Professional Documents
Culture Documents
Chapter 05 - The Bourne Shell Post
Uploaded by
Klaus BertokCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Chapter 05 - The Bourne Shell Post
Uploaded by
Klaus BertokCopyright:
Available Formats
180
5.
6.
7.
8.
9.
10.
11.
The UNIX Shells
Chapter 4
How can you make a script executable?
What is the strange term that is sometimes given to filename substitution?
Describe a common use for command substitution.
Describe the meaning of the terms parent shell, child shell, and subshell.
How do you think the kill command got its name?
Describe a way to override a standard utility.
What is a good umask value, and why?
CHAPTER
The Bourne Shell
Exercises
4.1 Write a script that prints the current date, your user name, and the name of your
login shell. [level: easy]
42 Experiment with the exec command by writing a series of three shell scripts
called a.sh, b.sh, and c.sh, each of which displays its name, executes ps, and
then execs the next script in the sequence. Observe what happens when you start
the first script by executing exec a.sh. [level: medium]
4.3 Why is the file that is created in the following session unaffected by the umask
value? [level: medium]
$
The Bourne shell, written by Stephen Bourne, was the first popular UNIX shell and is
available on all UNIX systems. It supports a fairly versatile programming language and
is a subset of the more powerful Korn shell that is described in Chapter 6. Knowledge
of the Bourne shell will therefore allow you to understand the operation of many
scripts that have already been written for UNIX, as well as preparing you for the more
advanced Kom shell.
is -i date.txt
glass
29 Aug 20 21:04 date.txt
uxuask 0077
date > date.txt
is -l date.txt
rw-rW-rW- 1 glass
29 Aug 20 21:04 date.txt
-rw-J-rW-
$
$
$
MOTIVATION
PREREQUISITES
You should have already read Chapter 4 and experimented with some of the core shell
facilities.
4.4 Write a script that creates three background processes, waits for them all to com
plete, and then displays a simple message. [level: medium]
OBJECTIVES
In this chapter, Ill explain and demonstrate the Bourne-specific facilities, including the
use of environment and local variables, the built-in programming language, and ad
vanced 110 redirection.
Project
Compare and contrast the UNIX shell features with the graphical shells available
on Windows. Which do you think is better? [level: medium]
PRESENTATION
The information is presented in the form of several sample UNIX sessions.
UTI LITI ES
The chapter introduces the following utilities, listed in alphabetical order:
expr
test
181
182
The Bourne Shell
Chapter 5
Variables
SHELL COMMANDS
The following shell commands, listed in alphabetical order, are introduced:
break
case..in..esac
continue
export
for..in..do..done
iLthen..elif..fi
read
readonly
set
trap
while..do..done
Bourne shell displays its prompt and awaits user commands. The standard Bourne shell
prompt is $, although it may be changed by setting the local variable PSi, described
later in the chapter. (Note that noninteractive Bourne shells do not read any start-up
files.)
One common use of .profile is to initialize environment variables such as
TERM, which contains the type of your terminal, and PATH, which tells the shell
where to search for executable files. Heres an example of a Bourne shell .profile
startup file:
INTRODUCTION
TERM=vtlOO
# Set terminal type.
export TERM
# Copy to environment.
# Set path and metacharacters
stty erase ? kill U intr C eof D
PATH=
: $HO/bin: ibm: /usr/sbin: /usr/bin: /usr/local/bjn
The Bourne shell supports all of the core shell facilities described in Chapter 4, plus the
following other facilities:
several ways to set and access variables
a built-in programming language that supports conditional branching, looping,
and interrupt handling
extensions to the existing redirection and command sequence operations
several new built-in commands
VARIABLES
The Boume shell can perform the following variable-related operations:
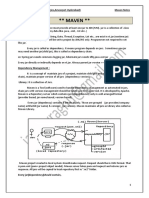
These facilities are diagram shown in Figure 5.1.
183
simple assignment and access
testing of a variable for existence
reading a variable from standard input
making a variable read only
exporting a local variable to the environment
The Bourne shell also defines several local and environment variables in addition to
those mentioned in Chapter 4.
Built-in
commands
/\
trap
set
read
Programming
Redirection
<& >&
for
case
while
Sequences
if
{. . .}
Variables
export readonly
Startup
Creating/Assigning a Variable
The Bourne shell syntax for assigning a value to a variable is
profile
FIGURE 5.1
Bourne shell functionality.
START-U P
The Bourne shell is a regular C program whose executable file is stored as Ibinlsh. If
your chosen shell is fbinlsh, an interactive Bourne shell is invoked automatically
when you log into UNIX. You may also invoke a Bourne shell manually from a script
or from a terminal by using the command sh (which has several command-line options,
described at the end of the chapter).
When an interactive Boume shell is started, it searches for a file called .profile
in the users home directory. If it finds the file, it executes all of the shell commands
that the file contains. Then, regardless of whether .profile was found, an interactive
{nainevalue}+
If a variable doesnt exist, it is implicitly created; otherwise, its previous value is over
written. A newly created variable is always local, although it may be turned into an en
vironment variable by means of a method Ill describe shortly. To assign a value that
contains spaces, surround the value by quotes. Heres an example:
$ firstName=Graham lastNaxne=Glass age=29
.assigii vars.
echo $firstName $lastName is $age
Graham Glass is 29
. .simple access.
$ narne=Graharn Glass
syntax error.
Glass: not found
$ narne=Graham Glass
.use quotes to built strings.
$ echo $name
.now it works.
Graham Glass
.
$.
184
Chapter 5
The Bourne Shell
Variables
Accessing a Variable
The Bourne shell supports the access methods shown in Figure 5.2. If a variable is ac
cessed before it is assigned a value, it returns a null string.
In the next example, I set the variable x to a default value and printed its value, all at
the same time:
$
echo x = $(x=10)
10
echo $x
Action
Syntax
$ name
$ {name}
$ {nameword}
$ {name+word}
$ {name=word}
$ {name?word}
Replaced by the value of name.
Replaced by the value of name. This form is useful if the
expression is immediately followed by an alphanumeric
character that would otherwise be interpreted as part of the
variable name.
Replaced by the value of name if set and word otherwise.
Replaced by word if name is set and nothing otherwise.
Assigns word to the variable name if name is not already set
and then is replaced by the value of name.
Replaced by name if name is set. If name is not set, word is
displayed to the standard error channel and the shell is
exited. If word is omitted, then a standard error message is
displayed instead.
FIGURE 5.2
.assigrl a default value.
..
.confirm the variable was set.
10
In the following example, I displayed messages on the basis of whether certain vari
ables were set:
$ flag=1
.assign a variable.
.conditional message #1.
echo $(flag+flag is set)
flag is set
$ echo $(flag2.i-flag2 is set)
.conditional message #2.
result is null
$
In the next example, I tried to access an undefined variable called grandTotal and re
ceived an error message instead:
$
$
$
total =10
value=$(total?total not set)
echo $value
assign a variable.
accessed OK.
look at its value.
10
Bourne shell special variables.
value=$(grandTotal?grand total not set)
grandTotal: grand total not set
I personally find these techniques for accessing variables to be hack methods of deal
ing with certain conditions, so I hardly ever use them. However, its good to be able to
understand code that uses them. The following examples illustrate each access method.
In the first example, I used braces to append a string to the value of a variable:
$
$
verb=sing
echo I like $verbing
I like
$ echo I like $(verb)ing
I like singing
185
.assign a variable.
.theres no variable verbing.
.now it works.
..
.not set.
$
In the final example, I ran a script that used the same access method as the previous ex
ample. Note that the script terminated when the access error occurred:
$ cat script.sh
.look at the script.
value=${grandTotal?grand total is not set)
echo done
# this line is never executed.
$ script.sh
.run the script.
script.sh: grandTotal: grand total is not set
..
Reading a Variable from Standard Input
Heres an example that uses command substitution to set the variable startDate to the
current date if its not already set to that:
$
$
startDate=$(startDate- date)
echo $startDate
Tue Wed 4 06:56:51 CST 1998
$_
.if not set, run date.
look at its value.
The read command allows you to read variables from standard input. It works as
shown in Figure 5.3. If you specify just one variable, the entire line is stored in the vari
able. Heres a sample script that prompts a user for his or her full name:
$ cat script.sh
list the script.
echo Please enter your name: \c
read name
# read just one variable.
186
ChapterS
TheBourneShell
# display the variable.
echo your name is $name
.run the script.
$ script.sh
Please enter your name: Graham Walker Glass
.whole line was read.
your name is Graham Walker Glass
.
$
Shell Command: read {variable} +
read reads one line from standard input and then assigns successive words from the
line to the specified variables. Any words that are left over are assigned to the last
named variable.
FIGURE 5.3
Description of the read shell command.
Heres an example that illustrates what happens when you specify more than one
variable:
.list the script.
$ cat script.sh
echo Please enter your name: \c
# read two variables.
read firstName lastName
echo your first name is $firstName
echo your last name is $lastName
.run the script.
$ script.sh
Please enter your name: Graham Walker Glass
first word.
your first name is Graham
.the rest.
your last name is Walker Glass
.run it again.
$ script.sh
Please enter your name: Graham
first word.
your first name is Graham
only one.
your last name is
.
Variables
187
to name environment variables. The env utility, described in Figure 5.5, allows you to
modify and list such variables. In the following example, I created a local variable called
DATABASE, which I then marked for export. When I created a subshell, a copy of the
environment variable was inherited:
$ export
.list my current exports.
export TERN
set in my .profile startup file.
$ DATABASE=/dbase/db
.create a local variable.
$ export DATABASE
.mark it for export.
$ export
.note that its been added.
export DATABASE
export TERN
$ env
list the environment.
DATABASE/dbase/dJD
HOME= /home/glass
LOGNAME=glass
PATH=: /usr/ucb: ibm: /usr/bin
SHELL=/bin/sh
TERN=vtloo
USER=glass
$ sh
.create a subshell.
$ echo $DATABASE
a copy was inherited.
/dbase/db
$ D
.terminate subshell.
.
Utility: env {variable
value}* [command]
env assigns values to specified environment variables and then executes an optional
command using the new environment. If no variables or command is specified, a list
of the current environment is displayed.
Exporting Variables
The export command allows you to mark local variables for export to the environment. It
works as shown in Figure 5.4. Although its not necessary, I tend to use uppercase letters
Shell Command: export {variable} +
export marks the specified variables for export to the environment. If no variables
are specified, a list of all the variables marked for export during the shell session is
displayed.
FIGURE 5.4
Description of the export shell command.
FIGURE 5.5
Description of the env command.
Read-only Variables
The readonly command allows you to protect variables against modification. It works
as shown in Figure 5.6. In the following example, I protected a local variable from mod
ification, exported the variable, and then showed that its copy did not inherit the readonly status:
$
$
password=Shazajv
echo $password
Shazam
$ readonly password
$ readonly
assign a local variable.
.display its value.
.protect it.
.list all readonly variables.
188
Chapter 5
The Bourne Shell
readonly password
$ password=Phoombah
password: is read only
$ export password
$ password=Phoornbah
password: is read only
$ sh
$ readonly
$ echo $password
Shazam
$ password=Alacazar
$ echo $password
Alacazar
$ D
$ echo $password
Shazam
Variables
Name
.try to modify it.
.export the variable.
.try to modify it.
.create a subshell.
the eorted password is not readonly.
. its value was copied correctly.
.but its value may be changed.
echo its value.
.terminate the subshell.
original value.
. .echo
189
Value
$@
an individually quoted list of all the positional parameters
$#
the number of positional parameters
$?
the exit value of the last command
$!
the process ID of the last background command
$-
the current shell options assigned from the command line or by the
built-in set command (see later)
$$
the process ID of the shell in use
FIGURE 5.7
Bourne predefined local variables.
The next example illustrates how $! may be used to kill the last background process:
Shell Command: readonly {variable} *
$
readonly makes the specified variables read only, protecting them against future
modification. If no variables are specified, a list of the current read-only variables is
displayed. Copies of exported variables do not inherit their read-only status.
sleep 1000 &
.create a background process.
.process ID of background process.
.kill it!
29455
kill $!
29455 Terminated
$ echo $!
29455
FIGURE 5.6
the process ID is still remembered.
Description of the readonly shell command.
Predefined Environment Variables
In addition to the core predefined environment variables (listed in Chapter 2), the
Bourne shell defines the enviromnent variables shown in Figure 5.8. Heres a small ex
ample that illustrates the first three predefined environment variables. I set my prompt
to something different by assigning a new value to PSi and changed the delimiter char
acter to a colon, saving the previous value in a local variable. Finally, I set PS2 to a new
value and illustrated a situation in which the secondary prompt is displayed.
Predefined Local Variables
In addition to the core predefined local variables, the Bourne shell defines the local
variables shown in Figure 5.7. Heres a small shell script that illustrates the first three
variables. In this example, the C compiler (cc) was invoked on a file that didnt exist,
and therefore the system returned a failure exit code.
. .list the script.
$ cat script.sh
echo there are $# conmand line arguments: $@
# compile the first argument.
cc $1
# display exit code.
echo the last exit value was $?
nofile
tmpfile
. . .execute the script.
$ script.sh
there are 2 command line arguments: nofile trnpfile
cc: Warning: File with unknown suffix (nofile) passed to ld
ld: nofile: No such file or directory
. . cc errored.
the last exit value was 4
.
$ PSI=sh?
sh? oldIFS=$IFS
sh? IFS=:
sh? ls:*.c
badguy.c
number.c
fact2.c
number2.c
sh? IFS=$oldIFS
sh? string=a long\
>
string
sh? echo $scring
a long string
. . set
a new primary prompt.
.remember the old value of IFS.
.change the word delimiter to a colon.
. this executes OK!
open.c
trunc.c
writer.c
reader.c
who.c
.restore the old value of IFS.
assign a string over 2 lines
>
is the secondary prompt.
look at the value of string.
.
190
The Bourne Shell
Chapter 5
Arithmetic
sh? PS2=???
sh? stringa long\
??? string
sh? echo $string
a long string
sh?
.change the secondary prompt.
.assign a long string.
is new secondary prompt.
. ???
.look at the value of string.
echo
expr index donkey
echo
expr match smailtalk
.*lk...attempt a match.
echo
expr match transputer
echo
expr transputer
echo
expr \ ( 4
echo
expr \
ke
. .
191
locate a substring.
1k
.attempt match.
*.2k
...attempt a match.
Value
Name
When the shell tokens a command line prior to its execution, it uses the
characters in this variable as delimiters. IFS usually contains a space, a
tab, and a newline character.
$IFS
\> 5 \)
.is 4
>
5 ?
$PS1
This variable contains the value of the command-line prompt, $ by
default. To change the prompt, simply set PSi to a new value.
$PS2
This variable contains the value of the secondary command-line prompt
( > by default) that is displayed when more input is required by the
shell. To change the prompt, set PS2 to a new value.
$SHENV
If this variable is not set, the shell searches the users home directory
for the .profile start-up file when a new shell is created. If the
variable is set, then the shell searches the directory specified by
SHENV.
\> 5
\)
\/ \ (
\< 7
\)
..
.4>5 or 6<7?
$
j
Utility: expr expression
expr evaluates expression and sends the result to standard output. All of the compo
nents of expression must be separated by blanks, and all of the shell metacharacters
must be escaped by a \. expression may yield a numeric or string result, depending on
the operators that it contains. The result of expression may be assigned to a shell
variable by the appropriate use of command substitution.
expression may be constructed by applying the following binary operators to
integer operands, grouped in decreasing order of precedence:
FIGURE 5.8
OPERATOR
Bourne shell predefined environment variables.
/%
ARITHMETIC
Although the Bourne shell itself doesnt support arithmetic directly, the expr utility
does and is used as described in Figure 5.9. The following example illustrates some of
the functions of expr and makes plentiful use of command substitution:
$ x=l
$
$
. .
x=expr $x
echo $x
initial value of x.
increment x.
$
$
xexpr 2 3
echo $x
\ 5
before
+.
17
echo
expr \
echo
expr length
3 \)
..
.regroup.
> > = < <=
echo
key
expr substr donkey
4 3
extract a substring.
comparison operators
&
logical and
logical or
Parentheses may be used to explicitly control the order of evaluation. (They also
must be escaped.) expr supports the following string operators as well:
OPERATOR
MEANING
string regularExpression
match string regularExpression
Both forms return the length of string if
both sides match, and each returns zero
otherwise.
find length of cat.
cat
multiplication, division, remainder
addition, subtraction
25
MEANING
FIGURE 5.9
Description of the expr command.
192
The Bourne Shell
Chapter 5
Conditional Expressions
Form
substr string start length
index string charList
length string
Returns the substring of string, starting
from index start and consisting of length
characters.
-b filename
True if filename exists as a block special file.
-cfilename
True if filename exists as a character special file.
Returns the index of the first character
in string that appears in charList.
-dfilename
True if filename exists as a directory.
-f filename
True if filename exists as a nondirectory.
Returns the length of string.
-gfilename
True if filename exists as a set group ID file.
-h filename
True if filename exists as a symbolic link.
-k filename
True if filename exists and has its sticky bit set.
-1 string
The length of string.
The format of regularExpression is defined in the appendix
FIGURE 5.9
(Continued)
n string
CONDITIONAL EXPRESSIONS
The control structures described in the next section often branch, depending on the
value of a logical expressionthat is, an expression that evaluates to true or false. The
test utility supports a substantial set of UNIX-oriented expressions that are suitable
for most occasions. It works as shown in Figure 5.10. A test expression may take the
forms shown in Figure 5.11 test is very picky about the syntax of expressions; the
spaces shown in this table are not optional. For examples of test, see the next section,
which uses them in a natural context.
(equivalent form on some UNIX systems)
test returns a zero exit code if expression evaluates to true; otherwise, it returns a
nonzero exit status. The exit status is typically used by shell control structures for
branching purposes.
Some Bourne shells support test as a built-in command, in which case they
support the second form of evaluation as well. The brackets of the second form must
be surrounded by spaces in order to work.
(See the text for a description of the syntax of expression.)
FIGURE 5.10
True
if string
contains at least one character
-p filename
True if filename exists as a named pipe.
-rfilename
True if filename exists as a readable file.
-s filename
True if filename contains at least one character.
-t fd
True if file descriptor fd is associated with a terminal.
-ufilename
True if filename exists as a set user ID file.
-w filename
True if filename exists as a writable file.
-x filename
True if filename exists as an executable file.
-z string
True if string contains no characters.
strl
True if stri is equal to str2.
stri!
Utility: test expression
[expression]
Meaning
str2
str2
True if stri is not equal to str2.
string
True if string is not null.
intl -eq int2
True if integer intl is equal to integer int2.
intl -ne int2
True if integer intl is not equal to integer int2
intl -gt int2
True if integer intl is greater than integer int2.
intl -ge int2
True if integer intl is greater than or equal to integer int2.
intl -lt int2
True if integer intl is less than integer int2.
intl -le int2
True if integer intl is less than or equal to integer int2.
! expr
True if expr is false.
exprl -a expr2
True if exprl and expr2 are both true.
exprl -o expr2
True if exprl_or_expr2_are true.
\( expr \)
Escaped parentheses are used for grouping expressions.
Description of the test command.
FIGURE 5.11
test command expressions.
193
194
Chapter 5
The Bourne Shell
Control Structures
195
CONTROL STRUCTURES
The Bourne shell supports a wide range of control structures that make the shell
suitable as a high-level programming tool. Shell programs are usually stored in
scripts and are commonly used to automate maintenance and installation tasks. The
next few subsections describe the control structures in alphabetical order; they as
sume that you are already familiar with at least one high-level programming
language.
case
..
in
..
esac
The case command supports multiway branching based on the value of a single string,
It has the syntax described in Figure 5.12. Heres an example of a script called
menu.sh that makes use of a case control structure (this script is also available on
line; see the preface for information):
#1 /bin/sh
echo menu test program
stopO
* reset loop termination flag.
while test $stop -eq 0
# loop until done.
do
cat << ENDOFMENtJ
# display menu.
1
: print the date.
2, 3: print the current working directory.
: exit
4
echo
echo your choice? \c
read reply
echo
case $reply in
1)
date
2 3)
pwd
4,)
stop=l
echo illegal choice
esac
done
# prompt.
* read response.
* process response.
# display date.
# display working directory.
# set loop termination flag.
# default.
# error.
case expression in
pattern {Jpattern}*)
list
esac
expression is an expression that evaluates to a string, pattern may include wildcards, and list is a list of one or more shell commands. You may include as many
patternlist associations as you wish. The shell evaluates expression and then com
pares it with each pattern in turn, from top to bottom. When the first matching pat
tern is found, its associated list of commands is executed, and then the shell skips
to the matching esac. A series of patterns separated by or symbols
( ) is all as
sociated with the same list. If no match is found, then the shell skips to the match
ing esac.
FIGURE 5.12
Description of the case shell command.
Heres the output from the menu.sh script:
$ menu.sh
menu test program
1
: print the date.
2, 3: print the current working
4
:exit
your choice? 1
Thu Feb 5 07:09:13 CST 1998
1
: print the date.
2, 3: print the current working
4
: exit
your choice? 2
/home/glass
1
: print the date.
2, 3: print the current working
4
:exit
your choice? 5
illegal choice
1
: print the date.
2, 3: print the current working
4
: exit
your choice? 4
directory.
directory.
directory.
directory.
196
Chapter 5
for
do
Control Structures
The Bourne Shell
then
echo negative
elif [ $nurnber -eq 0 J
then
echo zero
else
echo positive
fi
$ if.sh
enter a number: 1
positive
$ if.sh
enter a number: -1
negative
done
The for command allows a list of commands to be executed several times, using a dif
ferent value of the loop variable during each iteration. Its syntax is shown in Figure 5.13.
Heres an example of a script that uses a for control structure:
$ cat for.sh
for color in red yellow green blue
do
echo one color is $color
done
$ for.sh
one color is red
one color is yellow
one color is green
one color is blue
..
.list the script.
.execute the script.
197
.run the script.
run the script again.
if listi
then
list2
for name [in {word}*]
do
elif list3
then
list
else
list5
The for command loops the value of the variable name through each word in the
word list, evaluating the commands in list after each iteration. If no word list is sup
plied, $@ ($1..) is used instead. A break command causes the loop to end immedi
ately, and a continue command causes the loop to jump immediately to the next
iteration.
optional, else part may occur zero or one times.
The commands in listi are executed. If the last command in listl succeeds, the
commands in list2 are executed. If the last command in listi fails and there are
one or more elif components, then a successful command list following an elif
causes the commands following the associated then to be executed. If no success
ful lists are found and there is an else component, the commands following the else
are executed.
Description of the for shell command.
then
..
optional, elif part may be repeated several times.
fi
FIGURE 5.13
..
list4
done
if
..
FIGURE 5.14
fi
Description of the if shell command.
The if command supports nested conditional branches. It has the syntax shown in
Figure 5.14. Heres an example of a script that uses an if control structure:
$ cat if.sh
echo enter a number: \c
read number
if [ $number lt 0 1
.list the script.
trap
The trap command allows you to specify a command that should be executed when the
shell receives a signal of a particular value. Its syntax is shown in Figure 5.15. Heres an
198
Chapter 5
The Bourne Shell
Control Structures
example of a script that uses the trap control structure:
$
cat trap.sh
trap echo Control-C; exit 1 2
#
while 1
do
echo infinite loop
sleep 2
#
done
$ trap.sh
infinite loop
infinite loop
-C
.1 typed a
Control-C
displayed
xexpr $x
done
$ until.sh
x= 1
x=2
x= 3
list the script.
trap Ctl-C (signal #2)
.
.execute the script.
until listi
do
list2
done
Control-C here.
by the echo cormand.
The until command executes the commands in listi and ends if the last command in
listi succeeds; otherwise, the commands in list2 are executed and the process is re
peated. If list2 is empty, the do keyword should be omitted. A break command caus
es the loop to end immediately, and a continue command causes the ioop to jump
immediately to the next iteration.
The trap command instructs the shell to execute command whenever any of the
numbered signals signal is received. If several signals are received, they are trapped
in numeric order. If a signal value of 0 is specified, then command is executed when
the shell terminates. If command is omitted, then the traps of the numbered signals
are reset to their original values. If command is an empty string, then the numbered
signals are ignored. If trap is executed with no arguments, a list of all the signals and
their trap settings are displayed. (For more information on signals and their default
actions, see Chapter 13.)
FIGURE 5.16
Description of the until shell command.
while
FIGURE 5.15
Description of the trap shell command.
Note that when Control-C was typed, the shell executed the echo command followed
by the exit command.
done
The while command executes one series of commands as long as another series of com
mands succeeds. Its syntax is shown in Figure 5.17. Heres an example of a script that
uses a while control structure to generate a small multiplication table:
$
if
done
The until command executes one series of commands as long as another series of com
mands fails. It has the syntax shown in Figure 5.16. Heres an example of a script that
uses an until control structure:
$ cat until.sh
x=l
until [ $x gt 3
do
echo x = $x
.execute the script.
sleep for two seconds.
Shell command: trap. [[command] {signal}
do
until
199
cat multi.sh
[ $1 eq
] ; then
echo Usage: multi number
exit
fi
x=l
while
do
.list the script.
# set outer loop value
# outer loop
$x le $1
.list the script.
# set inner loop value
while [ $y le $1
do
echo expr $x \* $y
y=expr $y + 1
* generate one table entry
\c
# update inner loop count
200
Chapter 5
The Bourne Shell
done
echo
x=expr $x + l
done
$ multi.sh 7
1
2
3
2
4
6
3
6
9
4
8
12
5
10
15
12
6
18
14
7
21
Sample Project: track
# blank line
# update outer loop count
.
4
8
12
16
20
24
28
5
10
15
20
25
30
35
6
12
18
24
30
36
42
.execute the script.
7
14
21
28
35
42
49
201
date, which displays the current time
rm, which removes a file
my, which moves a file
sleep, which pauses for a specified number of seconds
grep, duff, sort, and sed are described in Chapter 3; who is described in Chapter 9. The
usage of track is as shown in Figure 5.18. Heres an example of track at work:
.track ivors sessions.
$ track -n3 ivor -t200
track report for ivor:
initial output.
login
ivor
ttyp3
Feb 5 06:53
track report for ivor:
.ivor logged out.
logout
ivor
Feb 5 06:55
ttyp3
C
terminate program using Control-C.
stop tracking
termination message.
while listi
do
list2
done
The while command executes the commands in listi and ends if the last command in
listi fails; otherwise, the commands in list2 are executed and the process is repeated.
If list2 is empty, the do keyword should be omitted. A break command causes the
loop to end immediately, and a continue command causes the ioop to jump immedi
ately to the next iteration.
FIGURE 5.17
Description of the while shell command.
Script: track [-ncount] [-tpause] userld
track monitors the specified users login and logout sessions. Every pause number of
seconds, track scans the system and makes a note of who is currently logged in. If the
specified user has logged in or logged out since the last scan, this information is dis
played to standard output. track operates until count scans have been completed. By
default, pause is 20 seconds and count is 10,000 scans. track is usually executed in the
background, with its standard output redirected.
FIGURE 5.18
Description of the track shell script.
The implementation of track consists of three files:
SAMPLE PROJECT: track
To illustrate a good percentage of the capabilities of the Bourne shell, Ill present a
small project that I call track. This script tracks a users log-ins and log-outs, generat
ing a simple report of the users sessions. The script utilizes the following utilities:
who, which displays a listing of the current users of the system
grep, which filters text for lines that match a specified pattern
duff, which displays the differences between two files
sort, which sorts a text file
sed, which performs preprogrammed edits on a file
expr, which evaluates an expression
cat, which lists a file
track, the main Bourne shell script
track.sed, a sed script for editing the output of the duff utility
track.cleanup, a small script that cleans up temporary files at the end
The operation of track may be divided into three pieces:
It parses the command line and sets the values of three local variables: user,
pause, and loopCount. If any errors occur, a usage message is displayed and the
script terminates.
It then sets two traps: one to trap the scripts termination and the other to trap
an INT (Control-C) or a QUIT (Control-\) signal. The latter trap invokes the
former trap by executing an explicit exit, so the cleanup script always gets called,
202
Chapter 5
The Bourne Shell
Miscellaneous Built-Ins
regardless of how the script terminates. The cleanup script takes the process ID
of the main script as its single argument and removes the temporary files that
track uses for its operation.
The script then loops the specified number of times, storing a filtered list of the
current users in a temporary file called .track.new.$$, where $$ is the process
ID of the script itself. This file is then compared against the last version of the
same output, stored in .track.old.$$. If a line is in the new file, but not in the
oldone, the user must have logged in; if a line is in the old file, but not in the
newone, the user must have logged out. If the output file from duff is of nonzero
length, it is massaged into a suitable form by sed and displayed. The script then
pauses for the specified number of seconds and continues to loop.
The output from two diffed who outputs is illustrated by the following session:
.the
$ cat track.new.1112
glass
ttypO
Feb
glass
ttyp2
Feb
.the
$ cat track.old.1112
glass
ttypo
Feb
glass
ttypl
Feb
$ diff track.new.1112 track.old.1112
2c2
< glass
ttyp2
Feb
.
..
>
glass
ttypl
Feb
new output from who.
4 23:04
4 23:04
old output from who.
4 23:04
4 23:06
the changes.
4 23:04
4 23:06
The sed script track.sed removes all lines that start with a digit or
and then sub
stitutes <for a login and >for a logout. Here is a listing of the three source files
(which are also available on-line; see the preface for more information):
---
track.sed
/[09] ./d
case $arg in
_t*)
# time
pause=expr substr $arg 3 10
203
# extract number
_n*)
# scan count
loopCount=expr substr $arg 3 10 # extract number
user=$arg
esac
done
if [ I
$user I
then
error=1
fi
if [ $error -eq 1 j
then
cat << ENDOFEP.OR
usage: track [-n#] [-t#l
user name
# check a user ID was found
# display error if error(s)
found
# display usage message
userld
ENDOFERROR
exit 1
# terminate shell
fi
trap track.cleanup $$; exit $exitCode 0 # trap on exit
trap exitCode=l; exit 2 3
# trap on INT/QUIT
> .track.old.$$
# zero the old track file.
count=0
# number of scans so far
while [ $count -lt $loopCount I
do
who
grep $user
sort > .track.new.$$
# scan system
diff .track.new.$$ .track.old.$$ I
sed -f track.sed > track.report. $$
if [ -s .track.report.$$ ]
* only report changes
then
# display report
echo track report for ${user}:
cat track.report. $$
fi
my .track.new.$$ .track.old.$$ * remember current state
sleep $pause
# wait a while
countexpr $count + 1
# update scan count
done
exitCode=0
# set exit code
s/</login/
s/>/logout/
track.cleanup
echo stop tracking
rm -f .track.old.$l .track.new.$1 .track.report.$1
track
pause=20
loopCount10000
error=0
for arg in $
do
MISCELLANEOUS BUILT-INS
#
#
#
#
default pause between scans
default scan count
error flag
parse command line arguments
The Bourne shell supports several specialized built-in commands. I have already de
scribed several of them, such as those related to control structures and job control, in
other sections of the chapter. This section contains an alphabetical list of the rest, to
gether with a brief description.
204
Chapter 5
The Bourne Shell
Miscellaneous Built-Ins
Read Command:
To execute the contents of a text file from within a shells environment (i.e., not by
starting a subshell, as you do when executing a shell script), use a period followed by
the name of the file. The file does not have to have execute permission. This command
is handy if you make modifications to your .profile file and wish to reexecute it. The
following command sequence illustrative:
$ cat .profile
TEFM=vtiO 0
export TERM
.profile
$
.
set
# turn off
echo goodbye $USER
echo $notset
set -u
# unset variables
echo $notset
# generate
$ script.sh b.c
is $1
+ is a.c
a.c
set
+ set
goodbye glass
script.sh: notset: parameter
.assume .profile
was just edited.
.re-execute it.
4.
205
trace.
will generate an error now.
an error.
.execute the script.
output by -v option.
.output by -x option.
.reguiar output.
output by -v option.
.output by -x option.
.regular output.
not set
.access unset variable.
.
Note that, since a subshell is not created to execute the contents of the file, any local
variables that the file sets are those of the current shell.
Shell Command: set -ekntuvx {arg} *
null Command
The null command is usually used in conjunction with the control structures listed ear
lier in the chapter and performs no operation, as shown in Figure 5.19. It is often used
in case structures to denote an empty set of statements associated with a particular
switch.
set allows you to choose the shell options that are displayed in Figure 5.21. Any re
maining arguments are assigned to the positional parameters $1, $2, and so forth,
overwriting their current values.
RGURE 5.20
Description of the set shell command.
Shell Command: null
The null command performs no operation.
Option
FIGURE 5.19
Description of the null shell command.
Setting Shell Options: set
The set command allows you to control several shell options. Its syntax is shown in
Figure 5.20. Figure 5.21 shows a list of the set options. The next example shows a brief
script that makes use of these options. The -x and -v options are useful in debugging
a shell script, as they cause the shell to display lines both before and after the vari
able, wildcard, and command substitution metacharacters are processed. I recom
mend that you always use these options when testing scripts. Here is the relevant
code:
$ cat script.sh
set vx a.c
is $1
look at the script
# set debug trace and overwrite $1.
# access first positional parameter.
Meaning
If the shell is not executing commands from a terminal or a start-up
file, and a command fails, then execute an ERR trap and exit.
Accept but do not execute commands. This flag does not affect interac
tive shells.
Execute the next command and then exit.
Generate an error when an unset variable is encountered.
Echo shell commands as they are read.
Echo shell commands as they are executed.
Turns off the x and v flags and treat further characters as arguments.
HGURE 5.21
set shell command options.
206
Chapter 5
The Bourne Shell
In addition to possessing the new facilities that have already been described, the
Bourne shell enhances the following areas of the common core:
When a grotip of commands is placed between parentheses, the commands are execut
ed by a subshell. The Bourne shell also lets you group commands by placing them be
tween braces, in which case they are still redirectable and pipeable as a group, but are
executed directly by the parent shell. A space must be left after the opening brace, and
a semicolon must precede the closing brace.
In the following example, the first cd command didnt affect the current working
directory of my login shell, since it executed inside a subshell, but the second cd com
mand did:
redirection
sequenced commands
Redirection
Besides employing the common core redirection facilities, the Bourne shell allows you
to duplicate, close, and redirect arbitrary I/O channels. You may associate the standard
input file descriptor (0) with file descriptor n by using the following syntax:
corrariand
<&
$ pwd
/home/glass
$ (cd /; pwd; is
.associate standard input.
Similarly, you may associate the standard output file descriptor (1) with file descriptor
n by using the following syntax:
$ command
>&
...
associate standard output.
To close the standard input and standard output channels, use this syntax:
command
<&>&-
pwd
.count files with subshell.
.my shell didnt move.
wc -1; }
.count files with shell.
.my shell moved.
COMMAND LINE OPTIONS
The Bourne shell supports the command-line options shown in Figure 5.22.
Option
Meaning
-c string
Create a shell to execute the command string.
-s
Create a shell that reads commands from standard input and sends
shell messages to the standard error channel.
-i
Create an interactive shell; like the -s option, except that the
SIGTERM, SIGINT, and SIGQUIT signals are all ignored. (For
information about signals, consult Chapter 13.)
FIGURE 5.22
Bourne shell command-line options.
wc -i)
.send standard output to ls.txt.
$ man is > is.txt
from standard error.
Reformatting page. Wait... done
..send error to err.txt.
$ man is > is.txt 2> err.txt
.look at the file.
$ cat err.txt
Wait... done
Reformatting page.
.associate stderr with stdout.
$ man is > ls.txt 2>&i
.look at first line of ls.txt.
$ head -i is.txt
Reformatting page.
.
display current working directory.
close stdin and execute command.
close stdout and execute command.
You may precede any redirection metacharacters, including the Bourne-specific ones
just described, by a digit to indicate the file descriptor that should be used instead of 0
(for input redirection) or 1 (for output redirection). Its fairly common to redirect file
descriptor 2, which corresponds to the standard error channel.
The next example illustrates the use of the foregoing redirection facilities. The
man utility always writes a couple of lines to the standard error channel: Reformat
ting page. Wait when it begins and done when it ends. If you redirect only stan
dard output, these messages are seen on the terminal. To redirect the standard
error channel to a separate file, use the 2> redirection sequence; to send it to the
same place as standard output, use the 2>&1 sequence, as shown in the following
commands:
22
$
$ command
..
22
$ pwd
/home/glass
$ { cd /; pwd; is
/
207
Sequenced Commands
ENHANCEMENTS
Command Line Options
You might also like
- Project Finance Practical Case Studies PDFDocument228 pagesProject Finance Practical Case Studies PDFVan HuyNo ratings yet
- BTRFS: The Linux B-Tree Filesystem: ACM Transactions On Storage August 2013Document55 pagesBTRFS: The Linux B-Tree Filesystem: ACM Transactions On Storage August 2013Klaus BertokNo ratings yet
- How Many Words Do We Read Per MinuteDocument94 pagesHow Many Words Do We Read Per MinuteKlaus BertokNo ratings yet
- Research: Real Analysis Exchange Vol. 21 (1), 1995-96, Pp. 270-277Document8 pagesResearch: Real Analysis Exchange Vol. 21 (1), 1995-96, Pp. 270-277Klaus BertokNo ratings yet
- 03 Lexing ParsingDocument78 pages03 Lexing ParsingKlaus BertokNo ratings yet
- CD Lab ManualDocument55 pagesCD Lab Manualkalai100% (1)
- S&W Performance, and Go-back-N ARQ: Unit 02.01.03 CS 5220: Computer CommunicationsDocument13 pagesS&W Performance, and Go-back-N ARQ: Unit 02.01.03 CS 5220: Computer CommunicationsKlaus BertokNo ratings yet
- 1 Digit LED Segment Displays V2.1Document6 pages1 Digit LED Segment Displays V2.1Klaus BertokNo ratings yet
- Workshop 6Document1 pageWorkshop 6Klaus BertokNo ratings yet
- CreateSpace Java Jan 2016 ISBN 1523251433Document122 pagesCreateSpace Java Jan 2016 ISBN 1523251433Klaus BertokNo ratings yet
- Cs6612 Compiler LaboratoryDocument67 pagesCs6612 Compiler LaboratoryArvind RathoreNo ratings yet
- DRBD Pacemaker Corosync Mysql Cluster Centos7 PDFDocument16 pagesDRBD Pacemaker Corosync Mysql Cluster Centos7 PDFKlaus BertokNo ratings yet
- A Brief Introduction to Neural NetworksDocument244 pagesA Brief Introduction to Neural NetworksCimarrones EmprendedoresNo ratings yet
- Python For Finance (Yan 2014-05-11)Document115 pagesPython For Finance (Yan 2014-05-11)Klaus BertokNo ratings yet
- BRDMDocument468 pagesBRDMKlaus BertokNo ratings yet
- CD Lab ManualDocument55 pagesCD Lab Manualkalai100% (1)
- Shopping CartDocument75 pagesShopping CartDeepakNo ratings yet
- Java Persistence API Mini Book OverviewDocument60 pagesJava Persistence API Mini Book OverviewAnda Roxana NenuNo ratings yet
- IP Addressing & Subnetting WorkbookDocument58 pagesIP Addressing & Subnetting Workbookbaraynavab94% (32)
- English Grammar SecretsDocument66 pagesEnglish Grammar SecretsMbatutes94% (33)
- 02 C ExamplesDocument49 pages02 C ExamplesGoli PrabhakarNo ratings yet
- 02 C ExamplesDocument49 pages02 C ExamplesGoli PrabhakarNo ratings yet
- DevDaily Java OO Training CourseDocument153 pagesDevDaily Java OO Training CourseKlaus Bertok100% (1)
- The VIM Book (Unknown Author)Document572 pagesThe VIM Book (Unknown Author)Moe B. Us100% (22)
- OopcDocument39 pagesOopcMalikUbaidNo ratings yet
- VoIP PDF CONFIGURACIONDocument6 pagesVoIP PDF CONFIGURACIONMauricio PradaNo ratings yet
- An Introduction To C++: Dave KleinDocument37 pagesAn Introduction To C++: Dave KleinKlaus BertokNo ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Attributes and Usage of Jsp:Usebean Action TagDocument7 pagesAttributes and Usage of Jsp:Usebean Action TagkarunakarNo ratings yet
- VMware WorkstationDocument406 pagesVMware WorkstationsocrazNo ratings yet
- Introduction To Computers and Java: Walter Savitch Frank M. CarranoDocument77 pagesIntroduction To Computers and Java: Walter Savitch Frank M. CarranoBrandon KozakNo ratings yet
- iFIX Database WhitepaperDocument6 pagesiFIX Database WhitepaperjavierleraNo ratings yet
- SpringMVC Image JSP File ExampleDocument2 pagesSpringMVC Image JSP File ExampleEr Nitesh PandeyNo ratings yet
- MODBUS Communication Module for Planar4 SystemDocument4 pagesMODBUS Communication Module for Planar4 SystemGilberto Alejandro Tun BritoNo ratings yet
- Mysql Workshop Environment: Ivan Ma 2019-03Document8 pagesMysql Workshop Environment: Ivan Ma 2019-03Dang Huu AnhNo ratings yet
- Fix Broken SudoDocument3 pagesFix Broken SudoadhomNo ratings yet
- 10 Crs Diag Jfv4Document18 pages10 Crs Diag Jfv4Palash SarkarNo ratings yet
- Assignment No 2: My SQL Server Data Types and Their PurposesDocument2 pagesAssignment No 2: My SQL Server Data Types and Their PurposeszaianbNo ratings yet
- VisualAge PLI Programming Guide Ver 2.1Document587 pagesVisualAge PLI Programming Guide Ver 2.1neokci100% (1)
- A Letter Engraving Custom MacroDocument15 pagesA Letter Engraving Custom Macrofirepower117No ratings yet
- BCS101 - Focp PDFDocument125 pagesBCS101 - Focp PDFsania2011No ratings yet
- Evolution of Computers Through GenerationsDocument21 pagesEvolution of Computers Through Generationssiva prasadNo ratings yet
- Fonseca 14Document80 pagesFonseca 14DanNo ratings yet
- Arm BookDocument221 pagesArm BookGandhimathinathanNo ratings yet
- Sparcclassic Sparcclassic X Sparcstation LX Service Manual 801 2176 13Document199 pagesSparcclassic Sparcclassic X Sparcstation LX Service Manual 801 2176 13b5666266No ratings yet
- LAUNCH X-431 PRO 3 Product IntroductionDocument14 pagesLAUNCH X-431 PRO 3 Product IntroductionWilmer HuangaNo ratings yet
- MET 270905 IIT Careers Shikha MalhotraDocument6 pagesMET 270905 IIT Careers Shikha MalhotraVijendra Bhardwaj100% (1)
- Vba Cheat SheetDocument4 pagesVba Cheat SheetGilang SamudraNo ratings yet
- AB-58C ManualDocument15 pagesAB-58C Manualrafiknet10No ratings yet
- SmarTeam Design Express For CATIA Installation GuideDocument29 pagesSmarTeam Design Express For CATIA Installation GuidelceppetelliNo ratings yet
- JeffreyVandenorth - Final Resume AMDocument2 pagesJeffreyVandenorth - Final Resume AMJeff VandenorthNo ratings yet
- Error - Arranque ServidorDocument3 pagesError - Arranque ServidorCamilo GonzalezNo ratings yet
- Perangkat Penunjang Pembuatan Studio MetaverseDocument2 pagesPerangkat Penunjang Pembuatan Studio MetaverseMaulana JamaludinNo ratings yet
- VMware VSphere ICM v6.7Document3 pagesVMware VSphere ICM v6.7grnarayanan.rama99250% (1)
- Assignment 1 - Embedded System-1Document13 pagesAssignment 1 - Embedded System-1tamil shinchan0% (1)
- Maven Notes on Dependency ManagementDocument19 pagesMaven Notes on Dependency ManagementVenkat GowdaNo ratings yet
- Biw Ora Db2 ExportDocument24 pagesBiw Ora Db2 Exportmhku1No ratings yet
- Dev ListDocument7 pagesDev ListAlex TrouveNo ratings yet