Professional Documents
Culture Documents
RPT World Eco Forum PDF
Uploaded by
Salahddin KhalilOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
RPT World Eco Forum PDF
Uploaded by
Salahddin KhalilCopyright:
Available Formats
2017
FIREEYE | MARSH & MCLENNAN CYBER RISK REPORT
CYBER
THREATS:
A perfect storm
about to hit Europe?
S P ECIAL R E P O RT / JAN UARY 2017
CONTENTS
Executive summary 3
The dramatically changing cyber threat landscape in Europe 5
The regulatory environment in Europe is about to change and profoundly 15
Cyber preparedness in Europe is improving,
but the journey has just begun 19
How can companies brace for the storm? 20
A call to action 23
2 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
Executive
summary
Cyber storm clouds are gathering over Europe Third, these two developments beg the question of how
on three fronts. prepared businesses are across Europe. To assess their state
First and foremost, the cyber threat environment is intensifying of preparedness, Marsh conducted a broad survey of 750
dramatically. Concerns about the misappropriation of financial European clients. The responses suggest that, while progress
and personal data while important have been supplanted has been made, a significant journey remains. If, as we
by the spectre of an even larger and more devastating threat. anticipate, cyber breaches begin to fill the headlines of the
Cyber attacks on critical infrastructure manufacturing plants, major European newspapers in 2017, management teams will
power stations, aviation systems, transportation networks, water be pressed, as never before, to address concerns from data
systems and even nuclear facilities are the new reality in protection authorities, supervisory boards and journalists about
Europe. And new vectors of attack are being launched against their state of preparedness. Rather than waiting until 2018,
political parties and electoral systems as national elections loom companies must work to confront this looming challenge now.
in France, Germany and the Netherlands in 2017.
As trusted cyber advisers, FireEye and Marsh & McLennan
Second, while this dynamic is unfolding, the regulatory each a leader in its industry have collaborated to produce this
environment in Europe is about to change profoundly. The report to help organizations in Europe avoid this perfect storm.
European Union has adopted a sweeping General Data
Protection Regulation (GDPR) that will impose significant new
obligations on industry and its handling of personal data. The
Rapporteur assigned by the European Parliament to lead the
final negotiations on the EU GDPR, Jan Albrecht, announced
upon its passage in the summer of 2016: The GDPR will Kevin Mandia Peter J. Beshar
Chief Executive Officer Executive Vice President
change not only the European Data protection laws but FireEye and General Counsel
nothing less than the whole world as we know it. Marsh & McLennan Companies, Inc.
...management teams will be pressed, as never
before, to address concerns from data protection
authorities, supervisory boards and journalists
about their state of preparedness.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 3
4 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
The dramatically
changing cyber
threat landscape
in Europe
Europe is being forced to confront a growing cyber
threat against physical assets. Hackers and purportedly
nation states are increasingly targeting industrial
control systems and networks power grids, chemical
plants, aviation systems, transportation networks,
telecommunications systems, financial networks and
even nuclear facilities.
In late 2014, the German Federal Office for In October 2016, the head of the International
Information Security (BSI) reported that a cyber Atomic Energy Agency at the United Nations,
attack had caused massive damage to a German Yukiya Amano, publicly disclosed for the first time
iron plant. Utilizing a combination of spear phishing that a disruptive cyber attack had been launched
and social engineering, hackers gained access to against a nuclear facility in Germany. This report
the iron plants office network, moved laterally to came on the heels of an analysis by the Nuclear
control the production network and then disabled Threat Initiative warning of lax cyber security at
the shut-off valves on the plants blast furnaces. In nuclear facilities in a number of countries across
the parlance of the industry, this was a kinetic or Europe.
physical attack against hard assets.
Thus, cyber attacks against critical infrastructure,
In late 2015, hackers turned their focus to the dubbed a potential Cyber Pearl Harbor by US
power industry. In one of the largest attacks of military officials, are no longer the fantasies of
its kind, hackers shut off the power to hundreds Hollywood producers, conspiracy theorists or sci-fi
of thousands of residents in Ukraine. According aficionados, but are the reality that governments
to public reports, the attacks that caused the and businesses across Europe must now confront.
power outage were accompanied by parallel
cyber intrusions into Ukraines train system and
TV stations.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 5
What EU countries are being targeted
with the greatest frequency?
Cyber hackers are increasingly opportunistic
smart, savvy, and innovative. Hackers are bypassing
traditional defenses by continually engineering new
methods of attack. Even sophisticated cybersecurity
programs are being thwarted, often by targeting weak
links in the chain, including vendors and employees.
Due to its advanced economies and important
geopolitical positioning, Europe is a prime target for
these attacks.
6 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
In 2016, hackers most often targeted
financial, manufacturing, telecom
industries and governments in Germany,
Great Britain, Belgium, Spain, Denmark,
Sweden, Norway and Finland.
CZECH REPUBLIC
DENMARK
HUNGARY
FRANCE
NORWAY
FINLAND 1%
4% 5%
ITALY 4%
4% SWITZERLAND
3%
7% 2% AUSTRIA
4%
SWEDEN POLAND 1%
6%
SPAIN
12% 19%
GERMANY
12%
16%
GREAT BRITAIN
BELGIUM
Figure 1. Illustrates targeted malware detections from January 2016 to September 2016
Targeting of EU countries
Europes largest economies remain the top targets, but the focus Had Turkey been included, it would far overshadow the EU nations
ranges broadly across the continent. Figure 1 shows targeted represented. Turkey accounted for a whopping 77 percent of all
malware detections from January to September 2016 for all EU targeted malware detections by FireEye in Europe.
nations except Turkey and Russia. (Nations not represented on
this chart received little or no malware assessments from FireEye.)
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 7
Germany powerfully demonstrates the changing What specific industries are being targeted
cyber environment. Last month, Thyssen Krupp, a and how?
large German industrial conglomerate, disclosed The vertical industry analysis below reveals which
that technical trade secrets were stolen in a cyber sectors are being targeted with the greatest
attack that dated back almost a year. The company frequency. The three industries that draw the greatest
filed a criminal complaint with the German State attention in Europe are:
Office for Criminal Investigation and stated publicly,
It is currently virtually impossible to provide viable Financial services
protection against organized, highly professional Manufacturing
hacking attacks. Telecommunications
The type of data being stolen in these attacks is In the third quarter of 2016, threats accelerated
particularly revealing. While sensitive personal in particular against manufacturers and telecom
information like financial or health records remains a operators. Conversely, retailers, a key focus of cyber
key focus, hackers are increasingly targeting higher attacks in the United States, are virtually at the
value data relating to infrastructure systems. Based bottom of the list in Europe.
on FireEyes research, 18 percent of the data that
was exfiltrated through cyber attacks in Europe In addition, governments are a primary target for
in 2016 related to companies industrial control hackers across Europe. Indeed, aggregating attacks
systems, building schematics and blueprints, while a against national, state and local governments into a
further 19 percent related to trade secrets. single category makes government the number one
target in Europe.
The federated nature of Europe also increases the
potential cyber risk across the continent. Each EU To date, there has been an underreporting of cyber
member state has a different cybersecurity maturity. incidents in the EU. Nonetheless, a handful of
As more and more components of infrastructure public reports reveal significant cyber incidents
are connected to the Internet and the Internet of across the continent. In 2016, cyber hackers stole
Things explodes in popularity, certain countries more than $75 million from a Belgian bank and $50
within Europe may lack the capabilities needed to million from an Austrian aircraft parts manufacturer
assess and implement a sophisticated cybersecurity through fraudulent emails mimicking legitimate
framework to defend against these emerging communications to fool companies into transferring
threats. As a result, hackers can take advantage of money to a hackers account.
the disparate architecture across the EU.
In sum, no sector of the economy is immune from
attack not industry, not government and not
even the not-for-profit sector. Accordingly, we need
a mindset, particularly between government and
industry, that we are all in this together.
8 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
Figure 2. Targeted malware detection across Europe during January - September 2016
60
45
Number of Events
30
15
0
Energy Entertainment Financial Government High-Tech Insurance Manufacturing Retail Service Services Telecom Transportation
Utilities Media Services Federal Provider Consulting
Hospitality
Q1 2016 Q2 2016 Q3 2016
...no sector of the economy is immune from attack not industry,
not government and not even the not-for-profit sector.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 9
DWELL TIME UNTIL Companies in Europe take 3x longer to So, what can be done to reduce the average
A COMPROMISE IS detect cyber intrusions dwell times?
DETECTED
FireEye found that companies in the European Unlike in the United States and other parts of
469
Union take three times longer than the global the world, it is quite rare in Europe for external
average to detect a cyber intrusion. The actors, including government agencies, to
regions mean dwell time the time between notify a company that its systems have been
compromise and detection was 469 days, breached. In fact, companies in Europe learn
DAYS IN EUROPE
versus a global average of 146 days. of breaches in their systems from external
146
parties only 12 percent of the time. This lack
The delay in identifying intrusions has profound of external notifications could also allow for
consequences. At a basic level, the notion speculation that a large number of intrusions
that hackers are rooting around in companies remain undiscovered.
DAYS networks undetected for 15 months is sobering,
GLOBAL AVERAGE as it allows ample opportunity for lateral By contrast, this has become fairly
movement within IT environments. commonplace in the US. As a result of outreach
by the Federal Bureau of Investigation, the
Equally important, dwell times of this length Secret Service and cybersecurity companies,
allow hackers the opportunity to develop more than half of all US companies (53 percent)
multiple entry and exit doors. When a learned that their information systems had
company does detect an intrusion, the natural been hacked by external parties.
first impulse is to shut down its system to stop
SOURCE OF the bleeding. Numerous stakeholders then This is a critical place where governments can
DISCOVERING press the organization and its management help enhance the cyber resilience of industry
COMPROMISES:
EMEA VS. USA team to get back online and operating. by sharing threat and actual breach intelligence
in real time. This type of cooperation from
12%
In this dynamic, FireEye has found that hackers national governments and organizations
compromised many organizations in Europe like Europol and sector specific information
a second time within months of the initial sharing & analysis centres (ISACs) will reduce
breach. Repeated breaches most often result average dwell times and thereby bolster cyber
EXTERNAL DISCOVERY from the use of unsuitable techniques to hunt resilience across the continent.
IN EMEA
initially for attacks within their environment.
Many companies still opt for a traditional
53%
forensic methodology, only analyzing a handful
of machines or systems. On average, however,
hackers in Europe have infected approximately
40 different machines in any given company
EXTERNAL DISCOVERY during the length of their cyber intrusions.
IN USA
10 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
How are motives and tactics changing? In December, the focus shifted to France. Frances
Hackers come in many forms and differing degrees of National Cybersecurity Agency, known as the ANSSI,
sophistication. In addition to attacks against critical summoned representatives of all political parties to
infrastructure, EU cyber threats are dominated by a detailed cyber briefing about the threat posed by
two distinct groups: hackers with political goals and cyber attacks.
hackers with financial motives.
Prior to the recent attacks in the US, few would have
considered political parties and voting machines as
Is politically motivated hacking on the rise? part of a nations critical infrastructure. With national
In 2016, FireEye observed numerous nation-state or elections looming in the Netherlands (March 2017),
nation-sponsored intrusions against EU governments, France (May 2017) and Germany (late 2017), however,
and specifically against foreign or defense ministries the risk posed to the integrity of the electoral process
of member states. Recently, nation-state sponsored is all too real.
threat actors have shown strong interest in extending
these attacks into the political arena.
In September 2016, politicians and employees of ... the notion that hackers are rooting
political parties in Germany were targeted with a
series of spear phishing e-mails, purportedly from around in companies networks
NATO headquarters, regarding a failed coup in Turkey
and the earthquakes that hit Italys Amatrice region. undetected for 15 months is sobering,
The links to these spurious e-mails contained malware.
Arne Schoenbohm, the head of the German BSI, as it allows ample opportunity
responded swiftly by warning political parties across
the spectrum in Germany that the country needed
for lateral movement within IT
to learn the lessons from the recent elections in the
United States.
environments.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 11
As more criminals successfully carry
out ransomware attacks, others are
enticed to try this growing type of
malware attack.
Criminal hackers still a dangerous threat
Cyber criminals continue to target organizations and private citizens
across Europe to steal information, stage cyber extortion attacks, and
steal money through fraudulent transactions.
The use of ransomware spiked significantly in 2016. Victims are
asked to pay a ransom in the form of bitcoins. Utilizing malware with
names like Cryptolocker, TorLocker and Teslacrypt, hackers encrypt
your files and then demand a ransom to unlock them. In one recent
example, a ransomware variant called Locky targeted users in more
than 50 countries many of them in Europe. Locky utilized exploit kits
and mass e-mailing campaigns, often seen with spam. The campaign
enticed recipients to open e-mail attachments that appeared to be
invoices but instead contained malware. Victims are asked to pay the
This is not a message that you want ransom to obtain a decryption key that will then unlock their systems.
to see on your network. As more criminals successfully carry out ransomware attacks, others
are enticed to try this growing type of malware attack. This form of
attack has been particularly prevalent in the health care space, with
one report contending that 88 percent of ransomware attacks target
the healthcare industry.1
1 Solutionarys Security Engineering Research Team Quarterly Threat Report, Q2 2016.
12 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
Figure 3. Ransomware evolution: Europe
30.00%
25.00%
Incidents of Ransomware Increase
20.00%
15.00%
10.00%
5.00%
0.00%
Jan Feb Mar Apr May Jun Jul Aug Sept
This chart depicts a monthly average of the
ransomware events that occurred from January to 2015 2016
September in 2015 and 2016. While the number of
events varied, the increase in events in 2016 over
the prior year is significant and worrisome.
In addition, there has been an increase in targeting of corporate
executives across Europe to carry out a scam known as CXxO fraud or
Business E-mail Compromise. Cyber criminals typically mimic a small-
to mid-size enterprise with international supply chains requiring regular
wire transfer payments. Hackers compromise legitimate business e-mail
accounts and then request unauthorized transfers of funds.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 13
The GDPR will change not only the
European Data protection laws but
nothing less than the whole world as
we know it.
14 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
The regulatory
environment in
Europe is about
to change
and profoundly
As European organizations encounter a rapidly
changing cyber threat landscape, what about
the regulatory environment?
While the front pages of the Wall Street This sea change in the public reporting
Journal, USA Today and the New York Times obligations of companies will carry
regularly feature reports of breaches against significant ramifications for governments,
US-headquartered companies, the situation businesses and consumers across Europe.
appears on the surface to be blissfully
different in Europe. It is exceedingly rare In addition, the Network Information
that Der Spiegel, Le Monde or Corriere della Security Directive, adopted by the EU in
Sera carry accounts of high-profile breaches July 2016, will place further demands on
against large European companies. governments and the operators of critical
infrastructure.
Why is that? The fundamental difference
in the two continents is that in the United
States, more than 50 federal, state and local EU General Data Protection Regulation
laws mandate disclosure of cyber breaches Jan Philipp Albrecht, a member of the
to regulators or affected consumers. Until European Parliament from Germany and
recently, the regulatory regime in Europe the Rapporteur for the GDPR, captured
was far different. the awesome aspirations of European
policymakers in approving this new
That is about to change profoundly. With regulation: The GDPR will change not only
the recent passage of the European Unions the European Data protection laws but
General Data Protection Regulation (GDPR), nothing less than the whole world as we
companies will soon be required to publicly know it.
disclose data breaches to national data
protection authorities and, where the threat Albrechts comment reflects the strength of
of harm is substantial, to affected individuals. the belief in Europe that privacy constitutes
Failure to do so could result in fines of as a fundamental human right.
much as four percent of a companys global
turnover a staggering sum.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 15
With the growth of Internet-related technology, companies must begin assessing the current state
companies have accumulated troves of personal of their operations and the sweeping breadth of the
data. Business procedures have typically been new requirements.
focused on aggregating broad categories of data
gleaned from consumers. Fearing the impact to the While the regulation is nearly 90 pages long, there
privacy rights of individuals, the European authorities are four broad themes that are worth emphasizing:
are now strengthening privacy law to control, limit
and expose the sweeping collection Individuals will have enhanced rights.
and use of data by many organizations. Companies will be forced to reassess the manner
in which they process and retain data.
Once implemented in May 2018, the GDPR will Companies will need to review their contractual
introduce a seismic shift in how companies retain arrangements with a host of third parties.
and utilize personal data of individuals subject to Companies will be held to far stricter
the EUs jurisdiction. To prepare for implementation, accountability and sanctions.
Figure 4. Components of GDPR implementation
Security breach
notification
Extra-territorial
Data impact
reach over EU
assessment
data
Enhanced
enforcement;
fines as high as
4% of global
Restriction on revenue Individual
secondary uses rights
Notice and Data privacy
consent officers
16 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
Sweeping jurisdiction
The GDPR purports to extend its reach far Businesses can expect both
beyond the borders of the European Union to any
organization that might collect or process personal regulatory authorities and individuals
data of an individual subject to EU jurisdiction
(known as EU data subjects). Extending data to make inquiries about how data is
protection beyond EU borders reflects the EUs view
that data privacy protections should apply wherever being processed.
data may travel. In practice, the broad jurisdictional
provisions signal a clear hope that the GDPRs
complex regulations will have a global impact. So that is the dramatically altered regulatory regime
that will begin to take effect in early 2018. What
insight do we have about how sweeping its impact will
Privacy impact assessments likely be?
Businesses can expect both regulatory authorities
and individuals to make inquiries about how data
is being processed. Individuals can object to any The Dutch mini-GDPR
data collection made without an adequate basis and This is where the Dutch mini-GDPR comes
can demand correction of inaccurate information. into play. After a series of cyber attacks in 2015,
Organizations must perform so-called data impact the Dutch Parliament passed a Personal Data
assessments prior to collecting data. Protection Act, known as the Wet Bescherming
Persoonsgegevens (WBP), in late 2015. In the time
The GDPR provides guidance on practices since the Dutch mini-GDPR took effect on January
to protect data, such as de-linking data from 1, 2016, companies have already notified the Dutch
identities (pseudonymisation), encryption, regular authorities of more than 5,500 cyber incidents.
assessments of technical controls, and incident Extrapolating these figures across the EU gives a
response plans that account for maintaining the glimpse of what management will likely confront in
confidentiality and integrity of data. response to inquiries from regulators, supervisory
boards and the press.
Affirmative consent and the right to
be forgotten Network Information Security Directive
The GDPR makes clear that no company may collect To enhance focus on the specific vulnerabilities
personal data without first notifying users of how regarding critical infrastructure, the EU separately
their data will be stored, protected and shared with enacted the Network Information Security (NIS)
third parties. In order to collect data, the company Directive. Also scheduled to take effect in 2018, the
must first obtain the individuals freely given, NIS Directive will impose additional obligations on
specific, informed and unambiguous consent for the EU member states and infrastructure operators to
collection. The GDPR will require users to give consent raise the baseline of their cybersecurity capabilities.
by affirmatively clicking on a consent notice or opting For example, the NIS Directive will require all member
for specific technical settings that allow for the data states to have a cybersecurity strategy, a national
collection. competent authority, and national cybersecurity
incident response teams.
Lastly, the GDPR codifies the right to be forgotten.
Already recognized by European courts and some Several EU nations have already demonstrated early
member states, the right to be forgotten allows data leadership. For example, Germany announced the
subjects to demand that their personal data be erased creation of a mobile Quick Reaction Force as part of
and no longer used for processing. its Federal Office for Information Security.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 17
Cyber preparedness in the
EU is improving, but the
journey has just begun
Marsh surveyed the cyber practices at more than 750
of its clients across continental Europe in the fall of
With the threat environment 2016.2 The study found that while high-profile events,
intensifying and the regulatory government initiatives, and legislation have pushed
cybersecurity to the forefront, far more work needs
environment about to change to be done.
profoundly, the question becomes For example, Marsh found that the percentage
whether industry and even of companies indicating that they assessed key
suppliers for cyber risk actually decreased from 23
government are ready for percent in 2015 to 20 percent in 2016. As numerous
attacks in the US and elsewhere have shown, hackers
these changes. often gain access to larger organizations by initiating
attacks against smaller vendors that provide services
like air conditioning or takeout food.
2 Continental European Cyber Risk Survey: 2016 Report
18 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
General awareness of the risk posed by cyber
31% 32%
attacks, while increasing, remains low. The
percentage of companies that report having a strong
understanding of their cyber posture increased from
21 percent in 2015 to 31 percent in 2016. Similarly,
companies that regard cybersecurity as a top-five COMPANIES THAT HAVE A COMPANIES THAT REGARD
risk increased from 17 percent in 2015 to 32 percent STRONG UNDERSTANDING CYBERSECURITY
in 2016, and the percentage of organizations that did OF THEIR CYBER POSTURE AS A TOP-FIVE RISK
not even include cyber on their risk register dropped
from 23 percent in 2015 to 9 percent in 2016.
Despite this progress, European companies, like their
counterparts around the world, have a long way
to go to keep pace with the dramatically changing
9%
ORGANIZATIONS THAT
threat and regulatory environments. DID NOT EVEN INCLUDE
CYBER ON THEIR RISK REGISTER
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 19
How can Government and industry, in Europe
and elsewhere, are engaged in a race
companies without a finish line. Adversaries
will be constantly adjusting their
brace for strategies and identifying new targets
the storm?
and more destructive attacks. Offense
is far easier than defense.
20 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
While there are many technological advances that will form part of the solution, potentially
including encryption at rest and blockchain, we focus on five non-technological recommendations.
1 Cybersecurity is not solely an IT issue.
The most senior members of a companys management team must engage and be at
least conversant with this dynamic risk. In your organization, can the CEO, the CFO or
the GC answer the following three questions:
What are your companys principal cyber vulnerabilities?
What are your key strategies for mitigating those risks?
Are adequate resources being devoted to the task at hand?
2 Vulnerability assessments are essential.
Every company should conduct a vulnerability assessment. The best place to start in
2017 is to benchmark your cyber protocols against an established standard. What are
your most critical cyber assets? Does your organization primarily rely upon proprietary
data or industrial control systems? Have you assessed the true financial consequences
of a large-scale breach?
3 Cyber risk is now a board-level issue.
Supervisory boards in Europe will be putting far more focus and pressure on
management teams in the coming year. Expect your board to ask questions about
patching of software vulnerabilities, implementing multi-factor authentication for user
access, and conducting risk assessments of third-party vendors and suppliers. If it takes
your organization three times longer to identify a cyber intrusion as other companies,
will that be satisfactory for your board?
4 Corporations should engage with external stakeholders.
If the premise is correct that cyber breaches will become a far more public issue for
European corporations in the coming 12-18 months, now is the time to prepare by
reaching out to build relationships of trust with data protection and law enforcement
authorities, policymakers and the press. In addition, have you engaged top-notch
security experts to respond to an incident?
5 Governments in Europe must lend a hand
to the business community.
Given the particular threat posed to critical infrastructure, governments in Europe
should reach out more affirmatively to the business community on two fronts:
By sharing threat intelligence in real time regarding the latest forms of attack and
known malicious IP addresses.
By promptly alerting businesses that their systems have been breached.
An enhanced level of trust between government and industry will pay dividends
in a host of different areas.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 21
22 SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017
A call to action
FireEye and Marsh & McLennan Companies joined together to provide
an overview of a fundamental challenge facing the European Union
the evolving threat landscape and questions surrounding the regions
ability to address new cyber threats. There are no quick fixes or
magic solutions. No sector, in isolation, can solve this issue on its own.
Rather, a true public-private partnership is required.
Our goal with this paper is to increase awareness of emerging threats
and recommend tangible steps for businesses and government across
Europe to enhance their cyber resilience.
SPECIAL REPORT / FIREEYE | MMC CYBER RISK REPORT 2017 23
About FireEye, Inc.
FireEye is the intelligence-led security company. Working as a seamless, scalable extension of customer security operations,
FireEye offers a single platform that blends innovative security technologies, nation-state grade threat intelligence, and
world-renowned Mandiant consulting. With this approach, FireEye eliminates the complexity and burden of cyber security for
organizations struggling to prepare for, prevent, and respond to cyber attacks. FireEye has over 5,300 customers across 67
countries, including more than 825 of the Forbes Global 2000.
For more information, please contact info@fireeye.com
About Marsh & McLennan Companies
Marsh & McLennan Companies provide advice and solutions to mitigate cyber risk. As the worlds most trusted cyber
insurance broker, Marsh, Inc. advises over 1,000 clients regarding network security and privacy issues and has won Advisens
award for Cyber Broker of the Year in 2014, 2015 and 2016.
www.marsh.com/us/services/cyber-risk.html
For more information, please contact: Thank you to our contributors:
Europe Ireland FireEye
Flavio Piccolomini Derek Smoker Tony Cole
CEO, Marsh Continental Europe Vice President of Marsh Ireland Kristi Houssiere
flavio.piccolomini@marsh.com derek.smoker@marsh.com Stuart McKenzie
39 02 48 53 84 62 +353 1 6048381 Jens Monrad
Nick Rossmann
Nilay Ozden Breege Lynn Tony Sapienza
Marsh FINPRO Practice Leader Senior Vice President of Marsh Ireland Lynn Thorne
nilay.ozden@marsh.com breege.lynn@marsh.com Kristen Verderame
44 78 25 22 84 54 +353 87 2590129
Marsh & McLennan
Giampaolo Scarso United Kingdom Devin Beresheim
Head of Client Advisory Services, Mark Weil Ronnie Brandes
Marsh Central Europe, Middle East CEO for Marsh UK & Ireland Matthew McCabe
and Africa mark.weil@marsh.com Bob Parisi
giampaolo.scarso@marsh.com 44 20 73 57 59 27 Tom Reagan
39 02 48 53 82 81 Inna Tsimerman
Peter Johnson
Jean Bayon de La Tour Marsh UK Cyber Advisory Lead
Marsh Cyber Development Leader peter.a.johnson@marsh.com
jean.bayondelatour@marsh.com 44 20 7357 3527
33 1 41 34 50 05
United States
Corrado Zana Thomas Reagan
MRC Business Resilience Leader Cyber Practice Leader
corrado.zana@marsh.com thomas.reagan@marsh.com
39 02 48 53 85 27 +1 212 345 9452
Robert Parisi
Cyber Product Leader
robert.parisi@marsh.com
+1 212 345 5924
FireEye, Inc.
1440 McCarthy Blvd. Milpitas, CA 95035
408.321.6300 / 877.FIREEYE (347.3393) / info@FireEye.com
www.FireEye.com
2017 FireEye, Inc. All rights reserved. FireEye is a registered trademark of FireEye, Inc. All other brands, products or
service names are or may be trademarks or service marks of their respective owners. SR.FEMM.EN-US.012017
You might also like
- 10 01 14 PDFDocument1 page10 01 14 PDFSalahddin KhalilNo ratings yet
- Addelali Benamour Asinag2fr PDFDocument7 pagesAddelali Benamour Asinag2fr PDFSalahddin KhalilNo ratings yet
- Adsl Routers PDFDocument42 pagesAdsl Routers PDFSalahddin KhalilNo ratings yet
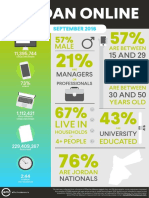
- 0907 Jordan Online PDFDocument5 pages0907 Jordan Online PDFSalahddin KhalilNo ratings yet
- Systeme Educatif PDFDocument10 pagesSysteme Educatif PDFSalahddin KhalilNo ratings yet
- Bitcoin Manifesto - Satoshi NakamotoDocument9 pagesBitcoin Manifesto - Satoshi NakamotoJessica Vu100% (1)
- Liste Verbes Irreguliers PDFDocument6 pagesListe Verbes Irreguliers PDFGonzalo FernandezNo ratings yet
- Cybersecurity Best Practices Guide For IIROC Dealer Members - enDocument52 pagesCybersecurity Best Practices Guide For IIROC Dealer Members - enaristoteles_cerberus2409No ratings yet
- Cyber Risk: A Guide ToDocument32 pagesCyber Risk: A Guide ToSalahddin KhalilNo ratings yet
- Cybersecurity Best Practices Guide For IIROC Dealer Members - enDocument52 pagesCybersecurity Best Practices Guide For IIROC Dealer Members - enaristoteles_cerberus2409No ratings yet
- EBOOK Sarah Mclean - La Famille ST John Tome 3 L Am PDFDocument187 pagesEBOOK Sarah Mclean - La Famille ST John Tome 3 L Am PDFSalahddin KhalilNo ratings yet
- CN Arabic Form PDFDocument4 pagesCN Arabic Form PDFSalahddin KhalilNo ratings yet
- Correction Exo 2 Cic PDFDocument2 pagesCorrection Exo 2 Cic PDFSalahddin KhalilNo ratings yet
- Correction Exo 1 Cic PDFDocument1 pageCorrection Exo 1 Cic PDFSalahddin KhalilNo ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (120)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- 雅思口语常用高效表达句型 PDFDocument3 pages雅思口语常用高效表达句型 PDFJing AnneNo ratings yet
- 02-Case Study ESSS - Milestone 01 Scope DefinitionDocument10 pages02-Case Study ESSS - Milestone 01 Scope Definition3LIX 311No ratings yet
- Near Miss ReportingDocument14 pagesNear Miss ReportingMuflihMuhammadNo ratings yet
- Ludermis Suardi Rhetorical Analysis EditedDocument5 pagesLudermis Suardi Rhetorical Analysis Editedapi-253530551No ratings yet
- Literarture Review For New DesignDocument2 pagesLiterarture Review For New Designsaumya irugalbandaraNo ratings yet
- Community-Based Health Planning Services: Topic OneDocument28 pagesCommunity-Based Health Planning Services: Topic OneHigh TechNo ratings yet
- Morphology & Syntax "Morpheme Forms": Page - 1Document10 pagesMorphology & Syntax "Morpheme Forms": Page - 1محمد ناصر عليويNo ratings yet
- Interim Financial ReportingDocument3 pagesInterim Financial ReportingHalina ValdezNo ratings yet
- 30.JG Summit Holdings V CA, GR No. 124293, Jan 31, 2005Document15 pages30.JG Summit Holdings V CA, GR No. 124293, Jan 31, 2005HNo ratings yet
- Litonjua JR Vs Litonjua SRDocument17 pagesLitonjua JR Vs Litonjua SRRubyNo ratings yet
- Computer Science and Engineering: Seminar Report On Mass Media byDocument17 pagesComputer Science and Engineering: Seminar Report On Mass Media byJohnny ThomasNo ratings yet
- Dharma DuraiDocument3 pagesDharma Duraivsection managerNo ratings yet
- Fashion OrientationDocument7 pagesFashion OrientationRAHUL16398No ratings yet
- Customer Information Update FormDocument1 pageCustomer Information Update FormmikeNo ratings yet
- Against Open Merit: Punjab Public Service CommissionDocument2 pagesAgainst Open Merit: Punjab Public Service CommissionSohailMaherNo ratings yet
- The City Bride (1696) or The Merry Cuckold by Harris, JosephDocument66 pagesThe City Bride (1696) or The Merry Cuckold by Harris, JosephGutenberg.org100% (2)
- Luovutuskirja Ajoneuvon Vesikulkuneuvon Omistusoikeuden Siirrosta B124eDocument2 pagesLuovutuskirja Ajoneuvon Vesikulkuneuvon Omistusoikeuden Siirrosta B124eAirsoftNo ratings yet
- Frivaldo Vs Comelec 1996Document51 pagesFrivaldo Vs Comelec 1996Eunice AmbrocioNo ratings yet
- Conceptual Art and The Politics of PublicityDocument253 pagesConceptual Art and The Politics of PublicityAlan Eric Sanguinetti77% (13)
- 02-7 QCS 2014Document5 pages02-7 QCS 2014Raja Ahmed Hassan0% (1)
- MultiCultural Counseling Competencies and StandardsDocument10 pagesMultiCultural Counseling Competencies and StandardsIrwan J S100% (1)
- Ephesians 5.32-33Document2 pagesEphesians 5.32-33Blaine RogersNo ratings yet
- Experience Certificate For English TeacherDocument2 pagesExperience Certificate For English TeacherShaher Alburaihy86% (7)
- Drugs: Use, Abuse and Addiction - Lesson Plan (Grades 9 & 10)Document23 pagesDrugs: Use, Abuse and Addiction - Lesson Plan (Grades 9 & 10)Dimple Lasala ElandagNo ratings yet
- BARD 2014 Product List S120082 Rev2Document118 pagesBARD 2014 Product List S120082 Rev2kamal AdhikariNo ratings yet
- Talavera, Nueva EcijaDocument2 pagesTalavera, Nueva EcijaSunStar Philippine NewsNo ratings yet
- 08 - Case Law-Unknown Case Law ListDocument28 pages08 - Case Law-Unknown Case Law ListNausheen100% (1)
- Brand Management Assignment 1 FINALDocument4 pagesBrand Management Assignment 1 FINALbalakk06No ratings yet
- Cosmetics & Toiletries Market Overviews 2015Document108 pagesCosmetics & Toiletries Market Overviews 2015babidqn100% (1)
- Jo LibbeDocument4 pagesJo LibbejacNo ratings yet