Professional Documents
Culture Documents
05 en MMTK Wireless Access-Point-Configuration Handout
Uploaded by
Kamal OdnOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
05 en MMTK Wireless Access-Point-Configuration Handout
Uploaded by
Kamal OdnCopyright:
Available Formats
ITRAINONLINE MMTK ACCESS POINT CONFIGURATION HANDOUT
Developed by: IT +46 Based on the original work of: Onno W. Purbo and Sebastian Buettrich
Table of Contents
1. About this document .............................................................................................................1 1.1 Copyright information.......................................................................................................2 1.2 Degree of difficulty...........................................................................................................2 2. Introduction...........................................................................................................................2 3. Before You Start....................................................................................................................2 4. Installing hardware and firmware...........................................................................................3 4.1 Physical installation.........................................................................................................3 4.2 Updating Firmware..........................................................................................................4 4.3 Connect your computer to the device .............................................................................4 5. Configuring hardware following the OSI model......................................................................5 5.1 The Physical Layer..........................................................................................................5 5.1.1 Channel Number.......................................................................................................5 5.1.2 Transmit power.........................................................................................................5 5.1.3 Speed or capacity.....................................................................................................6 5.2 The Link layer..................................................................................................................6 5.2.1 Operational Modes ...................................................................................................6 5.2.2 SSID (Service set identifier)......................................................................................7 5.2.3 Media Access Control...............................................................................................7 5.2.4 Access Control through MAC filtering........................................................................9 5.2.5 Encryption (WEP, WPA)............................................................................................9 5.2.6 Restricted access through authentication................................................................10 5.2.7 End-to-end encryption.............................................................................................10 5.3 The IP layer...................................................................................................................10 5.4 The Application Layer....................................................................................................11 6. Conclusions.........................................................................................................................11
1. About this document
These materials are part of the ItrainOnline Multimedia Training Kit (MMTK). The MMTK provides an integrated set of multimedia training materials and resources to support community media, community multimedia centres, telecentres, and other initiatives using information and communications technologies (ICTs) to empower communities and support development work.
1.1 Copyright information
This unit is made available under the Creative Commons Attribution-ShareAlike 2.5 License. To find out how you may use these materials please read the copyright statement included with this unit or see http://creativecommons.org/licenses/by-sa/2.5/.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/
1.2 Degree of difficulty
The degree of difficulty of this unit is Basic with some additional Advanced parts. All Advanced parts are marked with a red frame to emphasise the higher level of difficulty of that section.
2. Introduction
This unit provides a general methodology for installing and configuring wireless access points and routers. Instead of focusing on which button to press, we aim to provide an understanding of what each setting implies and when and why a certain setting is needed. The methodology follows the OSI model with main focus on the physical and the link layer. Additionally, a graphical web based step-by-step process of access point configuration is provided in Appendix 1.
3. Before You Start
Independent of which hardware you are using or what network topology you might want to set up, there is a set of general guidelines that you should always keep in mind. 1. Read the manual of the access point and get to know the device and its default settings. 2. Consider the physical installation placement (access to power, antennas, temperature, humidity etc.). See Site Survey for further information. 3. Plan the network (TCP/IP) before you start and make a drawing of the topology. Planning includes knowing your ISP's or LAN settings including DNS, etc. 4. Make sure that you have all documentation and material (physically, not only online), so you can work even if you are disconnected during the process. 5. Take notes about every step you take in the configuration process, especially when changing IP addresses, network settings and passwords. 6. Make sure that you have all necessary hardware needed (PC/laptop with wireless and Ethernet interfaces) 7. Make sure that you have all necessary software needed such as: TCP/IP software tools (ping, route) Vendor specific software (firmware upgrades, drivers, etc.) Software to measure/detect wireless signals (Kismet, Netstumbler)
4. Installing hardware and firmware
The first step of the configuration process is to install the hardware, connect the access point to your computer and (optionally) update the firmware. This section give you an overview of the general physical layout of an access points and how to physically install the device.
4.1 Physical installation
There are typically two different parts of the access points that you should pay attention to: 1. Status LEDs (diodes)1 1 LED= A light-emitting diode
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/ 2
2. Radio and Ethernet Interfaces A set of LEDs is normally found on top of the access point indicating the status of the device. The LEDs typically indicate with flashing or steady (green or red) light the following parameters: 1. 2. 3. 4. Power to the access point Active ports Internal error Ethernet connection (uplink)
The LEDs can give you highly valuable information while troubleshooting your network. We strongly suggest you to carefully study the meaning of each diode in the reference manual of your access point before starting the setup process. The basic interfaces of a wireless access point are. 1. Ethernet: often called WAN (connection to Internet) or LAN (connection to LAN). A pure access point (wireless bridge) has only one Ethernet port. An access point with more than one Ethernet port is normally a Wireless Router/Gateway. 2. Radio/Antenna(s): Wireless connection to clients More advanced wireless devices can be equipped with two or more wireless interfaces (two or more radios). On one of the rear sides, we can typically find the Ethernet interfaces together with a few other functionalities. 1. 2. 3. 4. Power input (12V, 5 V or 3.5 V DC): connect to DC power source. Reset button: Used to restore default settings LAN Connectors (RJ45): connect to LAN WAN port (RJ45): connects to a DSL, cable modem or any upstreams provider for uplink connectivity
Image 1: A typical setup of connectors and adapters on the rear end of an access point (wireless router). Furthermore, an access point is equipped with a (pair of) antenna(s) that can be built in or attached to the cover of the access point. The external antennas can normally be adjusted to fit a specific implementation.
4.2 Updating Firmware
The firmware is a software that has been written into the ROM (read-only memory) and become a permanent part of the device. One can say the firmware is a hard-software. The firmware will remain in the ROM memory after the device has been switched off. The BIOS program that controls every computer at start up is also a firmware. Vendors update the firmware of their products continuously to offer the latest configuration and correct reported bugs. Always update the access point to the latest stable firmware before you start to configure it and check for updates periodically.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/ 3
4.3 Connect your computer to the device
To configure the access point, you need to connect your PC or laptop to it. This can be done wired or wireless. It is highly recommendable to start the configuration using a wired connection and later, once basic settings are in place and you feel more confident with the configuration process, switch to wireless. The wired connection can be done using: 1. Ethernet cable via HTTP 2. Ethernet using vendor specific software based on SNMP 3. Serial cable (Null modem) using HyperTerminal or other serial communication program (if the access point has a Serial Port) Among the three options, the most common is to connect via Ethernet cable using HTTP. This way of configuring the access point is platform independent and only requires a web browser. Be aware, that the User Interface (UI) will look different from vendor to vendor and from model to model. They change constantly and you will never find two of the same kind. However, they all contain the same basic elements. Also be aware that not all the vendors refer to the same concepts with the same words. The basic concepts are introduced below: To be able to communicate with the access point, you need to belong to the same IP subnet. Look in the reference manual for the default IP address of the access point and change your own IP address accordingly. Thereafter, open a browser window and proceed with the configuration though the web based interface. There are also proprietary setup utilities for access points configuration which you install on your computer in order to setup a wireless device. They are normally based on a protocol known as SNMP. (See Troubleshooting Unit) The third option, using a serial cable, can be considered as your backup plan when things have gone wrong. This option implies that you need to have physical access to the device, and can hence not be done by anyone. Serial cable is typically used as way to reconfigure the access point when you have forgotten the password and do not want to reset to default settings. Normally, you can access the access points via the serial interface without knowing the password (or you can set up a non-password via the Serial Cable).
5. Configuring hardware following the OSI model
At first glance, access point configuration might look fairly complex, judging by the thickness of the reference manual. Normally, a great amount of settings are available and it can be difficult to distinguish the basic settings from the mode advanced settings. A pure1 access point only needs two settings: 1. SSID name 2. Channel number However, it is often convenient to set other parameters. Many optional parameters refers to security in terms of encryption and restricted access, but are of course important if you want to secure the connection. Below follows a theoretical approach to hardware configuration that follows the OSI model and puts emphasise on what each setting actually does and why it is needed. We strongly believe that to understand, WHY a certain configuration is important and WHAT a certain parameter implies, is essential for building high quality wireless networks.
1 By pure we mean an Access Point that acts a wireless bridge with NO routing capabilities. The access point does not provide NAT, DHCP etc. 4
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/
As we know by now, wireless networking is restricted to the first two layers of the OSI model, the physical and the link level. Since an access point is a wireless device, nothing else than a wireless hub, its pure wireless settings are all affecting the first two OSI layers. If the access points supports routing and NATing, they will also includes settings related to the OSI Layer 3: IP layer.
5.1 The Physical Layer
The parameters of an access points that affect the physical layer are the following:
5.1.1 Channel Number
When setting the channel of an access point, you determine the range of frequencies (Ghz) that the device will operate in. Before you set the channel, you should scan the frequency range of interest with a software like Netstumbler or similar, to avoid using the same channel as other networks (if present). By doing so, you will ensure a more idle frequency spectrum for your network. For IEEE 802.11b networks, use channels 1, 6 or 11 to ensure enough frequency separation to avoid conflicts. For 802.11a networks there is no risk of overlapping channels, so just make sure surrounding IEEE 802.11a access points are operating in different channels than the one you select. Some new access points have a feature that automatically sets the channel based on idle frequency by scanning the spectrum and finding out which ones that are already in use. See unit Site Survey for further information.
5.1.2 Transmit power
The higher the transmit power is, the larger coverage range the access point will give you. If you aim to archive as large coverage as possible, the transmit power should be set to the highest value. For many countries the upper legal limit it 100mW (20dB), while in others (many African countries) that upper limit is 1-3 W. Not all the access points will allow you to set up the output power. Notice that the upper legal limit of power needs to be calculated considering the gain of the antenna that you use. (See Radio Link Calculation) If you instead aim for increasing the overall capacity of the wireless network by adding access points close together, then the power should be set to to a lower value in order to decease overlap and potential interference. Alternatively, you will like to place antennas adequately to minimize inter-AP interference.
5.1.3 Speed or capacity
In some access points, it is possible to select the preferred speed of operation (11, 5.5, 2 or 1 Mbps for IEEE 802.11b). By doing so, the modulation technique of the data transfer is being changed. As default, set the speed to the highest possible value. If you are building a very long link and experience problems with packet loss, you can try to reduce the speed in order to have a more robust signal.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/
5.2 The Link layer
The parameters of an access points that affect the link layer are the following:
5.2.1 Operational Modes
The mode of the access point should not be confused with the two basic radio modes of any wireless card, which are infrastructure and ad-hoc. The mode of an access point refers to what kind of tasks it performs. The denotation of mode can many times be confusing since different vendors uses different names to describe an operational mode of a product. You should keep in mind that a pure access point only performs tasks related to radio functionality such as bridging. If a so called access point deals with IP related tasks, such as routing and NATing, we are talking about a wireless router. The different modes mainly differ in weather the access point performs bridging or routing/NATing. The section below describe a set of typical modes' that you will find in access points (or wireless routers). Note that the name of the mode can differ from vendor to vendor. Access Point Bridging (alt. Access Point Mode) The access point works as a pure bridge between a router and wireless clients. No routing or NATing takes place in the access point. This is the simplest configuration mode for an wireless access point. Gateway The access point acts as a wireless router between a LAN and a set of wireless clients by performing routing or NATing to its clients. The access point can obtain an IP address from the upstream provider by means of DHCP. The access point can deliver IPs by DHCP to its clients. Point-to-Point bridge (alt. Repeater mode) Two access points are used to bridge TWO wired networks. No NATing is performed in the access points as it simply passes on data packets. Point-to-Point routing (alt. Wireless Bridge Link) The access point is used as a wireless router between two separate LAN's. Wireless Ethernet adapter (alt. Wireless Client mode) This mode is used to connect any computer that does not support wireless adapters. By connecting an access point to such a device via Ethernet or USB, the access points can be used as a wireless adapter.
5.2.2 SSID (Service set identifier)
The SSID is the name of the wireless LAN and is also attached to all beacon packets sent by the access points1. The SSID is a case sensitive text string that accepts up to 32 alphanumeric characters and it is used to during the association process to a wireless network. The association process is equivalent to the action of plugging a cable into the wall. Clients that want to communicate with a certain access point, must use the SSID during the association process (see Client Installation for further information). The SSID of an access point is by default broadcasted (beacon) to announce its presence. That means that anyone with a wireless adapter can see your network in terms of your 1 More information about SSID: http://www.issa-uk.org/downloads/presentations/issauk/wp_ssid_hiding.pdf. 84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/ 6
SSID. If no extra security mechanism in terms of encryption (WPA) or authentication (MAC filtering, captive portal) has been implemented in the access point or the network, anyone can associate with your access point and reach the network behind it. Many access points offer the possibility to turn off the broadcasting of the SSID and in that way make it possible to hide the network to the public. This trick can be used to improve the wireless network security against average computer users. However, for advanced users it is a weak form of wireless network security since with the right tools, you can monitor and capture certain packets of the wireless network and in that way find the SSID.
5.2.3 Media Access Control
There are some advanced settings in access points that can be particularly relevant for congested (crowded) networks. Those parameters are for example Beacon interval, RTS/CTS and fragmentation. Beacon interval The beacon interval is the amount of time between access point beacon transmissions. The default value for this interval is generally 10ms, which implies that 10 beacons are sent every second. This value gives you sufficient support in terms of mobility within an office environment. If you need support for higher mobility, you can increase the beacon interval. Decreasing the beacon interval results in a reduced overhead in the network but it is likely that roaming between base stations will not work seamlessly. We recommend you not to change this value unless you have very good reasons to do so.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/
Request-to-send (RTS) / Clear-to-send (CTS) RTS/CTS is the method used by IEEE 802.11 wireless networks to reduce collisions caused by hidden nodes (See Advanced Wireless Networking). In brief, it is a method to grant access to use the medium which involves a handshaking process between an access point and a wireless node. RTS/CTS introduces Collision Avoidance in CSMA/CA and hence, makes the access method more robust. At the same time, it adds unavoidable overhead to the network. The RTS/CTS works as following. A node that wants to send data initiate the handshake with the access points by sending a RTS frame. The access points receives the RTS and responds with a CTS frame if the medium is idle. When the node receives the CTS, it starts to send its data. As all the nodes must be able to listen to the access point, the CTS frame will reach all nodes connected to it. The CTS frame includes a time value that the other nodes must wait until they send any RTS frame. A completed RTS/CTS handshake will ensure that the node can send its data without being corrupted by frames sent by other nodes. If there is only a few clients in the wireless network and all of them can see each other, the RTS/CTS option should be switched OFF. Using RTS/CTS in this case would only introduce overhead by including RTS/CTS frames and decrease the total throughput. If there is a chance of hidden nodes in the network, you should consider using RTS/CTS. In this case, RTS, CTS will both introduce overhead in terms of RTS/CTS frames but might also reduce the overall overhead in terms of fewer retransmissions of data frames. The questions is which factors that is the larger one? Do you introduce more overhead than you reduce? To find our, you need to measure the packet loss rate (on TCP level) for both options.
Fragmentation The IEEE 802.11 standard includes an optional feature that allows radio based NICs and access points to fragment data frames intro smaller pieces to improve performance in presence of interference or poorly covered areas. By sending smaller frames, the risk of collisions with other frames are less likely. This results in increased reliability of frame transmission (but higher overhead). The fragmentation value, normally between 256-2048 bytes, can be controlled by the user. The fragmentation effect will take place when the access point or the wireless nodes tries to send a frame with greater size than the fragmentation threshold. Just like the RTS/CTS function, you should first monitor the network and estimate the amount of retransmissions caused by collisions. If the level of collisions is high, then consider changing the fragmentation threshold. In the case of less than 5% collisions, do not use the fragmentation option since the overhead of the fragmentation frames would introduce more overhead than the nonexisting collisions would reduce.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/
5.2.4 Access Control through MAC filtering
MAC filtering implies that you allow only a limited set of known MAC addresses to connect to the access point. This is a very weak security measurement but can be used in combination with other more advanced solutions. An advanced user can easily capture packets that is coming from/to the network and find out which MAC addresses that are granted access. Thereafter, it can change the its own MAC address to one of the accepted ones and fool the access point by pretending to be someone else.
5.2.5 Encryption (WEP, WPA)
WEP (Wired Equivalent Privacy) is an old encryption protocol implemented in most access points nowadays. Although WEP has proven to have great weaknesses and is no longer considered to be a safe option for encryption, it is frequently used among average users. WEP uses the RC-4 40-bit encryption algorithm to scramble all data before transmission between access points and clients. Many vendors add proprietary encryption features to their software and raise the encryption level up to 128 bits. The WEP configuration done in the access point must always be reflected in the client side. Make sure that your client device support the encryption protocol, authentication type and key length that you configure your access point to run. If you choose to enable WEP, always remove the default WEP keys that are provided by the vendor and set your own private keys. If you use the 64-bit key (40 bit as actual key), you must enter a key consisting of 10 hexadecimal characters (0-9, a-f or A-F). The 128-bit key, that provides higher security, consists of a hexadecimal 26 characters long string. Remember! The current alternative to WEP is WPA (Wi-Fi Protected Access), which is the encryption protocol that was designed to address the problems of WEP. WPA2 is the second generation of WPA which is based on the IEEE 802.11i amendment. Still many access points on the market today (2006) supports only WEP by default. Normally, you will find that a firmware update of the access point and the wireless client to WPA is available. Check the vendor website for firmware upgrades. To improve the network security of your network by supporting WPA encryption, the following items needs firmware upgrade: 1. Wireless access points 2. Wireless network adapters 3. Wireless client programs (drivers, management tools etc) For more information regarding wireless encryption see Wireless Security.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/
5.2.6 Restricted access through authentication
Restricted access to a network by means of authentication can be done by using a Radius Authentication server. If a Radium Authentication server is implemented, the access point acts as a Radius client and must be aware of the database settings in the Radius server. As a part of the original IEEE 802.11 standard MAC functions, access points offer open system authentication and sometimes even share key authentication. Since neither one of these authentication systems have proven to be secure, many access points nowadays includes IEEE 802.1x mechanisms for allow authentication of users via an external authentication server. The topic of authentication goes beyond the scope of this unit and will not be further discussed.
5.2.7 End-to-end encryption
End-to-end encryption is the most secure way to protect transfer of valuable data. VPN (Virtual Private Network) offers an end-to-end encryption service and is supported by many access points today. In the case of implementing a VPN, the access point enable VPN Pass-through via PPTP/IPSec. VPN is beyond the scope of this unit and we will not be further discussed.
5.3 The IP layer
Strictly speaking, the IP layer is not a part of wireless communication. However, many access points are not pure access points and includes additional functionality such as routing and NATing. The table below describes briefly each parameters involves the IP layer. Setting IP Address Description The IP address of the access point is not necessary for performing its basic tasks (acting as a wireless hub). The IP address is used to access the device from a web application and to facilitate the configuration process. If the access points is used as a wireless router, the IP address of the access point must be on the same subnet as the router it is attached to and proper routing rules be set up. See Advanced Wireless Networking IP address of the outgoing connection of your network. IP address of the DNS server you announce by DHCP to the wireless clients
Netmask Gateway DNS
Table 1: IP related settings of an access point.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/ 10
5.4 The Application Layer
The most important setting of the whole configuration process is found in the application layer, - the admin password of the access point. The device always comes with a default password (user: admin pass: admin) that we strongly suggest that you change immediately to a stronger password. Avoid passwords that can be connected with you as a person or organization as they are easy to guess. If an unwanted person gains access to the admin password, he/she can hijack your access points and change the password so that you can not reach it. In this case, the only solution is to reset the access point manually or connect via the serial interface and change password.
6. Conclusions
Configuring an access point or a wireless router can be summarized in four big steps:
Understanding the hardware and the solution you want to build Setting up the wireless (physical layer) related parameters as channel, SSID, transmission power and speed. Setting up the wireless (link layer) related parameters as encryption or MAC access control Setting up the IP related parameters if you want to use the IP-functionalities of your access point as routing/NATing or DHCP server
The challenge should not be just to learn the menus of the configuration tool rather to understand what each of the parameters is doing. Every vendor will have a different configuration front-end but the concepts are going to be the same.
84895225.odt Last updated 16 February 2012 Available online from http://www.itrainonline.org/itrainonline/mmtk/
11
You might also like
- Open-Source Robotics and Process Control Cookbook: Designing and Building Robust, Dependable Real-time SystemsFrom EverandOpen-Source Robotics and Process Control Cookbook: Designing and Building Robust, Dependable Real-time SystemsRating: 3 out of 5 stars3/5 (1)
- Itrainonline MMTK Access Point Configuration HandoutDocument11 pagesItrainonline MMTK Access Point Configuration HandoutSantosh KhadkaNo ratings yet
- EW 7207APg ManualDocument41 pagesEW 7207APg ManualSebastiánRaimondoNo ratings yet
- Computer Networking: An introductory guide for complete beginners: Computer Networking, #1From EverandComputer Networking: An introductory guide for complete beginners: Computer Networking, #1Rating: 4.5 out of 5 stars4.5/5 (2)
- INTELLINET ROUTER Libretto9661-02-1Document24 pagesINTELLINET ROUTER Libretto9661-02-1gianmaria segaliniNo ratings yet
- Wp4001br2 ManualDocument43 pagesWp4001br2 ManualSinchan Sintetis100% (1)
- Practical Data Acquisition for Instrumentation and Control SystemsFrom EverandPractical Data Acquisition for Instrumentation and Control SystemsNo ratings yet
- AWAP602 ManualDocument41 pagesAWAP602 ManualdivxnsNo ratings yet
- Introduction To Packet TracerDocument4 pagesIntroduction To Packet Tracersaika sairaiNo ratings yet
- TC7650 (US) V1 User GuideDocument23 pagesTC7650 (US) V1 User GuideabattzNo ratings yet
- NetworksDocument103 pagesNetworksIamSajid JatoiNo ratings yet
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- PacketFence Network Devices Configuration Guide-3.4.1Document74 pagesPacketFence Network Devices Configuration Guide-3.4.1luigybertoNo ratings yet
- Serial Port Complete: COM Ports, USB Virtual COM Ports, and Ports for Embedded SystemsFrom EverandSerial Port Complete: COM Ports, USB Virtual COM Ports, and Ports for Embedded SystemsRating: 3.5 out of 5 stars3.5/5 (9)
- DCON Utility Pro User Manual: Version 2.0.1, February 2019Document49 pagesDCON Utility Pro User Manual: Version 2.0.1, February 2019harves100% (1)
- Longshine WA5 40P Manual EngDocument50 pagesLongshine WA5 40P Manual EngqueerprodigyNo ratings yet
- Administrator and Helpdesk Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesFrom EverandAdministrator and Helpdesk Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesNo ratings yet
- Bajtin, Mijail, "El Problema de Los Generos Discursivos" en Estetica de La Creación Verbal, México, Siglo XXI, 1982Document49 pagesBajtin, Mijail, "El Problema de Los Generos Discursivos" en Estetica de La Creación Verbal, México, Siglo XXI, 1982jmslayer8024No ratings yet
- Computer Knowledge Guide For All Competitive ExamsFrom EverandComputer Knowledge Guide For All Competitive ExamsRating: 3 out of 5 stars3/5 (4)
- 108M Wireless Router GuideDocument42 pages108M Wireless Router GuideJean Dos SantosNo ratings yet
- Lab 2 HandoutDocument7 pagesLab 2 Handouthassaan tanveerNo ratings yet
- CiscoDocument35 pagesCiscoFlorin Zamfir100% (1)
- Technical Reference Manual: (Hardware Version: 2.1)Document23 pagesTechnical Reference Manual: (Hardware Version: 2.1)S G ShivaPrasad YadavNo ratings yet
- En ENetwork IPTM v4040Document38 pagesEn ENetwork IPTM v4040abdelhf1No ratings yet
- CCNA Exploration 4.0.4.0 Instructor Packet Tracer Lab ManualDocument38 pagesCCNA Exploration 4.0.4.0 Instructor Packet Tracer Lab ManualshaytoonballaNo ratings yet
- 2 Port Pci Express Superspeed Usb 3.0 Card: Pexusb3S2Document10 pages2 Port Pci Express Superspeed Usb 3.0 Card: Pexusb3S2CS ENo ratings yet
- Wireless Broadband Router User's Manual w514rDocument62 pagesWireless Broadband Router User's Manual w514rlissbett_99No ratings yet
- HP COMPAQ D330UT-Network & InternetDocument20 pagesHP COMPAQ D330UT-Network & Internetgebo_manNo ratings yet
- Wirelessinformation Upgrades InstallsDocument33 pagesWirelessinformation Upgrades InstallsMr NovaNo ratings yet
- TX4400 Manual v0.94Document39 pagesTX4400 Manual v0.94ahmedalishNo ratings yet
- User's Manual 150Mbps Wireless Broadband Router Model No.: SP916NLDocument81 pagesUser's Manual 150Mbps Wireless Broadband Router Model No.: SP916NLpichirikabvNo ratings yet
- CH3SNAS Manual ENGDocument55 pagesCH3SNAS Manual ENGJavier EsparzaNo ratings yet
- HP-5101AC User Manual English PDFDocument29 pagesHP-5101AC User Manual English PDFlaksonoismiputrantoNo ratings yet
- AP8100 UserGuideDocument86 pagesAP8100 UserGuideAdilson SouzaNo ratings yet
- 03 1001 V5.00 EVRC2A-N Manual SoftwareDocument51 pages03 1001 V5.00 EVRC2A-N Manual SoftwareJureico Reynald Cornejo UrteagaNo ratings yet
- SP916NL User Manual PDFDocument80 pagesSP916NL User Manual PDFSamNo ratings yet
- IOTService User Manual 20181211Document62 pagesIOTService User Manual 20181211Anonymous yugocxnNo ratings yet
- Wifi Onu User Interface Guide v1.3 20160510Document25 pagesWifi Onu User Interface Guide v1.3 20160510IMANUEL ANGNo ratings yet
- EW 7209APg ManualDocument44 pagesEW 7209APg ManualGabriel H. MartinezNo ratings yet
- Catalog: Hdplayer Operating ManualDocument67 pagesCatalog: Hdplayer Operating Manualvuthe9102No ratings yet
- N150 Wireless Router Setup Manual: Netgear, IncDocument45 pagesN150 Wireless Router Setup Manual: Netgear, IncGandhi Hardik RNo ratings yet
- Ccna I Exploration Lab 2 - Intro To Packet Tracer Lab Required Materials - Data File Lsg01-Ptskills1.PkaDocument4 pagesCcna I Exploration Lab 2 - Intro To Packet Tracer Lab Required Materials - Data File Lsg01-Ptskills1.PkaElizabeth NewmanNo ratings yet
- Vacon NX OPTCI Modbus TCP Board User Manual DPD00900A UKDocument32 pagesVacon NX OPTCI Modbus TCP Board User Manual DPD00900A UKKiran AcharNo ratings yet
- Wap 0007Document90 pagesWap 0007aelaosNo ratings yet
- ViewPower User ManualDocument51 pagesViewPower User ManualjaaarfiNo ratings yet
- Unifi Modem Manual - D-Link DIR-615Document101 pagesUnifi Modem Manual - D-Link DIR-615feelgoodboy4366No ratings yet
- User Guide: TPPLC Utility For Tp-Link Powerline Adapters and ExtendersDocument24 pagesUser Guide: TPPLC Utility For Tp-Link Powerline Adapters and ExtendersNicolas DiamanteNo ratings yet
- RP Sb101u MLDocument42 pagesRP Sb101u MLapi-3736776No ratings yet
- Technical Lesson 6Document78 pagesTechnical Lesson 6PAUL GONZALESNo ratings yet
- AN1020-16T - Quick Installation GuideDocument16 pagesAN1020-16T - Quick Installation GuideAmir RazaqNo ratings yet
- Dovado Tiny Reference Manual 6.1.1Document24 pagesDovado Tiny Reference Manual 6.1.175310No ratings yet
- Advantech CANopen User ManualDocument98 pagesAdvantech CANopen User ManualdinhquangcdtbkNo ratings yet
- Tl-wn823n v2 User GuideDocument49 pagesTl-wn823n v2 User Guide123456No ratings yet
- Comm Setup Doosan FanucDocument27 pagesComm Setup Doosan FanucmarkoskitpNo ratings yet
- 3D Pythagoras: Name: Class: Date: Mark: /7 %Document5 pages3D Pythagoras: Name: Class: Date: Mark: /7 %noddynoddyNo ratings yet
- Teaching Comprehension: Little Red Riding HoodDocument13 pagesTeaching Comprehension: Little Red Riding Hoodnoddynoddy100% (1)
- 2D Pythagoras: Name: Class: Date: Mark: /12 %Document5 pages2D Pythagoras: Name: Class: Date: Mark: /12 %noddynoddyNo ratings yet
- 01 Bronze 1 - M1 EdexcelDocument14 pages01 Bronze 1 - M1 EdexcelnoddynoddyNo ratings yet
- Arithmeticpaper3 PDFDocument16 pagesArithmeticpaper3 PDFnoddynoddyNo ratings yet
- Entrance Into Year 4 Writing and Reading Mark Scheme and LevelsDocument27 pagesEntrance Into Year 4 Writing and Reading Mark Scheme and LevelsnoddynoddyNo ratings yet
- Mental Health Promotion - Building An Economic CaseDocument60 pagesMental Health Promotion - Building An Economic CasenoddynoddyNo ratings yet
- S-Reading Comp PDFDocument16 pagesS-Reading Comp PDFKarlita-BNo ratings yet
- 72, Sexual Health Top Tips Full Report FINAL 2Document71 pages72, Sexual Health Top Tips Full Report FINAL 2noddynoddyNo ratings yet
- My Revision Notes Edexcel As History From Second Reich To Third Reich - Warnock, Barbara (SRG)Document73 pagesMy Revision Notes Edexcel As History From Second Reich To Third Reich - Warnock, Barbara (SRG)noddynoddy67% (3)
- My Electricity BookDocument7 pagesMy Electricity BooknoddynoddyNo ratings yet
- 11+ SpellingsDocument14 pages11+ SpellingsnoddynoddyNo ratings yet
- Common Proper Nouns 1Document1 pageCommon Proper Nouns 1noddynoddyNo ratings yet
- My Revision Notes As Edexcel History - Bunce, Robin (SRG)Document81 pagesMy Revision Notes As Edexcel History - Bunce, Robin (SRG)noddynoddy50% (2)
- Fluency Fast Basic ChecklistDocument1 pageFluency Fast Basic ChecklistAdi CheteNo ratings yet
- UWS IT Strategic Plan Detailed 29 June2008Document164 pagesUWS IT Strategic Plan Detailed 29 June2008noddynoddyNo ratings yet
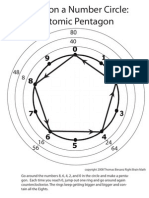
- Eights Atomic WorksheetDocument1 pageEights Atomic Worksheeta touch of classNo ratings yet
- The 5 Must Have Metrics For Your SaaS BusinessDocument10 pagesThe 5 Must Have Metrics For Your SaaS BusinessnoddynoddyNo ratings yet
- Twos Eights Atomic Worksheet 2Document1 pageTwos Eights Atomic Worksheet 2noddynoddyNo ratings yet
- Bouncing Off The Walls:: Adding Interactivity and If StatementsDocument3 pagesBouncing Off The Walls:: Adding Interactivity and If StatementsnoddynoddyNo ratings yet
- Scratch 4 TeachersDocument19 pagesScratch 4 TeachersnoddynoddyNo ratings yet
- Powell Collective ConsultationDocument29 pagesPowell Collective ConsultationnoddynoddyNo ratings yet
- Advice Note On Redundancy and Lay OffDocument12 pagesAdvice Note On Redundancy and Lay OffnoddynoddyNo ratings yet
- Data StreamDocument287 pagesData StreamnoddynoddyNo ratings yet
- Worcester Bosch 28i RSF Combi Installation ManualDocument40 pagesWorcester Bosch 28i RSF Combi Installation ManualnoddynoddyNo ratings yet
- Socialpolicy SocietyDocument21 pagesSocialpolicy SocietynoddynoddyNo ratings yet
- Candidates Letter Head of ICT and ComputingDocument1 pageCandidates Letter Head of ICT and ComputingnoddynoddyNo ratings yet
- Defining Social JusticeDocument3 pagesDefining Social JusticenoddynoddyNo ratings yet
- Book ReviewDocument1 pageBook ReviewnoddynoddyNo ratings yet
- 4D R Subtraction WS 9Document1 page4D R Subtraction WS 9noddynoddyNo ratings yet
- Daily Plankton Agrabinta CianjurDocument141 pagesDaily Plankton Agrabinta CianjurPutra Cahya GemilangNo ratings yet
- CCTV Guidelines - Commission Letter Dated 27.08.2022Document2 pagesCCTV Guidelines - Commission Letter Dated 27.08.2022Sumeet TripathiNo ratings yet
- Demand Determinants EEMDocument22 pagesDemand Determinants EEMPrabha KaranNo ratings yet
- Intertext: HypertextDocument8 pagesIntertext: HypertextRaihana MacabandingNo ratings yet
- Eureka Math Grade 2 Module 3 Parent Tip Sheet 1Document2 pagesEureka Math Grade 2 Module 3 Parent Tip Sheet 1api-324573119No ratings yet
- 1000 KilosDocument20 pages1000 KilosAbdullah hayreddinNo ratings yet
- 2018 H2 JC1 MSM Differential Equations (Solutions)Document31 pages2018 H2 JC1 MSM Differential Equations (Solutions)VincentNo ratings yet
- Bai Tap Av 12 Thi Diem Unit TwoDocument7 pagesBai Tap Av 12 Thi Diem Unit TwonguyenngocquynhchiNo ratings yet
- AREMA Shoring GuidelinesDocument25 pagesAREMA Shoring GuidelinesKCHESTER367% (3)
- Retail Visibility Project of AircelDocument89 pagesRetail Visibility Project of Aircelabhishekkraj100% (1)
- Hot Rolled Coils Plates & SheetsDocument40 pagesHot Rolled Coils Plates & Sheetssreekanth6959646No ratings yet
- ФО Англ.яз 3клDocument135 pagesФО Англ.яз 3клБакытгуль МендалиеваNo ratings yet
- Your Bentley Bentayga V8: PresentingDocument9 pagesYour Bentley Bentayga V8: PresentingThomas SeiferthNo ratings yet
- Snowflake ScarfDocument2 pagesSnowflake ScarfAmalia BratuNo ratings yet
- What Is An EcosystemDocument42 pagesWhat Is An Ecosystemjoniel05No ratings yet
- Ladies Code I'm Fine Thank YouDocument2 pagesLadies Code I'm Fine Thank YoubobbybiswaggerNo ratings yet
- RELATION AND FUNCTION - ModuleDocument5 pagesRELATION AND FUNCTION - ModuleAna Marie ValenzuelaNo ratings yet
- Chapter 15: Religion in The Modern World: World Religions: A Voyage of DiscoveryDocument11 pagesChapter 15: Religion in The Modern World: World Religions: A Voyage of DiscoverysaintmaryspressNo ratings yet
- CSR Report On Tata SteelDocument72 pagesCSR Report On Tata SteelJagadish Sahu100% (1)
- Knitting in Satellite AntennaDocument4 pagesKnitting in Satellite AntennaBhaswati PandaNo ratings yet
- Starbucks Progressive Web App: Case StudyDocument2 pagesStarbucks Progressive Web App: Case StudyYesid SuárezNo ratings yet
- TSC M34PV - TSC M48PV - User Manual - CryoMed - General Purpose - Rev A - EnglishDocument93 pagesTSC M34PV - TSC M48PV - User Manual - CryoMed - General Purpose - Rev A - EnglishMurielle HeuchonNo ratings yet
- Quarter 4 Week 1 EnglishDocument62 pagesQuarter 4 Week 1 EnglishJanine Jordan Canlas-BacaniNo ratings yet
- Planning Effective Advertising and Promotion Strategies For A Target AudienceDocument16 pagesPlanning Effective Advertising and Promotion Strategies For A Target Audiencebakhoo12No ratings yet
- Javascript NotesDocument5 pagesJavascript NotesRajashekar PrasadNo ratings yet
- D15 Hybrid P1 QPDocument6 pagesD15 Hybrid P1 QPShaameswary AnnadoraiNo ratings yet
- NASA Gemini 4 Press KitDocument94 pagesNASA Gemini 4 Press KitOrion2015100% (1)
- Cs205-E S3dec18 KtuwebDocument2 pagesCs205-E S3dec18 KtuwebVighnesh MuralyNo ratings yet
- What Is Terrorism NotesDocument3 pagesWhat Is Terrorism NotesSyed Ali HaiderNo ratings yet
- 30 de Thi Hoc Ky 2 Mon Tieng Anh Lop 9 Co Dap An 2023Document64 pages30 de Thi Hoc Ky 2 Mon Tieng Anh Lop 9 Co Dap An 2023Trần MaiNo ratings yet
- PHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZFrom EverandPHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZNo ratings yet
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNFrom EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNRating: 5 out of 5 stars5/5 (1)
- Cybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringFrom EverandCybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringRating: 5 out of 5 stars5/5 (40)
- AWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamFrom EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamNo ratings yet
- Microsoft Certified Azure Fundamentals Study Guide: Exam AZ-900From EverandMicrosoft Certified Azure Fundamentals Study Guide: Exam AZ-900No ratings yet
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- Networking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366From EverandNetworking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366No ratings yet
- Software-Defined Networks: A Systems ApproachFrom EverandSoftware-Defined Networks: A Systems ApproachRating: 5 out of 5 stars5/5 (1)
- Hacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.From EverandHacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Rating: 5 out of 5 stars5/5 (2)
- Concise Guide to OTN optical transport networksFrom EverandConcise Guide to OTN optical transport networksRating: 4 out of 5 stars4/5 (2)
- Azure Networking: Command Line Mastery From Beginner To ArchitectFrom EverandAzure Networking: Command Line Mastery From Beginner To ArchitectNo ratings yet
- Hacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxFrom EverandHacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxRating: 4.5 out of 5 stars4.5/5 (67)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsFrom EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNo ratings yet
- Alcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsFrom EverandAlcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsNo ratings yet
- Computer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityFrom EverandComputer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityRating: 4.5 out of 5 stars4.5/5 (13)
- AWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamFrom EverandAWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamRating: 5 out of 5 stars5/5 (1)
- Amazon Web Services (AWS) Interview Questions and AnswersFrom EverandAmazon Web Services (AWS) Interview Questions and AnswersRating: 4.5 out of 5 stars4.5/5 (3)