Professional Documents
Culture Documents
HW 2
Uploaded by
adnannoor0 ratings0% found this document useful (0 votes)
35 views1 pageLate submission will be penalized at 10% per day. Both hardcopy and softcopy are required (India students and remote students only need to submit softcopy.
Original Description:
Original Title
hw2
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentLate submission will be penalized at 10% per day. Both hardcopy and softcopy are required (India students and remote students only need to submit softcopy.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
35 views1 pageHW 2
Uploaded by
adnannoorLate submission will be penalized at 10% per day. Both hardcopy and softcopy are required (India students and remote students only need to submit softcopy.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
CS 550 HW#2
Name (please print)_____________________________________________________________
Instructions:
Due date: 11:25AM on Thursday, 03/24/11
This is individual written assignment; any information outside the lecture notes and text book
should be cited.
Both hardcopy and softcopy are required (India students and remote students only need to
submit softcopy). Please drop your hardcopy to TA’s mailbox (2nd floor of computer science
department), and submit the softcopy to “Digital Drop Box” on the Blackboard.
Name your file as this rule: “LastName_FirstName_*HW or PA number+”. E.g. “John_Doe_HW2”.
(HW for Written Assignment, PA for Programming Assignment).
For all programming assignments and projects, please submit the hardcopy of your
documentation only. You don't need to submit the hardcopy of your source code. In the
meantime, please zip all files (source code, documentation and etc.) and submit it to BB.
Late submission will be penalized at 10% per day.
3.1. Q: In this problem you are to compare reading a file using a single-threaded file server and a
multithreaded server. It takes 15 msec to get a request for work, dispatch it, and do the rest of the necessary
processing, assuming that the data needed are in a cache in main memory. If a disk operation is needed, as is
the case one-third of the time, an additional 75 msec is required, during which time the thread sleeps. How
many requests/sec can the server handle if it is single threaded? If it is multithreaded?
3.11. Q: Sketch the design of a multithreaded server that supports multiple protocols using sockets as its
transport-level interface to the underlying operating system.
5.5. Q: Outline an efficient implementation of globally unique identifiers.
5.21. Q: Consider a distributed file system that uses per-user name spaces. In other words, each user has his
own, private name space. Can names from such name spaces be used to share resources between two
different users?
6.4. Q: When a node synchronizes its clock to that of another node, it is generally a good idea to take
previous measurements into account as well. Why? Also, give an example of how such past readings could be
taken into account.
6.7. Q: Consider a communication layer in which messages are delivered only in the order that they were
sent. Give an example in which even this ordering is unnecessarily restrictive.
6.9. Q: In the centralized approach to mutual exclusion (Fig. 6-0), upon receiving a message from a process
releasing its exclusive access to the resources it was using, the coordinator normally grants permission to the
first process on the queue. Give another possible algorithm for the coordinator.
7.13. Q: When using a lease, is it necessary that the clocks of a client and the server, respectively, are tightly
synchronized?
7.14. Q: We have stated that totally ordered multicasting using Lamport's logical clocks does not scale.
Explain why.
7.18. Q: For active replication to work in general, it is necessary that all operations be carried out in the same
order at each replica. Is this ordering always necessary?
1 CS550 Spring 2011 – HW#2
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Broadcast Storm Problem in A Mobile Ad Hoc NetworkDocument12 pagesThe Broadcast Storm Problem in A Mobile Ad Hoc NetworkadnannoorNo ratings yet
- Parallel Algorithms: Peter Harrison and William KnottenbeltDocument65 pagesParallel Algorithms: Peter Harrison and William KnottenbeltadnannoorNo ratings yet
- Replace This Line With Your Paper Identification Number (Double-ClickDocument6 pagesReplace This Line With Your Paper Identification Number (Double-ClickedwinriNo ratings yet
- Speed Density (SD) MAP Vs Mass Air MAF-which Is BetterDocument3 pagesSpeed Density (SD) MAP Vs Mass Air MAF-which Is BetteradnannoorNo ratings yet
- Stronghold Crusader Extreme HD (V1.3e) - Readme: EnglishDocument18 pagesStronghold Crusader Extreme HD (V1.3e) - Readme: Englishindriawan ladjabNo ratings yet
- QoS Feature Package Description (ERAN15.1 - Draft A)Document10 pagesQoS Feature Package Description (ERAN15.1 - Draft A)Denmark Wilson100% (1)
- Network & System Solutions Specialist: Paid Co-Op Study & Work in CanadaDocument11 pagesNetwork & System Solutions Specialist: Paid Co-Op Study & Work in CanadaPatrick LavoieNo ratings yet
- WDM ProtectionDocument30 pagesWDM ProtectionEchekwube Chike JNo ratings yet
- Fortinet Transceivers: Transceiver Modules For Fortinet ProductsDocument5 pagesFortinet Transceivers: Transceiver Modules For Fortinet ProductsSHLOMI TOHARNo ratings yet
- DP Bluetooth 15102 DriversDocument866 pagesDP Bluetooth 15102 DriversRaphael Fagundes LopesNo ratings yet
- ISU Table NetworkDocument1 pageISU Table Networkkhyati. pgpm18gNo ratings yet
- NSC-7298 Wer.1.0Document256 pagesNSC-7298 Wer.1.0RafNo ratings yet
- CEH ToolsDocument7 pagesCEH ToolsLordWaderNo ratings yet
- How To Install Asterisk On Ubuntu 20.04 - LinuxizeDocument9 pagesHow To Install Asterisk On Ubuntu 20.04 - Linuxizeမန္း တူးNo ratings yet
- Comptia Network+ N10-006 Authorized Cert GuideDocument61 pagesComptia Network+ N10-006 Authorized Cert GuidejbiebsNo ratings yet
- CMail ServerDocument3 pagesCMail ServerAshok KumarNo ratings yet
- Ethernet Storage Guy Multimode VIF - 1597495433Document42 pagesEthernet Storage Guy Multimode VIF - 1597495433George ZavalisNo ratings yet
- HP 3PAR StoreServ Persistent Ports - Technical White PaperDocument13 pagesHP 3PAR StoreServ Persistent Ports - Technical White Paperarm_max78No ratings yet
- Hpe6-A15 - AccpDocument93 pagesHpe6-A15 - AccpNguyen Thai VinhNo ratings yet
- Configurar s7 ConectionDocument35 pagesConfigurar s7 ConectionDavi AraújoNo ratings yet
- Md. Ismail Hossain Asst. Manager at Jadoo Broadband Ltd. Dept. Core IP Planning Mail: Contact: 01970423912Document12 pagesMd. Ismail Hossain Asst. Manager at Jadoo Broadband Ltd. Dept. Core IP Planning Mail: Contact: 01970423912Channel oneNo ratings yet
- CH 4Document45 pagesCH 4Taleh BəkirovNo ratings yet
- M844 4 16-GEP-L A4 E ScreenDocument19 pagesM844 4 16-GEP-L A4 E ScreenrikyNo ratings yet
- VMS Presentation 2018Document17 pagesVMS Presentation 2018angga deri heryansyahNo ratings yet
- Enet At007 - en PDocument94 pagesEnet At007 - en PAkshay AryaNo ratings yet
- ICTNWK529 AT2 Install and Manage Complex Networks Noman BandiDocument41 pagesICTNWK529 AT2 Install and Manage Complex Networks Noman Bandishafe SPNo ratings yet
- Installing and Configuring SpanVADocument81 pagesInstalling and Configuring SpanVAAlfredo Martin100% (1)
- Ucopia Router ArchitectureDocument7 pagesUcopia Router Architecturemahad3vaNo ratings yet
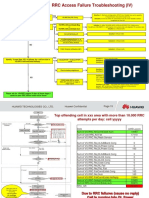
- RRC Access Failure Troubleshooting PDFDocument5 pagesRRC Access Failure Troubleshooting PDFBegumKarabatakNo ratings yet
- Windows 10 File Server or Terminal SetupDocument7 pagesWindows 10 File Server or Terminal SetupBobbyMocorroNo ratings yet
- Amol Bhaskar Tata PuneDocument4 pagesAmol Bhaskar Tata PuneS RaviNo ratings yet
- Technical Proposal For BSNL CDMA MNP ProjectDocument23 pagesTechnical Proposal For BSNL CDMA MNP ProjectajmalameenNo ratings yet
- Where Can You Find Sample Programs and Documentation For Communication From SIMATI... - ID - 48352979 - Industry Support SiemensDocument1 pageWhere Can You Find Sample Programs and Documentation For Communication From SIMATI... - ID - 48352979 - Industry Support SiemensMhd Samer AlHamwiNo ratings yet
- Introduction To Wireless MIMO - Theory and ApplicationsDocument63 pagesIntroduction To Wireless MIMO - Theory and Applicationskokusz76100% (2)