Professional Documents
Culture Documents
CCNA - EIGRP Authentication Configuration
Uploaded by
Jay MehtaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
CCNA - EIGRP Authentication Configuration
Uploaded by
Jay MehtaCopyright:
Available Formats
EIGRP Authentication Configuration
Routing protocols can be configured to prevent receiving false routing updates and EIGRP is no
exception. If you don’t use authentication and you are running EIGRP someone could try to form an
EIGRP neighbor adjacency with one of your routers and try to mess with your network…we don’t want
that to happen right?
EIGRP only offers MD5 authentication, there’s no plaintext authentication.
What does authentication offer us?
Your router will authenticate the source of each routing update packet that it will receive.
Prevents false routing updates from sources that are not approved.
Ignore malicious routing updates.
A potential hacker could be sitting on your network with a laptop running a router emulator, boot up a
Cisco router and try the following things:
Try to establish a neighbor adjacency with one of your routers and advertise junk routes.
Send malicious packets and see if you can drop the neighbor adjacency of one of your authorized
routers.
In order to configure EIGRP authentication we need to do the following:
Configure a key-chain
o Configure a key ID under the key-chain.
o Specify a password for the key ID.
o Optional: specify accept and expire lifetime for the key.
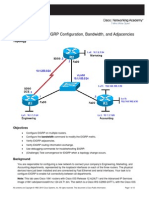
Let’s use two routers and see if we can configure EIGRP MD5 authentication:
The configuration for both routers is very basic:
Jack(config)#interface fastEthernet 0/0
Jack(config-if)#ip address 192.168.12.1 255.255.255.0
Jack(config)#router eigrp 12
Jack(config-router)#network 192.168.12.0
John(config)#interface fastEthernet 0/0
John(config-if)#ip address 192.168.12.2 255.255.255.0
John(config)#router eigrp 12
John(config-router)#network 192.168.12.0
EIGRP Authentication Configuration CNE - MAHER ABDELSHKOUR
The first thing we need to configure is a key-chain:
I called mine “KingKong” but it can be different on both routers, it doesn’t matter. The Key ID is a value
that has to match on both routers and the key-string is the password which has to match of course.
Jack(config)#key chain KingKong
Jack(config-keychain)#key 1
Jack(config-keychain-key)#key-string Banana
Jack(config)#interface fastEthernet 0/0
Jack(config-if)#ip authentication mode eigrp 12 md5
Jack(config-if)#ip authentication key-chain eigrp 12 KingKong
First you have to create the keychain and then you need to activate it on the interface. The “12” is the AS
number of EIGRP. The configuration on router John is exactly the same.
John#debug eigrp packets
EIGRP Packets debugging is on
(UPDATE, REQUEST, QUERY, REPLY, HELLO, IPXSAP, PROBE, ACK, STUB,
SIAQUERY, SIAREPLY)
John# EIGRP: FastEthernet0/0: ignored packet from 192.168.12.1, opcode
= 5 (authentication off or key-chain missing)
You can check if your configuration is correct by using debug eigrp packets. You can see that we received
a packet with MD5 authentication but I didn’t enable MD5 authentication yet on router John.
Let’s fix it:
John(config)#key chain KingKong
John(config-keychain)#key 1
John(config-keychain-key)#key-string Banana
John(config)#interface fastEthernet 0/0
John(config-if)#ip authentication mode eigrp 12 md5
John(config-if)#ip authentication key-chain eigrp 12 KingKong
EIGRP Authentication Configuration CNE - MAHER ABDELSHKOUR
Right away I can see that the EIGRP neighbor adjacency is working:
John# %DUAL-5-NBRCHANGE: IP-EIGRP(0) 12: Neighbor 192.168.12.1
(FastEthernet0/0) is up: new adjacency
What if I entered a wrong key-string?
Jack(config)#key chain KingKong
Jack(config-keychain)#key 1
Jack(config-keychain-key)#key-string Apples
Let’s see if KingKong likes apples…
John# EIGRP: pkt key id = 1, authentication mismatch
You will see the message above in the debug output on router John. At least it tells us that key 1 is the one
with the error.
You will see the message above in the debug output on router John. At least it tells us that key 1 is the one
with the error.
If you want to spice it up a bit you can set an accept and expire lifetime on keys. The idea behind this is
that you can have keys that are only valid for a day, a week, a month or something else. Do you want to use
this in real life? It might enhance security but it also makes maintenance a bit more complex…
Before you configure keys with a limited lifetime make sure you set the correct time and date. You can do
this manually on each router but it’s better to use a NTP (Network Time Protocol) server so all the routers
have the same time/date.
EIGRP Authentication Configuration CNE - MAHER ABDELSHKOUR
You might also like
- 100 ChatGPT Programming PromptsDocument15 pages100 ChatGPT Programming Promptsdb118100% (1)
- HTML5 Visual Cheat Sheet (Reloaded)Document1 pageHTML5 Visual Cheat Sheet (Reloaded)Antonio Lupetti100% (7)
- Analog Man Guide To Vintage Effects EbookDocument3 pagesAnalog Man Guide To Vintage Effects EbookEmmanuel Ramirez100% (1)
- CCENT Cheat SheetDocument18 pagesCCENT Cheat SheetJim D'FotoNo ratings yet
- Cisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3From EverandCisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3No ratings yet
- Misra C 2012 Amd-1Document29 pagesMisra C 2012 Amd-1kaesarxNo ratings yet
- E2 Lab 1 5 2Document11 pagesE2 Lab 1 5 2Ninja NuggetNo ratings yet
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationFrom EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNo ratings yet
- Router Switch CommandsDocument121 pagesRouter Switch CommandsIonel GherasimNo ratings yet
- Step-by-Step Configuration of Cisco Routers: Step1: Configure Access PasswordsDocument7 pagesStep-by-Step Configuration of Cisco Routers: Step1: Configure Access PasswordsLeworkDagne100% (1)
- Xlwings and ExcelDocument19 pagesXlwings and ExcelHoangdh0% (1)
- Site to Site VPN CLI Setup on GNS3Document6 pagesSite to Site VPN CLI Setup on GNS3dayno_majNo ratings yet
- ISP Lab Tutorial - GNS3Document19 pagesISP Lab Tutorial - GNS3Ceh0% (1)
- (CCNA) Cisco Commands Cheat Sheet #3Document8 pages(CCNA) Cisco Commands Cheat Sheet #3researcherjackNo ratings yet
- A Quick Guide To Android App Reversing: What Is Byte CodeDocument2 pagesA Quick Guide To Android App Reversing: What Is Byte Code51- Nadir AkramNo ratings yet
- Router Switch CommandscDocument128 pagesRouter Switch CommandscIonel GherasimNo ratings yet
- Configure EIGRP Authentication LAN WANDocument3 pagesConfigure EIGRP Authentication LAN WANRicardito Francisco Mena LagosNo ratings yet
- Eigrp AuthenticationDocument4 pagesEigrp AuthenticationzakirmmughalNo ratings yet
- Ping TracerouteDocument19 pagesPing TracerouteYe Zeiya SheinNo ratings yet
- Exercise - 9 - EIGRP - AuthenticationDocument2 pagesExercise - 9 - EIGRP - AuthenticationyashitaNo ratings yet
- Eigrp AuthenticationDocument3 pagesEigrp AuthenticationAbhishek KumarNo ratings yet
- Lab EIGRP 2Document15 pagesLab EIGRP 2Danny Ricce EnriqueNo ratings yet
- Ping and Traceroute UnderstandingDocument22 pagesPing and Traceroute Understandingdavekrunal46No ratings yet
- Understanding The Ping and Traceroute CommandsDocument21 pagesUnderstanding The Ping and Traceroute Commandsadramat1085No ratings yet
- CCIE Security IGP, EGP AuthenticationDocument26 pagesCCIE Security IGP, EGP AuthenticationMd. Rashedul AlamNo ratings yet
- Newclass Docs v.245 - RewiringDocument2 pagesNewclass Docs v.245 - RewiringJamesNo ratings yet
- CCNA Certification EIGRP Configuration Lab SimulationDocument8 pagesCCNA Certification EIGRP Configuration Lab Simulationergu vfuko fghuiNo ratings yet
- Lab 13.8.1 Configuring A Site-To-Site Ipsec VPN Using Pre-Shared KeysDocument6 pagesLab 13.8.1 Configuring A Site-To-Site Ipsec VPN Using Pre-Shared KeysKishore Reddy KandiNo ratings yet
- EIGRPDocument16 pagesEIGRPIndika RodrigoNo ratings yet
- 19-04 EIGRP - The Enhanced Interior Gateway Routing ProtocolDocument14 pages19-04 EIGRP - The Enhanced Interior Gateway Routing Protocolrichard akpagniNo ratings yet
- EIGRPDocument6 pagesEIGRPjayanandjaiNo ratings yet
- Packet Tracer - Configuring Basic Eigrp With Ipv4: ObjectivesDocument2 pagesPacket Tracer - Configuring Basic Eigrp With Ipv4: ObjectivesMehdi SultaniNo ratings yet
- Understanding The Ping and Traceroute Commands: Document ID: 12778Document20 pagesUnderstanding The Ping and Traceroute Commands: Document ID: 12778anadiguptaNo ratings yet
- Configure VPN on TP-LINK Routers with IPsec VPN ClientsDocument64 pagesConfigure VPN on TP-LINK Routers with IPsec VPN ClientssuadmujicNo ratings yet
- Cisco IOS Security TemplateDocument10 pagesCisco IOS Security TemplateshankerunrNo ratings yet
- S2S Ikev2 Configure-AsaDocument9 pagesS2S Ikev2 Configure-Asahesenzade38No ratings yet
- Chapter 2 Lab 2-3, EIGRP For IPv6Document31 pagesChapter 2 Lab 2-3, EIGRP For IPv6leoNo ratings yet
- Lab9,10: Router Configuration Using Packet TracerDocument28 pagesLab9,10: Router Configuration Using Packet TracerSanchitMishraNo ratings yet
- OSPF Authentication Password and MD5 ExplainedDocument13 pagesOSPF Authentication Password and MD5 ExplainedjayshuklatrainerNo ratings yet
- Networkforyou: Email Us: Whatsapp Us: +918143809578Document4 pagesNetworkforyou: Email Us: Whatsapp Us: +918143809578Khaing myal HtikeNo ratings yet
- CCNA - Lesson3Document6 pagesCCNA - Lesson3Ali OMEIZANo ratings yet
- Eigrp LabDocument18 pagesEigrp LabNuwan HemanthaNo ratings yet
- Configure Basic Router Settings LabDocument11 pagesConfigure Basic Router Settings Labumang patnaikNo ratings yet
- Troubleshoot Common EIGRP Issues - CiscoDocument36 pagesTroubleshoot Common EIGRP Issues - CiscoBheemesh ChowdaryNo ratings yet
- Verificacion de NatDocument10 pagesVerificacion de NatJuanan PalmerNo ratings yet
- Lab 2-1 EIGRP Configuration, Bandwidth, and Adjacencies: Learning ObjectivesDocument12 pagesLab 2-1 EIGRP Configuration, Bandwidth, and Adjacencies: Learning ObjectivesSergiy KalmukNo ratings yet
- Somesh Kale Roll No 630 SICDocument66 pagesSomesh Kale Roll No 630 SICSomesh kaleNo ratings yet
- HSRP TshootDocument5 pagesHSRP TshootGROUP SOFT GROUP SOFTNo ratings yet
- FlexVPN Site-To-Site Configuration ExampleDocument8 pagesFlexVPN Site-To-Site Configuration Examplesoumen1977No ratings yet
- Static Route Tracking Using IP SLADocument3 pagesStatic Route Tracking Using IP SLALucci SinghNo ratings yet
- Network Basic Concepts: 1.vlan Create and Check Command "Show Vlan Brief"Document3 pagesNetwork Basic Concepts: 1.vlan Create and Check Command "Show Vlan Brief"amiraliNo ratings yet
- Implementing EIGRPDocument8 pagesImplementing EIGRPanupkumarsaha112No ratings yet
- CNs-Lab 9-Cisco Switch ConfigurationDocument8 pagesCNs-Lab 9-Cisco Switch ConfigurationHemin EssaNo ratings yet
- New Microsoft Word DocumentDocument3 pagesNew Microsoft Word Documentcharles mainaNo ratings yet
- Ccnpv6 Route Lab2-1 Eigrp ConfigurationDocument13 pagesCcnpv6 Route Lab2-1 Eigrp ConfigurationJulio Anibal Ochoa Marroquin0% (1)
- 8-Troubleshooting EIGRP RoutingDocument13 pages8-Troubleshooting EIGRP Routingmansoorali_afNo ratings yet
- Ccnpv6 Route Lab2-1 Eigrp Config StudentDocument13 pagesCcnpv6 Route Lab2-1 Eigrp Config Studentadncl2No ratings yet
- CCNPv7 ROUTE Lab2-4 EIGRP-Named-Configuration InstructorDocument23 pagesCCNPv7 ROUTE Lab2-4 EIGRP-Named-Configuration InstructorNiko SB FSNo ratings yet
- 1.1.4.6 Lab - Configuring Basic Router Settings With IOS CLIDocument15 pages1.1.4.6 Lab - Configuring Basic Router Settings With IOS CLIJuan S. MorejónNo ratings yet
- Ccnpv6 Route Lab2-1 Eigrp Config Student FormDocument13 pagesCcnpv6 Route Lab2-1 Eigrp Config Student FormDany J. MarroquinNo ratings yet
- Packet Tracer - Configure Initial Router Settings: ObjectivesDocument8 pagesPacket Tracer - Configure Initial Router Settings: ObjectivesMENDOZA GASPAR PAOLA Ingeniería en Sistemas ComputacionalesNo ratings yet
- Tyit Sic Manual 2023-24Document56 pagesTyit Sic Manual 2023-24newvinayakprintsNo ratings yet
- Frame Relay Configuration PracticeDocument9 pagesFrame Relay Configuration PracticesovannlyNo ratings yet
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
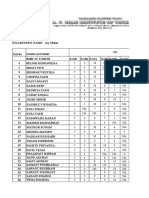
- BE-EXTC Students' Performance in Wireless Networks Unit TestDocument12 pagesBE-EXTC Students' Performance in Wireless Networks Unit TestJay MehtaNo ratings yet
- Wi MaxDocument26 pagesWi MaxJay MehtaNo ratings yet
- CCNA EIGRP SummarizationDocument2 pagesCCNA EIGRP SummarizationJay MehtaNo ratings yet
- Report FormatDocument5 pagesReport FormatJay MehtaNo ratings yet
- MATLAB - Programs On Control SystemDocument16 pagesMATLAB - Programs On Control SystemJay MehtaNo ratings yet
- MATLAB Control Systems Lab ManualDocument104 pagesMATLAB Control Systems Lab ManualRavi Umrao100% (2)
- Golden GateDocument69 pagesGolden GateabidouNo ratings yet
- LaTeX BookDocument1 pageLaTeX BookIndian Academy of Scientific and Engineering ResearchNo ratings yet
- Ajax For MobilityDocument2 pagesAjax For MobilitymachinelearnerNo ratings yet
- Student Email Setup GuideDocument6 pagesStudent Email Setup GuidedinhchungxdNo ratings yet
- Line Following Zumo Robot Programmed With SimulinkDocument19 pagesLine Following Zumo Robot Programmed With SimulinkNiravNo ratings yet
- M.E (Or) QBDocument21 pagesM.E (Or) QBkeerthi_sm180% (1)
- 8086 Lab ProgramsDocument138 pages8086 Lab Programsgraciousparul95% (19)
- Chapter 1 - Principles of Programming LangugesDocument37 pagesChapter 1 - Principles of Programming LangugesdileepNo ratings yet
- DBMS Exam Questions Cover ER Diagrams, Normalization, Transactions, IndexingDocument5 pagesDBMS Exam Questions Cover ER Diagrams, Normalization, Transactions, IndexingRajib SarkarNo ratings yet
- Binary Search TreeDocument47 pagesBinary Search TreeAman Pushpinder BirdiNo ratings yet
- R Through Excel - A Spreadsheet Interface - ReviewDocument3 pagesR Through Excel - A Spreadsheet Interface - ReviewinsightsxNo ratings yet
- Beyond ERP: Dept. of Information Systems SVKM's NMIMS University 1Document21 pagesBeyond ERP: Dept. of Information Systems SVKM's NMIMS University 1devesh_mendiratta_61No ratings yet
- HP Comware Lab (HCL) - Windows User Guide - v1.0Document26 pagesHP Comware Lab (HCL) - Windows User Guide - v1.0paul andradeNo ratings yet
- Y1npi6v: (Other Students Have To Answer Any Three Questions From Section A)Document3 pagesY1npi6v: (Other Students Have To Answer Any Three Questions From Section A)36rajnee kantNo ratings yet
- Time Response Analysis NotesDocument3 pagesTime Response Analysis NotesGilbert SigalaNo ratings yet
- Overview of Payroll SystemDocument7 pagesOverview of Payroll SystemGibson MelNo ratings yet
- Create Eye-Catching Posters in PowerPointDocument17 pagesCreate Eye-Catching Posters in PowerPointSyafiq FiqNo ratings yet
- Grason-Stadler GSI Tympstar Manual V1 Rev CDocument285 pagesGrason-Stadler GSI Tympstar Manual V1 Rev CHabiB-BoyGuysNo ratings yet
- Akash ResumeDocument4 pagesAkash ResumeAkash MukherjeeNo ratings yet
- Tech Adroit: Software & Studios LLPDocument18 pagesTech Adroit: Software & Studios LLPDeep SharmaNo ratings yet
- Cisco Ipv6 TransitionDocument34 pagesCisco Ipv6 TransitionDuong PhamNo ratings yet
- Tabel Entrian SDM DinkesDocument71 pagesTabel Entrian SDM Dinkesfredian siskaNo ratings yet