Professional Documents
Culture Documents
OBN208211 IManager N2000 BMS Platform Operation and Maintenance ISSUE2.00
Uploaded by
AndresCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
OBN208211 IManager N2000 BMS Platform Operation and Maintenance ISSUE2.00
Uploaded by
AndresCopyright:
Available Formats
Internal
OBN110201 iManager
N2000 BMS Platform
Operation and Maintenance
ISSUE 2.0
www.huawei.com
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved
References
N2000 Administrator Guide
N2000 Operator Guide
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 2
Upon completion of this course, you will understand:
Manage the N2000 User
Manage the Network Topology
Monitor Network Alarms
Monitor the Network Performance
Monitor the Environment and Power Supply
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 3
Chapter 1 Logging In to the N2000
Chapter 2 N2000 User Management
Chapter 3 Topology Management
Chapter 4 Alarm Management
Chapter 5 Performance Management
Chapter 6 Environment Monitoring
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 4
Logging In to the N2000
Double click on the desktop to display the Login dialog box
Set the IP address and server name of the
N2000 server
Enter the user name and password
Click Login to log in to the N2000 server
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 5
N2000 Main Interface on the Client
Menu Topology tool Window title Alarm panel
Menu bar
Tool bar
Navigation tree
Main window
Main view
Output window
Status bar
Login user Connection Login mode Login server Prompt Logo
duration
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 6
Changing the Password
Select System > Modify My Password from the main menu
The password:
•shall contain 8–16 characters.
•shall contain characters as well as numbers .
•must not be identical with the user name.
•must not be the same as the latest used eight ones.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 7
Chapter 1 Logging In to the N2000
Chapter 2 N2000 User Management
Chapter 3 Topology Management
Chapter 4 Alarm Management
Chapter 5 Performance Management
Chapter 6 Environment Monitoring
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 8
Basic Concepts
User
After installation, the N2000 provides a super user admin by default.
User rights include the rights to manage devices and the rights to
perform operations. That is, each user can only perform authorized
operations on authorized devices.
User Group
A user group is a group of users with the same rights to operate on the
N2000. The N2000 provides three default user groups:
− Maintainer group
− Operator group
− Monitor group
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 9
Basic Concepts
ACL
The access control list (ACL) determines the IP address from which a
user can log in to the N2000.
Security control is achieved in two layers:
− System ACL: It defines a series of IP addresses for N2000 clients.
Only clients with these IP addresses can access the N2000 server.
− User ACL: It defines the IP addresses with which a user can access
the N2000 server. All the IP addresses in the user ACL are in the
system ACL.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 10
Basic Concepts
Management right
Management rights specify the devices and resources a user can
mange, or an area a user group can manage. A new user has no right
to manage any resource by default.
Operation right
Operation rights specify the operations a user can perform. User
operation right is a triplet which consists of users, security objects and
operations.
Operation Set
An operation set is a group of operations related to a command set on
the N2000.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 11
Creating a User
Select System > Security Management from the main menu.
On the Security Object tree, select the Users node, right click and select
New User.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 12
Allocating Management Rights
On the Security Object tree, click a user under the Users node.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 13
Allocating Operation Rights
Click the Operation Right tab in the user panel.
On the Operation Right tab, click Add.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 14
Setting User ACL Rights
On the Security Object tree, click a user under the Users node.
In the right pane, click the ACL Setting tab.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 15
Managing N2000 User Groups
Creating a User Group
On the Security Object tree, select the User Groups node, right
click and select New User Group.
Allocating Management Rights to a User Group
Allocating Operation Rights to a User Group
Adding Users to a User Group
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 16
Managing Operation Sets
An operation set contains all operations available to the users of the
same operation type and level.
Creating an Operation Set
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 17
Managing Operation Sets
Adding Operations to an Operation Set
On the Security Object tree, click an operation set under the Operation
Sets node. In the right pane, click the Member tab.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 18
Chapter 1 Logging In to the N2000
Chapter 2 N2000 User Management
Chapter 3 Topology Management
Chapter 4 Alarm Management
Chapter 5 Performance Management
Chapter 6 Environment Monitoring
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 19
Overview
Topology management enables you to set up and manage the network
topology.
With the topological view, you can:
Monitor the running status of the entire network in real time.
Upload topological data of devices that are automatically discovered
or manually added.
Monitor devices at intervals and refresh their statuses, so as to keep
the view the same as the actual topology.
Observe the polling status and alarm status of the devices through
the colour of topological nodes.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 20
Main Window for Topology Management
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 21
Terms
Topological View
Topology is a map of managed communications network on the
N2000. The managed devices and links are shown on the device
explorer and in the topological view in the form of a tree and diagram.
In the view, you can configure data, manage faults and performance.
Submap
In the NMS, you can divide a large network into several smaller
networks by a certain rule, such as by geographical area. This helps
to manage the devices easily. Such small networks are called
submaps in the topology.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 22
Terms
Node
A node stands for a managed device in the network.
For a device with a single frame, one node stands for one device.
For a device with multiple frames, one node stands for one frame of
the device.
Link
A link is a connection between two nodes.
Container
A container is a type of topological node which contains nodes. One
container often stands for one device with multiple frames, and each
node in the container stands for one frame.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 23
Terms
NE
In topology management, an NE stands for a device in the managed
network. Different device types match different NE types, and
different icons represent different NE types in the topological view.
Polling Status
The NMS queries device status as well as other configuration data at
intervals, and then shows the status in the topological view. Possible
polling statuses are:
− Normal ,Unknown ,Offline ,Insignificant fault , Minor fault, Major
fault , Critical fault
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 24
Creating a Topological View
Adding a submap
Select Edit > Add Object from the main menu or right click on the main
view
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 25
Creating a Topological View
Creating an NE
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 26
Creating a Topological View
Creating a Link
Select two objects, right click, and then select Create Link
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 27
Querying Topological Objects
Select Edit > Search from the main menu, or press Ctrl+F, or click
The keyword
for searching
From the search result, select
the record you want to locate,
and then double click it or
click Locate.
You can locate the object
related to the record in the
topological view or on the
device panel.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 28
Setting Device Maintenance Information
Setting Maintainer information
Select Edit > Maintenance Info Template Setting from the main menu.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 29
Setting Device Maintenance Information
Setting Maintenance Information
Select Edit > Device Maintenance Info from the main menu.
specify the
location data
select a
maintainer
record
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 30
Discovering Device Automatically
Select Edit > Auto Discovery from the main menu.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 31
Chapter 1 Logging In to the N2000
Chapter 2 N2000 User Management
Chapter 3 Topology Management
Chapter 4 Alarm Management
Chapter 5 Performance Management
Chapter 6 Environment Monitoring
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 32
Alarm Category
Classified by Characteristics
Fault alarm
Event alarm
Cleared alarm
Classified by Function Modules
Power alarm
Environment alarm
Signalling alarm
Trunk alarm
Hardware alarm
……
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 33
Alarm Level
Critical alarm
Major alarm
Minor alarm
Warning alarm
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 34
Alarm Status Transition
NE
Report
Ack
Unacked & Acked & uncleared
uncleared alarm alarm
Recover Recover
Ack
Unacked &
History alarm
cleared alarm
Current alarm
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 35
Process of Reporting Alarms
Start
Report alarms
Mask alarms
Analyze alarm
correlation
Report alarms
Save alarms
Notify alarms
End
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 36
Get Alarm from Alarm Panel
Alarm panel shows the numbers of different severity alarms.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 37
Get Alarm from Topology
The status icon on the upper left of the topological object indicates the
alarm status of the object.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 38
Get Alarm from Alarm Browser
Select a alarm browsing profile to list the correlative alarms.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 39
Configuring an Alarm Profile
On the Fault Browser tree, select one node such as Realtime Alarm, Current
Alarm, etc. ,then right click. Select Create a Profile
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 40
Measuring Alarms
On the Fault Browser tree, right click the Alarm Statistics node.
Select Create a Profile
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 41
Alarm Operations
Querying Alarm Details
Locating an Alarm
Acknowledging an Alarm
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 42
Setting Auto Alarm Acknowledgement
Select Fault > Fault Setting > Dump&Sync&Ack
In the dialog box that appears, click the Ack tab
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 43
Setting Auto Alarm Dumping
Select Fault > Fault Setting > Dump&Sync&Ack
In the dialog box that appears, click the Dump tab
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 44
Setting Auto Alarm Synchronization
Select Fault > Fault Setting > Dump&Sync&Ack
In the dialog box that appears, click the Synchronize tab
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 45
Alarm Panel Management
Setting an Alarm Panel
Select Fault > Fault Setting > Local Property
In the dialog box that appears, click the Alarm Panel tab
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 46
Alarm Panel Management
Disabling the Alarm Sound
Select Fault > Audio&Visual > Stop Alarm Panel Sound from the
main menu.
Stopping the Current Alarm Sound
Select Fault > Audio&Visual > Stop Alarm Panel Current Sound
from the main menu.
Or click on the tool bar.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 47
Alarm Box Management
Setting an Alarm Box
Select Fault > Fault Setting > Local Property
In the dialog box that appears, click the Others tab
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 48
Alarm Box Management
Resetting an Alarm Box
Select Fault > Audio&Visual > Reset Alarm Box from the main menu.
In the dialog box that appears, select an alarm level, and then click OK.
Stopping Alarm Box Sound
Select Fault > Audio&Visual > Stop Alarm Box Sound from the main
menu.
Synchronizing an Alarm Box Data
Select Fault > Audio&Visual > Synchronize Alarm Box Data from
the main menu.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 49
Chapter 1 Logging In to the N2000
Chapter 2 N2000 User Management
Chapter 3 Topology Management
Chapter 4 Alarm Management
Chapter 5 Performance Management
Chapter 6 Environment Monitoring
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 50
Performance Management Overview
The N2000 supports the following functions:
NE performance monitoring
NE data analysis
Traffic measurement task management
Data query
Performance threshold alarm management
The N2000 enables you to know the running state of the network. In this
case, you can take some measures to avoid faults. You can analyze
network performance data and quality of service for better network
planning.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 51
Measurement Principles
Threshold alarm Create a Query performance
performance task results
N2000 N2000 N2000
Send collection
commands periodically
N2000
Report NE performance
result
Related SNMP NE
Analyse results Save results
N2000 N2000
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 52
Creating a Measurement Task
Select Performance&Stat > Task Management
In the Device Type drop-down list, select a device
In the task list area, right click, and then select Create Task.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 53
Querying Performance Data
Query by Measurement Object
Select Performance & Stat > Performance Data Management
In the pane that appears, click the Query By Measuring Object tab.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 54
Querying Performance Data
Query by Measurement Task
Select Performance & Stat > Performance Data Management
In the pane that appears, click the Query By Task tab
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 55
Analysing Time Distribution
Select Performance&Stat > Time Distribution Analysis from the main menu.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 56
Comparing Time Distribution
Select Performance&Stat > Compare Time Analysis from the main menu.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 57
Configuring Performance Alarm Threshold
Configure a performance threshold template
Select Performance&Stat >
Threshold Management >
Threshold Template
Management from the main
menu.
In the pane that appears, click
Create.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 58
Configuring Performance Alarm Threshold
Configure a performance threshold record
Select Performance&Stat >
Threshold Management >
Threshold Record
Management from the main
menu.
In the pane that appears, click
Create
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 59
Backing Up Performance Data
Manual backup
Select
Performance&Stat >
Data Maintenance >
Manual Maintenance
from the main menu.
click Configure to
select database tables
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 60
Backing Up Performance Data
Automatic Backup
Select
Performance&Stat >
Data Maintenance >
Timed Maintenance
from the main menu.
click Configure
to select
database tables
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 61
Deleting Performance Data
Manual Deleting
Select Performance&Stat > Data Maintenance > Manual Maintenance
Select Delete Data for Operation Strategy.
In the Database Table Set area, click Configure.
In the dialog box that appears, select database tables, and then click OK.
In the Time Range of Data to Process area, click …, and then select the
start time and end time.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 62
Deleting Performance Data
Automatic Deleting
Select Performance&Stat > Data Maintenance > Timed Maintenance.
In the pane that appears, click Add.
In the dialog box that appears, select Delete Data for Operation Strategy.
Set the name and description of the deleting task. In the Database Table
Set area, click Configure. In the dialog box that appears, select
database tables, and then click OK.
In the Time Strategy area, set the trigger time and time range to delete
data.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 63
Chapter 1 Logging In to the N2000
Chapter 2 N2000 User Management
Chapter 3 Topology Management
Chapter 4 Alarm Management
Chapter 5 Performance Management
Chapter 6 Environment Monitoring
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 64
Environment Monitoring Overview
With the EM management, you can monitor the environment and power
supplies of all the switches and access network (AN) devices.
The functions of the EM are as follows.
Centralized environment and power monitoring: monitors environment
and power supplies of all environment monitoring units (EMUs)
Single-point environment and power monitoring: monitors environment
and power supplies of a specified EMU
Environment and power alarm monitoring: monitors alarms of
environment and power supplies
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 65
Environment and Power Monitoring Window
Select Environment Monitoring > Start Environment Power Monitoring
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 66
Centralized Monitoring
Browsing EMU Data
Select Environment Monitoring > Start Environment Power Monitoring
In the Device Monitoring Range area, select a device
In the EMU List Field area, set the EMU list fields to display
Click OK or Apply
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 67
Centralized Monitoring
Browsing Environment and Power Supply Parameters
Select Environment Monitoring > Start Environment Power
Monitoring
In the EMU list, select an EMU, right click, and then select Query EMU
Details.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 68
Single-Point Monitoring
Starting the Environment Monitoring Panel
Method 1:
In the Environment & Power
Monitoring window, query EMUs. In the
EMU list, double click an EMU.
Method 2:
On the device navigation tree in the left
pane, select an NE node. Right click,
and then select Open Environment
Power Monitoring Panel.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 69
Single-Point Monitoring
Browsing Monitoring Information on the Panel
On the environment monitoring panel
Click the Basic Info tab, and then browse power supply parameters
in the Power Parameter Info area.
Click the Basic Info tab, and then browse environment parameters
in the Environment Parameter Info area.
Click the Basic Info tab, and then browse rectifier module data in
the Rectifier Information area.
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 70
Summary
In this course, we learned the common
functions and operations of the N2000,
from the following aspects:
Topology
Alarm
Performance
Environment and power supply
HUAWEI TECHNOLOGIES CO., LTD. All rights reserved Page 71
Thank You
www.huawei.com
You might also like
- UA5000 V100R019C01 Product DescriptionDocument105 pagesUA5000 V100R019C01 Product DescriptionSam AwiNo ratings yet
- Motive HDM en DataSheetDocument2 pagesMotive HDM en DataSheetshitbox222100% (1)
- Msan Ua5000Document33 pagesMsan Ua5000zohra1858No ratings yet
- 3HH-08082-DEAA-TCZZA-02-CLI TL1 Alarm Mapping Document - R4 4 XDocument160 pages3HH-08082-DEAA-TCZZA-02-CLI TL1 Alarm Mapping Document - R4 4 XStavros SotiriadisNo ratings yet
- Imanager U2000 Northbound XML Interface User Guide - (V100R002C01 - 05)Document120 pagesImanager U2000 Northbound XML Interface User Guide - (V100R002C01 - 05)Richard Johnson50% (2)
- slx-20 1 1-L2guideDocument291 pagesslx-20 1 1-L2guidePrinceRaiNo ratings yet
- Alcatel Lucent 7330 Product Information Manual 256Document256 pagesAlcatel Lucent 7330 Product Information Manual 256LokkyNo ratings yet
- Guide To Maintenance Quick Reference of Huawei Optical Networking DevicesDocument72 pagesGuide To Maintenance Quick Reference of Huawei Optical Networking Deviceschristal MIAKOUKILANo ratings yet
- NortelDocument110 pagesNortelVijay KumarNo ratings yet
- Radius Manager GuideDocument73 pagesRadius Manager GuideAlex KobeissyNo ratings yet
- Cable Modem Terminate System: SetupDocument68 pagesCable Modem Terminate System: SetupShakespeare Rodas100% (1)
- Bsc6900 GSM v900r014c00spc500 Release NotesDocument412 pagesBsc6900 GSM v900r014c00spc500 Release NotesWdfty UytyuNo ratings yet
- Model Tuning Presentation Procedure Compatibility ModeDocument58 pagesModel Tuning Presentation Procedure Compatibility ModenirolkojuNo ratings yet
- UA5000 Configuration Guide-PVM CLI (V100R017 - 08)Document401 pagesUA5000 Configuration Guide-PVM CLI (V100R017 - 08)Tiến Hồ Văn100% (5)
- Fiberhome S6800 Series Switch Command Reference Manual V1.0Document1,163 pagesFiberhome S6800 Series Switch Command Reference Manual V1.0Ronie SinghNo ratings yet
- 830-01929-08 ZMS OSS GuideDocument262 pages830-01929-08 ZMS OSS Guidepolan78No ratings yet
- AR1200 S&AR2200 S Hardware DescriptionDocument145 pagesAR1200 S&AR2200 S Hardware DescriptionTariq EhsanNo ratings yet
- Huawei Imanager U2000 Northbound CORBA Interface Developer Guide (Configuration)Document344 pagesHuawei Imanager U2000 Northbound CORBA Interface Developer Guide (Configuration)서상현100% (1)
- Tinsley 5941 Operating Manual (En)Document31 pagesTinsley 5941 Operating Manual (En)Dimas PermanaNo ratings yet
- Mellanox Ethernet Switch BrochureDocument4 pagesMellanox Ethernet Switch BrochureTimucin DIKMENNo ratings yet
- 20W RX 7639 - Qe - 1 0 0Document42 pages20W RX 7639 - Qe - 1 0 0Duval FortesNo ratings yet
- IP-10 Quick Startup Guide 9 (1) (1) .9Document12 pagesIP-10 Quick Startup Guide 9 (1) (1) .9bhavyapaliwalNo ratings yet
- Dopra Linux OS Security (SingleRAN - 20)Document57 pagesDopra Linux OS Security (SingleRAN - 20)waelq2003No ratings yet
- Genband Q10 SBC: The Intelligent Session Border ControllerDocument4 pagesGenband Q10 SBC: The Intelligent Session Border Controllerkaz78780% (1)
- UA5000 Configuration Guide PVM CLI V100R017 08 PDFDocument401 pagesUA5000 Configuration Guide PVM CLI V100R017 08 PDFMarvin HernandezNo ratings yet
- Project Report of Building Course Management System by Django FrameworkDocument29 pagesProject Report of Building Course Management System by Django Frameworksravan kumarNo ratings yet
- Huawei Tecal RH2288 V2 Server Compatibility List PDFDocument30 pagesHuawei Tecal RH2288 V2 Server Compatibility List PDFMenganoFulanoNo ratings yet
- HUAWEI BSC6000 V900R008 General Introduction: 2008-05 Security Level: Internal UseDocument32 pagesHUAWEI BSC6000 V900R008 General Introduction: 2008-05 Security Level: Internal UseroobowNo ratings yet
- Network Analyzer-Fiber Release 9.2.11: User GuideDocument206 pagesNetwork Analyzer-Fiber Release 9.2.11: User GuideMuhammad Waqas AslamNo ratings yet
- UA5000 Product Description (V100R019C02 - 02)Document105 pagesUA5000 Product Description (V100R019C02 - 02)Jeka TarevaNo ratings yet
- Autonomous Driving Network Whitepaper En1 PDFDocument84 pagesAutonomous Driving Network Whitepaper En1 PDFMohola Tebello GriffithNo ratings yet
- Oracle Fusion Middleware Installation On Linux 6Document5 pagesOracle Fusion Middleware Installation On Linux 6Khalid HossainNo ratings yet
- Huawei FusionSphere 6.5.0 Technical White Paper (Server Virtualization)Document26 pagesHuawei FusionSphere 6.5.0 Technical White Paper (Server Virtualization)Myo Lwin SoeNo ratings yet
- Huawei FusionServer Pro V5 Rack Server Data SheetDocument16 pagesHuawei FusionServer Pro V5 Rack Server Data SheetOussama BennaniNo ratings yet
- Visually Creating Blockchain Applications Using Hyperledger Fabric and JogetDocument17 pagesVisually Creating Blockchain Applications Using Hyperledger Fabric and JogetPooja SharmaNo ratings yet
- Nortel Cs 1000 Voip Phone System TechnicalDocument22 pagesNortel Cs 1000 Voip Phone System TechnicalSlayer KingNo ratings yet
- 2022 TL1-Northbound - Interface - TL1 - User - Manual - 04 PDFDocument344 pages2022 TL1-Northbound - Interface - TL1 - User - Manual - 04 PDFPedro MarangaoNo ratings yet
- Altair RN 04 05 06 10 88 TFDocument32 pagesAltair RN 04 05 06 10 88 TFSri NivasNo ratings yet
- Connected Fleet Solution: ConfidentialDocument10 pagesConnected Fleet Solution: ConfidentialAditya RanaNo ratings yet
- Huawei S9300E Switch Product BrochuresDocument9 pagesHuawei S9300E Switch Product BrochuresMaxNo ratings yet
- 3JL03001BTAAPCZZA01 - V1 - 5529 IDM Release 9.7 Installation Administration and User GuideDocument136 pages3JL03001BTAAPCZZA01 - V1 - 5529 IDM Release 9.7 Installation Administration and User GuidePlaystation IdentifierNo ratings yet
- Everything You Need to Know About Blu-ray FAQsDocument22 pagesEverything You Need to Know About Blu-ray FAQsSunil GuptaNo ratings yet
- EMUB User GuideDocument58 pagesEMUB User GuideИван МальковNo ratings yet
- 05 EsightDocument12 pages05 EsightAbrar AhmadNo ratings yet
- Hardware Description (MSOFTX3000)Document208 pagesHardware Description (MSOFTX3000)ABHILASHNo ratings yet
- XC90 Owners Manual MY10 en Tp10922Document291 pagesXC90 Owners Manual MY10 en Tp10922pakNo ratings yet
- Huawei E9000 Blade Server Chassis Datasheet: Quick SpecsDocument6 pagesHuawei E9000 Blade Server Chassis Datasheet: Quick SpecsSyed Mohammed WasiNo ratings yet
- Operation and Maintenance of m2000 HuaweiDocument112 pagesOperation and Maintenance of m2000 HuaweiAbdouTreizeNo ratings yet
- Operation and Maintenance of M2000 HuaweiDocument112 pagesOperation and Maintenance of M2000 HuaweiShalama Masuntlha100% (2)
- Neteco 1000U V100R002C10 Training SlidesDocument39 pagesNeteco 1000U V100R002C10 Training Slidesabera alemayehuNo ratings yet
- Guide M2000 ClientDocument58 pagesGuide M2000 ClientDONALFYNo ratings yet
- M2000 Basic Skill Training Compress - PART2Document20 pagesM2000 Basic Skill Training Compress - PART2Abdilla RaisNo ratings yet
- En-Us Attachment 0000001208419856Document1,575 pagesEn-Us Attachment 0000001208419856andess_bayNo ratings yet
- 06-Optix WDM Series Equipment Data Configuration Issue1.20Document99 pages06-Optix WDM Series Equipment Data Configuration Issue1.20btpservice brukinaNo ratings yet
- NodeB O&MDocument37 pagesNodeB O&MmanuelNo ratings yet
- Cisco Unified Communications Manager 11.x New Features Lab Self-Provisioning SetupDocument19 pagesCisco Unified Communications Manager 11.x New Features Lab Self-Provisioning SetupFaisal KhanNo ratings yet
- WCDMA NodeBV211 Operation and Manitenance 20100208 B V1 0Document37 pagesWCDMA NodeBV211 Operation and Manitenance 20100208 B V1 0Ehtesham KhanNo ratings yet
- Comandos Navigator HuaweiDocument49 pagesComandos Navigator HuaweiClaudio Saez50% (4)
- Pharmacy SystemDocument63 pagesPharmacy Systemsurenderb63% (19)
- Iphone: Fuzzing and Payloads: Charlie MillerDocument66 pagesIphone: Fuzzing and Payloads: Charlie MillerAndresNo ratings yet
- OAN012309 N2000 Field Maintenance Lab Guide ISSUE1.00Document7 pagesOAN012309 N2000 Field Maintenance Lab Guide ISSUE1.00AndresNo ratings yet
- OBN208111 IManager N2000 BMS System Monitor ISSUE1.00Document18 pagesOBN208111 IManager N2000 BMS System Monitor ISSUE1.00AndresNo ratings yet
- OAN112309 N2000 Field Maintenance ISSUE1.00Document75 pagesOAN112309 N2000 Field Maintenance ISSUE1.00AndresNo ratings yet
- OBN208111 IManager N2000 BMS Introduction ISSUE2.00Document47 pagesOBN208111 IManager N2000 BMS Introduction ISSUE2.00AndresNo ratings yet
- 4 - S23&33&53 Caracteristicas de CAPA-2 ISSUE1.00Document29 pages4 - S23&33&53 Caracteristicas de CAPA-2 ISSUE1.00AndresNo ratings yet
- Certificate Testing ResultsDocument1 pageCertificate Testing ResultsNisarg PandyaNo ratings yet
- Who will buy electric vehicles Segmenting the young Indian buyers using cluster analysisDocument12 pagesWho will buy electric vehicles Segmenting the young Indian buyers using cluster analysisbhasker sharmaNo ratings yet
- Private Schools Provide Better EducationDocument2 pagesPrivate Schools Provide Better EducationcitraNo ratings yet
- The CongoDocument3 pagesThe CongoJoseph SuperableNo ratings yet
- Embankment PDFDocument5 pagesEmbankment PDFTin Win HtutNo ratings yet
- Theoretical and Actual CombustionDocument14 pagesTheoretical and Actual CombustionErma Sulistyo R100% (1)
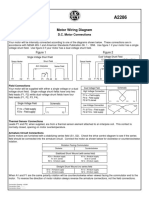
- Motor Wiring Diagram: D.C. Motor ConnectionsDocument1 pageMotor Wiring Diagram: D.C. Motor Connectionsczds6594No ratings yet
- Aleister Crowley and the SiriansDocument4 pagesAleister Crowley and the SiriansJCMNo ratings yet
- 40 26Document3 pages40 26Maxi452No ratings yet
- TutorialDocument324 pagesTutorialLuisAguilarNo ratings yet
- An Online ECG QRS Detection TechniqueDocument6 pagesAn Online ECG QRS Detection TechniqueIDESNo ratings yet
- Taking Back SundayDocument9 pagesTaking Back SundayBlack CrowNo ratings yet
- Juan Martin Garcia System Dynamics ExercisesDocument294 pagesJuan Martin Garcia System Dynamics ExercisesxumucleNo ratings yet
- Awakening The MindDocument21 pagesAwakening The MindhhhumNo ratings yet
- Ancient MesopotamiaDocument69 pagesAncient MesopotamiaAlma CayapNo ratings yet
- Nikola Tesla Was Murdered by Otto Skorzeny.Document12 pagesNikola Tesla Was Murdered by Otto Skorzeny.Jason Lamb50% (2)
- Elements of ClimateDocument18 pagesElements of Climateእኔ እስጥፍNo ratings yet
- The Apu Trilogy - Robin Wood PDFDocument48 pagesThe Apu Trilogy - Robin Wood PDFSamkush100% (1)
- Acuity Assessment in Obstetrical TriageDocument9 pagesAcuity Assessment in Obstetrical TriageFikriNo ratings yet
- Air Wellness QRSDocument2 pagesAir Wellness QRSapi-3743459No ratings yet
- Effect of Some Algal Filtrates and Chemical Inducers On Root-Rot Incidence of Faba BeanDocument7 pagesEffect of Some Algal Filtrates and Chemical Inducers On Root-Rot Incidence of Faba BeanJuniper PublishersNo ratings yet
- Convocation ProgramDocument125 pagesConvocation ProgramZirak TayebNo ratings yet
- Rotary Twin Scew Brochure UK HRDocument20 pagesRotary Twin Scew Brochure UK HRNguyễn Hữu DũngNo ratings yet
- LTE EPC Technical OverviewDocument320 pagesLTE EPC Technical OverviewCristian GuleiNo ratings yet
- Retaining Wall-Masonry Design and Calculation SpreadsheetDocument6 pagesRetaining Wall-Masonry Design and Calculation SpreadsheetfarrukhNo ratings yet
- Basic First AidDocument31 pagesBasic First AidMark Anthony MaquilingNo ratings yet
- Evolutionary PsychologyDocument10 pagesEvolutionary PsychologyShreya MadheswaranNo ratings yet
- A Fossil Hunting Guide To The Tertiary Formations of Qatar, Middle-EastDocument82 pagesA Fossil Hunting Guide To The Tertiary Formations of Qatar, Middle-EastJacques LeBlanc100% (18)
- Ro-Buh-Qpl: Express WorldwideDocument3 pagesRo-Buh-Qpl: Express WorldwideverschelderNo ratings yet
- Sibuyan Island ResiliencyDocument12 pagesSibuyan Island ResiliencyEndangeredSpeciesNo ratings yet