360 pagesMDM Server Administration Guide v2 2 0 3Manoj SamantraNo ratings yet
- Mwa Asi1159Document28 pagesMwa Asi1159cezarbtNo ratings yet
- BSC IT 5th Sem Assignment Solved AnswerDocument45 pagesBSC IT 5th Sem Assignment Solved AnswerAmarChaudaryNo ratings yet
- Java EE Notes For ProfessionalsDocument32 pagesJava EE Notes For ProfessionalsPeter RanieriNo ratings yet
- MigrationGuide enDocument131 pagesMigrationGuide enrajNo ratings yet
- Cisco CRST Communications Manager de Mexico S de RL de CVDocument104 pagesCisco CRST Communications Manager de Mexico S de RL de CVCharly GlezNo ratings yet
- Introduction To Oracle FormsDocument24 pagesIntroduction To Oracle Formsrevanth191794No ratings yet
- WA AE Impl WIN ENUDocument323 pagesWA AE Impl WIN ENUvenkateshk1No ratings yet
- Cart PDFDocument296 pagesCart PDFkwazir70No ratings yet
- GSM Based Remote Monitoring and BillingpptDocument41 pagesGSM Based Remote Monitoring and BillingpptNabojeet Aman0% (1)
- Stack1 RHEL JBoss Runbook R17 V1 PDFDocument44 pagesStack1 RHEL JBoss Runbook R17 V1 PDFSoko MukanyaNo ratings yet
- CoreJava iNetSolvDocument191 pagesCoreJava iNetSolvavinashf0267% (9)
- Application Server Troubleshooting Guide: Oracle Utilities Application FrameworkDocument36 pagesApplication Server Troubleshooting Guide: Oracle Utilities Application FrameworkRam MokaralaNo ratings yet
- 1.technical Training - Application Architecture & DomainsDocument17 pages1.technical Training - Application Architecture & DomainsSreekar PamuNo ratings yet
- Chapter 8 Internet Information ServicesDocument24 pagesChapter 8 Internet Information ServicesAzharuddin_SyedNo ratings yet
- Ambrishkeshari Resume 161029104505Document4 pagesAmbrishkeshari Resume 161029104505Suresh JagirdarNo ratings yet
- crm89 Installfd9Document339 pagescrm89 Installfd9sukshma settyNo ratings yet
- Oracle Retail Order Broker: Installation Guide Release 16.0Document48 pagesOracle Retail Order Broker: Installation Guide Release 16.0btm1981No ratings yet
- Oracle® Fusion Middleware: Understanding Oracle Data Integrator 12c (12.2.1.2.0)Document30 pagesOracle® Fusion Middleware: Understanding Oracle Data Integrator 12c (12.2.1.2.0)Ezhil RanjithNo ratings yet
- Backupdb@CookDocument280 pagesBackupdb@CookSean ThomasNo ratings yet