Professional Documents
Culture Documents
Bandwidth Management Using Weighted Fair Queuing
Uploaded by
Bajirao MastaniCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Bandwidth Management Using Weighted Fair Queuing
Uploaded by
Bajirao MastaniCopyright:
Available Formats
See
discussions, stats, and author profiles for this publication at: https://www.researchgate.net/publication/237040650
Bandwidth management using weighted fair
queuing
Conference Paper January 2008
DOI: 10.1145/1509315.1509352
CITATIONS
READS
182
3 authors:
Mohammed Abdul Qadeer
Shahid Habib
Aligarh Muslim University
Independent Researcher
73 PUBLICATIONS 241 CITATIONS
5 PUBLICATIONS 0 CITATIONS
SEE PROFILE
SEE PROFILE
Ahmad Yazdan Javaid
University of Toledo
19 PUBLICATIONS 25 CITATIONS
SEE PROFILE
All in-text references underlined in blue are linked to publications on ResearchGate,
letting you access and read them immediately.
Available from: Mohammed Abdul Qadeer
Retrieved on: 27 September 2016
Bandwidth Management using Weighted Fair Queuing
Mohammed A. Qadeer
Shahid Habib
A. Yazdan Javaid
Department of Computer Engg.
Aligarh Muslim University
Aligarh- 202002, India
Department of Computer Engg.
Aligarh Muslim University
Aligarh- 202002, India
Department of Computer Engg.
Aligarh Muslim University
Aligarh- 202002, India
maqadeer@gmail.com
shahid_lko2003@yahoo.com
ahmad2yazdan@gmail.com
ABSTRACT
In this paper, we present a new technique for Bandwidth
allocation among users in a server controlled network in a
technical, industrial or institutional setup. In creating our project
we shall be using fair queuing i.e. the system which is connected
to the internet and on which our software is installed will be
receiving all the packets requested from the user. Then putting all
packets in a queue and transmitting them after a suitable delay
will guarantee that the users receive the allocated bandwidth. The
method is to send all network traffic to a centralized bandwidth
manager that provides prioritization, rate limiting and other
related services.
Categories and Subject Descriptors
C.2.3. [Computer Communication Networks]: Network
Operations - Network management, Network monitoring, Public
networks.
General Terms
Algorithms, Management, Measurement, Documentation,
Performance, Design, Economics, Reliability, Experimentation,
Security.
Keywords
Resource Allocation, Bandwidth Limiting, Network Management,
Bandwidth management
1. INTRODUCTION
In the fields of networking and communications, there is a
continual concern over poor bandwidth utilization [1]. It is
sometimes the case that host computers can employ applications
or processes that are very bandwidth intensive, limit the amount
of bandwidth that other hosts have at their disposal. This in turn
limits the amount of work that can be done in a given amount of
time. In order to alleviate this problem, we believe that we can
develop a system wherein the amount of bandwidth that each
application or process uses on a network can be measured in realtime.
Permission to make digital or hard copies of all or part of this work for personal or classroom use is
granted without fee provided that copies are not made or distributed for profit or commercial
advantage and that copies bear this notice and the full citation on the first page. To copy otherwise,
or republish, to post on servers or to redistribute to lists, requires prior specific permission and/or a
fee.
International Conference On Advanced Infocomm Technology08,
Jul 2931, 2008, Shenzhen, China.
1.1 Existing Techniques
In this section, we review two classic packet queuing methods for
data networks [2], namely, Class based queuing and Priority
Queuing.
1.1.1 Class Based Queuing
Class Based Queuing (CBQ) is a queuing algorithm that divides a
network connection's bandwidth among multiple queues or
classes. Each queue then has traffic assigned to it based on source
or destination address, port number, protocol, etc. A queue may
optionally be configured to borrow bandwidth from its parent
queue if the parent is being under-utilized. Queues are also given
a priority such that those containing interactive traffic, such as
SSH, can have their packets processed ahead of queues containing
bulk traffic, such as FTP.
CBQ queues are arranged in a hierarchical manner. At the top of
the hierarchy is the root queue which defines the total amount of
bandwidth available. Child queues are created under the root
queue, each of which can be assigned some portion of the root
queue's bandwidth. For example, queues might be defined as
follows:
Root Queue (2Mbps)
Queue A (1Mbps)
Queue B (500Kbps)
Queue C (500Kbps)
In this case, the total available bandwidth is set to 2 megabits per
second (Mbps). This bandwidth is then split among three child
queues.
A queue can be configured to borrow bandwidth from its parent if
the parent has excess bandwidth available due to it not being used
by the other child queues. Consider a queuing setup like this:
Root Queue (2Mbps)
UserA (1Mbps)
ssh (100Kbps)
ftp (900Kbps, borrow)
UserB (1Mbps)
If traffic in the ftp queue exceeds 900Kbps and traffic in the
UserA queue is less than 1Mbps (because the ssh queue is using
less than its assigned 100Kbps), the ftp queue will borrow the
excess bandwidth from UserA. In this way the ftp queue is able
to use more than its assigned bandwidth when it faces overload.
When the ssh queue increases its load, the borrowed bandwidth
will be returned.
Copyright 2008 ACM 978-1-60558-088-3$5.00.
1.1.2 Priority Queuing
Priority Queuing (PRIQ) assigns multiple queues to a network
interface with each queue being given a priority level. A queue
with a higher priority is always processed ahead of a queue with a
lower priority. If two or more queues are assigned the same
priority then those queues are processed in a round-robin fashion.
system.
The queuing structure in PRIQ is flat -- you cannot define queues
within queues. The root queue is defined, which sets the total
amount of bandwidth that is available, and then sub queues are
defined under the root. Consider the following example:
The software will need to have a centralized place of operations.
This means that it will run on a centralized server. As a result, the
software will be in a secure and controlled environment, since
servers provide a high performance environment with the added
protection against potential security breaches.
Root Queue (2Mbps)
Queue A (priority 1)
Queue B (priority 2)
Queue C (priority 3)
The root queue is defined as having 2Mbps of bandwidth
available to it and three sub-queues are defined. The queue with
the highest priority (the highest priority number) is served first.
Once all the packets in that queue are processed, or if the queue is
found to be empty, PRIQ moves onto the queue with the next
highest priority. Within a given queue, packets are processed in a
First in First out (FIFO) manner.
It is important to note that when using PRIQ you must plan your
queues very carefully. Because PRIQ always processes a higher
priority queue before a lower priority one, it's possible for a high
priority queue to cause packets in a lower priority queue to be
delayed or dropped if the high priority queue is receiving a
constant stream of packets
1.2. Our Approach
Today in the modern communication world, the traffic that exists
in the Internet is becoming more and more abnormal. This was
mainly due to increase in number of users day by day which
results in bandwidth congestion, poor response time for end user's
etc. The most efficient solution to this problem is to manage and
allocate the existing bandwidth proportionally using suitable
queuing disciplines. It is a full featured technology which may
reduce the cost and improve network performance. If there was a
way to control bandwidth that a service already has, then it can
create a smarter network for all users [3]. This is the main
objective of our project. We explored ways to keep a real-time
log of which applications and hosts are using the most bandwidth
and divert or restrain the bandwidth in order to make the network
more efficient. This will be done by creating an application to sit
on server. This application will serve three primary purposes. It
will be a firewall, bandwidth allocator, and active application
monitor. The data collected will be the basis in creating a smarter
self-sustaining network. An improved condition of this project is
that it will be fully self-sustaining. The database on the server will
keep track of the running applications and prioritize those that are
running. There will be no need for a system administrator because
the database will decide based on priority to close or limit
bandwidth. Bandwidth can be either allocated on committed
bandwidth allocation basis to the users or on burstable bandwidth
allocation basis where extra bandwidth is allocated to the current
users. However we will deal with the first one
1.3 Design Requirements
What we plan to accomplish is the development of a product that
will help control the distribution of bandwidth in a network. There
are several key features that the product must have in order to
fulfill all the requirements of such a bandwidth controlling
1.3.1 Centralization of operations:
1.3.2 Windows GUI:
The user interface of the software will be windows-based. In
order for our product to reach the broadest market possible, it will
need to be compatible with the software that is already widely
used. In servers, specifically, the launch of such operating
systems as windows means that our software has to meet and be
compatible with Windows standards to be able to reach a high
volume of customers. Furthermore, a windows user interface will
be simpler to use and provide training for (if necessary).
1.3.3 Software Control:
This is one of the most important objectives of our project
because of the direct need to reduce bandwidth consumptions of
programs that may be of high importance in a work environment.
For example, in advertising companies, where high-end programs
are used to download, share and transfer information among
workstations, there is a great need to have a certain amount of
bandwidth available. In recent times, it has been found that the
use of unimportant programs such as Kazaa, Grokster, WinMX
and others is growing among employees. These programs take
valuable resources away from the company, which is investing its
money in a fast internet connection.
1.3.4 Data Transfer Rate:
Bytes per second of data sent and received will be monitored and
controlled by the software. To make it simpler for the network
manager, an added feature can be planned in the future where one
is able to create rules and filters that could regulate more
efficiently the way certain programs transmit data A few
constraints are recognized when designing the project. Since this
project is being created for the reason of conserving bandwidth,
the program itself must not impede on the data communications.
Since the design calls for the host machines to continually
connect to the database, bandwidth will be used during this
transfer. This will have to be monitored and programmed
efficiently.
2. THE FINAL APPROACH
2.1 Core of the Design
2.1.1 Fair Queuing
Fair queuing is a technique that allows each flow passing through
a network device to have a fair share of network resources [4].
Users or processes having paid for higher bandwidth will be
guaranteed that amount of bandwidth at all times.
2.2 System Design
The implementation idea was to simply restrict bandwidth based
on application priority because of the reason of the requirement of
such bandwidth limiting in any industrial, technical or
institutional setup.
Basic implementation is a five phase process. Starting from
authenticating the user to finally controlling every packet passing
through the server, all phases require a powerful and stable server,
being the reason behind selecting the platform for our application
as a UNIX platform. The phases are described below.
Procedure Call or DPC) that will later process the hardware
request and notify the upper layers that a packet has been
received. The CPU will process the DPC routine when no
interrupt requests are pending. Interrupt coming from the NIC are
disabled when a NIC device driver is performing its work because
a processing of a packet has to be completed before the next one
2.2.1 Authentication
The first phase basically involves authentication of users on the
network to check whether the user is authorized to access internet
from that particular terminal. We dont require any username and
password based authentication instead we will use ip address or
MAC address based authentication which is very secure and
invulnerable to any kind of network problems and attacks (passive
or active). The system also checks the priority of the service
based on its protocol and thus, determines the amount of
bandwidth which needs to be allocated to that particular service.
As soon as a user becomes active, packets are exchanged between
the server and the user. The server during this process captures
those packets and determines their MAC address from the datalink header and matches the address with those present on the
database. If an entry is found for that MAC address then an o.k.
message is sent to the user else a message connection refused is
send to the user. Since, IP addresses can change in a DHCP
environment MAC addresses are used to make the system less
vulnerable to unauthorized access from the users.
2.2.2 Packet Capturing
When the user gets the authentication, it gets access to the internet
through the server and can request whatever it wants. Now, to
limit bandwidth based on priorities, when the requests of each
user is granted and a reply is received, the incoming packets
needs to be captured and stored somewhere so as to provide a
limited rate to the user.
Packets can be captured either using hardware or a software.
Software tools are often preferred often because of their low cost
and high versatility. We will be using the libraries like jpcap and
winpcap to capture packets.
2.2.2.1 How are packets captured by the NIC?
Modern NICs have a small memory required to enable the
receiving and sending packets at the full link speed,
independently of the host capabilities .moreover , NICs perform
some preliminary checks such as CRC errors ,short Ethernet
frames, while packets are stored in the on board memory so that
invalid frames can be discarded immediately.
is serviced. Moreover since interrupt generation is a costly
operation, modern NICs allow more than one packet to be
transferred in the context of a single interrupt so that an upper
layer driver is able to process several packets each time it is
activated.
2.2.2.2 What is JPCAP
Traditionally, applications running in user space have been able to
view and operate on packets only when the packets originate in
user space or once the packets pass up through the protocol stack
into the application layer. Recently, however, computer
programmers and network administrators have seen a need to be
able to monitor packet traffic through the network and analyze in
user-space packets that are being processed by the kernel stack
code. For this purpose, many operating systems now provide the
ability for user-level processes to sniff or capture network
traffic, by employing packet taps in kernel space.
After a valid packet has been received by the NIC, this generates
a request toward the bus controller for a bus mastering data
transfer. At this point the NIC takes control of the bus, transfers
the packet to the NIC buffer in the hosts memory, releases the
bus and generates a hardware interrupt towards the Advanced
Programmable Interrupt Controller (APIC) chip. This chip wakes
up the OS interrupt handling routine, which triggers the Interrupt
Service Routine of the NIC device driver
Jpcap is an open source library for capturing and sending
network packets from Java applications. It provides facilities to:
The ISR of a well written device driver has little to do. Basically
it checks if the interrupt to itself and acknowledges it. Then the
ISR schedules a lower priority function (called the Deferred
Capture raw packets live from the wire.
Save captured packets to an offline file, and read captured
packets from an offline file.
Automatically identify packet types and generate
corresponding Java objects (for Ethernet, IPv4, IPv6,
ARP/RARP, TCP, UDP, and ICMPv4 packets).
Filter the packets according to user-specified rules before
dispatching them to the application.
send raw packets to the network
2.2.2.3 Problem using JPCAP/WINPCAP
Existing packet taps provide a useful mechanism for user space
monitoring of network packet traffic. However, these packet taps
do not provide means for altering the packets in user space or for
changing the flow of packets Jpcap captures and sends packets
independently from the host protocols (e.g., TCP/IP). This means
that Jpcap does not (cannot) block, filter or manipulate the traffic
generated by other programs on the same machine: it simply
"sniffs" the packets that transit on the wire. Therefore, it does not
provide the appropriate support for applications like traffic
shapers, QoS schedulers and personal firewalls.Packet capture
components are usually transparent to other software modules like
protocol stacks, thus not influencing the systems behavior .They
just insert a hook in the system so that they can be notified
usually through a callback function called tap()-as soon as a new
packet arrives from a network. Packet capture components are
usually implemented as network protocols drivers in Win32.A
packet not destined to the host will be captured by JPCAP if it is
running in the promiscuous mode (this mode captures all packets
whether destined to the host or not).The NIC upon recognizing
that the packet does not belong to it will not send it to the protocol
stack but will pass it onto the Ethernet. Our software will queue
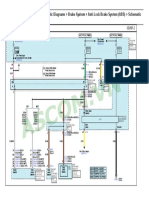
the packet and send it after a requisite delay. So the destination
will receive two packets: One send by our software and one by
the NIC. This will result in redundancy as shown in Fig 1 in
which two copies are created for every packet.
the stack, and it is then deleted from kernel space. Similarly, once
an outgoing packet has been processed by the application layer in
user space, it is copied to kernel space to be processed by the
remainder of the protocol stack, and it is then deleted from user
space.
2.2.2.4 The Solution
One solution may be implemented with a lightweight
modification to kernel code, and an associated application
programming interface (API). Provided with the collective ability
to divert packets from the kernel stack to user space and inject
packets back into the kernel stack from user space, a program
running in user space may then examine and manipulate packets
on their way through the kernel stack. In addition, provided with
the ability to divert packets from the kernel stack to user space, a
program running in user space may effectively drop packets
from the kernel stack.
The system facilitates creation of a special socket for passing
packets between kernel space and user space. The system in turn
facilitates creation and application of a packet filter associated
with the socket, in order to trap incoming or outgoing packets
being processed in the kernel at a designated point in a protocol
stack. Once a packet is trapped, it is moved through the socket
into user space, thereby at least temporarily preventing the
protocol stack from further processing the packet. In user space,
an application may operate on the packet, for instance, modifying
aspects of the packet or deleting the packet altogether. The system
in turn facilitates injection of a packet from user space into kernel
space, and into a designated point in the protocol stack for desired
stack processing.
When a packet passes between the application and transport
layers of the TCP/IP protocol stack, the packet moves between
user space and kernel space. Since user space and kernel space are
separate areas of memory, however, the process of moving a
packet typically includes copying the packet to the destination
area and then deleting the original. Thus, in practice, once an
incoming packet reaches the top of the kernel protocol stack, it is
copied to user space to be processed by the application layer of
Figure 2. The Solution
An example of one such packet filter is the BSD Packet Filter
or Berkeley Packet Filter (BPF).The main function of the filters
is to organize the packets based on their properties. The
classification of packets may be done by listening their respective
IP header, IP address, port numbers etc.
Another solution is not to pass copy of the packet to the user but
instead pass its address. Since the packet is initially stored in the
NIC buffer passing that address will ensure that no copy is
created.
Another solution is to modify the Deferred Procedure Call (DPC)
function so that it only notifies the packet capture drivers and not
the protocol layer drivers. So packet not destined to the host will
only be captured by JPCAP and processed by our software and
hence will not result in redundancy. However we will be using the
first solution.
2.2.3 Packet Queuing
When the system sees the packet, it can do one of three things:
1. Discard the packet: This allows the system to provide a very
robust and granular packet filtering mechanism.
2. Forward the packet at real time: This means that the packet
bypasses the entire bandwidth management system and is
immediately forwarded by the device. The end- result is
effectively the same as if bandwidth management was not
enabled at all. This will be done if some user is having such
privileges.
3. Prioritize the packet: This allows the mechanism to provide
actual bandwidth management services (applicable to rest of
the users).
Packets captured in previous step are now maintained in separate
dynamic queues based on their destination address so as to
transmit to their respective destination.
Any of the following methods can be used for queuing.
2.2.3.1 Maxmin fairness
Maxmin fair allocation maximizes the minimum share of a
session whose demand is not fully satisfied. It maximizes the
bandwidth allocation of each session subject to the constraint that
an incremental increase in allocation of the bandwidth cannot lose
feasibility or reduce the bandwidth of another session with a
bandwidth equal to or smaller than session i. For example, if four
sessions each require bandwidths 2, 2.6, 4, and 5, respectively,
but the total capacity is 10, the allocated bandwidths of the four
sessions would be 2, 2.6, 2.7, and 2.7, respectively, according to
the maxmin fairness.
2.2.3.2 Priority Queuing (PRIQ)
It assigns multiple queues to a network interface with each queue
being given a priority level. A queue with a higher priority is
always processed ahead of a queue with a lower priority. If two or
more queues are assigned the same priority then those queues are
processed in a round-robin fashion. However we will be using fair
queuing. An example of how weighted fair queuing works (as
shown in Figure 3).
Queues can be built on the basis of MAC address if the bandwidth
is allocated to the hosts. However if the allocation is done on the
type of application then queues will be built on the basis of
protocols, ports etc .If application based queuing is done then
packets are queued according to the application they belong to i.e.
ftp, http, udp or P2P.The queues of applications which are of
higher priority such as rtp will be allowed to send more no. of
packets than the applications which are of low priority as P2P in
order to ensure that they receive the allocated bandwidth. The end
users having MAC addresses MAC1, MAC2 and MAC3.Services
like real time transfer, ftp, and http have been allocated say 200
kbps, 200 kbps and 100 kbps bandwidth respectively. The total
bandwidth available to the server is say 500kbps.The incoming
packets are examined for the type of service (i.e. either their port
no. or protocol used).The NIC queues all the incoming packets
irrespective of the service. Then they are queued into their
respective queues. Packets belonging to the service having highest
priority will be queued in a queue that will be sending most no. of
packets in a unit time. The packets are sent from the queues to the
output buffer at certain intervals. In 1 second time the queue of
Service1 will be allowed to send 200 kb/1500 bytes packets,
Service2 will be allowed to send 200 kb/1500 bytes packets and
Service3 will be allowed to send 100 kb/1500 bytes packets
considering each packet to be of 1500 bytes. This pattern will be
followed in a round robin manner. A timer and a counter are used
to ensure that the queues send packets for specified duration only.
The time slot available to each queue is based on their service.
The services on the basis of port nos. etc. are mapped onto a
translation table which gives the allocated bandwidth to that
service
Figure 3. Packet Queuing
2.2.4 Inserting delay
All of the services are then provided the required rate (based on
their priority) by queuing the packets and making them wait for
their turn. A queue after sending packets will have to wait for its
turn again since the packets are send in a round robin manner.
One problem in sending the packets is that the traffic arrives in
bursts. A higher priority queue that has to send more no. of
packets may not have those much packets in its queue while the
low priority queue may have a higher no. of packets. The solution
to this problem is to monitor the flow of incoming packets and to
take it as criteria in deciding how much packets each queue will
send to guarantee each service its allocated bandwidth.
2.2.5 Packet transmitting
Finally, after determining the required delays for different users,
the packets received are now sent to the respective destinations by
the data rate determined by inserting delays between
transmissions of each packet. The packets are send by first finding
out the Network Interface address and then sending the packets to
that NIC. The libraries jpcap and winpcap are used for sending
the packets.
3. PRACTICAL APPLICATIONS OF
BANDWIDTH LIMITING
With the increasing proliferation of broadband, more and more
users are using Peer-to-Peer (P2P) protocols to share very large
files, including software, multi-media files, and applications. This
trend has exponentially increased traffic flows across a very wide
area network. If you are coping with excessive bandwidth
consumption due to P2P traffic, such as Bit Torrent, our
Bandwidth Limiter can solve your problem of poor bandwidth
utilization and high bandwidth consumption. The applications of
bandwidth limiter are:
Ensure that critical applications are not impacted by nonpriority traffic.
Deliver optimal application performance by allocating more
bandwidth for higher priority applications
Provide flexible bandwidth limits and traffic queuing
Control rate classes based on any traffic variable
Enable application bandwidth to be shared across similar
priority applications for better resource sharing
Ensure that specific types of application traffic stay within
authorized boundaries
3.1 Increasing Security
Denial of Service attacks can come from a variety of sources,
under a variety of guises. Sophisticated attacks are difficult to
prevent as attack traffic appears as legitimate traffic. A way to
thwart denial of service attacks is to set rate limits at traffic
ingress points for suspect traffic, such as TCP SYN packets,
PING packets and gateway broadcasts packets. Universities can
limit outgoing attack traffic without stripping users freedom by
imposing a rate limit on all packets destined for unknown
application ports. Bandwidth Limiter can also provide a monitor
mode whereby statistics on each traffic class are collected without
actual bandwidth enforcement. This allows administrators to
observe the typical amount of bandwidth consumed by each type
of suspect traffic under normal conditions, then, set bandwidth
limits that can prevent and alert them of potential attacks. Packet
filtering can be done at the NIC to prevent packets such as ICMP
etc from flooding the users. The filter can be based on protocol
type, port no., subnet, etc
4. WHY BANDWIDTH LIMITER IS
BETTER
First of all there isnt any software available that runs on a host
running other applications also. The Bandwidth Limiter provided
by 24 Online runs as a separate OS. Also Bandwidth Limiter can
be used to provide following functionalities:
traffic loggers
traffic generators
user-level bridges and routers
network intrusion detection systems (NIDS)
network scanners
Security tools
Secondly, the performance of our system is quite good in
providing the Quality of service required by todays data
operators and organizations. The system will be able to provide
actual bandwidth allocated to the particular service. Obviously, in
any organization, the resources are allocated on the basis of
priorities, so same will be done by our system. Since time is spent
in capturing the packets, therefore, in queuing them and then
sending them, there is a minor delay in the users receiving the
packets. Also the OS has to run many other processes and each
process receives a quantum of time to execute. However taking
into the account the fewer resources our product requires and the
freedom of running the application along with other applications
and the near to the allocated bandwidth each user receives, it is
obviously better than contemporary Bandwidth Limiters
One of the greatest problems that organizations encounter in
networking and communications is poor bandwidth utilization.
Even with current technologies, it is not easy to determine in realtime how a network is being used. This situation leads to
uncontrolled allocation of network resources to host computers
that employ applications or processes that are very bandwidth
intensive, thereby limiting the amount of bandwidth that other
hosts have at their disposal. As mentioned earlier in this report,
the main technical objective of the project is to implement a
networking tool that will allow better management of network
traffic. A careful examination of the technical challenges,
combined with the financial aspect of what the processes and
equipment required will involve has led us to conclude that this
project is feasible. Some of the most important aspects considered
during the analysis of the products performance are its ability to
prioritize and allocate network bandwidth among hosts on a
network, provide enough security as to prevent tampering with or
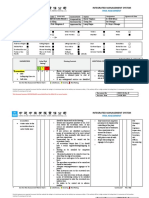
taking over a disproportionate amount of bandwidth, centralized
operations, multiplatform GUI, etc. A short overview of what the
implementation of our project might look like can be seen in the
Figure 4.
5. REFERENCES
[1]. Tanenbaum, A.S., Computer Networks, third ed., PrenticeHall, Inc., Englewood Cliffs, NJ, 1996, 380 381.
[2]. Bertsekas, D.P., Gallager, R., Data Networks, Prentice-Hall,
Englewood Cliffs, NJ, 1992.
[3]. Bolliger, R.., Gross, T.R., Bandwidth monitoring for
network-aware applications, High Performance Distributed
Computing, 2001. Proceedings. 10th IEEE International
Symposium on , 7-9 Aug. 2001, 241 -251
[4]. Shreedhar, M., Varghese George, Efficient Fair Queuing
using Deficit Round Robin
[5]. Tommy K Paul 1994 Building Network Bandwidth
Network News - The Network Professional Association
monthly publication
http://www.sju.edu/%7Ejhodgson/netw/tp_asg4.html
[6]. Bandwidthcontroller.com
Internet
sharing
guide
http://bandwidthcontroller.com/internet-sharing.html
[7]. Douglas E. Comer., 1995, Internetworking with TCP/IP
Vol.1: Principles, Protocols, and Architecture. 4th Edition
Upper Saddle River: Prentice Hall.
[8]. H. Zhang, D. Ferrari, Rate-controlled service disciplines J.
High Speed Networks 3 (4) (1994) 389412 connection
admission control for bandwidth management of an Internet
access link, Communications Magazine, IEEE , Volume: 38
Issue: 5 , May 2000 Page(s): 160 -167
[9]. Dr Orhan Gemikonakli (2003) Network Management
http://www.cs.mdx.ac.uk/staffpages/orhan/csy4061/netman1.
htm
[10]. Juniper.net (1999) Managing Bandwidth from a Large
Traffic
Source
http://www.juniper.net/solutions/literature/solutionbriefs/351
000.pdf
[11]. Cisco Systems (2001) Meet the Cisco Intelligent Engine
2100 Service Provider Solutions
[12]. SearchNetworking.com (2001) Data Transfer Rate
http://searchnetworking.techtarget.com/sDefinition/0,,sid7_g
ci213492,00.html
[13]. The Internet Services Company (2002) Active Bandwidth
Management
Device
Networking
http://www.interchannel.net/product/networking/bandwidth.
htm
You might also like
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- TP 5990Document40 pagesTP 5990Roberto Sanchez Zapata100% (1)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Approval Process Handbook 2019-20Document1 pageApproval Process Handbook 2019-20Arvind SharmaNo ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5795)
- APIs and Business Functions GuideDocument104 pagesAPIs and Business Functions GuideSindhu RamNo ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Royal 77Document131 pagesRoyal 77victorNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Generators Acapp 2nd1718 4Document19 pagesGenerators Acapp 2nd1718 4Anonymous uCjM4Q0% (2)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- 2018 G 1.0 MPI KAPPA Schematic Diagrams Brake System Anti-Lock Brake System (ABS) Schematic DiagramsDocument1 page2018 G 1.0 MPI KAPPA Schematic Diagrams Brake System Anti-Lock Brake System (ABS) Schematic DiagramsHuy Trần QuốcNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- CSCEC HSE-F-01 Risk Assessment Form - Excavation& Backfilling - RA-02Document12 pagesCSCEC HSE-F-01 Risk Assessment Form - Excavation& Backfilling - RA-02Dan SarmientoNo ratings yet
- Seminar On: Underwater WeldingDocument30 pagesSeminar On: Underwater WeldingGAJENDRA KUMARNo ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- Material de Inspección VisualDocument27 pagesMaterial de Inspección VisualGuillermo BarragánNo ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Rube GoldbergDocument20 pagesRube Goldbergapi-297309213No ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- RT-1000 Terex, RT-100 TonDocument14 pagesRT-1000 Terex, RT-100 TonMaximo CC100% (1)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Cement Invoice No. For TCDocument3 pagesCement Invoice No. For TCAzhar ShaikhNo ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- 3 - Chemical Thermodynamics and ThermochemistryDocument3 pages3 - Chemical Thermodynamics and ThermochemistryYawn D ArtistNo ratings yet
- System Requirements PerformancesDocument3 pagesSystem Requirements PerformancesΒΙΒΗ ΓΚΑΣΙΩΝΗNo ratings yet
- Productguide - Chemicals Aceites FleetriteDocument12 pagesProductguide - Chemicals Aceites FleetriteJose AlbertoNo ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Bonny 13 EspañolDocument284 pagesBonny 13 EspañolOscar CorderoNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Uwiciit Brochure v42Document2 pagesUwiciit Brochure v42Javian CampbellNo ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Accounting Information SystemDocument2 pagesAccounting Information SystemJansen Alonzo BordeyNo ratings yet
- Sample Soil Report 1Document27 pagesSample Soil Report 1prince francisNo ratings yet
- Handout Contoh SoalDocument12 pagesHandout Contoh SoalIntan NugrahaNo ratings yet
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Conpress: Moidinafsan - Cv15@Rvce - Edu.InDocument3 pagesConpress: Moidinafsan - Cv15@Rvce - Edu.InMoidin AfsanNo ratings yet
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- APK 20091019 Electrocardiography+CablesDocument18 pagesAPK 20091019 Electrocardiography+Cablesأحمد العريقيNo ratings yet
- Top Secrets of The VedasDocument54 pagesTop Secrets of The Vedasbiswajit_paulNo ratings yet
- Buzzer WT1205Document1 pageBuzzer WT1205Tiago Alves Dos SantosNo ratings yet
- Malate + NAD Oxaloacetate + NADH + HDocument14 pagesMalate + NAD Oxaloacetate + NADH + HRonaldNo ratings yet
- History: Aviation Is The Practical Aspect or Art ofDocument3 pagesHistory: Aviation Is The Practical Aspect or Art ofEarle J ZaficoNo ratings yet
- Aero EngineDocument118 pagesAero EngineTarun Choudhary100% (1)
- Quality Assurance and ValidationDocument62 pagesQuality Assurance and ValidationMacharia ZachariaNo ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Basic Design of AHU (General)Document64 pagesBasic Design of AHU (General)Dimyati Es100% (5)
- History of Information Technology: PremechanicalDocument5 pagesHistory of Information Technology: PremechanicalMichael RamogaNo ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)