Professional Documents
Culture Documents
Practical E-Payment Scheme
Uploaded by
IJCSI EditorCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Practical E-Payment Scheme
Uploaded by
IJCSI EditorCopyright:
Available Formats
IJCSI International Journal of Computer Science Issues, Vol.
7, Issue 3, No 7, May 2010 18
ISSN (Online): 1694-0784
ISSN (Print): 1694-0814
Practical E-Payment Scheme
Mohammad Al-Fayoumi1, Sattar Aboud2 and Mustafa Al-Fayoumi3
1
Information Systems, Abdulaziz University
Jedda, KSA
2
Information Technology Advisor, Iraqi Council of Representative
Bagdad, Iraq
3
Computer Information Systems, Al-Zaytoonah University of Jordan
Amman, Jordan
Online payment: in which vendor checks the payment sent
Abstract by purchaser with a bank before serving the purchaser.
E-payment is now one of the most central research areas in e- Offline payment: in which over spending must be
commerce, mainly regarding online and offline payment detected, and consequently, no online link to the bank is
scenarios. Customers are generally passive in e-commerce needed.
transaction. Relied on a blind signature, this paper introduces an The e-payment schemes [1] can be sub-divided into two
e-payment protocol, in which customers have more initiative,
groups according to the online assumptions.
and can terminate the transaction before possible cheats, its
security is enhanced. Moreover, the cost of workers and Payments by transaction method: in which single
communications falls down considerably while the cost of payment does not need previous arrangements
trusted authority and protecting information is increased. As between purchaser and vendor.
there is no trusted authority in the proposed scheme, network Payments by account method: in which purchaser
overcrowding and conspiracy problems can be avoided. and vendor should have a system account with
Furthermore, the protocol satisfies fairness and non-repudiation. bank and certain type of agreement between both
This helps merchant and bank to speed up the financial before carrying out the real payment transaction.
transaction process and to give user instant services at any time.
The payment by transaction can further be divided into
Also, in this paper, we will discuss an important e-payment
protocol namely pay-word scheme and examine its advantages two subgroups.
and limitations, which encourages the authors to improve the The credit card payment transaction: is tailored
scheme that keeps all characteristics intact without compromise for a large charge payment of some hundreds or
of the security robustness. The suggested protocol employs the even thousands of dollars. In contrast, net money
idea of blind signature with the thought of hash chain. We will transaction is usually of low value payment with
compare the proposed protocol with pay-word protocol and difficult transaction cost and online features,
demonstrate that the proposed protocol offers more security and similar to the thought of the e-payment
efficiency, which makes the protocol workable for real world
transaction. The drawback of the credit card
services.
payment transaction is the fee of transactions,
Keywords: E-payment protocol, public key cryptography, blind
signature scheme, e-commerce.
particularly from the perspective of the vendor
who has to pay some invoices to the clearing
house according to the contract agreement with
1. Introduction them. This certainly will have direct impact on
the cost policy and the interest between the
With the increasing impact of intangible merchandise in possible users.
worldwide economies and their immediate delivery at The e-payment by small value transactions on
small cost, traditional payment systems tend to be more service: This is acquiring certain interest from the
costly than the modern one. Online processing can be of area of research. A number of important services
considerable value compared with the manual one. of e-payment are e-publishing and multimedia
However, there are two methods of running e-payment service. In these services, due to the small
systems. transaction amount, the merchant acquires
IJCSI International Journal of Computer Science Issues, Vol. 7, Issue 3, No 7, May 2010 19
www.IJCSI.org
relatively shopping mall revenue from every hash chain. We then proposed a blind signature scheme
transaction. that will be used in the protocol for reaching better
As a result, expensive calculations such as digital efficiency without conceding its security characteristics.
signature should be limited in order to reduce the Therefore, before discussing the rest of this paper, we will
investments in software applications. In recent years, e- list the notation used as follows.
payments [2, 3] offering a relatively key improvement in U: User
the online revenue malls. The foundation of e-payments is M: Merchant
to take benefit of the high level of viewers by presenting B:
content for a low price. Other alternative of this thought is Bank
to rating fractions of cents for equally fractional contents p: Prime number
sums. The main features in e-payment protocol are less m: Message
charges of payment amount and high occurrence of d: Private Key
transactions on the e-commerce system. g: A generator of multiplicative group
e: Expiry information for redemption
2. E-Payment Scheme Requirements h: Secure hash function
The e-payment protocol encompasses three participants
which are as follows: 3. Related Works
User: The user (customer) purchases e-currency from the
bank employing actual money by e-payment. The user can In 1988 Chaum, Fiat and Naor proposed their protocol
then utilize e-currency to carry out e-payment to buy entitled untraceable electronic cash [5] which relies on a
goods. single use token method. The user creates blinded e-bank
Merchant: The merchant is the data storage which currency note and passes it to the bank to be signed using
provides user with both services and information. bank public key. The bank signs the currency note,
Bank: The bank is the trusted authority. It mediates subtracts the value from the user account, and returns the
between user and merchant in order to ease the duties they signed currency note back to the user. The user removes
carry out. In general, the bank acts like a broker offering the blind thing and utilizes it to buy goods from the super
the e-coins for the e-payments. market. The super market checks the authenticity of the
While using e-currency, a shared set of characteristics for bank currency note using the bank public key and passes it
an e-payment protocol is: to the bank where it is verified contrary to a list of
Anonymity: e-cash must not supply any user with currency note already used. The amount is deposited into
information; it means that it must be anonymous e- the supermarket account, the deposit approved, and the
currency transaction. supermarket in turn emits the merchandise. In 1995,
Divisibility: e-cash can be sub-divided since the notes Glassman, Manasse, Abadi, Gauthier and Sobalvarro
have a basic piece. present their protocol entitled "The Millicent protocol for
Transference: e-cash can be transferred to a trusted inexpensive electronic commerce"[6] which is a
authority by providing the suitable amount of currency. decentralized e-payment protocol, and it allows payments
Over spending detection: e-cash must be used for only as low as 1/10 of a cent. It employs a type of e-coins. It is
once. introduced to make the cost of committing a fraud more
The e-payments are stored and then converted to digital than the cost of the real transaction. It utilizes asymmetric
type. This will cause new difficulties during developing encryption techniques for all information transactions.
secure e-payment protocol. The payment is simply Millicent is a lightweight and secure scheme for e-
duplicated against the conventional physical paying commerce through the internet. It is developed to support
methods. As the digital payment is characterized as simple buying goods charging less than a cent. It is relied on
sequences of bits, nothing in them stops them copying. decentralized validation of e-currency at the seller server
When a security of the payment protocol is reliant on the without any further communication, costly encryption, or
method the payments are hidden from the unknown. Every off-line processing. Also, in 1997, Rivest suggested his
individual that can have access to payments may utilize protocol entitled "Electronic lottery tickets as e-payments"
them numerous times. We notice that getting anonymous [7]. In this protocol there is a possibility to reduce the
cash transaction is an essential issue, and at the same time number of messages engaged with every transaction. Also,
giving efficiency is another matter. In this paper, we study the lottery ticket scheme is relied on the assumption that
a merchant pay-word protocol [4],that gives anonymity financial agents are risk-neutral and will be satisfied with
characteristic using the idea of blind signature scheme and fair wagers. In 1998, Foo and Boyd proposed another
protocol called "A payment scheme using vouchers" [8].
IJCSI International Journal of Computer Science Issues, Vol. 7, Issue 3, No 7, May 2010 20
www.IJCSI.org
The e-vouchers can be moveable but the direct exchange
between purchasers and vendors is impossible. As a result,
a financial agent is needed and this will raise the
transactions charges of exchange. However, during the last Customer (U)
decade several new e-payment protocols [9, 10] have been
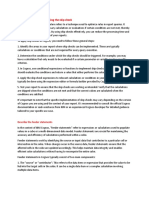
suggested. In this section, we will discuss pay-word CU=(IDS,IDU,AU,PKU,EU,IU)SKS MU=(IDM,CU,Wo,EC,IM)SKS
protocol which is an efficient and flexible protocol [4].
P = (Wi,i)
MU,P = (Wi,i)
4. The Pay-Word Protocol Bank (B) Merchant (M)
In 2001, Rivest and Shamir [4] introduced the pay-word
protocol, which is a credit-typed protocol. The protocol
employs RSA public key cryptography [11] and the idea
of hash chain [12]. In the pay-word protocol, if a
registered user U requests the merchant M for a service,
Fig. 1 Transaction operation of the pay-word protocol.
he should generate a pay-word chain that works as cash
made due to merchant M . The merchant M then must
Remarks: pay-word is developed as a credit-based scheme.
check if the user U is authorized and the pay-word cash
It takes benefit of hash chain to ensure time efficiency,
chain of the protocol is created by the user U . and reaches non-denial for every payment belonging to the
Afterward, the merchant M gathers user pay-word and same chain by just one signature. After receiving a
redeems the payment from the bank B . The pay-word certificate, a user is authorized to transact with a merchant
protocol decreases the number of on-line connections in a specified amount without online communication with
between bank B and merchant M , since the merchant the bank, provides the user more flexibility. However, the
M does not need to pay for each buy. The pay-word chain scheme suffers from the following limitations.
creation with size n and can be stated as xi h( xi 1) , First, the pay-word is a merchant specific
such that i n 1, n 2,..., 0 . If creating the pay-word, the payment scheme, so users have to preserve set of
user U chooses an arbitrary number xn , named a seed, and specific information of chains corresponding to
distinct merchants.
then xn is hashed iteratively in reverse order until the root
Second, the user has to carry out hash chain
of the chain x0 is created. Throughout shopping, the processes as many as the number of merchants
user U in order from x1 to xn releases pay-word, and the every time he needs to perform business with.
merchant M checks it simply by hash process. Third the user has to keep all the different pay-
Pay-word is a merchant M certain payment protocol, words of every merchant and the last index used
namely the pay-word chain is spent only to a specific for the transactions.
merchant M . If a user U contacts a new merchant M for Fourth, the user could make payments exceeding
ordering service, besides making a new chain, the user U his authorized credit limit.
should pass a commitment to merchant M . The
commitment includes the identity of the merchant M , the
certificate published by the bank B , the root of an unused
5. The Proposed Protocol
chain, the present date and other information. To
This paper is introduced an efficient protocol, and make a
implement continuous transactions, the user U pays pay-
simple comparison between the proposed protocol and the
word within the chain which belongs to the merchant M . above described pay-word protocol. Also, gauging the
Following a suitable time, the merchant M will contact efficiency and security of the protocol will take place in
with the bank B to order redemption. For every chain, the section 6. However, any such protocol should contain at
merchant M passes the newest pay-word he received and least four schemes, registration scheme, blind signature
the user U commitment to the bank B ; so, hashing from scheme, transaction scheme, and redemption scheme. The
newest pay-word to the root of the chain can validate the proposed protocol adopts the same procedures of the pay-
rightness of transactions. When the validating is correct, word scheme except the blind signature scheme. Thus, in
the bank B debits user U account with the used size of the this section, we will introduce a new blind signature
chain and credits merchant M account with the same scheme using discrete logarithm problem [13]. We will
amount. We show the transaction operation of the pay- show this improvement makes the pay-word protocol more
word protocol in Figure 1. efficient and keeps all other characteristics balanced.
IJCSI International Journal of Computer Science Issues, Vol. 7, Issue 3, No 7, May 2010 21
www.IJCSI.org
5.1 Blind Scheme Find the public key y g modp 2 mod113 14
d 11
1.4.
The user gives a withdrawal request to the bank before his 1.5. Determine the public key ( p 113, g 2, y 14)
order for some service from merchant. The steps of the and private key (d 11)
scheme are as follows: 1.6. Suppose z 7
Step 1: Bank 1.7. Send z 7 to the user
1.1. Generate an arbitrarily prime number p Step 2: User
1.2. Select a generator g of the multiplicative of group 2.1. Assume v 10 and u 17
Z *p 2.2. Find f v y * h ( m )( u 2 1) mod p
1.3. Pick the private key d such that 1 d p 2 1014 * h(8)(17 2 1) mod 113
1.4. Finds the public key y g d mod p 1014 * h(8)(290) mod 113
1.5. Determine the public key ( p, g , y) and private 41
2.3. Send (e 6, f 41) to the bank. Where e
key (d )
represents an upper limit of cash that the user can use.
1.6. Pick a random number z p 2
2.4. Suppose c 15
1.7. Send z to the user 2.5. Finds k v * c 10 * 15 mod 113 37
Step 2: User 2.6. Finds a ( k ) y * ( u z ) mod p
2.1. Pick a random integers v and u 3714 * (17 7) mod 113
2.2. Finds f v * h ( m )( u
y 2
1) mod p 12
2.3. Send (e, f ) to the bank, where e represents an 2.7. Pass a 12 to the bank
upper limit of cash that the user can use. Step 3: Bank
2.4. Pick an arbitrary integer c
2.5. Finds k v * c mod p 3.1. Find a 1 mod p
2.6. Pass a ( k ) y * ( u z ) mod p to the bank 12 1 mod 113
12 * 66 mod113 1
2 2 * d
Step 3: Bank Finds j h (e) * ( f ( z 1) * a )
d 2
3.2. mod p
3.1. Finds a 1 mod p
2 2 * d h(6)11 * (41(7 2 1) * 12 2 ) 2*11 mod 113
Finds j h ( e ) * ( f ( z 1) * a )
d 2
3.2. mod p
h(6)11 * (41 * 50 * 62) 22 mod 113
3.3. Pass ( a 1 , j ) to the user
h(362797056 ) * (127100) 22 mod 113
Step 4: User 19
4.1. Finds 3.3. Pass ( a 1 , j ) ( 66 ,19 ) to the user
w (u * z 1) * a 1 * ( k ) y (u * z 1)(u z ) 1 mod p
4.2. Finds x j * v 2 * ( c ) 4 mod p
The parameter (e, w, x) is the signature on message m . Step 4: User
However, one entity can verify this signature by checking
4.1. Finds
whether x y ( j * v 2 * (c) 4 ) y mod p
w (u * z 1) * a 1 * ( k ) y (u * z 1)(u z ) 1 mod p
5.2 Example (17 * 7 1) * 66 * (37)14 (17 * 7 1)(17 7) 1 mod 113
12 (17 * 7 1)(10) 1 mod 113
Step 1: Bank
12 (120)(34) mod 113
1.1. Suppose p 113
12 12
1.2. Assume a generator g 2
4.2. Finds x j * v 2 * ( c ) 4 mod p
1.3. Suppose the private key d 11
IJCSI International Journal of Computer Science Issues, Vol. 7, Issue 3, No 7, May 2010 22
www.IJCSI.org
19 * 10 2 * (15) 4 mod 113 The pay-word protocol 5 * Th 9 * Ta 5 * Tm
19 * 100 * 50625 mod 113 Proposed protocol 4 * Th 8 * Ta 4 * Tm
92
The parameter (e 6, w 12, x 92) is the signature on Actually, the modular exponentiation is a costly operation
message m . However, one entity can verify this signature in comparison with addition or hash function operations.
As a result it is simple to observe from Table 1 that the
by checking whether x y ( j * v 2 * (c) 4 ) y mod p
proposed protocol is more efficient than the pay-word
9214 (19 * 10 2 *15 4 )14 mod 113 protocol. Furthermore, when any entity computes and
obtains small public key y , then the proposed protocol
18 (19 * 100 * 50625)14 mod 113
18 18 becomes more efficient. This makes public key operations
quicker while the secret key operations remaining
5.3 Forgery Detection unchanged. In this case, when an entity uses the short
public key attack, he cannot succeed with this try since
The user U gets the bank B signature on m prior to any every signature is being randomized by certain random
transaction. But, in order to process an accurate numbers. So, the proposed protocol decreases expensive
redemption, the merchant M should have information of exponential operation and has better time efficiency.
the payment transaction. It is almost unfeasible for any
entity to forge the user U payment without knowing the
6. Conclusion
private key d . Thus, the opponent cannot forge signature.
But to successfully achieve the verification of the In this paper, we described the characteristics of e-
formula x y ( j * v 2 * (c) 4 ) y mod p , an opponent has to payment protocol and evaluated one of the most important
calculate x where x j * v 2 * ( c ) 4 mod p provided e-payment protocols that relied on a hash chain. The hash
chain typed scheme gives anonymity security
the results of h(e) , h ( m ) and w . However, it is characteristic besides other security features of e-payment
computationally intractable to obtain the value of protocol. The use of the blind signature scheme and hash
d without solving the discrete logarithm that is hard to function makes the protocol more efficient and guarantees
solve such a problem. Thus, the opponent is unable to the payment untraceable. Though, we notice that the blind
forge the signature. scheme of the protocol takes significantly more computing
time and we present an alternate blind scheme using the
5.4 Efficiency discrete logarithm that gives more efficiency than the
existed protocol. The research accomplished in this paper
In the e-payment protocol, the profit acquired by a has vast future prospects and can be extended towards a
merchant is little in every transaction. It is unwise to check substantial protocol using hash function so that the
the transaction employing a complicated technique that modular exponentiation and costly operation can be
leads the average cost of the protocol more than the profit. avoided and also security depth can be reached.
On the other hand, large calculation in e-payment is not
wise. In order to gauge efficiency of the proposed
References
protocol, we compare the enhanced blind scheme with the [1] A.Tiwari, S. Sanyal, A. Abraham, J. Knapskog, and S.
pay-word scheme [4]. The time complexity of the Sanyal, "A Multi-factor Security Protocol for Wireless
remaining scheme stays the same in both protocols. We Payment-Secure Web Authentication Using Mobile
employ the following notation to gauge the efficiency of Devices", IADIS International Conference Applied
the schemes. Computing, 2007, pp.160-167.
Th : Calculation time for hash function operation [2] S. van, A. Odlyzko, and R. Rivest, T. Jones and D. Scot,
"Does anyone really need micropayments", proceeding of the
Ta : Calculation time for addition in modular International Conference of Financial Cryptography, LNCS
multiplication 2742, Springer, 2003, pp. 69-76.
Tm : Calculation time for multiplication modular [3] L. Jun, L. Jianxin, and Z. Xiaomin, "A System Model and
Protocol for Mobile Payment", Proceedings of the IEEE
exponentiation International Conference one-Business Engineering
(ICEBE05), 2005.
Table 1: Computations of efficacy in blinding scheme [4] R. Rivest, and A. Shamir, "Pay-word and MicroMint: Two
simple micropayment schemes", International Journal of
Protocol Name Blinding Scheme Network Security, Vol. 2, No. 2, 2001, pp. 81-90.
IJCSI International Journal of Computer Science Issues, Vol. 7, Issue 3, No 7, May 2010 23
www.IJCSI.org
[5] D. Chaum, Fiat, and M. Naor, "Untraceable electronic cash", from U.K. In 1990, he joined the institute of technical foundation,
Proceeding Advances in Cryptology, LNCS 403, Springer, in Iraq as an assistant professor and a head of computer system
1988, pp. 319-327. department. In 1993 he moved to Arab University College for
science and technology in Iraq as an associate professor and a
[6] M. Hwang, and P. Sung, "A study of micro-payment based dean deputy. In 1995 he joined the Philadelphia University in
on one-way hash chain", International Journal of Network Jordan as an associate professor and a chairman of computer
Security, Vol. 2, No. 2, 2006, pp 81-90. science and information system department. In 2004 he moved to
[7] R. Rivest, "Electronic lottery tickets as micropayments", the Amman Arab University for graduate studies, graduate college
Proceeding of the International Conference of Financial for computing studies as a professor. Then he moved to the
Cryptography, LNCS 1318, Springer, 1997, pp. 307314. department of computer information systems at the Middle East
University for graduate studies, Amman-Jordan as a professor.
[8] E. Foo, and C. Boyd, "A payment scheme using vouchers",
Currently, he is a advisor of information technology of the Iraqi
Proceeding of the International Conference of Financial Council of Representatives His research interests include areas
Cryptography, LNCS 1465, Springer, 1998, pp. 103-121. like public key cryptography, digital signatures, identification and
[9] M. Baddeley, "Using e-cash in the new economy: An authentication, software piracy, networks security, data base
economic analysis of micro-payment systems", security, e-commerce and e-learning security and algorithm
analyzes and design. He has supervised many PhD's and
Journal of Electronic Commerce Research, Vol. 5, masters degrees research thesis and projects of diverse areas.
No. 4, 2004. He has published more than 70 research papers in a multitude of
[10] J. Tellez, and J.Sierra, "Anonymous Payment in a Client international journals and conferences.
Centric Model for Digital Ecosystem", IEEE DEST, 2007,
pp. 422-427, Mustafa A. Al-Fayoumi received the
[11] R.Rivest, A. Shamir, and L. Adleman, "A Method for B.S. degree in computer science from
obtaining digital signatures and public-key cryptosystems", Yarmouk University, Irbid, Jordan, in
1988. He received the M.S. degree in
Communications of the ACM, Vol. 21, No. 2, 1978, pp. computer science from the University of
120-126. Jordan, Amman, Jordan, in 2003. In
[12] D.Stinson, Cryptography: Theory and Practice, CRT 2009, he received a Ph.D. degree in
Press, 2006. computer science from the Faculty of
[13] M. Al-Fayoumi, and S.J. Aboud, "Blind Decryption and Science and Technology at Anglia
Ruskin University, UK. In 2009, he joined
Privacy Protection", American Journal of Applied the Al-Zaytoonah University of Jordan, in
Sciences, Science Publications Vol.2, No. 4, 2005, pp. 873- Jordan, as an assistant professor. His research interests include
876. areas like computer Security, cryptography, identification and
authentication, Wireless and mobile Networks security, e-
application security, simulation and modeling, algorithm analyzes
and design, information retrieval and any other topics related to
Mohammad Al-Fayoumi received his
them. He has published about 10 research papers an international
B.S. degree in 1974. In 1977, he earned
journals and conferences.
his Master degree in mathematics, and a
postgraduate diploma in computer
science was received in 1979. A Ph.D.
was received in 1982 in the area of
computing science. The last two degrees
were awarded from Bucharest
University; he joined the Yarmouk
University, 1982 in Jordan, as an assistant professor and a head
of computer science department. In 1986 he moved to collage of
business studies in Kuwait and then moved back to Jordan in
Applied Science University as associate professor and a head of
computer science department. In 2005 he moved to the Middle
East University for Graduate Studies in Jordan as an associate
professor and a dean of information technology faculty, he
promoted to a professor rank in August, 2008. Currently, he is a
professor and advisor of graduate studies at the King Abdulaziz
University, Saudi Arabia. His research interests include areas of
information security, computer simulation, systems development,
e-commerce, e-learning and internet security and algorithm
analyzes and design. He has supervised many PhD's and
masters degrees research thesis and projects of diverse areas.
He has published more than 40 research papers in a multitude of
international journals and conferences, in addition to a nine books
in the area of computer sciences.
Sattar J. Aboud received his B.S.
degree in 1976. In 1982, he earned his
Master degree. A Ph.D. was received in
1988. The last two degrees in the area of
computing science and were awarded
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 6 - November 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 6 - November 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 6 - November 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 6 - November 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- A New Semantic Similarity Metric For Solving Sparse Data Problem in Ontology Based Information Retrieval SystemDocument9 pagesA New Semantic Similarity Metric For Solving Sparse Data Problem in Ontology Based Information Retrieval SystemIJCSI EditorNo ratings yet
- Efficient Algorithm For Redundant Reader Elimination in Wireless RFID NetworksDocument8 pagesEfficient Algorithm For Redundant Reader Elimination in Wireless RFID NetworksIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 9, Issue 4 - July 2012 IssueIJCSI EditorNo ratings yet
- A Situational Approach For Web Applications DesignDocument15 pagesA Situational Approach For Web Applications DesignIJCSI EditorNo ratings yet
- CALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 7, Issue 6 - November 2010 IssueDocument1 pageCALL FOR PAPERS International Journal of Computer Science Issues (IJCSI) - Volume 7, Issue 6 - November 2010 IssueIJCSI EditorNo ratings yet
- The Morphological Analysis of Arabic Verbs by Using The Surface PatternsDocument4 pagesThe Morphological Analysis of Arabic Verbs by Using The Surface PatternsIJCSI EditorNo ratings yet
- Real-Time Video Streaming Over Bluetooth Network Between Two Mobile NodesDocument3 pagesReal-Time Video Streaming Over Bluetooth Network Between Two Mobile NodesIJCSI EditorNo ratings yet
- Modeling Throughput Performance in 802.11 WLANDocument7 pagesModeling Throughput Performance in 802.11 WLANIJCSI EditorNo ratings yet
- Faster and Efficient Web Crawling With Parallel Migrating Web CrawlerDocument5 pagesFaster and Efficient Web Crawling With Parallel Migrating Web CrawlerIJCSI EditorNo ratings yet
- Performance Evaluation of Two Reactive Routing Protocols of MANET Using Group Mobility ModelDocument6 pagesPerformance Evaluation of Two Reactive Routing Protocols of MANET Using Group Mobility ModelIJCSI EditorNo ratings yet
- On One Approach To Scientific CAD/CAE Software Developing ProcessDocument7 pagesOn One Approach To Scientific CAD/CAE Software Developing ProcessIJCSI EditorNo ratings yet
- Hello Flood Attack and Its Countermeasures in Wireless Sensor NetworksDocument5 pagesHello Flood Attack and Its Countermeasures in Wireless Sensor NetworksIJCSI EditorNo ratings yet
- Policy Based Decentralized Group Key Security For Mobile Ad-Hoc NetworksDocument6 pagesPolicy Based Decentralized Group Key Security For Mobile Ad-Hoc NetworksIJCSI EditorNo ratings yet
- Image Compression Algorithms For Fingerprint SystemDocument6 pagesImage Compression Algorithms For Fingerprint SystemIJCSI EditorNo ratings yet
- A Theoretical Approach To Link Mining For PersonalizationDocument4 pagesA Theoretical Approach To Link Mining For PersonalizationIJCSI EditorNo ratings yet
- Quotient Based Multiresolution Image Fusion of Thermal and Visual Images Using Daubechies Wavelet Transform For Human Face RecognitionDocument10 pagesQuotient Based Multiresolution Image Fusion of Thermal and Visual Images Using Daubechies Wavelet Transform For Human Face RecognitionIJCSI EditorNo ratings yet
- Extraction of Dominant Attributes and Guidance Rules For Scholastic Achievement Using Rough Set Theory in Data MiningDocument10 pagesExtraction of Dominant Attributes and Guidance Rules For Scholastic Achievement Using Rough Set Theory in Data MiningIJCSI EditorNo ratings yet
- Fast Clustering of Self-Similar Network Traffic Using WaveletDocument8 pagesFast Clustering of Self-Similar Network Traffic Using WaveletIJCSI EditorNo ratings yet
- Music Sound and Picture Perception: Topography of The Human Brain Electrical ActivityDocument9 pagesMusic Sound and Picture Perception: Topography of The Human Brain Electrical ActivityIJCSI EditorNo ratings yet
- Non Linear Image Segmentation Using Fuzzy C Means Clustering Method With Thresholding For Underwater ImagesDocument6 pagesNon Linear Image Segmentation Using Fuzzy C Means Clustering Method With Thresholding For Underwater ImagesIJCSI EditorNo ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Infosys - Phase 2 Selected & Eligible For Internship-SrmDocument4 pagesInfosys - Phase 2 Selected & Eligible For Internship-SrmhabersNo ratings yet
- Solution For Exam 4Document6 pagesSolution For Exam 4Mauricio FloresNo ratings yet
- Euphoria User ManualDocument795 pagesEuphoria User ManualUnknown0200% (1)
- HDL Designer Series Release NotesDocument32 pagesHDL Designer Series Release NotesdupipiNo ratings yet
- Smart Card ReadersDocument16 pagesSmart Card ReadersNareshNvNo ratings yet
- Arm Cortex M7 Processor DatasheetDocument12 pagesArm Cortex M7 Processor DatasheetAlfonso Hernández MagdalenoNo ratings yet
- Proposal For Ecommerce WebsiteDocument3 pagesProposal For Ecommerce WebsitejayNo ratings yet
- Vehicle Breakdown Assistance Management SystemDocument52 pagesVehicle Breakdown Assistance Management SystemSohum Patel100% (1)
- Ses DGDocument208 pagesSes DGMrChwet AumNo ratings yet
- Compiler-Lexical AnalysisDocument59 pagesCompiler-Lexical Analysisvidhya_bineesh100% (1)
- 11.7.2.1 Common Problems and Solutions For Windows Operating SystemsDocument5 pages11.7.2.1 Common Problems and Solutions For Windows Operating SystemsgiorgiNo ratings yet
- E-Billing Project ReportDocument102 pagesE-Billing Project Reportselvam427475% (4)
- Karsten NohlDocument28 pagesKarsten NohlandpikNo ratings yet
- Palo Alto Networks Security Best Practices ChecklistDocument12 pagesPalo Alto Networks Security Best Practices ChecklistKaushal KishorNo ratings yet
- Fall 2020 - Cloud Computing and Big Data - HW 1Document7 pagesFall 2020 - Cloud Computing and Big Data - HW 1rahulNo ratings yet
- 3rd Week AssignmentDocument2 pages3rd Week AssignmentAfdal Luthfi100% (1)
- Intro To CUDADocument76 pagesIntro To CUDADisinlung Kamei DisinlungNo ratings yet
- Installing Thermo GC Devices 3.0Document3 pagesInstalling Thermo GC Devices 3.0stemman95No ratings yet
- Instructions-Simple (Suitable For AHD-DVRíóSDI-DVRíóEDVRúDocument9 pagesInstructions-Simple (Suitable For AHD-DVRíóSDI-DVRíóEDVRúAnonymous i8RqffNo ratings yet
- Artificial Intelligence and Machine Learning: Visvesvaraya Technological University, BelagaviDocument50 pagesArtificial Intelligence and Machine Learning: Visvesvaraya Technological University, BelagaviAddy RaoNo ratings yet
- Automesh 4gtm PDFDocument8 pagesAutomesh 4gtm PDFFrancis LinNo ratings yet
- HD-VP210A Specification v3.2Document7 pagesHD-VP210A Specification v3.2Rudy Quispe CcenteNo ratings yet
- Seqrite EPS Cloud GuideDocument104 pagesSeqrite EPS Cloud Guidert1220011No ratings yet
- Maris Navico Manuals ECDIS900 Users Guide Rel LDocument309 pagesMaris Navico Manuals ECDIS900 Users Guide Rel LAdi PrasetyoNo ratings yet
- M4 - Socio Cyber InformaticsDocument27 pagesM4 - Socio Cyber InformaticsIt's meNo ratings yet
- User Manual: FP-3500T/3600T/3650T SeriesDocument95 pagesUser Manual: FP-3500T/3600T/3650T SeriesNafian PratamaNo ratings yet
- WORK CYCLE 7.2 Web Application Configuration GuideDocument132 pagesWORK CYCLE 7.2 Web Application Configuration GuideTANGNo ratings yet
- Design and Analysis of Algorithm LaboratoryDocument32 pagesDesign and Analysis of Algorithm Laboratorysyed adilNo ratings yet
- 2 & 5 MarksDocument25 pages2 & 5 MarksSamarth PhutelaNo ratings yet
- Java Training AssignmentsDocument11 pagesJava Training AssignmentsTushar Gupta100% (1)