Professional Documents
Culture Documents
Enemy of The State of Privacy
Uploaded by
Robert IngOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Enemy of The State of Privacy
Uploaded by
Robert IngCopyright:
Available Formats
Enemy of the State of Privacy
By Robert Ing, DSc, FAPSc, CPO
In the 1998 movie, “Enemy of the State”, actor Will Smith’s personal
privacy is invaded by his own government using high technology
devices planted in his home, office and even on his person. Sounds far
fetched? The technology does exist to do everything portrayed in the
movie and much more. The only difference between the movie and
real life is that unlike the movie where government agents physically
entered the home and office of Smith, this is not necessary to breach
the privacy of any citizen.
If you are like most individuals, you have unknowingly permitted
yourself to be tracked, documented and your privacy breached in
exchange for living a life of convenience. When you sign applications
and agreements for your credit cards, bank accounts, vehicle leases
and mortgages have you really read the fine print? The fine print in
most cases states that you give your permission to have your personal
information collected by, “exchanged” with, and even sold to third
parties throughout the course of your business dealings. Do you
belong to a reward points or discount program? The fine print of the
agreement may allow program operators to track your spending habits
(where and what you buy), allow them to share and even sell this
information to third parties and put you on mailing and telephone
solicitation lists of companies you’ve never heard of.
While this may seem more of an inconvenience than an invasion of
privacy consider the case of Mr. X. Mr. X had signed up for a reward
Dr. Robert Ing is a forensic points program linked to his credit card. This meant everywhere and
scientist, broadcaster and
author. An internationally every time he used his credit card he would get points for all of his
acclaimed forensic transactions to be used towards vacations, gasoline and a new car.
intelligence specialist, he
Mr. X was in line for a promotion with his firm, a major multi-national
has traveled the world
on behalf of the interests of corporation. As part of the selection process he would have to submit
governments and major to a background check and security clearance. The firm conducting
corporations. Dr. Ing has
appeared on major North
the check performed what is known as a character lifestyle check and
American broadcast news through their sources were able to obtain a record of Mr. X’s spending
networks on the issues of habits over a two year period as documented by the reward points
forensic intelligence,
espionage risk
program he had enrolled in. It was noted by an entry on his spending
management, privacy, record that he had on one occasion frequented a small retail
identity theft, electronic establishment whose operator had been convicted of child
surveillance and Internet
crime.
pornography. As a result, Mr. X was not given a clearance for the
promotion and was later released from the firm’s employ. Further
For more articles by investigation found that the establishment in question was a
Dr. Robert Ing visit
www.drroberting.com
convenience store chain where Mr. X purchased a box of chocolates
for his wife’s birthday. This was the one and only documented time he
had entered this establishment.
Similar tracking of individuals is also done via their personal computers.
In this case, most individuals are all too quick to breeze through the
Terms of Service posted on websites and in software and as a result
surrender their privacy all too easily. People who do any form of online
commerce from ordering merchandise off of a website, to online
banking and stock trading are often tracked by having small files placed
on their computers without their knowledge, known as cookies to
gather and track personal and personal preference information. By
accepting the Terms of Service users agree to have the cookies placed
on their computer. Although the word “cookie” may not be specifically
used in the text of the document. Cookies, also known in the computer
security world as Spyware may provide information about the computer
owners name, address, telephone number and e-mail address all
culled from information provided by the users themselves when they
first registered their computer operating system and software.
Additional information may be obtained on the type of software and
computer used, websites visited, Internet searches performed and total
time spent at the computer.
As well, Internet Service Providers and e-mail providers may also keep
tabs on users by monitoring account activity. Account activity of this
nature would include received and sent e-mail addresses, websites
visited and an inventory of all of the software installed on the computer.
Information obtained from the use of Spyware and the monitoring of
account activity are routinely justified in the corporate world as
processes designed to selectively send specific advertising offers that
users may be interested in based on their “tracked” previous purchases
or activity and to ensure the quality of services delivered to users by
monitoring user access activity.
Dr. Robert Ing is a forensic
scientist, broadcaster and
author. An internationally
However, information accessed by or sold to the wrong hands could be
acclaimed forensic devastating to an individual. An example of this occurred when Ms. Y,
intelligence specialist, he a grade school teacher had her name come up on an e-mail mailing list
has traveled the world
on behalf of the interests of
associated with a contraband prescription drugs operation that had
governments and major been seized during a raid. Although it had been later found that Ms. Y,
corporations. Dr. Ing has like many others on the list were simply targeted victims of a mass e-
appeared on major North
American broadcast news
mail solicitation list, the fact that information from her e-mail account
networks on the issues of provider indicated the receipt of a message from the operation and a
forensic intelligence, sent reply message that could have raised further suspicion. However,
espionage risk
management, privacy,
given that the e-mail activity log did not store the body of the message
identity theft, electronic and Ms. Y’s explanation of the reply simply being a request to be
surveillance and Internet removed from the mailing list seemed credible given no other
crime.
communiqués were logged. More importantly, Ms. Y would have never
For more articles by been placed on the list if the health related website she registered with
Dr. Robert Ing visit as a user had not sold her information to an e-mail marketing firm who
www.drroberting.com
later re-sold it to the contraband drugs operator.
While most may find comfort in privacy laws directed towards protecting
personal information collected by firms in the course of doing business
with and servicing their customers, there is little refuge or comfort when
an individual is confronted with accepting the terms of the fine print in
their user agreements or to be forever without service.
So you say you can’t imagine your life without your cellular telephone. If
you are like most people, you keep your cellular on as you go about your
business every day. Did you know that using just the signal from your
cellular telephone and its unique electronic identification number that your
whereabouts within a 4 city block radius can be easily time stamped to
the second, dated and determined. This capability of passively tracking
and recording the whereabouts of individuals has been effectively used
as supporting evidence to place or not to place suspects at or near the
scenes of crimes. Call records of cellular telephones have also been
instrumental in keeping people in and out of jail as well when it comes to
alibis. The same holds true for the detailed billing feature of monthly
cellular bills, you know . . . that listing of date, time and telephone number
called or received. The detailed billing feature has been the demise of
many an unfaithful spouse. As one U.S. intelligence official once said,
“… cellular telephones are one of the greatest surveillance advancements
of our time. They enable unobtrusive surveillance of practically anyone at
anytime.”
So perhaps you’re thinking you should just turn your cellular telephone off
and maybe spend some time just taking a walk to the mall and having a
quiet cup of coffee in the food court. Look up, way up! Do you see those
shiny black domes in the ceiling, or those boxes with black glass or the
obvious camera in a white or grey box hanging off of a post? You see
Dr. Robert Ing is a forensic them on street corners, in malls, office buildings, transit stations and
scientist, broadcaster and
author. An internationally highways. You are under surveillance and your presence is being
acclaimed forensic recorded, dated and time stamped. Security video camera surveillance is
intelligence specialist, he more widespread in major cities than the public thinks. If you live or work
has traveled the world
on behalf of the interests of in downtown Montreal, Ottawa, Toronto or Vancouver a typical one way
governments and major trip will cause your image to be recorded an average of 9 times by 7
corporations. Dr. Ing has independent video surveillance systems. 85% of video surveillance
appeared on major North
American broadcast news systems are owned and operated by corporations for use on their
networks on the issues of property such as malls and office buildings, with no legislated guidelines
forensic intelligence, on what they can do with this recorded surveillance data. Security video
espionage risk
management, privacy, recordings are kept an average of 3 months before they are erased or
identity theft, electronic purged.
surveillance and Internet
crime.
For more articles by
Dr. Robert Ing visit
www.drroberting.com
To get away from it all you may consider a quiet drive in the country, far
removed from the hustle, the bustle and those privacy invaders but . . .
you can run but you can’t hide. Most new vehicles come equipped with a
safety option that allows you to be in instant live two-way communication
with a dispatch centre should you have an accident or just get lost. This
service will not only talk you through your emergency but also unlock your
doors if you are locked out and will even pinpoint the exact location of
your vehicle using GPS satellite tracking if it is stolen. GPS satellite
tracking is the same technology used by the military and just like military
targets; your vehicle’s location can be determined within 3 metres.
Similar in-vehicle security only systems also use GPS to track and locate
stolen vehicles. This technology is not only available as an option when
you purchase your new or used vehicle but is now standard equipment on
most vehicles you may rent for that weekend getaway.
Although the safety and security benefits of these devices are numerous,
so are the privacy risks. One area of concern is that the in-vehicle two-
way communication feature can be activated by the dispatch centre
without the vehicle occupants being aware that every word they say can
be monitored and recorded. Moving vehicles and their parked locations
can also be determined without any occupant knowledge. During the
past few years there have been documented cases where law
enforcement agencies have utilized such means as an aid to
conventional surveillance methods.
The real ability to put an average citizen under surveillance, collect
personal information and invade privacy used to be the sole domain of
governments about 25 years ago. However, with the accessibility to, and
affordability of technology, the ability albeit in a limited way to track and
Dr. Robert Ing is a forensic create dossiers on individuals by corporate snoops and even private
scientist, broadcaster and
author. An internationally individuals is an easy task. Bearing in mind that unlike governments,
acclaimed forensic private corporations and individuals acting alone or on behalf of someone
intelligence specialist, he else are not bound by such stringent controls to protect the democratic
has traveled the world
on behalf of the interests of rights and freedoms of citizens. While privacy and personal information
governments and major laws do dictate how businesses must store and disseminate information
corporations. Dr. Ing has pertaining to their customers, loopholes are easily created by fine print
appeared on major North
American broadcast news user agreements and the acceptance by the potential customer of the
networks on the issues of user agreement is demanded in order to obtain service from the business
forensic intelligence, in question.
espionage risk
management, privacy,
identity theft, electronic
surveillance and Internet
crime.
For more articles by
Dr. Robert Ing visit
www.drroberting.com
Unlike governments, private corporations and individuals are able to
operate in grey or open areas of the law in collecting and comparing
information from other private corporations and individuals with minimal
checks and balances. Furthermore, when one considers that despite
legislation and codes of conduct, the bottom line is that there will always
be someone who knows someone, who knows someone else who can
obtain the required information through a low level contact with access to
the requested information. If this sounds funny, don’t laugh because any
street savvy privateer will reluctantly admit that this is how things really
get done.
Personal privacy must start and stop with the individual. You must
carefully review service agreements before accepting them. Is the
service, product or convenience you are interested in really worth giving
up some of your privacy? Do you really want to give someone the
potential ability to track your movements on a daily basis?
Just a final thought . . . don’t be surprised if a total stranger comes up to
you one day and can tell you what colour you prefer in underwear, where
you shop, that you take the long way home and that you would be able to
call your mother more often if you didn’t stay so long on your computer.
Only you have the power to not let this happen.
About the Author
Dr. Robert Ing is a forensic intelligence specialist and has appeared on
North American news networks on the issues of technology crime,
Dr. Robert Ing is a forensic computer security, privacy and identity theft.
scientist, broadcaster and
author. An internationally For more articles by Dr. Robert Ing please visit www.drroberting.com
acclaimed forensic
intelligence specialist, he
has traveled the world
on behalf of the interests of Copyright © 2005-2011 Dr. Robert Ing, www.drroberting.com
governments and major
corporations. Dr. Ing has
appeared on major North
American broadcast news Permission is granted to publish this article electronically or in print, free
networks on the issues of
forensic intelligence, of charge, as long as the article appears in its entirety,
espionage risk
management, privacy, full credit is given to the author and a link or reference to the author's
identity theft, electronic webpage www.drroberting.com is provided.
surveillance and Internet
crime.
For more articles by
Dr. Robert Ing visit
www.drroberting.com
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5795)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- List of MarketingDocument78 pagesList of MarketingMohamad IchwanNo ratings yet
- 13 Satanic Rules of BusinessDocument2 pages13 Satanic Rules of BusinessRobert Ing100% (1)
- Leklai Amulets by Robert IngDocument3 pagesLeklai Amulets by Robert IngRobert Ing100% (1)
- Selling Your Soul To Satan by Robert IngDocument5 pagesSelling Your Soul To Satan by Robert IngRobert Ing25% (4)
- The Chinese Divining Pendulum by Robert IngDocument27 pagesThe Chinese Divining Pendulum by Robert IngRobert Ing100% (9)
- The Canadian Military Radio Frequency Guide by Robert IngDocument20 pagesThe Canadian Military Radio Frequency Guide by Robert IngRobert Ing100% (1)
- Production of BiodieselDocument49 pagesProduction of Biodieselteja100% (1)
- Human Skull Mapping ReferenceDocument5 pagesHuman Skull Mapping ReferenceRobert IngNo ratings yet
- Iron Coffin Nail PendulumDocument2 pagesIron Coffin Nail PendulumRobert Ing100% (1)
- Basic Accident InvestigationDocument40 pagesBasic Accident InvestigationRobert Ing100% (4)
- Atrumus Parietis Libri - The Dark Book of Curse, Jinx and Spell AnnihilationDocument16 pagesAtrumus Parietis Libri - The Dark Book of Curse, Jinx and Spell AnnihilationRobert Ing42% (12)
- Common Satanic Symbols and Their Meaning by Robert IngDocument11 pagesCommon Satanic Symbols and Their Meaning by Robert IngRobert Ing100% (5)
- The Novice's Guide To Scrying by Robert IngDocument4 pagesThe Novice's Guide To Scrying by Robert IngRobert Ing100% (6)
- The Art of Forensic Detection and Sherlock Holmes by Robert IngDocument5 pagesThe Art of Forensic Detection and Sherlock Holmes by Robert IngRobert IngNo ratings yet
- Epsilon Range Bomba HorizontalDocument8 pagesEpsilon Range Bomba HorizontalsalazarafaelNo ratings yet
- No. 3 - Republic vs. DiazDocument7 pagesNo. 3 - Republic vs. DiazMark Gabriel MarangaNo ratings yet
- Notice: Customhouse Broker License Cancellation, Suspension, Etc.Document2 pagesNotice: Customhouse Broker License Cancellation, Suspension, Etc.Justia.comNo ratings yet
- Is 3073Document34 pagesIs 3073rohan sharmaNo ratings yet
- L - HRF22B0301 - Hose & Pulley Block (ZM, METRIC)Document5 pagesL - HRF22B0301 - Hose & Pulley Block (ZM, METRIC)Gustavo RodriguezNo ratings yet
- The Influence of The Transformational LeaderDocument9 pagesThe Influence of The Transformational Leaderkenmuira100% (1)
- 3 CBLSF 50 HDocument6 pages3 CBLSF 50 HNaz LunNo ratings yet
- Treatment of Dairy Waste Water Using Adsorbents From Solid WasteDocument7 pagesTreatment of Dairy Waste Water Using Adsorbents From Solid WasteIJRASETPublicationsNo ratings yet
- 09-03-2023 Ramadhan - Small PDFDocument13 pages09-03-2023 Ramadhan - Small PDFAmmarah RamnarainNo ratings yet
- Ten Rules of NetiquetteDocument11 pagesTen Rules of NetiquetteAriel CancinoNo ratings yet
- SCADA Generic Risk Management FrameworkDocument49 pagesSCADA Generic Risk Management FrameworkAnak PohonNo ratings yet
- Basic Principles of Immunology: Seminar OnDocument43 pagesBasic Principles of Immunology: Seminar OnDr. Shiny KajalNo ratings yet
- GROZ Tools & Equipment 2018Document3 pagesGROZ Tools & Equipment 2018ayush bansalNo ratings yet
- Thermo King CG 2000Document155 pagesThermo King CG 2000Connie TaibaNo ratings yet
- Amended Formal ComplaintDocument87 pagesAmended Formal ComplaintWXYZ-TV Channel 7 DetroitNo ratings yet
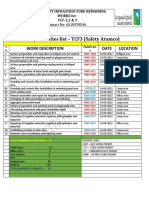
- Daily Activities List - TCF3 (Safety Aramco) : Work Description Date LocationDocument2 pagesDaily Activities List - TCF3 (Safety Aramco) : Work Description Date LocationSheri DiĺlNo ratings yet
- Picasso OperatingInstructions Manual 211018 WEBDocument27 pagesPicasso OperatingInstructions Manual 211018 WEBBill McFarlandNo ratings yet
- Autodesk Inventor Practice Part DrawingsDocument25 pagesAutodesk Inventor Practice Part DrawingsCiprian Fratila100% (1)
- Arti ResearchDocument10 pagesArti Researcharti nongbetNo ratings yet
- Modern Theory of Interest: IS-LM CurveDocument36 pagesModern Theory of Interest: IS-LM CurveSouvik DeNo ratings yet
- Save Energy Save EarthDocument2 pagesSave Energy Save EarthMega Ayu100% (2)
- Ge Washing Machine ManualDocument52 pagesGe Washing Machine Manuallillith1723No ratings yet
- Vol 17 No 3 and No 4 Fort Laramie and The Sioux War of 1876Document19 pagesVol 17 No 3 and No 4 Fort Laramie and The Sioux War of 1876Лазар СрећковићNo ratings yet
- Process and Inter-Process Systems For All Industries.: Cleaning Validation: An Overall PerspectiveDocument7 pagesProcess and Inter-Process Systems For All Industries.: Cleaning Validation: An Overall PerspectiveDesarrollo de Colecciones IVIC-BMRNo ratings yet
- Raul C. Cosare v. Broadcom Asia Inc. and Dante ArevaloDocument4 pagesRaul C. Cosare v. Broadcom Asia Inc. and Dante ArevaloRam Migue SaintNo ratings yet
- Corrugated Horn AntennasDocument4 pagesCorrugated Horn AntennasmiusayNo ratings yet
- BS en 12285-1-2003 (2006)Document162 pagesBS en 12285-1-2003 (2006)dahzahNo ratings yet
- Maxillofacial Trauma and Management - Dental Ebook & Lecture Notes PDF Download (Studynama - Com - India's Biggest Website For BDS Study Material Downloads)Document24 pagesMaxillofacial Trauma and Management - Dental Ebook & Lecture Notes PDF Download (Studynama - Com - India's Biggest Website For BDS Study Material Downloads)Vinnie SinghNo ratings yet