Professional Documents
Culture Documents
Norton AntiVirus 2007 - Updated
Uploaded by
api-3850155Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Norton AntiVirus 2007 - Updated
Uploaded by
api-3850155Copyright:
Available Formats
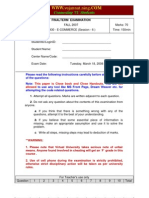
Symantec Norton AntiVirus 2007
Course Guide
Support Readiness Training
July 24, 2006
Supporting Norton AntiVirus 2007 1
Supporting Symantec Norton Anti Virus 2007
July 28, 2006
C op yr igh t Not ic e
Symantec and the Symantec logo are U.S. registered trademarks of Symantec
Corporation. Other brands and products are trademarks of their respective
holder/s. Copyright © 2005 Symantec Corporation. All Rights Reserved. Any
technical documentation that is made available by Symantec Corporation is the
copyrighted work of Symantec Corporation and is owned by Symantec Corporation.
NO WARRANTY. The technical documentation is being delivered to you AS-IS, and
Symantec Corporation makes no warranty as to its accuracy or use. Any use of the
technical documentation or the information contained therein is at the risk of the
user. Documentation may include technical or other inaccuracies or typographical
errors. Symantec reserves the right to make changes without prior notice.
No part of this publication may be copied without the express written
permission of Symantec Corporation, 20330 Stevens Creek Blvd., Cupertino,
CA 95014.
Authorized Symantec courseware materials contain a yellow Symantec watermark
on the front side of each page. Use of unauthorized courseware materials is strictly
prohibited and should be reported to Symantec Corporation immediately.
T r ad e m a rk s
Symantec, the Symantec logo, Intruder Alert, NetProwler, Raptor, VelociRaptor,
Symantec Desktop Firewall, Symantec Enterprise VPN, Symantec Enterprise
Firewall, Symantec Ghost, Symantec pcAnywhere, RaptorMobile, NetRecon,
Enterprise Security Manager, NAV, Norton Anti Virus, Symantec System Center,
Symantec Web Security, Mail-Gear and I-Gear are trademarks of Symantec
Corporation.
Windows is a registered trademark of Microsoft Corporation. Pentium is a registered
trademark of Intel Corporation. Other product names mentioned in this manual
may be trademarks of their respective companies and are hereby acknowledged.
Supporting Norton AntiVirus 2007 2
Course overview
Course description
This is a training program to support the latest release of Norton AntiVirus. It is
estimated that this training will be a three-days, instructor-led, hands-on program
that is designed for the global technical support organizations.
The Norton AntiVirus 2007 course is divided into eleven sections. The instructor's
lecture is followed by lab exercises in which students apply knowledge gained
throughout the course.
Intended audience
This course is intended for those who have responsibility for supporting, installing,
and configuring Norton AntiVirus.
Course prerequisites
It is assumed that the following prerequisites have been met:
• Students have a working knowledge of Microsoft Windows operating systems.
• Students have a working knowledge of computer security practices and
software.
• Students have read the Norton AntiVirus 2007 User’s Guide.
Course objectives
After you complete this course, you will be able to do the following:
• Install Norton AntiVirus 2007
• Understand the install-over matrix for Norton AntiVirus 2007
• Troubleshoot installation of Norton AntiVirus 2007
• Identify the components of Norton AntiVirus 2007
o Auto-Protect
o Manual Scanning
o Email Scanning
o Instant Messenger Scanning
o ccEraser
o Internet Worm Protection
• Understand techniques for troubleshooting Norton AntiVirus 2007 issues
• Monitor Norton AntiVirus activities via reporting section
• Understand the Symantec shared components used in Norton Antivirus 2007
o SymProtect
o Norton protection Center
o Activation
o Subscription
o LiveUpdate
Supporting Norton AntiVirus 2007 3
Unit 1 Introduction to Norton Antivirus 2007.....................................
Overview........................................................................................................7
Introduction to Threats....................................................................................8
What is new to Norton Antivirus 2007...............................................................10
Summary.....................................................................................................11
Unit 2 Installing Norton AntiVirus....................................................
Overview......................................................................................................12
System Requirements.................................................................................. 13
Installation Options........................................................................................14
Installation Features.....................................................................................20
Key file and Registry locations.........................................................................24
Component Installation................................................................................. 25
Installation Technologies................................................................................26
Installation Screenshots................................................................................27
Troubleshooting Installation............................................................................32
Summary.....................................................................................................40
Unit 3 User Interface....................................................................
Overview.....................................................................................................41
New Features................................................................................................42
User Interface Files and their Functions...........................................................46
Summary.....................................................................................................47
Unit 4 Scanning Technology...........................................................
Overview......................................................................................................48
How Scanning works? .................................................................................. 49
Decomposer.................................................................................................50
Quarantine...................................................................................................51
Blood Hound Heuristics..................................................................................53
Summary.....................................................................................................54
Unit 5 Auto-Protect.......................................................................
Overview.....................................................................................................55
What Auto-Protect does? ...............................................................................56
How Auto-Protect works? ..............................................................................55
Auto-Protect files and their functions...............................................................57
Repair Modes...............................................................................................58
Auto-Protect Options and Configuration............................................................59
Troubleshooting Auto-Protect.........................................................................60
Summary................................................................................................... 63
Unit 6 Manual Scanning................................................................
Overview.....................................................................................................64
What Manual Scanning does?.........................................................................65
How Manual Scanning works? .........................................................................65
Manual Scanning files and their functions.........................................................65
Manual Scanning Options and Configuration......................................................68
Troubleshooting Manual Scanning....................................................................69
Summary.....................................................................................................71
Supporting Norton AntiVirus 2007 4
Unit 7 Email Scanning...................................................................
Overview......................................................................................................72
Supported email clients..................................................................................73
What Email Scanning does? ...........................................................................73
How Email Scanning works? ...........................................................................74
Email Scanning files and their functions............................................................75
Email Scanning Options and Configuration........................................................75
Troubleshooting Email Scanning......................................................................76
Summary.....................................................................................................78
Unit 8 Instant Messenger Scanning.................................................
Overview.....................................................................................................79
What Instant Messenger Scanning does? ..........................................................80
How Instant Messenger Scanning works? .........................................................80
Instant Messenger Scanning files and their functions..........................................80
Instant Messenger Scanning Options and Configuration......................................81
Summary.....................................................................................................82
Unit 9 Internet Worm Protection.....................................................
Overview......................................................................................................83
What Internet Worm Protection does? .............................................................84
How Internet Worm Protection works? .............................................................85
Internet Worm Protection files and their functions..............................................85
Internet Worm Protection Options and Configuration..........................................86
Differences between Internet Worm Protection, Personal Firewall component of
Norton Internet Security and Windows XP firewall..............................................89
Troubleshooting Internet Worm Protection........................................................90
Summary.....................................................................................................91
Unit 10 ccEraser............................................................................
Overview.....................................................................................................92
What ccEraser does?.....................................................................................93
How ccEraser works? ....................................................................................93
ccEraser files ...............................................................................................93
Load points cleaned.......................................................................................94
Summary.....................................................................................................95
Unit 11 SymProtect.......................................................................
Overview......................................................................................................96
What SymProtect does? .................................................................................97
How SymProtect works? ................................................................................97
Summary.....................................................................................................99
Unit 12 Advanced Options..............................................................
Overview....................................................................................................100
Advanced Options in Norton AntiVirus 2007.....................................................101
Summary....................................................................................................103
Supporting Norton AntiVirus 2007 5
Unit 13 Message Center.................................................................
Overview....................................................................................................104
What Message Center does? .........................................................................105
Reading Norton AntiVirus Logs ......................................................................107
Summary....................................................................................................110
Unit 15 Symantec Shared components.............................................
Overview....................................................................................................111
Summary....................................................................................................115
Appendix A.................................................................................................116
Appendix B................................................................................................ 120
Supporting Norton AntiVirus 2007 6
Unit
1
Introduction to Norton AntiVirus
Overview
Description
Norton AntiVirus is the fourteenth release of the Norton AntiVirus product line. This
latest version continues to provide enhanced protection to the customers against
latest threats and malicious content. The user interface is enhanced and optimized,
to provide a new exciting experience to the customers.
Objectives
In this unit we will cover the following:
• Introduction to threats
• Introduction to Norton AntiVirus 2007
• New features in this release
Supporting Norton AntiVirus 2007 7
Intr od uctio n to thr eats
Virus
A computer virus is a small program written to alter the way a computer operates,
without the permission or knowledge of the user. A computer virus attaches itself to
a program or file so it can spread from one computer to another, leaving infections
as it travels. Almost all viruses are attached to an executable file, which means the
virus may exist on your computer but it cannot infect your computer unless you run
or open the malicious program. It is important to note that a virus cannot be spread
without a human action, (such as running an infected program) to keep it going.
Worms
Worms are programs that replicate themselves from system to system without the
use of a host file. This is in contrast to viruses, which require the spreading of an
infected host file. A worm is similar to a virus by its design, and is considered to be a
sub-class of a virus. Worms spread from computer to computer, but unlike a virus, it
has the ability to travel without help of any host files. The biggest danger with a
worm is its ability to replicate itself on your system, so rather than your computer
sending out a single worm, it could send out hundreds or thousands of copies of
itself, creating a huge devastating effect.
Trojan Horses
Trojan horses are impostors, files that claim to be something desirable but, in fact,
are malicious. A very important distinction from true viruses is that they do not
replicate themselves, as viruses do. Trojans contain malicious code that, when
triggered, cause loss or even theft, of data. For a Trojan horse to spread, you must,
in effect, invite these programs onto your computer, for example, by opening an
email attachment.
Trojans are also known to create a backdoor on your computer that gives malicious
users access to your system, possibly allowing confidential or personal information to
be compromised. Unlike viruses and worms, Trojans do not reproduce by infecting
other files nor do they self-replicate.
Backdoor
Also called a trapdoor. An undocumented way of gaining access to a program, online
service or an entire computer system. The backdoor is written by the programmer
who creates the code for the program. It is often only known by the programmer. A
backdoor is a potential security risk.
Dropper
An executable file that, when run, "drops" a virus. A 'Dropper' file has the capability
to create or run a virus and infect the user's system when it is executed. When a
'Dropper' file is scanned, the scan may not detect a true virus, because the viral code
has not yet been created. The viral code (and virus) is created when the 'Dropper'
file is executed. Heuristics scanning often detects droppers before regular scanning
will.
Supporting Norton AntiVirus 2007 8
Joke Programs
Joke Programs are programs that change or interrupt the normal behavior of your
computer, creating a general distraction or nuisance.
Spyware
Spyware is a generic term for a class of software designed to either gather
information for marketing purposes or to deliver advertisements to Web pages.
Although software of this type is legitimate, it can be installed on your computer
without the user’s knowledge. Spyware can be installed in, but is not confined to,
three forms:
• As software bundled and installed with another software application
• As a stand-alone installation package
• As a modification to the HTML of a Web page
Adware
Adware is a type of program that displays an advertisement of some sort, usually
related to a specific Web site cached in the Web browser. In some cases, it changes
the home page of your Web browser to point to a specific Web site. Because Adware
is not malicious in nature, it is not considered a virus.
Dialers
Dialers are programs that use a system, without your permission or knowledge, to
dial out through the Internet to a 900 number or FTP site, to accrue charges. Dialers
are typically associated with websites that contain Adult content.
Hack Tools
Tools used by a hacker to gain unauthorized access to your computer. One example
of a hack tool is a keystroke logger -- a program that tracks and records individual
keystrokes and can send this information back to the hacker
A “Rootkit” is similar to a hacktool and is used by an intruder to gain administrator-
level access to a computer or computer network.These tools are generally difficult to
detect and are installed by cracking a password or exploiting a known vulnerability to
access a remote computer.
Remote Access
Programs that allow another computer to gain information or to attack or alter your
computer, usually over the Internet. Remote access programs detected in virus
scans may be recognizable commercial software, which are brought to the user’s
attention during the scan.
Security Risks
Threats which do not conform to the strict definitions of Viruses, Trojan horses,
Worms, or other expanded threat categories, but which may present a threat to your
computer and its data.
Supporting Norton AntiVirus 2007 9
W h a t i s n e w t o N or t o n A n t i v i r u s 2 0 0 7 ?
Previous versions of Norton Antivirus offered customers robust features that
protected them from malicious software and other internet threats. Norton Antivirus
2007 extends this protection to include the new features that protect them from new
threats and vulnerabilities such as:
• Advanced support for removal of Spyware Threats
• New User Interface rendering engine
• Changes to the installation Engine
• Improved User Interface
• Inclusion of the Symantec-Yahoo! Internet Explorer Toolbar
• Enhanced Common Error Display
• Error Log submission
Features removed:
• Home Page protection
• Script Blocking (Since Norton AntiVirus 2006)
Supporting Norton AntiVirus 2007 10
Summary
In this unit we covered the following:
• Introduction to threats
• Introduction to Norton AntiVirus 2007
• New features in this release
Supporting Norton AntiVirus 2007 11
Unit
2
Installing Norton AntiVirus 2007
Overview
Description
This unit focuses on installation of Norton AntiVirus 2007. The installation of the
2007 products is remarkably optimized and requires less user intervention as
compared to the previous releases.
Objectives
After you complete this unit, you will be able to do the following:
• Describe system requirements for installation
• Describe the installation options for Norton AntiVirus
• Locate key installed file locations and registry keys
• Describe the order of component installation
• Discuss the installation technologies used in Norton AntiVirus
• Define the difference between installation and configuration issues
• Describe the uninstallation process
• Troubleshoot installation issues
Supporting Norton AntiVirus 2007 12
System requirements
Before installing Norton Antivirus 2007 customers should review the hardware and
software requirements. These requirements are detailed in the following pages under
the hardware and software sections.
Operating System requirements
Norton Antivirus 2007 is supported only on the following operating systems:
• Windows XP Home or Professional, Tablet PC or Media Center Editions
• Windows Vista (32 bit only)
Norton AntiVirus 2007 is not supported on Windows 95/98/Me/NT/2000, NEC PC98,
Macintosh, Linux, or server versions of Windows 2000/2003/XP computers.
Hardware requirements
The following list illustrates the minimum hardware requirements for Norton Antivirus
2007 to be installed. Platform performance is directly related to the robustness of the
hardware and the resources taken from other applications running on a PC.
Customers will find increased performance in Norton Antivirus with a more robust
hardware
Windows XP editions
300-MHz processor
256 MB of RAM
175 MB of available hard disk space
CD-ROM or DVD-ROM drive
Internet Explorer 6.0
Administrator privileges to install program
Supporting Norton AntiVirus 2007 13
Installation options
Installation from CD
Installation from CD is the most common way of installing Norton AntiVirus 2007.
Installation runs from the Autorun file on the CD automatically. If the installation
doesn’t start automatically, you can open the CD and double-click the Navsetup.exe
file.
Installation from download
The Download is packaged into a single file from a third-party organization to
facilitate easier downloading. After the package has been downloaded the installation
files are unwrapped to a temporary location the contents of which are same to that
of the Norton AntiVirus 2007 CD. After that the NavSetup is launched.
The following screenshots will help you better in understanding the process of
purchasing, downloading, and installing the product from SymantecStore.
The SymantecStore page for Home users
Supporting Norton AntiVirus 2007 14
Selected the product to purchase
The product is added to the cart
Supporting Norton AntiVirus 2007 15
In the same page: Purchase Information
In the same page: Providing a password for the purchase
Supporting Norton AntiVirus 2007 16
Button to start the download
Download Manager starts downloading. Windows XP SP2 may block the download
Supporting Norton AntiVirus 2007 17
Click on Install to install the Symantec download Manager
The download starts
Supporting Norton AntiVirus 2007 18
After downloading the extraction process starts automatically.
After extracting all the installation files to the Temp folder, it will start NAVSetup,
which will continue the installation. From here, the installation process is same as in
the CD version. The complete process and screenshots are added at end of this unit.
Upgrade or install over
If the setup detects a previous installation of Norton AntiVirus 2004 or later, it
automatically removes the earlier version. If the version is earlier than 2004, it must
be uninstalled manually from Add/Remove programs before installing the Norton
AntiVirus 2007. If the uninstallation fails, the following tools can be used to remove
the product from the computer:
RNav2003.EXE to remove NAV 2003 and its previous versions
RNISUPG. EXE to remove NIS 2003 or NPF 2003 and its previous versions
SymClean.EXE to remove NAW 2003 and its previous versions
Supporting Norton AntiVirus 2007 19
Installation features
The following section describes the features and components that are involved in the
Norton AntiVirus 2007 installation. The new features that are incorporated in the
Norton AntiVirus 2007 installation are:
• 3rd Party Installers
• Report Install Success or Failure
• Automatic Error Log Submission
• Error checking of .EXE Installs
• Uninstall Subscription Check
• MSI 4.0
• Improved Install over
Navsetup.exe
Navsetup.exe is responsible for controlling MSI-based installations in Norton
AntiVirus 2007.
Pre-flight checks
The installer checks the client machine prior to making any changes to make sure
that it meets all requirements. The following checks are made:
Check for Internet Explorer 5.01 Service Pack 2
Check for Minimum Operating System
Check for Admin user rights
Check for Server Operating System
Check for Multiple Terminal Services users
Check for LiveUpdate running
Check for running Norton AntiVirus windows
Check for Symantec AntiVirus Corp. Edition on the system
Check for Services and Files marked for deletion
Check for newer versions of Norton AntiVirus
Check for old versions that cannot be installed over
Check for other AntiVirus products
Pre-install scanner
The Pre-install scanner is a simple, lightweight virus scanner capable of detecting
and repairing viruses which can interfere with the installation, configuration wizard or
activation process. The preinstall scanner scans only the load points does not scan
files contained in archives. This eliminates the need for the decomposer DLL’s and
significantly reduces the dependencies list. The preinstall scanner scans for Adware
and Spyware as well.
Supporting Norton AntiVirus 2007 20
How Pre-install Scanner works
The diagram below shows how the Pre-install Scanner works:
NAVSetup
PreScan.exe
ccEraser.dll
ecmldr32.dll
ccScanS.dll
Virus Definitions from CD
Scans the load points for
threats
Prescan.exe interacts directly with ccEraser.dll & ccScanS.dll to begin the scan.
ccScanS.dll, in turn interacts with ecmldr32.dll and the virus definitions to scan the
users computer. Preinstall Scanner is dependent the following four Symantec
components:
1 SymSetup.exe loads the scanner, Prescan.exe.
2 The scanner uses the Norton AntiVirus plug-in DLL file to start the scan.
3 The pre-install scan is run.
Dependencies
The Pre-Install Scanner is dependent on these Symantec components:
1. ccScanS.dll
2. ecmldr32.dll
3. Virus Definitions
4. ccEraser.dll
Supporting Norton AntiVirus 2007 21
3rd Party Installers
During the installation the user would get an option to install the Symantec-Yahoo
tool bar. This toolbar adds to the functionality of Internet Explorer. If the installation
fails, it will fail silently and continue the installation without alerting the user.
Common Error Display
NAVSetup supports Common Error Display error messages. The Common Error
Display (CED) messages work exactly the same way the product errors work. After
alerting the user about an installation error, the software will direct the user to an
online Knowledge Base article.
Report Install Success or Failure
Norton AntiVirus 2007 installation will provide automatic submission system for
reporting install success or failure.
Automatic Error Log Submission
If the installation fails, users will be able to submit their error log through the CED
reporting system.
Supporting Norton AntiVirus 2007 22
Error checking of .EXE Installs
The installer will also check the results of executable based nested installers such as
LiveUpdate. If the installations of these components fail, NAVSetup will alert the user
using Common Error Display.
Uninstall Subscription Check
During uninstallation of the program if there is still any subscription left in the
product, users will be informed on the period remaining in the subscription.
Conditions which display the Subscription remainder dialog:
- When users manually uninstall via Add/Remove
- When some other program launches Symantec uninstaller
Conditions which do not display the dialog:
- When installing the same or newer version of NAV. And, all install over scenarios
including reinstallation and upgrade.
Improved Install over
The installer will be able to upgrade older Norton AntiVirus products. This is done by
removing the previous product prior to installing the new one. Products that can be
upgraded will include:
• Norton AntiVirus 2004
• Norton AntiVirus 2004 Professional Edition
• Norton AntiVirus 2005
• Norton AntiVirus 2006
The installer will also be able to upgrade any of these products when they are
installed within a suite product such as Norton Internet Security or Norton System
Works. The following table shows the 2007 product Install-over matrix:
Product being installed
RETAIL TRIAL OEM SUITE
RETAIL N/A ALLOW ALLOW ALLOW
Currently TRIAL NOTIFY N/A NOTIFY NOTIFY
installed
product OEM ALLOW ALLOW ALLOW ALLOW
SUITE ALLOW ALLOW ALLOW N/A
ALLOW = Allow Install-Over; BLOCK= Block Install Over; NOTIFY = Allow, with
notification that the licensing scheme is going to change.
NAV2007 will be capable of installing over a version with a higher Minor version
number when the installed product is an OEM product and product being installed is
a Retail/SCSS product. That is, NAV 12.0.0.xx Retail will be able to install over NAV
12.0.2.xx OEM, but NAV 12.0.0.xx Retail will NOT be able to install over NAV
12.0.2.xx Retail.
Supporting Norton AntiVirus 2007 23
Key file and Registry locations
The Location of files and the directory structure is the same in Norton AntiVirus 2007
as its previous versions, with an additional list of directories and files under the
Standard Path. The list provided below contains information about the Folders that
are created after installing Norton AntiVirus.
Folders list:
C:\Program Files\Norton AntiVirus
C:\Program Files\Symantec\
C:\Program Files\Common Files\Symantec Shared
C:\Documents and Settings\All Users\Application Data\Symantec\
C:\Documents and Settings\<<User Name>>\Application Data\Symantec\
Registry key locations
The registry keys that are created during the installation of Norton AntiVirus contain
information to ensure the proper functionality and settings of the product and its
components. The key registry locations of interest are:
• HKEY_LOCAL_MACHINE\Software\Symantec\Installed Apps
This key lists all of the Symantec Products and components installed on the
computer, as well as their locations.
• HKEY_LOCAL_MACHINE\Software\Symantec\Shared Defs
This key list the components of Norton AntiVirus that use definitions, as well as the
name of the definition file used by each component and the locations of these
definition files.
• HKEY_LOCAL_MACHINE\Software\Symantec\Symsetup\refcounts
This key lists the GUID (Globally Unique Identifier, a unique 128-bit number that is
produced to identify any particular Symantec component) for each component as
well as the number of installations that have been counted by Digital Rights
Management for each.
• HKEY_LOCAL_MACHINE\Software\Symantec\CommonClient
This key lists the version of the Common Client that is installed.
Supporting Norton AntiVirus 2007 24
Component installation
Understanding the order of component installation in Norton AntiVirus is important.
Knowing this helps troubleshoot where an installation may have failed and the
dependencies that might contribute to the problem.
Order of component installation
The order of Norton AntiVirus 2007 component installation from first to last:
ccCommon.MSI
SYMLT.MSI Norton AntiVirus SYMLT MSI
CfgWiz.MSI
OPCSharedCore.MSI Online Platform Client Shared Components
SymCUW.MSI
OPCLM.MSI
PIF.MSI PIF installer
uiNPC.MSI Norton Protection Center
Parent.MSI Norton AntiVirus Parent MSI
cfCore.MSI Component Framework
SPBBC32.MSI SPBBC 32bit
SymNet.MSI SymNet
AppCore.MSI
AV.MSI
SRTSP.MSI Symantec Real Time Storage Protection Component
Firewall.MSI Firewall Component
IWP.MSI Internet Worm Protection
SymHTMLU.MSI
SymTheme.MSI
MSGCntr.MSI
SubEng.MSI
NAV.MSI Norton AntiVirus
Short.MSI NAVShortcut
Help.MSI Norton AntiVirus Help
Indicators of a successful installation in the Registry
The following registry keys will indicate successful installations of Norton AntiVirus
and can be located in the following path:
HKEY_LOCAL_MACHINE\Software\Symantec\Norton AntiVirus\
Success key - On a successful installation the key value is set to “success”.
Value = (String) "install"
Data = (String) "success"
Version key – Upon a successful installation of NAV this key contains the internal
version number.
Value = (String) "version"
Data = (String) "x.y.z"
Supporting Norton AntiVirus 2007 25
Installation Technologies
This section deals with the Norton Antivirus 2007 installation technology. These
items include: Navsetup and the Microsoft Installer.
Navsetup
Navsetup.exe is responsible for controlling MSI-based installations in Norton
AntiVirus 2007. The primary functions of Navsetup are:
• Perform all pre-install launch condition checking and prompt for any unmet
conditions.
• Displays all install UI panels; including the wizard pages, progress pages and
any error dialogs.
• Call each child (MSI) install in the correct order.
• Keep track of all products installed during installation and remove them
during uninstall.
Microsoft Installer
The Microsoft Installer (MSI) handles the installation of all Norton AntiVirus 2007
components. MSI is only concerned with installation; it doesn’t do pre-installation
checks such as those done by Navsetup.exe. The MSI installers check to see only
that Navsetup.exe launched the MSI.
Note: In Norton AntiVirus 2007, users are unable to run the MSI files as stand-alone
executables. Navsetup.exe must be used to control the MSI packages.
Supporting Norton AntiVirus 2007 26
Installation Screenshots
1. The Autorun screen
2. License Agreement – The screen to enter the Product key
Supporting Norton AntiVirus 2007 27
3. Installation options: You can install Norton AntiVirus on customized path
4. Start the Pre-install scanner
Supporting Norton AntiVirus 2007 28
5. Pre-install scanner in progress
6. File copying starts automatically
Supporting Norton AntiVirus 2007 29
6. Installation is complete
7. The Activation Window
Supporting Norton AntiVirus 2007 30
8. Activation complete
Supporting Norton AntiVirus 2007 31
Troubleshooting Installation
Installation issues arise due to a failed or partial installation of Norton AntiVirus.
There are several causes for the installation to fail. Some of the common causes are
software environment, software bugs, operating system configuration / policy
settings etc. This section will provide an overview of the type of issues that can arise
during the installation and the basic troubleshooting logic that can be followed to
resolve these issues.
Before discussing the installation issues, it is important to understand the installation
technology itself. The flowchart below provides an overview of the installation
procedure that we’ve covered so far:
Supporting Norton AntiVirus 2007 32
There are various stages where the installation may fail. And the resolution depends
on the stage or the area of the installation in which, it is failing. One of the areas
where the installation fails is the “file copy” process or the automatic uninstall
process of a previous version.
The resolution for any issue that may arise in this stage depends on the type of
issue/error message that’s encountered. With the integration of the Common Error
Display with the installer, a majority of the installation issues can easily be identified
and resolved.
In case of any installation failure, generally a “9999, XXX” series error would be
flagged. The procedure to troubleshoot installation issues is outlined below:
1. Ensure the computer is threat free.
2. Ensure the integrity of the installation media/files
3. Ensure that all requisite dependencies are satisfied. These include Windows
Services (Such as Event logging, Remote Procedure Call, Windows Installer
service and their dependencies)
4. Ensure that there are no applications active/running in the background that
might interfere with the installation process.
In many cases, issues might also occur due to a failed uninstall attempt of a previous
installation. This could be an uninstall attempt of a previous version or a failed
installation attempt of the same version. In both cases, it is recommended to remove
the remnants before attempting a clean installation. Here is the list of SymSetup
errors which can appear based on the action that it performs:
9999,171 This error message indicates an installation failure
9999,172 This message indicates an uninstall failure
9999,173 This message indicates a modify failure
This message appears when it is unable to find/read the MSI
9999,174
database
This message appears when an error occurs while removing previous
9999,175
product
Issue
"9999,171 The installation encountered an error and is unable to continue."
Solution
1. Follow the link to the Knowledge Base Article.
2. If the issue persists, uninstall using Norton Removal tool and reinstall.
3. If the issue persists, collect the installation log file and examine the possible
causes.
For the 9999,171 error message there are 6 documents currently available. These
documents are created depending on the stage where the installation fails. When the
user clicks on the URL in the CED, it will direct the user to the appropriate document
depending on the parameters that CED fetches.
Supporting Norton AntiVirus 2007 33
You can view the exact document that the user is directed to from the URL.txt file.
To view this file:
1. Enable Hidden System Files and folders in the Windows Explorer folder options.
2. Go to C:\Documents and Settings\All Users\Application Data\Symantec\Errlogs
You should see at least one zip file in the folder. If you see multiple files, please look
at the latest one. The zip file will have a randomly-generated name. For example:
{D1A19EF5-5886-4EEE-BEE5-694827069F2D}1cc9b170.zip
3. Open the file URL.txt and look the values for the “a” and “h” variable.
For example, the file contents will look like this:
http://www.symantec.com/techsupp/servlet/ProductMessages?&module=9999&error
=171&language=English&product=Norton+AntiVirus+2006&version=12.0.0.94&e=2
753&a=1603&h=NAV_CTO_Action_comm&k=AVSTE.dll&l=PARENT.MSI&c=false
&m=2753&n=11.5.0&build=Standard
Depending on the “a” and “h” variable, direct the user to the appropriate document.
The Lotus Notes internal document will have the “a” and “h” variable for the
document. The link for all the documents is provided below:
Title: 'Error: "9999,171 The installation encountered an error and is unable to
continue" when installing your Norton program'
Document ID: 2005102615163513
http://service1.symantec.com/Support/sharedtech.nsf/docid/2005102615163513
Title: 'Error: "9999,171 The installation encountered an error and is unable to
continue" when installing your Symantec program'
Document ID: 2005101916055513
http://service1.symantec.com/Support/sharedtech.nsf/docid/2005101916055513
Title: 'Error: "9999,171 The installation encountered an error and is unable to
continue" when installing your Norton program'
Document ID: 2006030913475313
http://service1.symantec.com/Support/sharedtech.nsf/docid/2006030913475313
Title: 'Error: "(9999,171) The installation encountered an error and is unable to
continue" when installing your Norton program'
Document ID: 2005101816411513
http://service1.symantec.com/Support/sharedtech.nsf/docid/2005101816411513
Title: 'Error: "(9999,171) The installation encountered an error and is unable to
continue" when installing your Symantec program'
Document ID: 2005100611361513
http://service1.symantec.com/Support/sharedtech.nsf/docid/2005100611361513
Title: 'Error: "(9999,171) The installation encountered an error and is unable to
continue" when installing your Norton program'
Document ID: 2005070717173313
http://service1.symantec.com/Support/sharedtech.nsf/docid/2005070717173313
Supporting Norton AntiVirus 2007 34
Differentiating between an installation and a configuration
issue
NAVSetup
NAV Installer
Installation Issues
(Module 9999)
MSI
File copy process is over
Configuration issues Configuration Wizard
- Module 3009
- Cfgwiz does not launch
- Cfgwiz crashes
CfgWiz.exe finishes
Feature Issues
(Module 1002, 4002, 1007...)
NAV User Interface
Installation issues
Installation issues arise from failed or corrupted installations. Installation error
normally appears before the file copy process is over.
Configuration issues
Configuration issues are typically caused by the settings or environmental issues.
Configuration issues could be caused by settings of features such as Email Scanning,
Internet Worm Protection etc.
Supporting Norton AntiVirus 2007 35
Removing Norton AntiVirus 2007
This section was intended to include a detailed description of a complete
uninstallation of Norton AntiVirus. Given the sensitive nature of Digital Rights
Management, and the tamper-resistance of SymProtect, the following points to
remember will suffice:
Always use the Add/Remove Programs first
The Windows Installer (MSI) will remove the proper registry keys, files, directories,
services to uninstall Norton AntiVirus 2007. Always try this method before moving
If you need to reinstall, make sure that you have the Product Key and the
installation CD or the download files
If the product installed is a download version, make sure that it is re-downloadable.
Also, make sure that you have the Product Key.
Select Norton AntiVirus from the Add/Remove program and Click Remove
Supporting Norton AntiVirus 2007 36
Select Remove
Subscription Period Warning
Supporting Norton AntiVirus 2007 37
Clicking Next will start the uninstallation process
If you have files in the Norton AntiVirus Quarantine, you will get the prompt to keep
it in the quarantine or delete it. If you are reinstalling Norton AntiVirus, and if you
have files in the Quarantine to repair, then you can keep the files. The Norton
AntiVirus Quarantine is explained in detail in Unit 4.
Supporting Norton AntiVirus 2007 38
The removal process in progress
Uninstallation completes. Restart the computer
Supporting Norton AntiVirus 2007 39
Summary
In this unit we have covered the following:
• Describe system requirements for installation
• Describe the installation options for Norton AntiVirus
• Locate key installed file locations and registry keys
• Describe the order of component installation
• Discuss the installation technologies used in Norton AntiVirus
• Define the difference between installation and configuration issues
• Describe the uninstallation process
• Troubleshoot installation issues
Supporting Norton AntiVirus 2007 40
Unit
3
User Interface
Overview
Description
This unit focuses on the user interface changes in Norton AntiVirus 2007. The User
interface of Norton AntiVirus 2007 has been greatly improved as opposed to any of
the previous version's .The interface now is enhanced and simplified.Also, It is
optimized for easy usability and performance.
Norton Antivirus 2007 uses a new rendering engine to display its interface instead of
Internet Explorer. The new engine integrates with the existing components
seamlessly and provides Norton AntiVirus 2007 with a fresh and streamlined user
interface.
Objectives
After you complete this unit, you will be able to do the following:
• Understand the new features of Norton AntiVirus 2007 user interface
• Understand the technology used by the new user interface.
• The differences between the 2006 and 2007 user interface.
Supporting Norton AntiVirus 2007 41
New Features
The important features of the new interface are:
• Usage of the new terra-informatica rendering engine.
• All New integrated Norton Protected Center and Norton AntiVirus windows
• Tabbed approach
• Less User intervention required to perform any task including Scans and
Configuration
• The program window can be maximized
• New Options menu which follows the programs usability flow.
• Removal of many redundant options
• The General Security risks option is now specialized for spyware protection
configuration
• New scanning window and dynamic interface
Tabbed approach
The program window which can be maximized stays static and the actions and
configurable options appear under the tabs or as drop down menus as displayed in
the screen shot below:
Supporting Norton AntiVirus 2007 42
Options Menu
Also, the options menu follows the program interface design and supplements the
program usage. The Screens shot of the Options Menu with the enhancements are as
provided below:
Supporting Norton AntiVirus 2007 43
Removal of Redundant options
Options and User interface options that were redundant in the previous versions
have been replaced or removed, this is a part of the stream lined interface which
ensures maximum usability. Multi tiered and redundant options such as "How to
respond when a virus is found”, which is common between AutoProtect, Email
scanning and IM scanning have been removed and are replaced by easier interfaces.
An example of this approach is explained below:
The Email Scanning Options windows in version 2006
The Email Scanning Options windows in version 2007
Supporting Norton AntiVirus 2007 44
New window structure and dynamic interface
The scanning window and the Log viewer are completely changed to ensure that they
adhere to the program interface seamlessly. Also, the interface is dynamic in nature;
it changes with the change in status of the program and the computer security.
Norton AntiVirus 2007 Interface
Norton AntiVirus 2007 Scan Window
Supporting Norton AntiVirus 2007 45
User Interface Files and their Functions
The Norton AntiVirus 2007 user interface is now enhanced and uses SymHTML. The
SymHTML component has a new integrated engine that uses Terra Informatica,
which is a faster HTML rendering engine than the Internet Explorer rendering engine.
This should resolve the User Interface responsiveness issues that were in the
previous versions.
SymHTML reads SymTheme.dll to fetch the product theme and applies it to the
interface. You will still be able to open the product if the SymTheme.dll is missing or
corrupted. However, the user interface will be plain in this case.
File dependencies
• SymHTMLU.dll: Responsible to render the UI.
• SymTheme.dll: Holds the UI themes.
• UIStub.exe: The interface executable which replaces NMain.exe from the
previous versions. This file is a part of the Norton Protection Center
component and launches the product interface.
Supporting Norton AntiVirus 2007 46
Summary
In this unit we have covered the following:
• Understand the new features of Norton AntiVirus 2007 user interface
• Understand the technology used by the new user interface.
• The differences between the 2006 and 2007 user interface.
Supporting Norton AntiVirus 2007 47
Unit
3
Scanning Technology
Overview
Description
Norton AntiVirus includes various components that scan the computer like Auto-
Protect, Full System Scan, Email Scanning etc.However, a single scanning engine is
used by these components. In this unit, we will describe this technology used by the
Norton AntiVirus 2007. Other Norton Components that use the scanning engine are
described in detail in the forthcoming units.
Objectives
In this unit we will cover the following:
• Understand the new Scanning Engine for Norton AntiVirus 2007
• Understand Decomposer and its usage
• Describe Quarantine
• Understand the Bloodhound Heuristics
• Describe Scan and Deliver
Supporting Norton AntiVirus 2007 48
Scanning Technology
The most important component of Norton AntiVirus is its Scanning engine. This is the
core of the product and is continuously used. The functioning of this component is as
explained below:
When a scan request is initiated, The Norton AntiVirus executable (NAVW32) would
forward the request to the core AntiVirus module (AVModule) by parsing it through
the options as configured by the user. Also, it sends the Scan Interface (avScanUI)
the details pertaining to the current scan request.
The Scan Interface would then communicate with the core AntiVirus module, which
then provides the details of the scan being performed to the Scan Interface, through
which it is provided to the user.
The core AntiVirus module would read the files on file system through the Kernel
Mode Symevent files and then scans the file, using the threat definitions installed. If
a threat is detected by core AntiVirus Module, further action is performed according
to the user’s configuration preference (Alert, Delete, Quarantine).
The procedure is as illustrated below:
UI
NAVW32 (2) Handle Scan avScanUI (5) Status display
(1) Configure
Options User Session
AppCore service
(3) Scan
avModule
(4) Scan Details
Supporting Norton AntiVirus 2007 49
Decomposer
Decomposer is the component responsible for uncompressing archives. These
compressed archives are sometimes referred to as packaged files. The decomposer
component supports a majority of archive types. These include the following file
types:
.amg .hqx .rar
.arj .html .rtf
.cab .lha .tar
.dat .lzh .uue
.exe MIME .zip
.gz OLE (.doc, .xls, etc.)
Decomposer files
Since the decomposer is only responsible for decompressing files to be scanned by
the scan engine, there are 16 decomposer objects; each is responsible it’s respective
file types above.
Decomposer Limitations
Decomposer also has limitations on the level and ability in dealing with some items;
these limitations include the following:
• Decomposer can only scan to 10 levels of compression. Or a package within a
package, within a package, 10 levels deep, if there is an infection beyond 10
levels of compression, then Norton AntiVirus will not be able to detect it.
• Decomposer cannot open password protected compressed files.
• Decomposer cannot modify certain file types (.cab, .arj, etc.) This means
Norton AntiVirus can detect infection inside these files, but will not be able to
repair or quarantine this type of package file.
Supporting Norton AntiVirus 2007 50
Quarantine
Quarantine generally means "to impose a state of enforced isolation", this is required
for computer files that are untrusted or infected. These files could be placed in the
quarantine folder which is a "safe" place to store threat infected files without
infecting other files on the computer.
When Norton AntiVirus quarantines a file, it puts the file in encrypted container
format so that no other application can access it, and then stores it in the Quarantine
folder. This encryption uses an MD5 hashing algorithm.
Quarantine backs up an infected item before it attempts to repair it by default this
option can be configured for user’s convenience. From the Quarantine console, the
user can also submit an infected file to Symantec Security Response for analysis.
Supporting Norton AntiVirus 2007 51
What Quarantine does
The Quarantine functions as a safe place as it separates the infected files from the
Operating System by encrypting them. This ensures that the file cannot further infect
the computer in any way. Also, if an infected file is not repaired, and if it is stored in
the Quarantine folder, you can try to repair the file with the new set of virus
definitions when it is available.
A file is quarantined in the following scenarios:
• When a threat is detected on the user’s computer, he would receive a prompt
for the action to be performed, which includes quarantining the file.
• If the file is being repaired then a copy of the file is stored in the quarantine
folder and is then acted upon by the Virus scanning component. Should the
repair fail or if the scan engine does not have the required antivirus files.
• If the user has configured Norton AntiVirus to quarantine all threats.
In all of the above scenarios the file is encrypted using an encryption algorithm and
is then physically moved to the quarantine folder. The quarantine engine then
interacts with the threat through the threat scanner module in order to get the
category type for each item it stores and displays it to the user in the type column.
Once a file is quarantined the user could either try to repair the file and submit it to
Symantec Security Response if repair fails, or Delete the file.
Also, if the repair fails and the user chooses to retain the file, then the user could
repair the files after updating the virus definitions.
How Quarantine works
Quarantine files
The files pertaining to quarantine are provided below
• Qconres.dll- Norton AntiVirus QConsole Resource DLL
• QBackup.dll - Norton AntiVirus Quarantine backup
• Qspak32.dll -Norton AntiVirus Quarantine File Storage
• Quar32.dll - Norton AntiVirus Quarantine
All the quarantined items are stored in the
C:\Documents and Settings\All Users\Application Data\Symantec\SRTSP\Quarantine
Supporting Norton AntiVirus 2007 52
Blood Hound Heuristics
Heuristics is method of scanning for viruses by looking for patterns or activities that
are virus like. Most antivirus programs have a heuristic scanning method to detect
unknown viruses in the wild. The disadvantage of a heuristic scan is that it may
result in a number of false alarms (false positive).
Traditionally, AV solutions have relied strongly on signature-based scanning, also
referred to as scan string-based technologies. The signature-based scan engine
searches within given files for the presence of certain strings (often also only in
certain regions). However, signature-based scanning only detects known malware
and may not detect against new attack mechanisms.
Heuristic scanning is similar to signature scanning, except that instead of looking for
specific signatures, heuristic scanning looks for certain instructions or commands
within a program that are not found in typical application programs. As a result, a
heuristic engine is able to detect potentially malicious functionality in new, previously
unexamined, malicious functionality such as the replication mechanism of a virus,
the distribution routine of a worm or the payload of a Trojan.
Nowadays heuristic implement rule-based systems. This means, that the component
of the heuristic engine that conducts the analysis (the analyzer) extracts certain
rules from a file and this rules will be compared against a set of rule for malicious
code. If there matches a rule, an alarm can be triggered.
Supporting Norton AntiVirus 2007 53
Summary
In this unit we have covered the following:
• Understand the new Scanning Engine for Norton AntiVirus 2007
• Understand Decomposer and its usage
• Describe Quarantine
• Understand the Bloodhound Heuristics
Supporting Norton AntiVirus 2007 54
Unit
Unit 5
Auto-Protect
Overview
Description
Auto-Protect is the real-time scanner of Norton AntiVirus. By using a set of virus
definitions, Auto-Protect feature provides real-time protection against Viruses,
Trojans, Worms, and Expanded threats. Auto-Protect scans any file accessed on your
system. This ensures that all files in any active state are inspected and verified
before the user acts on them. This is the module that makes sure that your system is
protected at all times. Auto-Protect can only sustain this level of protection if the
system has current and up-to-date virus definitions.
Objectives
After you complete this unit, you will be able to do the following:
• Understand what Auto-Protect does
• Describe the technology used in Auto-Protect
• Understand the main Auto-Protect files and its functions
• Discuss the Auto-Protect Options and Configuration
• Troubleshooting Auto-Protect issues
Supporting Norton AntiVirus 2007 55
What Auto-Protect does
Auto-Protect loads into memory when the operating system loads, thus protecting
the user at all times. Auto-Protect uses the kernel mode driver SymEvent to hook
the Windows file operation stack so the Norton AntiVirus driver, SAVRT, can scan any
file when it has been accessed by the Operating System. Auto-Protect is actively
scanning all files on host PC which include:
• Removable media such as floppy disks, zip disks, USB thumbnail drives or
compact disks
• Files accessed or download from the internet, including cached web files
• New Files as they are created
• Files that are received by POP mail clients
How Auto-Protect works
The Norton AntiVirus Auto-Protect provides extensive protection to the computer, by
scanning files as they are accessed.This is achieved through the help of Symevent
drivers which are kernelmode drivers, that access data synchronously with the
Operating System drivers.
When a file Read or Write request is generated, the Windows Input/Output manager,
will pass the information to the Symevent files.If the file is being written these
drivers will call the Norton AntiVirus scanning engine and check for threats.Once the
procedure is complete, a request to write the file is sent to the Filesystem drivers.
In case of a read operation, the Symevent files send a read request to the
FileSystem drivers and then send the file to the scanning Engine.The file is then
made available to the Windows Input/Output manager if the scanning operation is
successful. For further information on the Scanning Engine, refer to "Unit-4 Scanning
Technology"
The following flowchart describes the functionality of AutoProtect, in a bottom-up
approach:
Supporting Norton AntiVirus 2007 56
Auto-Protect UI Agent
NAVAPSVC.EXE Activity Log
SAVRT32.DLL NAV Options UI
File Input / Output User mode
request Kernel mode
Input / Output manager
SAVRT
SAVRT Drivers Symevent
SAVRTPEL
File System (driver)
Auto-Protect files and their functions
symevent.sys: Kernel-mode driver for operating system
savrt.sys: Kernel-mode driver for operating system
navapsvc.exe: Starts the Auto-Protect service
navapw32.dll: Norton Antivirus agent for Auto-protect
apwcmdnt.dll: Command library for Auto-protect
Auto-Protect interactions and dependencies
In addition to the key files that are installed by Norton Antivirus 2007, there also
exists a dependency on the Remote Procedure Call Service (RPCSS) by the product.
This service is provided by Windows based platforms for miscellaneous RPC services
and by default the service is active. The possibility does exist for a customer to
manually disable it. Disabling the RPC service will cause inconsistent behavior and
errors in the Norton Antivirus 2007 product.
Supporting Norton AntiVirus 2007 57
Repair Modes
Auto-Protect has the ability to scan items contained compressed files in real-time.
Uncompressed files are normally scanned in synchronous mode. Compressed files
are locked and scanned in asynchronous mode (user mode) to close specific
vulnerabilities.
Subsequent attempts to open the file are blocked until a complete scan ended.
Should an open occur while the item is being scanned, a system tray alert will notify
the user that the file may appear locked until the complete compressed file scan is
ended. The files performing this action include; Savrt32.dll, Navapsvc.exe,
Navapw32.dll and Navapw32.exe.
Auto-repair: Auto-Protect will try to repair the infected file. If it fails to repair it, it
will deny access to the file
Repair then quarantine: Auto-Protect will try to repair the infected file. If it fails to
repair it, it will try to quarantine it. If it then fails to quarantine it, it will deny access
to the file
Deny access: Auto-Protect just denies access to the infected file. It doesn’t try to
repair or quarantine the file.
Supporting Norton AntiVirus 2007 58
Auto-Protect Options and Configuration
Supporting Norton AntiVirus 2007 59
Troubleshooting Auto-Protect
One of the major causes of Auto-Protect to fail or produce error messages is
generally due to the Auto-Protect files and Services’ failure to start automatically.
Issue
Norton AntiVirus Auto-Protect is disabled on startup
Solution
Title: 'Norton AntiVirus Auto-Protect is disabled on startup'
Document ID: 2004092415251106
http://service1.symantec.com/Support/nav.nsf/docid/2004092415251106
For Auto-Protect to function properly, the following items should be loaded and
running:
1. Symevent
2. SAVRT
3. ccApp
4. NAVAPSvc.exe
4. The product licensing is valid
5. Virus Definitions
The most common cause of the is issue would be the ccapp.exe file being disabled at
startup or due to the Norton AntiVirus Auto-Protect service being stopped or not
being set to automatic. Correcting these values would resolve this issue.
However, if the issue persists then it would be necessary to ensure that the
computer is threat free by performing a virus scan. It can either be a manual scan
using Norton AntiVirus or an Online Virus scan. By verifying that all detected threats
are removed and following the procedure mentioned above to enable the Symantec
files.
If the issue persists, then starting the computer only with Symantec and Microsoft
services would help in resolving any conflicts. Finally, if the issue still persists then it
could be due to corruption of files and uninstalling and reinstalling Norton AntiVirus
would resolve the issue. The procedure above is represented as a flowchart below:
Supporting Norton AntiVirus 2007 60
Issue
Error: "Norton AntiVirus 2006 has encountered an internal program error"
(4002,517)
Solution
Title: 'Error: "Norton AntiVirus 2006 has encountered an internal program error"
(4002,517)'
Document ID: 2005102808565606
http://service1.symantec.com/Support/nav.nsf/docid/2005102808565606
1. Check whether the ccApp is loading
This issue can mainly happen if the ccApp is not set to load at startup. Check
whether the ccApp is checked in the MSCONFIG. If it is set to load at startup, then
check using task manager whether the ccApp is running. It can happen that the
ccApp crashes during the startup. In that case, a restart of the computer can resolve
the issue.
2. Check whether navapsvc service is set to automatic and is running
Supporting Norton AntiVirus 2007 61
In services, check whether startup type of navapsvc service is set to Automatic. Also
make sure that the status of the service is “Started”. If the service is stopped, you
can right-click and select “Start” to start the service.
3. Delete a leftover registry key from
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
Search and delete the “DeleteFlag” key from this location.
4. Reinstall the Symevent files
If the issue persists, then this can happen if the Symevent files are corrupted and
not loading. Download the sevinst.exe file and run it to reinstall the Symevent files.
5. Uninstall and reinstall Norton AntiVirus
If reinstalling the Symevent does not resolve this issue, then this issue can be due to
corrupted Norton AntiVirus files. An uninstall and reinstall should resolve the issue.
Supporting Norton AntiVirus 2007 62
Summary
In this unit we have covered the following:
• Understand what Auto-Protect does
• Describe the technology used in Auto-Protect
• Understand the main Auto-Protect files and its functions
• Discuss the Auto-Protect Options and Configuration
• Troubleshooting Auto-Protect issues
Supporting Norton AntiVirus 2007 63
Unit
6
Manual Scanning
Overview
Description
The Norton AntiVirus manual scanner provided a reactive protection against Viruses,
Trojans, worms, and expanded threats. This protection is provided by allowing the
user:
• To scan a specific location on the hard drive by right-clicking on the file\folder
and choosing “Scan with Norton AntiVirus.”
• To scan files and folders on the local network drives.
• To scan the load point files and registry keys
Objectives
After you complete this unit, you will be able to do the following:
• Understand what Manual Scanning does
• Describe how manual scanning works
• Understand the main files of Manual Scanning
• Understand the different stages of manual scanning
• Discuss the Manual Scanning Options and Configuration
• Troubleshooting Manual Scanning issues
Supporting Norton AntiVirus 2007 64
What Manual Scanning does
A manual scan lets you check for viruses and other threats in specific files or folders.
You can include additional types of files to scan, such as boot records. You can also
specify whether you want the manual virus scan to check all files on your computer
or exclude files based on their extensions. Lastly, you can specify that scans include
memory infections and infections referenced by threats.
Scan within compressed files
Norton AntiVirus can scan and repair files inside compressed files. With this higher
level of security, there can be a trade-off in computer performance. Norton AntiVirus
uses its own decomposer to decompress and scan the archived files. The files are
decompressed to Windows Temporary folder where the scan is performed.
Scan active programs and start-up files
When Scan active programs and start-up files is turned on (this feature is on by
default), all manual scans will first scan files that have already infected your system
or that can potentially infect your system when your computer first starts up.
Specifically these files are:
Files associated with processes currently running in memory
Files with start-up folder entries
Files with system start INI file entries
Files with system start batch file entries
Files referenced by system start registry keys
How Manual Scanning works
The manual scanner initiates at the users request and performs the scan on the
specified location. By using the Scanning engine and providing it with the required
input data.The operation is explained in detail under the Scanning technology.
Manual Scanning files and their functions
Scanning is performed by the following files and processes:
• NAVW32.exe
• avModule
• avScanUI
• cScanUIc
Supporting Norton AntiVirus 2007 65
Option to run Full System Scan
Scan Window
Supporting Norton AntiVirus 2007 66
Scan Results Summary
Attention Required
Supporting Norton AntiVirus 2007 67
Detailed Results
Manual Scanning Options and Configuration
Supporting Norton AntiVirus 2007 68
Troubleshooting Manual Scanning
Issue
Norton AntiVirus scanner stops before reaching 100 percent complete
Solution
Title: 'Norton AntiVirus scanner stops before reaching 100 percent complete'
Document ID: 2000011717445506
http://service1.symantec.com/Support/nav.nsf/docid/2000011717445506
1. Clear all the Temp files and Temporary Internet files
Some corrupted Temp files can freeze the scanning. If the files are corrupted Norton
AntiVirus will not be able to read the file causing the process to terminate or freeze.
2. Run a scan in Safe mode
Running a scan in safe mode can resolve this if the issue is caused due to a virus
infection. Some threats may initiates numerous process and take much resources
which may affect the scanning process. Running in Safe mode can prevent many
viruses from loading automatically
3. Uncheck compressed file scanning
Some corrupt compressed files on your computer can cause this issue. Norton
AntiVirus decomposers will not be able to decompress these corrupt file which can
terminate the process.
4. Determine which file is causing the issue
This is the best way to find out the exact cause of the issue. If the scanning is
getting freezed at any particular file, it will be a good option to exclude the file from
being scanned and let Norton complete the scan. If the scan is stopping at a
particular compressed file, you can extract the file and create a new archive to make
sure that the archive is not corrupted.
Issue
Norton AntiVirus scanner stops before reaching 100 percent complete
Solution
Title: 'Error: "Norton AntiVirus 2006 was unable to scan your computer for
infections" (3019,6) when running a virus scan'
Document ID: 2006050113575206
http://service1.symantec.com/Support/nav.nsf/docid/2006050113575206
1. Check whether the Norton program is set to run in Compatibilty mode
Supporting Norton AntiVirus 2007 69
Setting NAVW32.exe to run in compatibility mode and performing a scan case easily
reproduce this issue. Check whether NAVW32.exe and other Norton files are set to
run in compatibility mode.
2. Uncheck the compressed file
This error can appear if scan encounter some corrupt compressed files. Unchecking
the compressed file scanning can allow Norton AntiVirus to complete the scan.
3. Uninstall and reinstall Norton AntiVirus
If the issue persists, then uninstall and reinstall Norton AntiVirus, as this error can
happen due to some corrupted program files
Supporting Norton AntiVirus 2007 70
Summary
In this unit we have covered the following:
• Understand what Manual Scanning does
• Describe how Manual Scanning works
• Understand the main files of Manual Scanning
• Understand the different stages of manual scanning
• Discuss the Manual Scanning Options and Configuration
• Troubleshooting Manual Scanning issues
Supporting Norton AntiVirus 2007 71
Unit
7
Email Scanning
Overview
Description
Norton AntiVirus 2007 scans incoming and outgoing emails for threats and malicious
code. As emails are one of the most sought after channels for virus infections, this
enhanced version of Email Scanner is designed to protect the best security towards
email-based infections.
Objectives
In this unit we will cover the following:
• Understand what Email Scanning does
• Describe how Email Scanning works
• Understand the main files of Email Scanning
• Discuss the Email Scanning Options and Configuration
• Troubleshooting Email Scanning issues
Supporting Norton AntiVirus 2007 72
Supported email clients
Norton Antivirus 2007 supports antivirus scanning of the email clients that are
compatible with the AvModule plug which will be discussed in detail in the following
unit. Email scanning has been tested and is supported for the following POP3-
compatible and SMTP-compatible (Simple Mail Transfer Protocol) email clients:
• Outlook Express 4.0, 5.x, 6.x
• Outlook 97/98/2000/XP/2003
• Netscape Messenger 4.x
• Netscape Mail 4.x, 6.x, 7.x
• Eudora Light 3.0, Eudora Pro 4.0, Eudora 5.0, Eudora 6.0J
• Pegasus Mail 3.0
• IncrediMail XE
• Becky! Internet Mail 1.x, 2.0
• AL-Mail32 1.11
• Datula 1.x
• PostPet 2.1, 2.06, 3.0
• Shuriken Pro 3
• Mozilla Thunderbird 1.0
• At-Mail
Email clients not supported
Norton AntiVirus does not support the following email clients:
• IMAP
• AOL
• POP3s with Secure Sockets Layer (SSL)
• Web-based email such as Hotmail and Yahoo! Mail
• Lotus Notes
Note: Norton AntiVirus does not support email connections that use Secure Sockets
Layer (SSL). SSL is a security protocol designed to provide secure communications
on the Internet. If you use an SSL connection, Norton AntiVirus automatically detects
that connection and skips scanning it the connection completely.However, any data
that is transmitted through the connection is scanned as and when data is accessed
on the disk.
What Email Scanning does
Norton AntiVirus Email Scanning verifies that email and attachments are free from
viruses and other malicious code as you download them from your Internet service
provider (ISP). The Outgoing Email Scanning feature verifies that the email that you
send is free from viruses and malicious code before you send it.
Incoming Email Scanning is supported only on POP3 mail accounts. POP3 is the
industry standard, which is used by the majority of Internet service providers. It also
supports the less common APOP, QPOP, and VPOP standards. Outgoing Email
Scanning supports SMTP servers.
Supporting Norton AntiVirus 2007 73
Disabling Email Scanning does not leave the computer unprotected against viruses
that are distributed as email attachments. Norton AntiVirus Auto-Protect scans
incoming files as they are saved to your hard drive, including email and email
attachments. Email Scanning is just another layer on top of this.
How Email Scanning works
When you click on Send/Receive mail in email client, the client sends your user name
and password to the ISP, where they are verified. If the username and password are
valid, all messages that are queued to be sent are forwarded to Port 25, which is the
SMTP port. avModule, which is monitoring port 25 for outbound email, forwards the
emails into a single file in the Windows temporary folder, which is scanned for
viruses. Once Norton AntiVirus has determined that email is virus-free, all messages
are marked as sent, and they are forwarded to the ISP mail server for delivery.
When there are new emails available for download, the mail server sends it to the
computer through Port 110. Port 110 is the POP3 (incoming) port. avModule, which
is monitoring port 110 for incoming email, forwards the emails into a single file in the
Windows temporary folder, which is scanned for viruses. Once Norton AntiVirus has
determined that email is virus-free, it responds to the server telling it to mark the
messages as received.
Email client AvModule Email Server
In case of infection
AvProdsvc
If the default repair options fails
AvProdApp
For user intervention
avScanUI
All incoming / outgoing emails will be scanned by AvModule if the feature is turned
on. AvModule will notify AvProdSvc of any detection that are made. AvProdSvc will
return instructions to remove and quarantine all threats contained in the e-mail. If
there are threats that need additional processing, AvProdSvc will call into AvProdApp
for the current active session, which will in turn invoke avScanUI to display UI to the
user so they can address the threats manually.
Supporting Norton AntiVirus 2007 74
Email Scanning files and their functions
Key email scanning files are:
AVMail.dll
ccEmlPxy.dll
rcEmlPxy.dll
Email Scanning Options and Configuration
Supporting Norton AntiVirus 2007 75
Troubleshooting Email Scanning
Issue
Cannot download email with Norton AntiVirus email scanning enabled
Solution
Title: 'Cannot download email with Norton AntiVirus email scanning enabled'
Document ID: 2003060310162506
http://service1.symantec.com/Support/nav.nsf/docid/2003060310162506
1. Check that your Email program is set to not hang up after receiving
Make sure that the option to hang up after receiving emails is disabled. Enabling this
option can cause this issue.
2. Disable third-party firewall
This issue can occur iif the user is using some third-party firewall and if the firewall is
set to block the Email Scanning files
3. Verify that the Windows temporary folder is configured correctly
Email Scanning scans the emails from Windows Temporary folder. If the Temp
environment variable is not set properly, then Email Scanning will not be able to take
the emails to the Temp location for scanning. Also, it is advisable to clear the
contents of the Temp folder, as the corrupt contents can also cause this issue.
4. Disable Email Scanning, download the problem email and then restart email
scanning
This step is a workaround that allows you to download problem email or email with a
very large attachment. Once the email is downloaded, re-enable the Email Scanning.
Supporting Norton AntiVirus 2007 76
Issue
Cannot send email with Norton AntiVirus email scanning enabled
Solution
Title: 'Cannot send email with Norton AntiVirus email scanning enabled'
Document ID: 2003100110523806
http://service1.symantec.com/Support/nav.nsf/docid/2003100110523806
1. Check that your Email program is set to not hang up after sending
Make sure that the option to hang up after receiving emails is disabled. This option
can cause this issue when Email Scanning enabled.
2. Disable third-party firewall
This issue can occur iif the user is using some third-party firewall and if the firewall is
set to block the Email Scanning files
3. Verify that the Windows temporary folder is configured correctly
Email Scanning scans the emails from Windows Temporary folder. If the Temp
environment variable is not set properly, then Email Scanning will not be able to take
the emails to the Temp location for scanning. Also, it is advisable to clear the
contents of the Temp folder, as the corrupt contents can also cause this issue.
4. Disable Email Scanning, send the problem email and then restart email scanning
This step is a workaround that allows you to send problem email or email with a very
large attachment. Once the email is sent, re-enable the Email Scanning.
Supporting Norton AntiVirus 2007 77
Summary
In this unit we have covered the following:
• Understand what Email Scanning does
• Describe how Email Scanning works
• Understand the main files of Email Scanning
• Discuss the Email Scanning Options and Configuration
• Troubleshooting Email Scanning issues
Supporting Norton AntiVirus 2007 78
Unit
8
Instant Messenger Scanning
Overview
Description
Norton AntiVirus Instant messenger protection is the real-time scanning technology
that protects users from malicious items in instant messenger attachments. Instant
Messenger scanning is an added protection for a secured file transfer through Instant
Messenger programs.
Objectives
In this unit we will cover the following:
• Understand what Instant Messenger Scanning does
• Describe how Instant Messenger Scanning works
• Understand the main files of Instant Messenger Scanning
• Discuss the Instant Messenger Scanning Options and Configuration
Supporting Norton AntiVirus 2007 79
What Instant Messenger Scanning does?
Instant Messenger scanning scans files that are downloaded through the Instant
Messenger clients from AOL, Yahoo and MSN.
Norton Antivirus Instant Messenger scanning supports the following instant
messenger programs:
• AOL Instant Messenger, version 4.7 or later
• Yahoo! Messenger, version 5.0 or later
• Windows Messenger, versions 4.6, 5.0
• MSN Instant Messenger, Versions 4.6 and above
Note: If a user is using any other IM client than the ones listed above, then Norton
AntiVirus Auto-Protect will scan any incoming files as they are saved to the hard
drive. Norton AntiVirus plug-in is just another layer on top of this.
How Instant Messenger Scanning works
When the Instant Messenger completes the file download, it will call the Norton
AntiVirus scanner to scan the file. The scan is performed by ccIMScan.exe which
resides between the downloaded file and the NAV scanner. This file sets the scanning
parameters required for IM scanning.
Instant Messenger Scanning files and their functions
Instant messenger protection detects viruses in instant messenger attachments.
Instant messenger protection interacts with the following items:
• ccApp.exe - Responsible for instant messenger protection. All other modules
are either direct or indirect plug-ins to ccApp.
• ccImscan.dll - Plugs into ccApp.exe. ccImscan.dll is responsible for
configuring and unconfiguring all three clients (Yahoo, MSN, and AOL Instant
Messengers)
• ccImscan.exe - Used in the command line with AIM and YIM to scan file
downloads
• OptionsUI - Enables or disables clients by sending a message to ccImscan.dll
• avModule performs all instant messenger scanning and uses ccImscan.dll and
• ccImscan.exe
Instant messenger protection interactions and dependencies Key dependencies
include:
• ccApp.exe - Common Client
• ccScan.dll - Common Client scan engine
• avModule - Symantec scan manager
Supporting Norton AntiVirus 2007 80
Instant Messenger Scanning Options and
Configuration
Supporting Norton AntiVirus 2007 81
Summary
In this unit we have covered the following:
• Understand what Instant Messenger Scanning does
• Describe how Instant Messenger Scanning works
• Understand the main files of Instant Messenger Scanning
• Discuss the Instant Messenger Scanning Options and Configuration
Supporting Norton AntiVirus 2007 82
Unit
9
Internet Worm Protection
Overview
Description
Internet Worm Protection is an inbound firewall that protects your computer against
worms and other malicious network / Internet activities. Worms are threats that
replicate themselves through the network and can be prevented from entering a
computer with the help of Internet Worm Protection. Through Internet Worm
Protection, incoming network traffic can be restricted and incoming connections to
specific installed applications can also be controlled.
Objectives
In this unit we will cover the following:
• Understand what Internet Worm Protection does
• Describe how Internet Worm Protection works
• Discuss the Internet Worm Protection Options and Configuration
• Differences between Internet Worm Protection, Personal Firewall component
of Norton Internet Security and Windows XP firewall.
• Troubleshooting Internet Worm Protection issues
Supporting Norton AntiVirus 2007 83
What Internet Worm Protection does?
Internet Worm Protection can detect and avoid the following type of attacks /
threats:
• Buffer overrun – known viruses that try to exploit a buffer overrun in a
vulnerable application will be detected by IDS, if they don’t drop a file. E.g.
SQL Slammer
• Exploiting an application – Exploiting known bugs in network using
applications, like Internet Explorer, can be detected by IDS, if they don’t drop
a file.
• Fragmented or malformed packets – Malformed TCP/IP packet attacks are
detected by the firewall and blocked.
• Denial of Service attacks – IWP protects against DoS attacks by using Auto
Block.
• Unknown remote control-type worms can be detected by the firewall if they
open a port to listen for incoming commands.
Note: Internet Worm Protection does not detect new viruses that come in the
form of email attachments. Internet Worm Protection also will not alert if the
worm sends data out only.
Internet Worm Protection uses several techniques to prevent these attacks. The list
below describes these techniques in detail:
Port Blocking
The port blocking feature monitors all outgoing connections and allows those
incoming connections for which, a request was sent. If an incoming connection is
being made without a request by the receiving computer, then the port blocking
feature will block this connection.
General Rules
This section monitors the incoming data flow and takes appropriate action when the
flow matches a pre-defined rule. The General Rules section also allows the users to
create a rule to suit their needs. Refer to the Configuration section for more
information on creating a General Rule.
Traffic analysis
Monitors network traffic for malicious activity. If such activity is detected, Internet
Worm Protection blocks the traffic, logs the event, and issues an alert.
Exploit detection
Prevents another computer from exploiting bugs in your computer’s software. Worms
use these bugs to transfer infected files onto your computer.
Supporting Norton AntiVirus 2007 84
Threat level
Scans an application for known viruses, and determines whether a program is
malicious.
How Internet Worm Protection works?
Once enabled, Internet Worm Protection works continuously in the background to
make sure that your computer is protected from malicious network activity and
worm replication. To be able to trap malicious activities, Internet Worm Protection
monitors specific events that occur. Below is a list of events that the Internet Worm
Protection handles or monitors:
Listen events
Listen events are triggered when an application opens a port for “listening”.
Examples are FTP and web servers, and multiplayer internet games.
IP traffic events
IP events are triggered by incoming traffic to open ports. Usually a listen event is
generated before the traffic is received so the user has already permitted or blocked
the application. However, IP events can occur in cases where the agent wasn’t
running when the application tried to listen. This frequently happens at system
startup.
IDS events
If traffic analyzed by the IDS engine is determined to be malicious the traffic is
blocked and an IDS event is triggered.
Supporting Norton AntiVirus 2007 85
Internet Worm Protection Options and Configuration
The following section describes how each feature can be configured and customized.
Exclusions
Internet Worm Protection monitors the incoming Internet / network traffic and blocks
it if the data transfer matches the attack signatures that are present in the
signatures list. An attack signature is a unique arrangement of information that can
be used to identify an attacker's attempt to exploit a known operating system or
application vulnerability.
Any signature can be excluded from being matched simply by un-checking it from
the signatures’ list. However, excluding a signature would mean allowing that
particular type of data transfer to happen. In case of a false positive, a General Rule
(or a Program Control Rule) can be created to allow specific type of data transfer to
happen, while the signature remains blocked.
Program Control
A user can control a program’s access to the Internet using this feature. However,
the access in this case would be inbound. Using this feature, it is not possible to
block a program from establishing an Internet connection but an attempt to initiate a
control or connection to the program from a remote system can be blocked. If you
would like to add a program that requires an inbound blockage, just add the program
in the Programs’ list and select the Block option.
Supporting Norton AntiVirus 2007 86
General Rules
At times, users may want to block specific type of data transfer from specific
computers in the network or the Internet. Using the General Rules feature, users can
create “Rules” to block specific type (or all type of data) from entering the computer.
By default, Internet Worm Protection offers certain pre-defined rules that prevent
specific type of connections and keep malicious data transfer at bay. Users can
create their own rules by clicking on the “Add” button and following the
comprehensive on screen instructions. However, it is important to know that the
rules listed here execute and work on a hierarchy basis
Supporting Norton AntiVirus 2007 87
AutoBlock
When Internet Worm Protection detects an attack, it places the attacking computer's
IP address in the "AutoBlock" zone. While a computer's IP address is in the
AutoBlock zone, it cannot establish a connection. By default, the computer will be
placed in the AutoBlock zone for 30 minutes.
You can also unblock a computer that's blocked by the AutoBlock feature and to
block the computer permanently, you can "Restrict" the computer.
Supporting Norton AntiVirus 2007 88
IWP Vs Personal Firewall Vs Windows XP Firewall
IWP Personal Firewall Windows XP firewall
All outbound traffic is Outbound Traffic is Filtered Inbound Traffic is Filtered
allowed
All traffic from local All traffic from local All traffic is allowed.
networks is allowed. networks is blocked by
default.(can be configured
to allow it)
Has Intrusion Detection Intrusion Detection No Intrusion Detection
signatures that monitor signatures that monitor signatures
Incoming Connections both Incoming and
Outgoing Connections
Incoming traffic alerts are Incoming traffic alerts set Incoming traffic is allowed.
set to “Permit” instead of to “Block”.
“Block”
No Home Networking Provides customized No Personalized settings
options available. settings for a home available for known
network. networks.
Has fewer logging Logging is Verbose Only textual logging is
capabilities. available.
Supporting Norton AntiVirus 2007 89
Troubleshooting Internet Worm Protection
Different issues that might arise with the Internet Worm Protection feature
• Cannot connect to the Internet after installing Norton AntiVirus
Unable to access Internet after installing Norton AntiVirus
The most likely cause of this issue would be the Internet Worm Protection (IWP)
feature. Hence, disabling IWP and checking for the issue would assist in determining
the exact cause of the issue.
If the issue does not persist, then this could be caused due to the filtering nature of
Internet Worm Protection, as it might sometimes block Internet access to certain
applications that do not have valid rules created for them. This is true if the user is
using an application provided by his Internet Service Provider to log into or access
internet that is not configured with Internet Worm Protection.
Configuring the Internet Worm Protection feature for use with the erring application
would restore internet access. However, if that fails then recreating the Internet
Worm Protection program control list will resolve all conflicts.
Supporting Norton AntiVirus 2007 90
Summary
In this unit we covered the following:
• Understand what Internet Worm Protection does
• Describe how Internet Worm Protection works
• Discuss the Internet Worm Protection Options and Configuration
• Discuss the differences between Internet Worm Protection and Personal
Firewall component of Norton Internet Security and the Windows Firewall.
• Troubleshooting Internet Worm Protection issues
Supporting Norton AntiVirus 2007 91
Unit
10
ccEraser
Overview
Description
The ccEraser was a feature of Norton AntiVirus 2006 that has been carried
forward and is improved for 2007. This feature is designed to remove the side
effects of threat attacks in the Windows registry, batch files, startup folder, ini
files and memory resident threats. ccEraser replaces the Generic Side Effects
Engine that was introduced in Norton AntiVirus 2005. Norton AntiVirus 2007 will
detect and remove Spyware and other expanded threats on-demand through the
use of ccEraser.
Objectives
After you complete this unit, you will be able to do the following:
• Understand what ccEraser does.
• Understand how ccEraser works.
• Describe the files and functions of ccEraser
Supporting Norton AntiVirus 2007 92
What ccEraser does?
Manual and preinstallation scans
ccEraser is designed to provide an expanded set of tools to improve the detection
and removal of Expanded Threats. It will have its own definitions, and have the
ability to deal with Viral Infections and Expanded Threat infections, including
Spywares.
How ccEraser works?
ccLib.lib
avModule.dll ccEraser.dll ccScan.dll
EsrDef.xml
Navapsvc.exe
User Mode
Kernel Mode
SAVRT Symevent
ccEraser files
ccLib.lib
EsrDef.xml
ccScan.dll
Supporting Norton AntiVirus 2007 93
Load points cleaned
The following is a list of the common load points that are cleaned by the ccEraser.
Registry keys
■ HKEY_USERS\<UserID>\Software\Microsoft\Windows\CurrentVersion\Run
■ HKEY_USERS\<UserID>\Software\Microsoft\Windows\CurrentVersion\RunOnce
■ HKEY_USERS\<UserID>\Software\Microsoft\Windows\CurrentVersion\RunServices
■
HKEY_USERS\<UserID>\Software\Microsoft\Windows\CurrentVersion\RunServicesO
nce
■ HKEY_USERS\<UserID>\Software\Microsoft\Windows NT\CurrentVersion\Windows
■ HKEY_USERS\<UserID>\Software\Mirabilis\ICQ\Agent\Apps
■ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
■ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
■ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnceEx
■ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices
■
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServicesOn
ce
■ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Windows
■ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Winlogon
■ HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services
■ HKEY_LOCAL_MACHINE\Software\Classes\<extension>file\shell\open\command
Startup folder
The following items are part of the startup folder load points.
■ C:\Documents and Settings\All Users\Desktop\Startup
■ C:\Documents and Settings\All Users\Desktop\Startup\Launch.bat
.ini files
The following ini files are also checked as load points.
■ C:\Windows\System\Win.ini
■ C:\Windows\System\System.ini
■ C:\Windows\System\Wininit.ini
Processes
Processes that are terminated by the ccEraser are treated differently from effects at
the load points. Users are prompted to stop the processes so that they know which
programs are stopping.
Supporting Norton AntiVirus 2007 94
Summary
In this unit we have covered the following:
• Understand what ccEraser does.
• Understand how ccEraser works.
• Describe the files and functions of ccEraser
Supporting Norton AntiVirus 2007 95
Unit
11
Behavior Blocking (SymProtect)
Overview
Description
Many computer threats attack security software to prevent detection or removal.
These threats are known as retroviruses. These programs terminate processes,
delete files, or remove registry keys in an attempt to prevent the user from
responding to the threat. To counter this threat, Symantec Consumer products
include Behavior Blocking (known as SymProtect), to protect our software from
attacks.
Objectives
After you complete this unit, you will be able to do the following:
• Understand what SymProtect does
• Discuss how SymProtect works
• Determine the possible issues with the Behavior Blocking
Supporting Norton AntiVirus 2007 96
What SymProtect does?
SymProtect is a technology which prevents modification or deletion of Symantec
files, folders, processes and registry keys by unauthorized applications or
accidentally by the user.
However, it does not prevent the reading of our files and registry keys to avoid
interfering with normal operations, such as backup. Authorized applications have full
access, so they do not require any changes to continue to work.
In order to be protected by SymProtect, a Symantec application provides a list of
files and registry keys that are to be protected. An “.eve” file that carries a Symantec
Digital Signature is automatically protected.
The following authorization methods are used by Norton AntiVirus 2007 to authorize
an application, which can make changes to protected resources:
• Digitally signed by Symantec
Applications which are signed with a Symantec digital signature are free to
access all protect assets. This will cover a great deal of legacy products,
Intelligent Updaters and all fix tools should also be signed.
• Running from a preregistered path
An administrator can preconfigure a path, or set of paths, such that
applications that run from those locations are authorized. This might be a
network share location, or a location on the local disk on which software is
delivered.
• Possessing a preregistered name
The product can register the name of the authorized software, such as
System Restore or the Windows XP Backup program,
%SystemRoot%\System32\Ntbackup.exe.
How SymProtect works?
Manifest files
In order for SymProtect to protect resources, their names need to be listed in an
encrypted
XML file known as a manifest. Items to exclude from protection are also listed in the
Manifest. There are separate manifest files for directories and named kernel objects.
The contents of the manifest file can also be viewed in C:\Program Files\Common
Files\Symantec Shared\SPManifests.
Supporting Norton AntiVirus 2007 97
SymEvent is a kernel mode process. The kernel is the core of the operating system.
It is the piece of software responsible for providing secure access to the machine's
hardware and to various computer processes. Most applications do not run in kernel
mode. SymEvent can intercept calls to and from the applications and the kernel.
A flowchart of the order of events that are followed after an attempt to modify
Symantec files are as shown below:
Resources that are monitored
All the Symantec Program folders, common folders, Registry keys under the HKLM
and HKCR paths are protected. A list of protected resources is provided below:
Table 9.1 lists the core SymProtect files.
File name Description
Spbbcdrv.sys SymProtect driver
Spbbcevt.dll Handles SymProtect events
Spbbcsvc.exe Responsible for the SymProtect Service
Updmgr.exe Handles SymProtect updates
Supporting Norton AntiVirus 2007 98
Summary
In this unit we have covered the following:
• Understand what SymProtect does
• Discuss how SymProtect works
Supporting Norton AntiVirus 2007 99
Unit
12
Advanced Options
Overview
This section deals with the Miscellaneous Options that are available in Norton
AntiVirus 2007. These options
Objectives
In this unit we will cover the following:
• Discuss the Advanced options in Norton AntiVirus 2007
• Discuss how to exclude scan and signature
• Understand how to password protect Norton AntiVirus Options
• Describe Norton AntiVirus plug-in for Norton AntiVirus
Supporting Norton AntiVirus 2007 100
Advanced Options in Norton AntiVirus 2007
New
Advanced Options
Which disk, folders, or files, to
Edit
exclude from risk scanning
Remove
Scan Exclusions
New
Which disk, folders, or files, to
Edit
exclude from Auto-Protect scanning
Remove
New
Which known security risks to
Signature Exclusions exclude from scanning
Remove
Risk Details
Spyware
Which category or security risks to
detect
Adware
Dialers
Spyware Protection
Joke Programs
Remote Access
Which additional security risks to
Hack Tools
detect
Trackware
Other
What to do when virus protect is Alert me if my virus-protection is
out of date out-of-date
How to control access to options Turn on password protection for my
settings Symantec product
Change Password
Miscellaneous Turn on protection for my Symantec
How to protect my product
product
How to assist Symantec Security
Automatically submit security risks
Response
How to keep Microsoft Office
Turn on Office Plug-in
documents protected
Supporting Norton AntiVirus 2007 101
Scan Exclusions
Using this option, you can exclude files, folders, or drives from the Norton AntiVirus
scan. Norton AntiVirus keeps two different exclusion lists for Auto-Protect and
Manual Scan.
If you have any particular file to exclude from both Auto-Protect and Manual scan,
then you have to add the file separately in the Auto-Protect and Manual scan
exclusion list.
Signature Exclusions
Using signature exclusions, you can exclude any expanded threat from getting
removed by Norton AntiVirus scan. If you wish to run some non-viral threats like
adwares which NAV is detecting on every scan, then you can add those threats in the
signature exclusions. After that, Norton AntiVirus will not alert about that threat in
the subsequent scans.
Also, if Norton AntiVirus has detected any false positive for a legitimate program, you
can add that in Signature Exclusions until an updated virus definitions are available.
Spyware Protection
This option allows you to select what types of expanded threats that Notron AntiVirus
should detect. You can select the option to scan for high risk items like spyware
while excluding low risk threats like adwares and joke programs.
Options Password
Options Password allows you to set a password for Norton AntiVirus Options. You will
be prompted to enter the password when ever you try to change the Norton
AntiVirus options.
Microsoft Office plug-in
The Microsoft Office plug-in allows Norton AntiVirus to scan Microsoft Office files as
they are opened. Isolation of symptoms regarding the Norton Antivirus Microsoft
Office Plug-in:
• You should disable the office plug-in if you suspect it is causing problems
opening or saving Word, Excel, Power Point, or other Microsoft Office
documents.
• If you decide to uninstall Norton AntiVirus you should unregister and rename
the Officeav.dll file to ensure this plug-in will not cause future issues.
• If you disable the Microsoft Office plug-in, Auto-Protect still scans Microsoft
Office documents in real time.
Supporting Norton AntiVirus 2007 102
Summary
In this unit we have covered the following:
• Discuss the Advanced options in Norton AntiVirus 2007
• Discuss how to exclude scan and signature
• Understand how to password protect Norton AntiVirus Options
• Describe Norton AntiVirus plug-in for Norton AntiVirus
Supporting Norton AntiVirus 2007 103
Unit
14
Message Center
Overview
With the changes to the user interface of Norton AntiVirus the Log viewer is also
updated to ensure maximum program usability and ease of use. It has been
streamlined and is now available as Message Center.
The Message Center provides a categorical view of all logged events and also makes
it easy to track and view the events and their details including the firewall events
and also the Antivirus events.
Description
The components of Norton Antivirus log all activities that are performed by them.
These Message Center provides the user, the ability to read and analyze these
activities, which include events such as alerts, application activities, and threat
activities that have occurred in Norton AntiVirus 2007.
Objectives
After you complete this unit, you will be able to do the following:
• Understand what Message Center Logs are.
• Study about the Activity logs.
• Discuss what logs do.
• Identify and analyze the various logs created.
Supporting Norton AntiVirus 2007 10
4
What Message Center does?
Message Center stores all event data that is generated by Norton AntiVirus. This is
achieved by common client files which monitor all event details that components
produce. The Message Center component is a generic log viewer that is plug-in
driven and provides a common user interface to display logged events, including all
of those listed above.
Activity logs record the events and activities that occur with the program. The
information stored in the log files can be used extensively for troubleshooting as they
store all events that occur in the program’s environment.
Message Center allows a technician or a user to view the events that occur in the
program’s environment. This technique allows a user or a technician to look what
exactly happened with the program and also helps in tracking or narrowing down an
issue through the recorded details.
The following categories of information are available in the Message Center of Norton
AntiVirus 2007:
o Internet Worm Protection
o Security Risks
o Manual Scans
o Quarantine Items
o Submissions
Supporting Norton AntiVirus 2007 105
Norton AntiVirus activities
Internet Worm Protection
This displays a list of events that are logged by the Internet Worm Protection. The
Internet Worm Protection logs are best used when a specific program is having
difficulty connecting to the Internet or to a Network.
Security Risks
This provides the user with details about all security risks that were detected by
Norton AntiVirus; this includes threats detected by Manual Scans, Auto Protect, Email
scanning and IM scanning. The information provided the about the threats that are
partially removed or those which were not deleted, would be of importance in
ensuring optimum security.
Manual Scans
This provides information about the various components that perform scans that are
initiated by the user. Such as context scans, IM scanning and Email scanning events.
It provides information about the various scan entries such as the number of files
scanned, infection detection and removal details could be obtained.
Quarantine Items
This contains a list of items that are quarantined either automatically or that have
been added manually. Also, the quarantined file could be submitted to the Symantec
Security Response through this console.
Submissions
This option displays in detail the files that are submitted to the Symantec Security
Response and the status of their submission. It also provides the details about the
file, the threat detected in it and the date and time the file was updated. This
information could be used by the customer to ensure that a suspicious file has been
sent to Security Response for analysis.
Supporting Norton AntiVirus 2007 106
Reading Norton AntiVirus Logs
The Log files provide a great level of detail about the activities that are performed by
the user. These include a detailed statistics which would be of assistance in
troubleshooting Connectivity issues.
To read a particular log file choose a log entry and click on “More info” on the right
side information Window to view details of the selected event.
The Detailed information view would provide information about the actions that were
recommended and the actions that were performed by the user. Also a link for more
information about the particular log type being viewed would be available.
Information about each log type and its functionality is explained below:
Full history
The Full history view display all log entries. Selecting an entry displays brief
summary about it in the "Alert Details" window. Clicking on the More details display
complete information about the event. The information provided for events of each
feature are explained below.
Internet Worm Protection Alerts
The window displays a list of alerts and events that are generated by the Internet
Worm Protection Component. It contains the name, priority and status of the event.
The alert details window displays the event details as mentioned above and
information about any IP addresses and files involved and a description of the event.
Security Risks
The alert details window displays the Risk name, type and any impact that it has on
the computer. It also displays the component which detected the risk which could be
either of the two "AutoProtect" or "Manual Scan" and the recommended and
performed actions. Finally it displays the filename, path and file information.
The advanced details window in addition to the above provides the product name
and version which generated the alert .The component version and the internal
definition version. These would be helpful in trouble shooting virus removal issues.
Also, it displays a link to the Symantec Security response article corresponding to the
threat. And general information about Viruses and Auto-protect as provided in the
Help files.
Supporting Norton AntiVirus 2007 107
Manual Scan results
The results of a manual scan operation are different from the results of the other
scanning related log entries. The alert window displays all the information that the
advanced details provide. Which are the Component that initiated the scan, the Task
name for the scan and finally the time taken for the completion of the Scan in
Seconds. And, the results of that scan, this includes the number of
• Master Boot Records
o Scanned
o Infected
o Repaired
• Boot Records
o Scanned
o Infected
o Repaired
• Files
o Scanned
o Infected
o Repaired
o Quarantined
o Excluded
Supporting Norton AntiVirus 2007 108
Quarantine Items
The event window displays details about Priority, title and the status of removal of
the threat. The alert details display the Risk name and level, the threat Category and
the component which placed it in quarantine. It also does provide the state of the
threat removal.
The advanced details window displays the risk type, eraser version and the internal
definition version. Also, it provides a link to the corresponding Symantec Security
response article about the threat.
In the advanced details window the Threat could be Sent to the Security Response
Team, Deleted permanently or be restored back.
Submissions
This Window displays a list of "submissions" and their priorities and names. The
details window displays details about the date the event was updated, the source
which updated the file and the description of the updated file.
Supporting Norton AntiVirus 2007 109
Summary
In this unit we have covered the following:
• Understand what is the Message Center
• Describe what Message Center does
• Discuss what logs do.
• Identify and analyze the various logs created.
Supporting Norton AntiVirus 2007 110
Unit
15
Symantec Shared components
Overview
Description
Explaining the Symantec Shared components in details is not within the scope of this
manual. But, without explaining the components like Activation and LiveUpdate,
Norton AntiVirus manual will not be complete.
Here, we discuss how Norton AntiVirus uses the Activation and LiveUpdate
components to activate and update the product.
Objectives
In this unit we will cover the following:
• Understand what Activation does
• Describe what Norton Protection Center does
• Understand what LiveUpdate does
• Describe how Norton AntiVirus uses LiveUpdate
Supporting Norton AntiVirus 2007 111
Activation
Digital Rights Management is a technology that protects you from pirated or
counterfeit software. It limits the use of a Norton program to those who purchased
the program legitimately. When you install a Norton program, you are required to
use a unique product key to activate it. You can activate your Norton program during
installation, or after you install. If you choose to activate after you install, you must
activate within a limited time, or the product will not work.
Norton Protection Center
Norton Protection Center detects and prompts the user about the security status and
the status of the Norton Product, including the Virus Definition, previous scan date
and other product related data.
Norton Protection Center reports on how safe it is for you to use your computer to
perform popular tasks. It groups your activities into five protection categories. Your
protection is based on the programs that you have installed. To improve your
protection status, ensure that your installed programs are up to date.
The Security Basics category includes programs that protect your computer from
viruses and other security risks, and ensures that the protection is updated
frequently. It reports on whether your disks have been scanned for viruses recently,
whether you have spyware protection, and whether you receive Windows updates
and antivirus updates automatically.
After the installation a Norton Protection Center icon appears on the Windows
System tray which provides the status of the Norton AntiVirus.
Supporting Norton AntiVirus 2007 112
The Norton Protection Center Interface
Supporting Norton AntiVirus 2007 113
LiveUpdate
LiveUpdate is a program through which, a user can download virus definitions and
program updates. It is recommended to run LiveUdpate immediately after the
product’s installation and frequently, to check if there are any updates released for
the installed product. The version of LiveUpdate that ships with Norton AntiVirus
2007 is Version 3.1.
Also, note that the user needs to have a valid subscription in order to download the
updates through LiveUpdate.
Following are the Norton AntiVirus components that are updated by
LiveUpdate:
LiveUpdate
Automatic LiveUpdate
Symevent Installer - Consumer
Common Client Core
Common Client Core Resource
Symantec Security Software
Decomposer
ccpd_Retail_Licensing_Technology
NortonProtectionCenter
Component Framework
Submission Engine
Submission Engine Data
SPBBC
IDS - Consumer
Symnet Consumer
Appcore - Beta
Symantec Known Application
System
COH White List
COH Update
SRTSP Consumer
Firewall - Pre Release
Symantec Trusted Application List
AV IDS Defs 2006 Microdefs25
AV IDS Defs 2006 Microdefs25
Avenge Microdefs25 NAV2007
NAVNT 2007 - Pre Release
Avenge Microdefs25 nav2007
Supporting Norton AntiVirus 2007 114
Summary
In this unit we have covered the following:
• Understand what Activation does
• Describe what Norton Protection Center does
• Understand what LiveUpdate does
• Describe how Norton AntiVirus uses LiveUpdate
Supporting Norton AntiVirus 2007 115
Appendix
A
Acronyms
DLL – A Dynamic link library is a collection of shared libraries in the Microsoft
Windows. These libraries usually have the file extension DLL. The code in a DLL is
usually shared among all the processes that use the DLL
MSI - The Windows Installer (previously known as Microsoft Installer) is an engine
for the installation, maintenance, and removal of software in Windows. The
installation information and the files to be installed are packaged in these.
Windows Registry- Windows registry is a database which stores settings and
options for the operating system and information and settings for all the hardware,
software, users, and preferences of the PC.The Registry is split into five logical
sections, which are further divided in to sub sections and keys. The sections of the
registry are: HKEY_CLASSES_ROOT, HKEY_LOCAL_MACHINE,
HKEY_CURRENT_USER, HKEY_USERS, and HKEY_CURRENT_CONFIG
Remote Registry – Remote Registry is a Windows registry editor that displays the
registry for a remote device and enables you to add, delete, and modify registry keys
and entries remotely over a network or Internet.
Windows Services - A service is an application that conforms to the interface rules
of the Service Control Manager (SCM). It can be started automatically at system
boot, by a user through the Services control panel applet, or by an application that
uses the service functions. Services can execute even when no user is logged on to
the system.
GUID- A GUID is a 128-bit integer (16 bytes) that can be used across all computers
and networks wherever a unique identifier is required. Such an identifier has a very
low probability of being duplicated.
Service Pack- A Service pack is the means by which product updates, fixes and/or
enhancements are distributed. Service packs may contain updates for system
reliability, program compatibility, security, and more. All of these updates are
conveniently bundled for easy downloading.
NetMeeting - Microsoft NetMeeting is a Voice over Internet and videoconferencing
client included in Microsoft Windows (from Windows 98SE to Windows XP). It also
has features such as white boarding, Desktop sharing, and file transfers.
AutoRun - AutoRun is the ability of the operating system to automatically take some
or the default action upon the insertion of a removable media such as a CD-ROM,
DVD-ROM, or flash media. This feature can be bypassed by holding down the shift
key as the media is inserted.
IM- Instant Messenger, it is a real-time communication medium between two or
more people. The text is conveyed via computers connected over a network such as
the Internet.
Supporting Norton AntiVirus 2007 116
Port- A Port is an interface between the computer and other computers or devices
used to transfer data from one computer to another via a cable that links connecting
ports.
Packet - A packet is a self-contained bundle of data sent over a packet switching
network. Packets are typically less than 1500 bytes in size.
Protocol - A method or predefined set of rules by which two dissimilar systems can
communicate
Hosts – The Hosts file is used to look up the Internet Protocol address of a device
connected to a computer network. It also provides mapping of device names to IP
addresses. When accessing a device by name, the networking system will attempt to
locate the name within the hosts file; this is used as a first means of locating the
address of a system, before accessing the Internet domain name system
IIS - Internet Information Services is the Microsoft's Web server that runs on
Windows NT platforms is tightly integrated with the operating system; it is relatively
easy to administer.
NetBIOS - Network Basic Input/Output System allows applications on separate
computers to communicate over a local area network. It provides services related to
the session layer. It does not support a routing mechanism, so applications
communicating on a wide area network must use another "transport mechanism"
(such as TCP/IP) rather than, or in addition, to NetBIOS.
TCP- Transmission Control Protocol is one of the core protocols of the Internet
protocol suite. Using TCP, applications on networked hosts can create connections to
one another, over which they can exchange data or packets. The protocol guarantees
reliable and orderly delivery of data both at the sender to receiver ends.
IP- The Internet Protocol (IP) is a data-oriented protocol used for communicating
data across a packet-switched internetwork. It is a network layer protocol and is
encapsulated in a data link layer protocol. As a lower layer protocol, IP provides a
unique global addressing amongst computers.
IPaddress- IP address is a unique number that is used by devices to identify and
communicate with each other on a computer network utilizing the Internet Protocol
standard (IP).
Mac address - Media Access Control address is a unique identifier available in NIC
and other networking equipment. Most network protocols use one of three
numbering spaces managed by the IEEE: MAC-48, EUI-48, and EUI-64, which are
designed to be globally unique. A computer in the network can be identified by using
its MAC and IP address.
Supporting Norton AntiVirus 2007 117
DNS - Domain name system translates domain names to IP addresses, it also stores
and associates information with domain names, also DNS lists mail exchange servers
accepting e-mail for each domain.
SMTP - Simple Mail Transfer Protocol is the protocol used to send mail between
servers and to send mail from your client to a mail server.
FTP - File Transfer Protocol is the language used for file transfer from computer to
computer across a network such as the Internet.
IGMP - Internet Group Management Protocol is a communications protocol used to
manage the membership of Internet Protocol multicast group.
ICMP - Internet Control Message Protocol is used by networked computers to send
error messages.
Bootp - Bootstrap Protocol, is a UDP network protocol used by a network client to
obtain its IP address automatically. This is usually done in the bootstrap process of
computers or operating systems running on them. The BOOTP servers assign the IP
address from a pool of addresses to each client.
Telnet - TELNET is a network protocol used on the Internet or local area network
LAN connection. It is used to provide user oriented command line login sessions
between hosts on the Internet. The name is derived from the words telephone
network, since the program is designed to emulate a single terminal attached to the
other computer.
HTTP – HyperText Transfer Protocol is the protocol used to transfer or convey
information on the World Wide Web. It is a patented open internet protocol whose
purpose is to provide a way to publish and receive HTML pages.
HTML - HyperText Markup Language is a computer language designed for the
creation of web pages with hyperlinks and other information to be displayed in a web
browser. HTML is used to format text; that is to denote certain text as headings,
paragraphs, lists and also structure information in a particular manner.
XML - Extensible Markup Language is a computer language that provides a text-
based format for information and services to be encoded with a common structure
and semantics that both computers and humans can understand. It can easily be
extended to include user-specified and default tags.
URL - Uniform Resource Locator is a string of characters conforming to a
standardized format, which refers to a resource on the Internet by its location.
ISP – An Internet Service Provider is a company that provides an Internet
connection. They also provide services such as Internet transit, domain name
registration and hosting, dial-up or DSL access, leased line access and co-location
Supporting Norton AntiVirus 2007 118
EPMAP –End Point Mapper allows clients on a network to find servers, services of
servers and objects managed by those services on the host. This is achieved by a
database called the local endpoint map.
Loopback - A diagnostic test that returns the transmitted signal back to the sending
device after it has passed through a network or across a particular link. The returned
signal can then be compared to the transmitted one. The discrepancy between the
two helps to trace the fault.
Supporting Norton AntiVirus 2007 119
Appendix
B
Advanced Tools
Reading MSI log file
The Microsoft Installer creates log files for each instance of its installation and places
the logs in the Temp folder. These installation logs can be very handy while
troubleshooting installation issues. The installer logs every activity that takes place
during the installation and maintains several conventions to record specific events.
Based on these conventions, installation errors and the “cause” of the error can be
narrowed down.
Accessing the logs
To access the logs,
1. Click Start >Run
2. Type %temp% and click Open
3. In the Temp folder, look for a .log file with the name of the product that just
installed (or attempted to install).
For e.g. A Norton Internet Security 2006 installation log file would have the
name: Norton Internet Security 2006 7-7-2006 6h50m10s.log
The name of the log file also contains the date and time when the log was
created.
Analyzing the log
A typical MSI log file will contain entries starting with MSI (c), MSI (s) or MSI (n)
followed by the action that took place during the installation at that point of time.
Let’s now discuss some of the key entries of a typical MSI log file:
MSI (c) – Denotes an operation that’s taking place in the client engine (NAVsetup).
MSI (s) – Denotes an operation happening in the Windows Installer service.
MSI (n) – Denotes a nested installation activity.
Note: The 4 digit number that follows the “Note” string denotes the code for the
action that’s following. At times, this number can be used to lookup information on
the Microsoft website to determine the exact action that took place. If an error
occurs during the installation, then the error message would contain the same 4 digit
code.
Return Values
Every action that’s performed during the setup is noted in the log file. And the
completion of each action is logged as a “Return Value”.
Supporting Norton AntiVirus 2007 120
Return Value 1: If the Return Value for an action is ‘1’, then the action was
successfully performed.
Return Value 2: A Return Value of ‘2 ‘ideally indicates user abortion or an instruction
by the user to cancel the installation.
Return Value 3: Return Value 3 indicates a failed install action. And this is the key
value to look for while troubleshooting.
Reading an MSI log file
While reading an MSI log file for errors, it’s a good practice to search for errors from
the bottom of the document. Reach the bottom of the document, and do a top
search for the “Return Value 3” string. If there’s a Return Value 3 entry in the log,
analyze the values just above the “Return Value 3” entry for the actual cause of the
failure. The resolution for the installation issue depends on the cause of the failure.
Let’s now take a look at a failed install log file:
In the above Norton AntiVirus log, the installation has encountered an error while
trying to install a file (in this case msvcp71.dll). We also understand from this log
that the installation was being done through the hard drive and not a CD-ROM, as
the file’s (msvcp71.dll) path is shown as Desktop. An error has occurred in this
installation due to the file’s absence in the source. The error: “System error 3. Verify
that the file exists and tat you can access it.” clearly confirms this.
The solution is this case would be to make sure that the product source is complete
and has all the required files and folders.
Supporting Norton AntiVirus 2007 121
Windows Event Logs
This unit will provide you an overview of the Windows Event logs. After the
completion of this unit, you will be able to do the following:
• Read / understand and analyze the Windows event logs
• Clear the event logs
• Export the event logs to a text format
Using the Windows Event logs, a user can check all the events that occur in the
computer irrespective of the user being logged on / off. Information about the
computer’s hardware / software or an application crash can also be gathered through
the Windows event logs.
Accessing the Windows Event logs:
There are several ways of accessing the Windows Event logs:
1. Click Start
2. Click Control Panel
3. Click Performance and Maintenance
4. Click Administrative Tools
5. Double-click Event Viewer.
A Windows XP computer logs events in three types of logs.
1. Application log
2. Security log
3. System log
Application log
This log contains events logged by installed applications. If a particular program
crashes during its launch or during an operation, then this log can be analyzed to see
what component or file of the program caused the crash.
System log
The system log contains all entries related to the operating system components.
Information on drivers that fail to load or any system service that fails to start will be
logged here.
Security log
Security logs make entries of successful and unsuccessful login attempts. It also logs
the attempts made to access a restricted file / folder etc.
Supporting Norton AntiVirus 2007 122
Event Entries
Windows Event Logs create three types of event entries:
Error
An error occurs due to loss of functionality. If a specific file or a program fails to load
(either manually or automatically), then this event can be termed as an error, as
there’s an interruption to the normal behavior. These types of “Error” events will be
recorded in the Application logs as Error
Warning
Any event that may cause a problem in the future will be an ideal Warning type of
log entry. For e.g. Low Disk Space
Information
An event that starts successfully or a Service that loads successfully started.
Success Audit
A successful Windows Login.
Failure Audit
An unsuccessful login attempt.
Information to look for
If you’re looking for application specific information because of a specific program
not functioning properly, then “Application log” is the place to look for. Since this log
contains “Application specific” information, it can be utilized to check if all Norton
services have started. Double-clicking on a service that’s listed in the Application log
will provide us more information on the status of the service.
Supporting Norton AntiVirus 2007 123
Double-click on the ccSvcHst entry to view more information.
At times, after determining that a required Norton service is stopped, when you try
to start it, you may not be able to do so. In this case, look for the status of a
dependant service. If the dependant service is stopped, then we won’t be able to
start the service in question.
Supporting Norton AntiVirus 2007 124
Orca
(By Erik Carlstrom, with contributions from Nate Cantrell and Andrew Doggett)
Orca is a utility that has been created by Microsoft to give software
developers the ability to view information in an MSI installation package. In order to
obtain Orca, it is necessary to obtain the either the Orca.msi file from Microsoft, or
install the Microsoft Software Developers Kit and then installing. Information on how
to obtain and install Orca can be obtained from the following Microsoft Knowledge
Base article:
http://support.microsoft.com/default.aspx?scid=kb;en-us;255905
The primary developer use for Orca is to edit MSI files. However, it can be an
invaluable support tool for viewing these files as well. In order to use Orca to view
the content of an .msi file, locate the file in question and right click on the file. Orca
installs a context menu handler that allows you to then choose “edit with Orca.” This
will then open the Orca editor and display all of the information contained with the
.msi file in question.
There is a large amount of information that can be found by using Orca. Not
all of this information is useful for troubleshooting purposes. Therefore, we will only
concentrate on the items necessary to aid with our troubleshooting.
SymNestedInstaller Table
The first section to look at is the SymNestedInstaller table within the
products’ .msi file, which gives us the following information: product codes,
installation patch, the type of installation (executable, or MSI script), and the order
of installation. In this example, we are looking at the NSW.msi file. This is the
“parent” MSI file for the Norton SystemWorks product. It lists all of the other
installation packages that will be launched, and run during the installation process.
For our purposes in this document, as outlined in below, we are concerned with the
installation path; install type, and the order.
Supporting Norton AntiVirus 2007 125
From the figure we can tell, that we are only going to receive logging from
the following installation packages: MSRedist, NSWLT, NSW, NAV, NU, NCS, Ghost,
and PassMan. The LUSetup, LRSetup, and Sevinst installation packages are
executables, and therefore will not insert logging information in the installation log
file.
CustomAction Table
Within the installation log file, will be every action that is outlined by the .msi
file. These are located within the CustomAction table within Orca. In the example
below we can see several examples of these actions, such as RollBackStuff, Upgrade,
EnableOBC, etc. In analyzing an installation log file, we would expect to see
instances of every singly action listed in this table.
All of the custom actions that are listed above will be found at some point,
during the actual installation sequence.
InstallExecuteSequence Table
If we go to the InstallExecuteSequence table, we can look at the order for
each action that will occur when this .msi package is run. If a particular action fails,
or is skipped, we can look in the CustomAction table to determine if that action is a
Symantec action or a Microsoft action. Within the table below, we see the sequence
column. This gives us the ability to determine the exact order of the actions that
occur for this .msi package.
Supporting Norton AntiVirus 2007 126
Property Table
The Property Table can be used to obtain the ProductCode and UpgradeCode
for any MSI package, as shown below.
The ProductCode and UpgradeCode are important to note, in case a removal was not
completely done. The ProductCode is sometimes the sole means of identification for
Uninstall keys. These are located in the registry at HKEY_LOCAL_MACHINE\
Software\Microsoft\Windows\CurrentVersion\Uninstall. The UpgradeCode’s are
located in the registry at
HKEY_CURRENT_USER\Software\Microsoft\Installer\UpgradeCodes\ (for Windows
98, Me and 2000) and
HKEY_LOCAL_MACHINE\Software\Classes\Installer\UpgradeCodes\ (for Windows
Xp).
Without looking in Orca, there are other methods for obtaining ProductCode
and UpgradeCode information. For example, on Windows Xp if you go to
HKEY_CLASSES_ROOT\Installer\Products\<GUID>\SourceList you can look on the
right at the PackageName. This means the GUID in the path is the ProductCode. If
you are doing a removal, and want to find the UpgradeCode, you can delete keys
already found (HKEY_CLASSES_ROOT\Installer\Products\<ProductCode>) and then
Supporting Norton AntiVirus 2007 127
go back to HKEY_CLASSES_ROOT\Installer\, search for the ProductCode and delete
any key found. Once you come to a registry value on the right with the
ProductCode, and you will have found the UpgradeCode. This can be useful in cases
where a previous product is preventing the install from completing successfully.
Supporting Norton AntiVirus 2007 128
MSI Log Analyzer
The MSI Log Analyzer is a utility that is used to analyze reports generated from the
Windows Installer log files. This is of great assistance in troubleshooting installation
issues.
The Windows Installer Verbose Log Analyzer enables users to select a log file for
analysis, once a log file is open it then provides a preview of the log file and when
the Analyze button is selected it provides a detailed view of the log file and options
to debug the log files.
For further information on the MSI Log Analyzer, please refer the following MSDN
documentation of the Tool:
http://msdn.microsoft.com/library/en-us/msi/setup/wilogutl_exe.asp
A screenshot of the utility is as provided below:
Supporting Norton AntiVirus 2007 129
DebugHlp
This tool replaces the Symlogon and Symlogoff registry keys. This tool enables
verbose logging for MSI and activities that take place within the program
environment.
Using the tool
Debughlp.exe tool needs to be executed before installing the Norton program so that
the debugger can track and log the MSI activities. Unlike MSI log files, logging
through DebugHlp.exe is done module-wise. Once Debugging is enabled, the logs are
saved in C:\Symlogs folder. To use the DebugHlp tool:
1. Click Start
2. Click Run
3. Drag and drop the DebugHlp.exe
4. Enter the switch to start debugging and hit the enter key.
5. Logging starts.
The tool Debughlp.exe can be used with 3 switches.
/Debugon
This switch enables logging and starts creating logs in the Symlogs folder.
/DebugOff
This switch turns off debugging
/DebugOnOff
Enables and disabled degugging instantly. This switch is used to log instant activities.
/Runconfigwiz
Forces the configuration wizard to execute.
Supporting Norton AntiVirus 2007 130
Once the installation is complete, browse through the Symlogs folder to view logs of
individual installation modules.
Each log file holds the install information for that specific module. In case of an error,
the verbose logging will give information about that specific error and the cause of
the error.
If the debugger is enabled while the Norton program is working, then it logs debug
information related to all activities. Any error feature based error message can be
tracked by looking into log that corresponds to that feature.
Debughlp.exe logs the updates that LiveUpdate downloads and installs as well. The
information on Update logging is held in Spa.log
Supporting Norton AntiVirus 2007 131
AccessEnum
AccessEnum is a utility that can be used to view user accesses to a tree of directories
or registry keys. It gives you a full view of your file system and Registry security
settings
It uses standard Windows security APIs to populate its list view with read, write and
deny access information. This information can be very useful in troubleshooting
installation or usage issues while using Norton applications.
AccessEnum can be obtained from:
http://www.sysinternals.com/Utilities/AccessEnum.html
With this, you can verify that the User has sufficient permissions to read and write
the ROOT directories and registry keys to ensure that all files can be read and
written to by both the User and the Norton Program started by the user.
Process Explorer
Process Explorer is a tool which shows the complete information about a process
including which handles and DLLs that a particular process has opened.
It also has a search capability that will quickly show you which processes have
particular handles opened or DLLs loaded
The display consists of two sub-windows. The top window shows a list of the
currently active processes, including the names of their owning user accounts. The
information displayed in the bottom window depends on the mode that Process
Explorer is in, which can be either of the two:
Handle Mode
If the bottom Window is in the handle mode you can see the handles that the
process selected in the top window has opened.
DLL Mode
If Process Explorer is in DLL mode you’ll see the DLLs and memory-mapped files that
the process has loaded.
Process Explorer can be downloaded from the link provided below:
http://www.sysinternals.com/Utilities/ProcessExplorer.html
Most of the access denied error messages that you get can be determined and
troubleshoot using Process Explorer and AccessEnum. For more details on Access
denied error, please read the document from Microsoft:
http://support.microsoft.com/kb/q245068/
Supporting Norton AntiVirus 2007 132
Tracert
This diagnostic tool determines the path taken to a destination by sending ICMP Echo
Request messages. Tracert determines the path by sending the first Echo Request
message with a TTL of 1 and incrementing the TTL by 1 on each subsequent
transmission until the target responds or the maximum number of hops is reached.
The maximum number of hops is 30 by default and can be specified using the -h
parameter.
The following Command Switches are available with this utility:
-d : Prevents tracert from attempting to resolve the IP addresses of intermediate
routers to their names.
-h MaximumHops : Specifies the maximum number of hops in the path to search
for the target (destination).
-j HostList : Specifies that Echo Request messages use the Loose Source Route
option in the IP header with the set of intermediate destinations specified in HostList.
With loose source routing, successive intermediate destinations can be separated by
one or multiple routers. The maximum number of addresses or names in the host list
is 9. The HostList is a series of IP addresses (in dotted decimal notation) separated
by spaces.
-w Timeout : Specifies the amount of time in milliseconds to wait for the ICMP Time
Exceeded or Echo Reply message corresponding to a given Echo Request message to
be received. If not received within the time-out, an asterisk (*) is displayed. The
default time-out is 4000 (4 seconds).
TargetName : Specifies the destination, identified either by IP address or host
name.
-? : Displays help at the command prompt.
Further Information about the utility can be obtained at the “Tracert” page of the
Windows XP documentation. A link for the same is provided below:
http://www.microsoft.com/resources/documentation/windows/xp/all/proddocs/en-
us/tracert.mspx?mfr=true
This tool can be used to determine the path traversed while trying to access a
Website.
Supporting Norton AntiVirus 2007 133
InstallRite
InstallRite is a program used to detect the modifications that are made to the
system after installing a program. When you perform a scan with InstallRite, it
makes a full database of your system, including files, folders, date stamp of files,
CRC check and Registry.
InstallRite Scan
After running the scan, you install the program on the machine. Then you
perform another scan of your machine hard drive, and any changes reported
compared to the initial scan is considered to be part of the software installation. We
it is finished, you get a complete image of the trace left by an installation package.
The “Export details to HTML” and “Export detail to TEXT” option can be used to get a
copy of the log from the customer’s computer.
The files that are added during the installation of the program
You can view the added, modified and deleted registry keys
Supporting Norton AntiVirus 2007 134
InstallRite will even let you build an InstallKit, which is a self-extract file that will
copy all files and registry entries as they have been identified as part of a software
package. You can also use this to perform uninstalls.
In addition it provides "application cloning" as opposed to "disk cloning." This
is interesting, because it is not a sequential script or a batch file. In fact, it is much
simpler than this, it gives you the final result of the installation process, not the
process itself. This means that you can install a piece of software, configure it to suit
your needs, and then make an InstallKit containing all your custom settings. It
allows PATH redirection, so if some machines have different path names, it will still
be working. You can specify what action to take when encountering existing files,
and force or prevent rebooting after install.
The latest version of InstallRite (Version 2.5) can be downloaded from:
http://www.epsilonsquared.com/anonymous/InstallRite25.exe
Supporting Norton AntiVirus 2007 135
HijackThis
This section will provide you a brief overview on the HijackThis tool. After you
complete this section, you will be able to do the following:
• Describe the usage of the HijackThis tool
• Analyze the results / logs generated by the tool
• Troubleshoot a relevant issue using the tool
HijackThis scans all the load points and displays the contents or values that are
stored in them. It also shows the Processes that run in the background when the tool
is run. While HijackThis displays the values and data present in the load points, it is
up to the user to decide which program or file is malicious and which is valid. Once a
file or a program has been identified as illegitimate or malicious, it can be easily
deleted through the tool. The HijackThis tool itself cannot differentiate between a
legitimate and an illegitimate program. There are various ways of differentiating a
legitimate program from an illegitimate one, which will be covered in a later section.
Let’s now have a look at the tool itself.
Obtaining the tool
HijackThis can be downloaded from the following link:
http://www.hijackthis.de
Note: Extract the downloaded zip file and save HijackThis.exe in a folder.
Double-clicking on the tool should open a screen with several options. To analyze all
load points and running tasks, click on the “Do a System Scan and Save log file”
button. Clicking on this button should open a screen similar to the one shown below:
Each entry shown in this window has a specific value in the beginning. Each value
has its own specifications. Following is a description of each value:
* R0, R1, R2, R3 - Internet Explorer Start/Search pages
* F0, F1 – Programs that start automatically
* N1, N2, N3, N4 - Netscape/Mozilla Start/Search pages
* O1 - Hosts file redirections
* O2 - Browser Helper Objects
Supporting Norton AntiVirus 2007 136
* O3 - Internet Explorer toolbars
* O4 - Autoloading programs from Registry
* O5 - IE Options icon not visible in Control Panel
* O6 - IE Options access restricted by Administrator
* O7 - Regedit access restricted by Administrator
* O8 - Extra items in IE right-click menu
* O9 - Extra buttons on main IE button toolbar, or extra items in IE 'Tools' menu
* O10 - Winsock hijacker
* O11 - Extra group in IE 'Advanced Options' window
* O12 - IE plugins
* O13 - IE DefaultPrefix hijack
* O14 - 'Reset Web Settings' hijack
* O15 - Unwanted site in Trusted Zone
* O16 - ActiveX Objects (Downloaded Program Files)
* O17 - Lop.com domain hijackers
* O18 - Extra protocols and protocol hijackers
* O19 - User style sheet hijack
* O20 - AppInit_DLLs Registry value autorun
* O21 - ShellServiceObjectDelayLoad Registry key autorun
* O22 - SharedTaskScheduler Registry key autorun
* O23 - Windows NT Services
HijackThis also creates a log file for the user’s convenience so that it can be sent
across to an expert (or a technician for an analysis).
Identifying an illegitimate program
Once the log file has been obtained, it can either be analyzed manually or can be
pasted on the HijackThis website (www.hijackthis.de) for automatic analysis.
Manual Analysis
Manual analysis deals with differentiating a legitimate program from an illegitimate
one. When a suspicious entry is found in the HijackThis results / log, the suspicion
can be confirmed by looking up information in the security response website. To
delete a malicious entry, simply place a check mark next to the entry (s) and click
the “Fix Checked” button to delete the malicious file.
Note: Before deleting a file through HijackThis, make sure that the file / program is
malicious.
By analyzing the log / results, browser hijackers and host file redirections can also be
countered. To remove a host file entry, simply place a check mark next to the O1
value (s) and click the “Begin Fix” button. Do not remove entries in the host file that
may be intentionally added by systems administrators.
Supporting Norton AntiVirus 2007 137
Miscellaneous Tools
There are several Miscellaneous Tools available in HijackThis that can be used for
advanced troubleshooting. The following section provides an overview of the
advanced HijackThis options:
Process Manager
Process Manager is a Task Manager like tool that shows all running tasks along with
their paths and Process IDs. Information about DLL file dependencies can also be
viewed by clicking the “Show DLLs” check box.
Hosts file manager
This option opens a small hosts file editor to remove / modify the hosts file entries.
Delete a file on reboot
A file specified through this option will be deleted upon the next system restart. This
option can be ideally used if a user is unable to delete a file that’s in use or is
running in the background.
Delete an NT service
This is a “handle with care” option that deletes a specified NT-service.
Uninstall Manager
Remove entries from the Add/Remove Programs’ list using this feature. This option
can be used to remove an entry of a program that’s left out in the Add/Remove
Programs list despite of that program being uninstalled.
The main usage of HijackThis tool is to identify malicious programs and eliminate
them. The usage of this tool needs to be controlled and operated in a relevant
environment. Do not delete a file or a program through HijackThis which you are
unsure of being illegitimate. Always consult a Supervisor or a lead before doing so.
Supporting Norton AntiVirus 2007 138
You might also like
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Data Migration Tool For Azure DevOps Migration GuideDocument60 pagesData Migration Tool For Azure DevOps Migration GuideMadhu ReddyNo ratings yet
- Digital Marketing Vocabulary ListDocument17 pagesDigital Marketing Vocabulary Listmorgan haferNo ratings yet
- Snowflake's SnowPro Certification Preparation GuideDocument6 pagesSnowflake's SnowPro Certification Preparation GuideAnantNo ratings yet
- Textbook 638Document150 pagesTextbook 638mistermakaveliNo ratings yet
- Galla Suma: Education ExperienceDocument1 pageGalla Suma: Education ExperienceSuma GallaNo ratings yet
- MIS PPT System Development Life Cycle (SDLC) NikhilDocument12 pagesMIS PPT System Development Life Cycle (SDLC) NikhilNikhil thomas Abraham100% (1)
- Norton AntiVirus 2007 - UpdatedDocument138 pagesNorton AntiVirus 2007 - Updatedapi-3850155No ratings yet
- NAV2005 Instructor GuideDocument148 pagesNAV2005 Instructor Guideapi-3850155No ratings yet
- Norton360 Level 1 UpdatedDocument130 pagesNorton360 Level 1 Updatedapi-3850155No ratings yet
- WapinformationDocument10 pagesWapinformationapi-3850155No ratings yet
- DynamicDocument6 pagesDynamicapi-3850155No ratings yet
- Standard BusinessDocument12 pagesStandard Businessapi-3850155No ratings yet
- Sign HereDocument5 pagesSign Hereapi-3850155No ratings yet
- Shared Tech Lab Guide KeyDocument4 pagesShared Tech Lab Guide Keyapi-3850155No ratings yet
- Norton AntiVirus 2006 Instructor GuideDocument104 pagesNorton AntiVirus 2006 Instructor Guideapi-38501550% (1)
- Shared Tech Instructor Lab GuideDocument26 pagesShared Tech Instructor Lab Guideapi-3850155No ratings yet
- Shared Tech Student Lab GuideDocument26 pagesShared Tech Student Lab Guideapi-3850155No ratings yet
- Norton Internet Security 2008 Level 2 Training ManualDocument26 pagesNorton Internet Security 2008 Level 2 Training Manualapi-3850155No ratings yet
- EFOA Company B200 Pilot Training ManualDocument262 pagesEFOA Company B200 Pilot Training ManualElkin Felipe Ocampo AgudeloNo ratings yet
- Norton Internet Security 2007 L2Document162 pagesNorton Internet Security 2007 L2api-3850155No ratings yet
- Norton Internet Security 2007 L2Document162 pagesNorton Internet Security 2007 L2api-3850155No ratings yet
- Top 52 DBMS Interview Questions (2022)Document24 pagesTop 52 DBMS Interview Questions (2022)Akhila RNo ratings yet
- Ai and Big DataDocument6 pagesAi and Big DataDHNAU ARAVINTH KNo ratings yet
- Java Vs RustDocument4 pagesJava Vs Rustphilip.lambert.za8793No ratings yet
- Hadoop FundamentalsDocument14 pagesHadoop FundamentalsHari SampathiraoNo ratings yet
- Architectural Styles of Distributed SystemsDocument15 pagesArchitectural Styles of Distributed Systemsliwase6772No ratings yet
- It430 Collection of Old PapersDocument10 pagesIt430 Collection of Old Paperscs619finalproject.comNo ratings yet
- Try Out 2 SLT: To Allow Integration and Data Exchange Between SAP Components, The Following Service Is NeededDocument7 pagesTry Out 2 SLT: To Allow Integration and Data Exchange Between SAP Components, The Following Service Is NeededSaiful lahNo ratings yet
- STLCDocument3 pagesSTLCapi-3856336No ratings yet
- Client Server Network - Advantages and Disadvantages - I Answer 4 UDocument3 pagesClient Server Network - Advantages and Disadvantages - I Answer 4 UMahmudul HasanNo ratings yet
- Epm BackupDocument58 pagesEpm BackupdmdunlapNo ratings yet
- Blockchain Based Document Verification SystemDocument22 pagesBlockchain Based Document Verification SystemKaran ThakkarNo ratings yet
- Zta Nist SP 1800 35b Preliminary Draft 3Document264 pagesZta Nist SP 1800 35b Preliminary Draft 3Roxana ArancibiaNo ratings yet
- MySql NDB ClusteringDocument6 pagesMySql NDB ClusteringMahadi Hasan JoyNo ratings yet
- 2.1 Firewalls and ACLsDocument16 pages2.1 Firewalls and ACLskxeNo ratings yet
- Alis 67 (4) 257-267Document11 pagesAlis 67 (4) 257-267Sougata ChattopadhyayNo ratings yet
- Lesson 3 - The RPA Journey and The BA's RoleDocument3 pagesLesson 3 - The RPA Journey and The BA's Roleichaz22No ratings yet
- BMC Control M Version Comparison Chart For 9.0.18 Launch v2Document3 pagesBMC Control M Version Comparison Chart For 9.0.18 Launch v2amicableaman949No ratings yet
- ZELIMIR MCDOWELL's RESUMEDocument2 pagesZELIMIR MCDOWELL's RESUMEZelimirNo ratings yet
- Configuring Activefactory For Archestra License Server Communication Across A FirewallDocument12 pagesConfiguring Activefactory For Archestra License Server Communication Across A FirewallBruno SamosNo ratings yet
- Sharding-Hashgraph A High-Performance Blockchain-Based Framework For Industrial Internet of Things With Hashgraph MechanismDocument10 pagesSharding-Hashgraph A High-Performance Blockchain-Based Framework For Industrial Internet of Things With Hashgraph Mechanismyanshaowen0211No ratings yet
- Infrastructure Deployment WBS Project PlanningDocument2 pagesInfrastructure Deployment WBS Project PlanningM iqbalNo ratings yet
- BACnet IoT Gateway Start-Up GuideDocument94 pagesBACnet IoT Gateway Start-Up GuidepatoebmNo ratings yet
- PPL Unit-IDocument76 pagesPPL Unit-Ijyothinarne07No ratings yet
- Daniel (M)Document6 pagesDaniel (M)Sri GuruNo ratings yet