Professional Documents
Culture Documents
DWT-SVD Based Visual Cryptography Scheme For Audio Watermarking
Uploaded by
theijesOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
DWT-SVD Based Visual Cryptography Scheme For Audio Watermarking
Uploaded by
theijesCopyright:
Available Formats
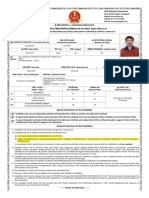
International Journal of Engineering Science Invention
ISSN (Online): 2319 6734, ISSN (Print): 2319 6726
www.ijesi.org ||Volume 5 Issue 11|| November 2016 || PP.61-65
DWT-SVD Based Visual Cryptography Scheme for Audio
Watermarking
Mukul Y. Kantharia 1, Nikhil P. Patel2
1
2
(EC Department, B & B Institute of Technology /GTU, India)
(EC Department, B & B Institute of Technology /GTU, India)
Abstract: Secured access to the Internet and data resources has a high impact in defense system. This
dependency has brought many threats to information security. As aresult, reliably secure mechanisms are
required to protect most untold and blueprint of defenseinformation against vulnerabilities like ID spoofing and
unauthorized access to top most system of country. In this paper, we proposed algorithm based on audio
watermarking using DWT-SVD algorithm with visually crypted image message. The army people may have
access to listen radio and communicate through walkie talkie which is audio format data. In proposed work we
are hiding visually crypted image massage in audio file which may decrypted by proving shared image and
extracted watermark image without affecting original audio. We did comparative analysis of various attacks on
audio file after watermarking and calculated robustness and SNR value to support out work.
Keywords- SVD, DWT, VC, SNR, Robustness, Audio watermarking
I. Introduction
Visual cryptography is a cryptographic technique which allows visual information (pictures, text, etc.) to be
encrypted in such a way that decryption becomes a mechanical operation that does not require a computer. One
of the best-known techniques has been credited to Moni Naor and Adi Shamir, who developed it in 1994. They
demonstrated a visual secret sharing scheme, where an image was broken up into n shares so that only someone
with all n shares could decrypt the image, while any n1 shares revealed no information about the original image.
Each share was printed on a separate transparency, and decryption was performed by overlaying the shares.
When all n shares were overlaid, the original image would appear. Applications that take full advantage of such
simple yet secure scheme[1]. Audio Watermarking is a watermarking technique in which left and right channel of
audio file is modified based on watermark object (visually crypted image). Discrete wavelet transform is used to
find lowest frequency region of audio file. After that lowest frequency part (LL) region may processed with
singular vector decomposition (SVD). Low frequency region having least information of object so we can
modify singular part of decomposed vector for embedding the watermarked bit.
II. Visual Cryptography with Dwt-SVD Audio Watermarking
1.1 Visual Cryptography
Visual Cryptography Scheme (VCS) is an encryption method that usescombinatorial techniques to encode secret
text message. The idea is to convert the text massage into an image and encode this image into N twilight
images. Thedecoding only requires only selecting some subset of these N images, making intensity of hidden
part of them, and stacking them on top of each other. In this Paper,we will provide the readers an overview of
the basic VCS constructions, as well asseveral extended work in the area for audio watermarking purpose. In
addition, we also review several techniques with improved VCS (by selecting Exor and Exnor operation in
random manner) that take full advantage of such simple yet secure scheme.The simplest Visual Cryptography
Scheme is given by the following setup. Asecret image consists of a collection of dark(0) and bright(1) pixels
where each pixel isprocessed independently. To encode the secret, we divide the original image into n
modifiedversions (referred as shares) such that each pixel in a share now subdivides into m darkand bright subpixels. To decode the image, we simply pick a subset S of those n sharesand copy each of them onto a
transparency. If S is a "qualified" subset, then stackingall these transparencies will allow visual recovery of the
secret.
Fig. 2.1 VCS scheme[1]
www.ijesi.org
61 | Page
DWT-SVD Based Visual Cryptography Scheme for Audio Watermarking
Figure 2.2 provides anexample of such construction. Suppose the secret image "GCET Engineering College" is
divided into 4 shares,which is denoted by ={1,2,3,4} and that the qualified sets are all subsets of
{1,2},{2,3} and {3,4}.Then the qualified sets are exactly the following:
qual = {{1,2},{2,3},{3,4},{1,2,3},{2,3,4},{1,3,4},{1,2,3,4}} (2.1)
Fig 2.2 (a) Original Image (b),(c) Generated Shared image after VCS, (d) Recovered image from generated
shares
1.2 Audio Watermarking with SVD-DWT
The DWT will be used to find extreme low frequency region so after embedding least number of audio content
may be unaffected. In our paper , we proposed 3 level DWT for better imperceptible and robustness. The four
level DWT is shown in Fig. 2.3.
Fig. 2.3 Three Level DWT decomposition [2]
SVD is used to find singular vector of decomposed dwt vector. Proposed work is changing diagonal s value of s
matrix to embedded watermark image bit (after VCS).
Table 2.1 S matrix formation
S11
0
0
0
0
S22
0
0
0
0
S33
0
0
0
0
S44
III. Proposed Work
The proposed system having two basic parts, first one is Visual Cryptography of Secrete image and the will
forward for audio watermarking.
Fig 3.1 Watermark Embedding System.
www.ijesi.org
62 | Page
DWT-SVD Based Visual Cryptography Scheme for Audio Watermarking
In Embedding system, secrete image will firstly have processed for visual cryptography scheme, based on VCS
scheme share 1 and share 2 of secrete image is available for next procedure. Each share part in now
independently processed with Audio watermarking method based on improved DWT-SVD algorithm (proposed
by Al. Haj) with slight modification in extraction part.
The audio file is rearranging in to finite block structure for processed with discrete wavelet
transformation(DWT). In proposed work, 4-level DWT was processed to get less informative part of audio
signal in terms of most low frequency part of audio file so after watermarking main audio file is least changed
will reflect best SNR. Components of DWT is now processed with Singular vector decomposition (SVD) to
obtain S matrix. Modification of S matrix is taken place based on watermarked image bits (algorithm 1). Last
step of algorithm is to take inverse SVD and then Inverse DWD to obtain audio watermarked file with secrete
visually encrypted image. {both share images are passed through this process}
Algorithm 1 (Embedding Procedure) for both share1 & share2
----------------------------------------------------------------------------------------------------------------------------- ---------I. Input Secrete image
II. Apply VCS system to get Share1(s1) & Share2(s2)& reform images in to vector form. (1x N)
III. Take Audio file (Mx2)- Left and RightChannel Part { [a,s]=audioread(name.mp3).
IV. Divide Audio file in to finite blocks (15000 sample value/block taken)
V. Find DWT of selected block. ([da,db]=wavedec2(block)) and reform D matrix. [3]
VI. Process D matrix for SVD decomposition. ([U, S, V]=svd(D)].
VII. Modify S value based on watermark image bits i.e. Snew= Wn + * S (Wn: Image bit n, : intensity of
watermark)
VIII. Find inverse SVD ( U * Snew * VT) and its inverse DWT(waverec).
(Final Audio File with Watermarked Image).
To get Encrypted image back we have to segregate audio file which we got after embedding process. Fig. 3.2 is
related with segregation of watermarked audio.
Fig 3.2 Watermark Segregation/Extraction System.
The Watermarked audio file is firstlydivided in to finite block for processing for discrete wavelet
transformation. The formatted D matrix is now processed for SVD decomposition for watermark extraction
process. Based on New S matrix value and old S(S vector of Extraction process), we may find watermarked
image bits(Wn) by implementing equation 3.1.
W n 1, if
S o ld
(3.1)
Snew
W n 0 , if
S o ld
Snew
We can get both shares using same process and both shares are now passed through visual DE cryptographic
process by use of Ex-OR or Ex-NOR gate operation based on defined schemes. Output of that process is our
hidden secrete image behind audio file.
www.ijesi.org
63 | Page
DWT-SVD Based Visual Cryptography Scheme for Audio Watermarking
Algorithm 2 (Segregation/Extraction Process)
----------------------------------------------------------------------------------------------------------------------------- ---------I. Input watermarked audio file.
II. Divide Audio file in to finite blocks (15000 sample value/block taken)
III. Find DWT of selected block. ([da,db]=wavedec2(block)) and reform D matrix. [3]
IV. Process D matrix for SVD decomposition. ([U, Snew, V]=svd(D)].
V. Find Wn value based on Equation 3.1.
VI. Reshape Wn (1 x N) vector into Matrix Image for display. (both shares)
VII. Do Ex-Oring or Ex-Nor operation using both shares which reforms original image.
IV. Results And Discussion
Robustness and SNR value is calculated based on Equation 4.1 and 4.2 [3]
n
S N R ( d b ) 1 0 lo g 1 0
i 1
; A o r ig in a lA u d io , A ' W a te r m a r k e d A u d io
(A A )
'
(4.1)
i 1
WnWn'
i
i 1
(W n , W n ')
; W n O r ig in a lW a te r m a r k b it , W n ' E x tr a c te d B it
Wn
i 1
(4.2)
n
2
i
Wn'
2
i
i 1
For results and comparative analysis, we had considered so many attacks like ECHO, Cropping and Amplifying
on watermarked audio file. Table 4.1 shows comparative analysis of such attacks with robustness and SNR
values.
Table 4.1 Comparative analysis of Robustness value and SNR for Different attacks.
0 .1
0 .2
0 .3
Attacks
Cropping
Amplify
Echo
Bass Boost
AWGN Noise
Random Noise
= 1 , SNR= 76.7
=1, SNR= 78.9
= 0.95. SNR= 72.9
= 0.96, SNR= 73.2
= 1, SNR= 74.2
= 1, SNR= 70.1
= 1, SNR= 68.7
= 1. SNR= 78.9
= 0.95. SNR= 68.57
= 0.96. SNR= 68.86
= 1, SNR= 68.29
= 1, SNR= 67.69
= 1, SNR= 66.90
= 1, SNR= 65.29
= 0.95, SNR= 64.19
= 1, SNR= 64.11
= 1, SNR= 60.19
= 1, SNR= 62.45
4.1 Results
Fig. 4.1 Results of DWT-SVD based Audio watermarking image (VCS output) and Reconstruction
www.ijesi.org
64 | Page
DWT-SVD Based Visual Cryptography Scheme for Audio Watermarking
V. Conclusion
Digital Audio watermarking has its own advantages to protect copyright content on internet or elsewhere. Our
Aim in this proposed work is simply focused on defense system for military protected, surveillance area to
communicate in secured and safe manner. Hiding digital text / image data in audio file is more challenging as
audio file is vector format and image is matrix (array structure). In further security, we deploy
visualcryptography concept in DWT-SVD based robust method for perfect & secured communication system
for army. Beauty of this algorithm is one can send encrypted message via radio broadcasting without any special
military equipment. We have checked robustness and SNR value for all attacks with comparative analysis. In
future one can focus on improvement of visual cryptography algorithm along with DWT-SVD Algorithm.
References
Journal Papers:
[1]
[2]
[3]
[4]
[5]
[6]
F. Liu, C.K. Wu, X.J. Lin , Color visual cryptography schemes,IET Information Security, 2(4), 2008, 151 165.
Ali Al-Haj, An imperceptible and robust audio watermarking algorithm, EURASIP Journal on Audio, Speech, and Music
Processing (Springer journal), 2014.
Khalid A. Darabkh, Imperceptible and Robust DWT-SVD-Based Digital Audio Watermarking Algorithm, Journal of Software
Engineering and Applications, 7,2014, 859-871.
M. Naor and A. Shamir, Visual cryptography II: improving the contrast via the cover base, in "Security Protocols", M. Lomas, ed.,
Lecture Notes in Computer Science ,1189 ,1997,, 197-202.
K Bhat, I Sengupta, A Das, An adaptive audio watermarking based on the singular value decomposition in the wavelet domain.
Digital Signal Process. 20, 2010, 15471558.
M Hsieh, D Tseng, Y Huang, Hiding digital watermarks using multiresolution wavelet transform. IEEE Trans. Ind. Electron.m
48(5),2001, 875882.
www.ijesi.org
65 | Page
You might also like
- Defluoridation of Ground Water Using Corn Cobs PowderDocument4 pagesDefluoridation of Ground Water Using Corn Cobs PowdertheijesNo ratings yet
- Development of The Water Potential in River Estuary (Loloan) Based On Society For The Water Conservation in Saba Coastal Village, Gianyar RegencyDocument9 pagesDevelopment of The Water Potential in River Estuary (Loloan) Based On Society For The Water Conservation in Saba Coastal Village, Gianyar RegencytheijesNo ratings yet
- Mixed Model Analysis For OverdispersionDocument9 pagesMixed Model Analysis For OverdispersiontheijesNo ratings yet
- Design and Simulation of A Compact All-Optical Differentiator Based On Silicon Microring ResonatorDocument5 pagesDesign and Simulation of A Compact All-Optical Differentiator Based On Silicon Microring ResonatortheijesNo ratings yet
- Influence of Air-Fuel Mixtures and Gasoline - Cadoba Farinosa Forskk Bioethanol Fuel Mixtures On Emissions of A Spark - Ignition Engine.Document9 pagesInfluence of Air-Fuel Mixtures and Gasoline - Cadoba Farinosa Forskk Bioethanol Fuel Mixtures On Emissions of A Spark - Ignition Engine.theijesNo ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5795)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- New Phone Enrollment Process With Intune 3Document26 pagesNew Phone Enrollment Process With Intune 3Ré ChickNo ratings yet
- iOS Hacking: Advanced Pentest & Forensic TechniquesDocument60 pagesiOS Hacking: Advanced Pentest & Forensic TechniquesÖmer Coşkun100% (1)
- JustificationDocument8 pagesJustificationBiniyamNo ratings yet
- Cable Operating SystemDocument21 pagesCable Operating SystemBarry AllenNo ratings yet
- Laptop Policy - CernerDocument2 pagesLaptop Policy - Cernermamatha mamtaNo ratings yet
- Admit Card SSC JeDocument6 pagesAdmit Card SSC JePankaj ThakurNo ratings yet
- The Internet's Own Boy: A ReviewDocument3 pagesThe Internet's Own Boy: A ReviewHarshit LathiNo ratings yet
- Edmondson Claremore 2 9-23-14Document1 pageEdmondson Claremore 2 9-23-14Price LangNo ratings yet
- CHP 3Document3 pagesCHP 3rio octavianus yapieterNo ratings yet
- Blaster RemovalDocument3 pagesBlaster RemovalflorincrNo ratings yet
- Cyber Law Encompasses Laws Relating ToDocument4 pagesCyber Law Encompasses Laws Relating ToVaalu MuthuNo ratings yet
- Rank StateDocument1 pageRank StateMahipat BhuraniNo ratings yet
- Wod KeysDocument37 pagesWod Keysjlaczko2002No ratings yet
- More Examples of Interpreting Wait Events To Boost System PerformanceDocument122 pagesMore Examples of Interpreting Wait Events To Boost System PerformanceRagin ChittaliyaNo ratings yet
- Law Assignment 2Document10 pagesLaw Assignment 2KNEYINo ratings yet
- Les MisérablesDocument725 pagesLes MisérablesAnca Pop0% (1)
- HTZ4 Ammo For The Info WarriorDocument20 pagesHTZ4 Ammo For The Info WarrioremaNo ratings yet
- Imprivata Credential Provider WrappingDocument4 pagesImprivata Credential Provider Wrappingcruxv05No ratings yet
- Terence Claer CSS350 IP2Document10 pagesTerence Claer CSS350 IP2Terence ClaerNo ratings yet
- Fouriour SeriesDocument39 pagesFouriour SeriesHerberTNo ratings yet
- Cryptography and Network Security: Third Edition by William StallingsDocument27 pagesCryptography and Network Security: Third Edition by William StallingssantoshbjsNo ratings yet
- Loki 97Document22 pagesLoki 97Diego Durán100% (1)
- Theft of Pride by Jack Sharp (Andy Weir)Document155 pagesTheft of Pride by Jack Sharp (Andy Weir)Gerald Barahona AlbertiNo ratings yet
- Career in Cyber SecurityDocument2 pagesCareer in Cyber SecurityVipul KaushikNo ratings yet
- Edu303 Quiz 1Document3 pagesEdu303 Quiz 1Xia AlliaNo ratings yet
- Endeavor Usage Via MainframeDocument6 pagesEndeavor Usage Via MainframeNivinGovindanNo ratings yet
- Developing National Cybersecurity Strategy For EthiopiaDocument75 pagesDeveloping National Cybersecurity Strategy For Ethiopiaisrael100% (1)
- Chapter 8Document19 pagesChapter 8phillipNo ratings yet
- Password Cracking With Rainbow TablesDocument15 pagesPassword Cracking With Rainbow TablesFatima AljawhraNo ratings yet
- Factsheet IXGuard 3.1 EnglishDocument2 pagesFactsheet IXGuard 3.1 EnglishMada PerdhanaNo ratings yet